From 04.02.2026 to 05.02.2026, CyberSec Asia will be held in Thailand. Organised by VNU Asia Pacific in collaboration with the National Cyber Security Agency (NCSA) of Thailand, the CyberSec Asia conference focuses on addressing regional cybersecurity challenges and evolving threats, regulations, and innovations. With more than 4,000 visitors and 100+ speakers, Qualysec will also be among the key participants at the event. As a cybersecurity company specialising in VAPT, AI agentic application security, and preemptive security measures, we focus on preemptive security measures to identify risks across web, mobile, cloud network, API, and IoT systems before attackers can exploit them.
Vulnerability Assessment and Penetration Testing (VAPT) forms an essential defence mechanism against security weaknesses. It prioritises the weaknesses through reimagining artificial intelligence (AI). At CyberSec Asia 2026, industry leaders and experts are showing how AI-enabled VAPT elevates vulnerability detection, threat activation, reporting, and risk prioritisation in ways that neither old nor contemporary methods can match. This blog will help you to understand the shift towards AI-supported security, emerging risks, implications for cybersecurity governance, and new ways forward.
Securing AI: The Shift to AI-First Security
Today, 1 in 6 cybersecurity breaches involve attackers using AI as a primary tool, and 1 in 4 attacks result in major data breaches. AI Cyber threats and attacks are now more complex than ever; they are persistent and automated.
How are attackers using AI to cause cyber breaches?
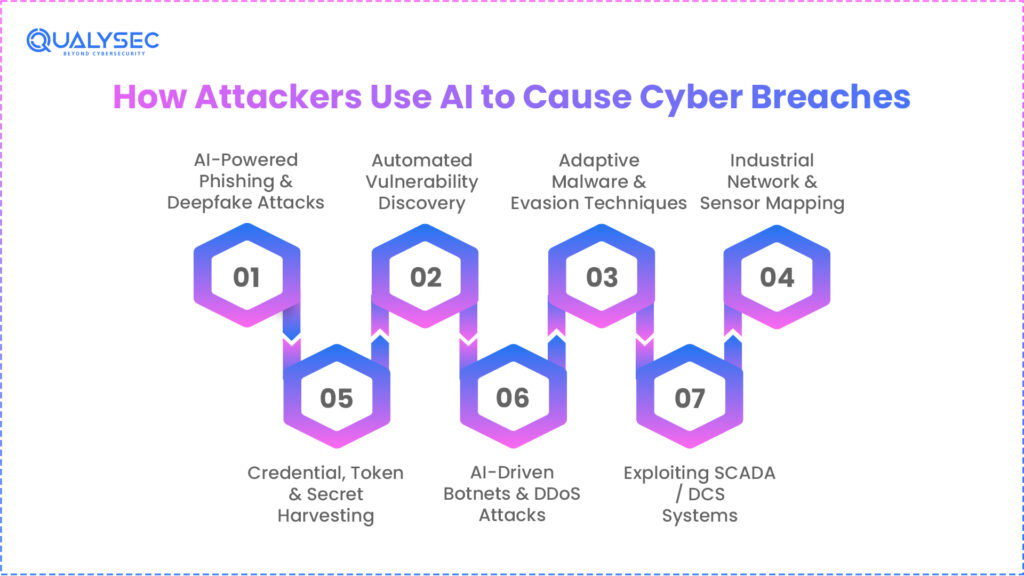
AI has become a powerful tool for cyberattackers. They are taking advantage of AI’s speed and capability to do more complex cyberattacks, which are harder to detect. Here is how the attackers are using AI for their ulterior motive:
- Automating phishing and creating deepfake voice calls and videos.
- AI security tools can automate scans across trading systems, APIs, and payment gateways to discover new weaknesses.
- AI enables malware to choose its attack targets, such as backup systems or PACS servers, and to evade detection by constantly changing its behaviour.
- Automated tools can map extensive industrial networks and sensors to find unsafe configurations that attackers can breach.
- AI bots try hundreds of permutations and combinations at scale to analyse the pattern behind the security systems. It also probes cloud APIs and developer endpoints to collect keys, tokens, and secrets that may be exposed due to misconfiguration.
- AI can adjust tactics to enable large botnets that coordinate distributed denial-of-service (DDoS) attacks.
- AI helps attackers find weak spots in SCADA/DA systems.
Connect with us to take the next step in protecting your AI-driven business, preventing data leaks, and building trust.
Protect Your AI Systems from Cyber Threats

Why is traditional VAPT not enough?
Vulnerability Assessment and Penetration Testing, known as VAPT, emerged as a solid response to growing cyber threats in the late 1990s and early 2000s. While the Vulnerability Assessment focused on scanning systems to detect technical flaws such as unpatched software, misconfigurations, and weak authentication. Penetration Testing went one step further by simulating attacks to exploit those weaknesses. Traditional VAPT tools like Nessus and OpenVAS scan for known CVEs and are used by security teams for basic discovery.
In modern times, when AI carries out the majority of cyberattacks, conventional VAPT is periodic and relies on manual or semi-automated processes that ethical hackers perform. It misses complex attack chains and cloud misconfigurations, and sometimes produces outdated, overwhelming reports that cannot keep pace with rapidly evolving technology and evolving attacker tactics.
Limitations
- No runtime data: Techniques used in VAPT often miss security flaws triggered at runtime. Without analysing the application in its running state, attackers can easily miss cross-site scripting (XSS), SQL injection, or authentication bypasses.
