Online threats keep getting trickier every year. Hackers aren’t just lone wolves anymore—they work in groups and use clever ways to break into systems. That’s why businesses need more than just basic security tools like antivirus software or firewalls. They need to think like hackers to stay ahead. That’s where Red Team in Cybersecurity comes in. In this post, we’ll look at what they are, what they do, and why they matter in 2025.
What is a Red Team in Cybersecurity?
A Red Team in Cybersecurity is a specialised team that simulates real-world hackers or adversaries to determine how secure an organisation really is. They utilise the same methods as cybercriminals and attempt to find and exploit vulnerabilities in systems, networks, and people—yes, people, because human error is a reality.
What Does a Red Team Do?
Red Teams evaluate your security in all directions: on the internet, in person, and through your staff. They may try to hack into your systems, send an email to your staff pretending to be someone else, or gain access to your building by pretending to be a delivery person.
Red Teams find the weakness before the bad guys do. After they test their security, they provide a report that allows you to fix the weaknesses, which ultimately increases your security standing.
“Read also: What is Cyber Security Testing?“
Red Team vs. Blue Team vs. Purple Team
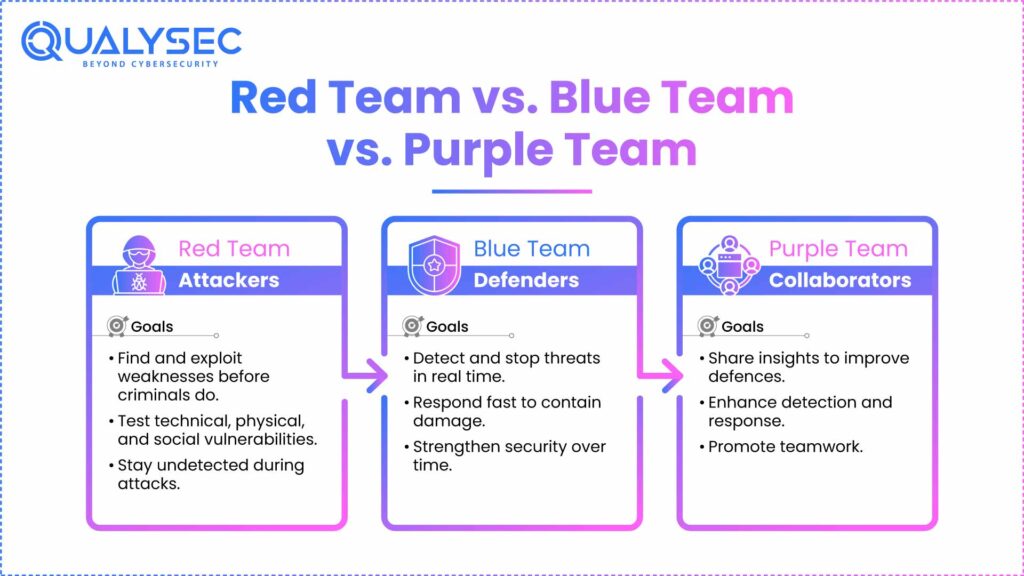
There are different roles in cybersecurity for different teams to protect the organisation, which often include the Red Team, Blue Team, and Purple Team.
Each team plays a role, but they all work towards the same objectives, which is better security. If you understand all team structures, it can help develop strong defences against the issues today. We will discuss what the teams each do quickly.
Red Team (Attackers)
The Red Team acts like the bad guys. They try to penetrate your systems using actual tricks of the trade, including fake emails or planted malware. The Red Team is not only “hacking” your systems; they’re evaluating how your business is capable of detecting, responding, and recovering from an attack. They act covertly, simulating real criminals, to make the test as representative as possible.
Blue Team (Defenders)
The Blue Team is your line of defence. The Blue Team consists of security analysts or incident responders who are responsible for monitoring threats, detecting, and stopping them. During a Red Team attack, it is the combined responsibility of the Blue Team to detect it in real time. Part of their job is to harden systems, fix weaknesses, and build an effective response plan.
Purple Team (Collaboration)
The Purple Team works as the bridge between the Red Team and Blue Team. They help both sides share what they’ve learned and work together. This way, everyone gets better at spotting and stopping attacks. Purple Teaming should discourage silo-based practices and proceed towards a holistic understanding of what worked and didn’t work, and what attack and defence can do together to improve over time, leading to a smarter and stronger security operations capabilities.
How Can a Red Team Help Organisations Stay Safe from Cyber Threats?
A Red Team aids organisations in understanding cyber threats by simulating actual attacks in an orchestrated environment. Most red teaming exercises test organisations on how an attacker may look to exploit weaknesses across their people’s systems, their networks, or the humans that are part of it (using social engineering).
Unlike a standard security test, red teaming is predicated on an attacker’s ability to remain undetected, survive on the target system, and be inventive. Being aware of how their defenses detect and respond to real threats, while identifying shortcomings in their processes, tools, and staff awareness, is valuable for the organisation.
Accordingly, organisations can remediate to close these gaps before a real attack occurs, which significantly improves their overall posture.
Take Control of Your Cybersecurity Posture – Partner with Qualysec.
Talk to our Cybersecurity Expert to discuss your specific needs and how we can help your business.
How Can Qualysec Help You?
At Qualysec, we don’t perform regular scans or casual testing. We conduct full-scope Red Team engagements that simulate all aspects of real-world attacks tailored to your organisation’s specific configuration. From phishing attacks to deep system penetrations, our experts can accomplish anything – and they will, with complete confidence and silence.
After the simulation, you receive a separation report that you can use to secure your organisation. We will work closely with your team to build a long-term security strategy. Think of us as your offensive security partner – helping you stay one step ahead.
Discover the Gaps in Your Cyber Defenses – Contact Qualysec Now.
Conclusion
Cybersecurity in 2025 is not just about being defensively smart, but also being defensively proactive. Red Team in Cybersecurity operations gives your organisation a true look at how vulnerable you are, while ensuring you improve along the way.
Whether you’re a startup or a global enterprise, investing in Red Team operations is a critical requirement. Be smart. Be prepared. Let the Red Team help you find out where to fortify your game. Select the original saying, “fortify your game.”
Find Your Weak Spots Before Hackers Do – Get Started with Qualysec.
Latest Penetration Testing Report

FAQ’s
1. Is Red Teaming a type of penetration testing?
Not really. Both methods evaluate security, but penetration testing is limited to finding technical vulnerabilities. Red Teaming simulates the entire attack, including technical, physical, and social attacks. It is used to determine how well an organisation detects and responds to an attack.
2. How often should the Red Team exercise be performed?
The frequency of Red Team exercises relies on many factors, including the size of the organisation, the industry, and the organisation’s risk appetite. However, many organisations gain the benefits of at least one Red Team operation per year, whenever they implement major infrastructure changes or have other major organisational changes.
3. Can a small business reap the benefits of Red Teaming?
Yes! While small businesses may think they aren’t a target for cybercriminals, they are. Red Teaming helps an organisation identify actual weaknesses and can be scaled for smaller budgets and infrastructures.





















































































































































































































































































































































































































































































































































































































0 Comments