- No continuous monitoring: When a developer deploys new code, an API, or a configuration change, the change introduces a flaw in the security system. That vulnerability can be exploited immediately by the attacker. Traditional VAPT testing can detect vulnerabilities only when the scheduled test runs, not those that appear after the test.
- Limited depth: Traditional scanners focus on known weaknesses but often fail to simulate lateral movement, privilege escalation, and complex behavioural attack patterns that occur in real-time attacks.
- False positives and negatives: Traditional VAPT can generate irrelevant alerts or false vulnerabilities, slowing the process.
- No integration into development workflows: VAPT results are mostly static and not integrated into the software development lifecycle (SDLC). Security issues are manually prioritised, which delays remediation.
- Emerging AI: As mentioned above, attackers are using AI in various ways to cause cyber breaches, and traditional testing methods that rely on known vulnerabilities and static signatures cannot keep pace with these rapidly evolving threats.
How is VAPT used in AI tools and applications?
Vulnerability Assessment and Penetration Testing (VAPT) helps in protecting AI tools and AI-driven applications. Many pre-defined processes by Qualysec help in better assessment, and the AI application VAPT secures AI systems against risks and adversarial inputs.
- VAPT helps in identifying unpatched software and misconfigurations in AI software through automated vulnerability scanning.
- Penetration testing simulates real-world attacks on AI models to exploit weaknesses that cause false outputs.
- VAPT helps in assessing data pipelines in AI applications by scanning the trained data, which later helps in preventing model poisoning during vulnerability assessment phases.
- AI applications use VAPT to detect weak authentication, over-permissive access, or data exfiltration endpoints common in cloud networks.
- VAPT employs behaviour-based exploitation tasks to emulate lateral movement in AI services, which reveal multi-step attack paths.
- VAPT tests generative AI for faster injection attacks through prompt injection testing, where testers detect malicious inputs that bypass security safeguards and extract sensitive training data.
Read more about: How to Perform an AI Risk Assessment
How AI-Driven enterprises are benefiting from VAPT?
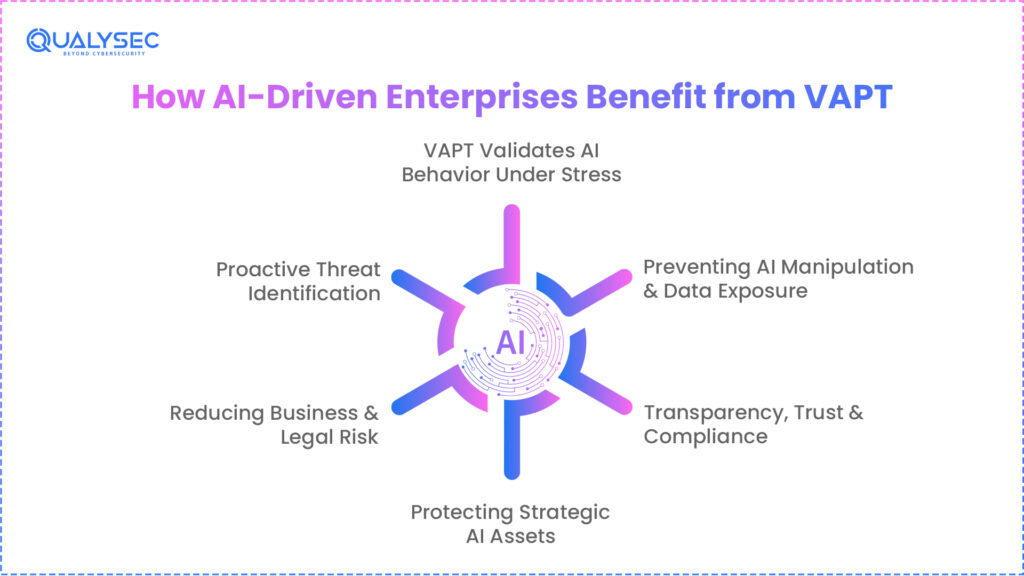
We know that AI is everywhere; it has moved from experimentation to core business operations. AI is helping organisations in customer interaction, decision-making, risk scoring, automation, and even revenue generation.
The Need for AI Application Security
AI systems not only operate autonomously; they can interact with customers, influence business decisions, and evolve themselves over time. Therefore, AI application security is not merely an obligation; it is a need. VAPT evaluates whether AI systems in an organisation behave reliably under stress and misuse.
Preventing AI Manipulation & Data Exposure
Currently, AI systems are being manipulated through input, and models can be coerced into revealing sensitive data. VAPT assesses whether users can misuse AI applications to approve incorrect transactions, leak confidential information, or generate such outputs that can expose the organisation to unwanted consequences.
Transparency, Trust & Compliance
Transparency is one of the major factors supporting a business’s growth. Regulatory authorities, shareholders, partners, and even end users demand evidence that organisations secure their AI systems, actively test the risks associated with those AI systems, and protect sensitive data, and the VAPT provides such evidence. It allows organisations to validate AI systems before and after deployment.
Protecting Strategic AI Assets
From a strategic perspective, AI has become a competitive differentiator, a repository of abundant information and knowledge, and a processor of sensitive, regulated, and unregulated data. This makes AI systems primary targets for data extraction, intellectual property theft, and abuse of the decision-making process. Through AI pentesting, VAPT treats AI models, pipelines, prompts, and agents as first-class assets that require the same efforts of protection as the financial system and customer data.
Proactive Threat Identification
VAPT helps organisations discover weaknesses in their AI application systems, which attackers can use to exploit their systems, thus decreasing their chances of suffering financial losses and reputation damage.
Reducing Business & Legal Risk
Risk(s) related to AI systems are penalised by regulatory actions, civil lawsuits, and loss of brand image & customer trust. VAPT provides answers to the following questions:
- Have the organisations tested how their AI systems fail?
- Do the people in key managerial positions of organisations understand AI risk exposure?
- Can management show control over AI behaviour?
- Is the organisation prepared to explain AI-related incidents?
Download a sample Pentesting Report to See How AI-Driven Enterprises Strengthen Security, Mitigate Risks, and ensure AI Reliability.
Get a Free Sample Pentest Report

How Qualysec plays its part by protecting AI apps and tools through VAPT
Qualysec, a global cybersecurity company that specialises in Vulnerability Assessment and penetration testing (VAPT) in protecting AI applications, tools, and digital assets. Our VAPT services span a wide range of environments from web, mobile, and cloud to API, network, IoT, and AI/ML systems, which makes it an effective partner for organisations seeking end-to-end security validation. This approach focuses on identifying and mitigating vulnerabilities that traditional testing can overlook, including model logic flaws, data injection paths, and insecure integration points.
Our cybersecurity protection strategy is a process-based VAPT methodology, which combines both manual expert testing and automated scanning. We simulate real-time attacks to detect weaknesses in AI pipelines, such as misconfigurations, weak API authentication, insecure data handling, and logic bypasses that could be exploited in production. Our AI/ML application VAPT services explicitly identify, examine, and remediate vulnerabilities in AI and machine learning applications, including potential data leaks, insecure model access, and bias-related flaws. We support organisations in maintaining regulatory compliance and achieving industry standards such as ISO 27001, PCI DSS, HIPAA, and GDP. For AI-driven companies that operate in highly regulated sectors, this compliance readiness backed by VAPT assessment enhances trustworthiness with end users, stakeholders, partners, and regulators.
Conclusion
CyberSec Asia 2026 shows a defining moment for cybersecurity in the age of artificial intelligence. As enterprises have embraced AI in their core businesses, they no longer limit attackers to exploiting infrastructure weaknesses. They are now actively targeting AI logic, data pipelines, APIs, and autonomous decision systems, and this shift demands an equal response and remediation measures. AI Application VAPT combines vulnerability assessment with penetration testing to help organisations shift from static, point-in-time security checks to achieve continuous, adaptive, and evolving risk validation.
For the AI-driven enterprises, protecting sensitive data, maintaining regulatory compliance, preserving brand trust, and ensuring the safe and responsible deployment of AI technologies are paramount concerns. Organisations that invest in VAPT position themselves better to anticipate threats and reduce exposure to vulnerabilities, in line with regulatory and compliance requirements.
Schedule a meeting with our AI expert to know how VAPT can secure your AI systems.
Speak directly with Qualysec’s certified professionals to identify vulnerabilities before attackers do.
Frequently Asked Questions (FAQs)
1. In what ways is VAPT applied to protect AI tools?
VAPT scans AI software for unpatched issues and misconfigurations. It simulates attacks on models to expose output manipulation and assesses data pipelines against poisoning. The tests cloud endpoints for exfiltration, and emulate behavioural exploits in services.
2. Why do AI-driven enterprises need VAPT?
VAPT ensures AI systems are not easy prey to manipulation that leads to faulty decisions or data leaks. It protects competitive assets such as models and pipelines, and safeguards against IP theft.
3. How is VAPT shifting cybersecurity from reactive to proactive?
VAPT combines automated vulnerability assessment with adaptive penetration testing. VAPT moves enterprises from periodic checks to continuous validation, anticipating AI-targeted attacks on logic, data, and decisions for resilient operations.
4. How does VAPT support NIST AI RMF compliance for high-risk AI systems?
VAPT helps in mapping the vulnerabilities to NIST’s Govern, Map, Measure, and Manage functions through adversarial testing, logging, and risk prioritisation, proving traceability and robustness for regulated AI deployments.
5. What role does VAPT play in EU AI Act obligations starting August 2026?
AI application VAPT verifies high-risk AI requirements like risk mitigation, high-quality datasets, human oversight, and cybersecurity accuracy in line with the transparency rules of the EU AI Act.

























































































































































































































































































































































































































































































































































































































0 Comments