Through a credential-stuffing attack, 4.2 lakh consumer records from a minor Indian fintech company were exposed in January 2025. The breach’s root was an unvalidated API endpoint they had missed throughout their yearly security audits. Though the company held a VAPT certification, they had received a fundamental automatic scan report rather than a thorough, human penetration test. This is a scenario that emphasises the importance of choosing experienced VAPT testing companies in India for comprehensive security assessments.
Businesses are losing hundreds of crores annually because of the discrepancy between what they believe they are acquiring and what many cybersecurity providers truly provide.
We at QualySec know the consequences of this misunderstanding all too well as VAPT service providers ourselves. This handbook seeks to eliminate the noise. We have dissected the leading penetration testing companies now working in India, contrasting everything from the compliance-heavy Big Four auditors to niche, manual-first teams like ours.
Whether you are starting your first company or assessing new offers, this guide will assist you in choosing the best security partner depending on your particular sector needs, budget, and legal requirements.
What is VAPT? Understanding Vulnerability Assessment and Penetration Testing
Vulnerability Assessment and Penetration Testing (VAPT) is a security method that assists enterprises in locating, observing, and remediating weaknesses in applications, networks, cloud platforms, and IT infrastructure.
- Vulnerability Assessment is based on scanning and identifying risks, including old software, poor setups, or unpatched applications.
- Penetration testing goes one step further and attempts to test in the real world how those would actually fare, and attempts to exploit those weaknesses and figure out how those weaknesses would lend themselves to an advantage to a person gaining unauthorised access or even stealing information in the real world.
The integration of the two methods, VAPT services in India, enables businesses to have a clear picture of their security posture and be compliant with security standards, such as ISO 27001, PCI DSS, and GDPR, by enhancing resilience in the long term.
Our Evaluation Methodology: To guarantee a fully furnished regulatory compliance, we verified active empanelment status as of the Q1 2026 benchmark, interviewed and confirmed with 15+ CISOs, and reviewed 50+ anonymised sample reports from Indian cybersecurity firms for manual depth. We did not reply to marketing claims.
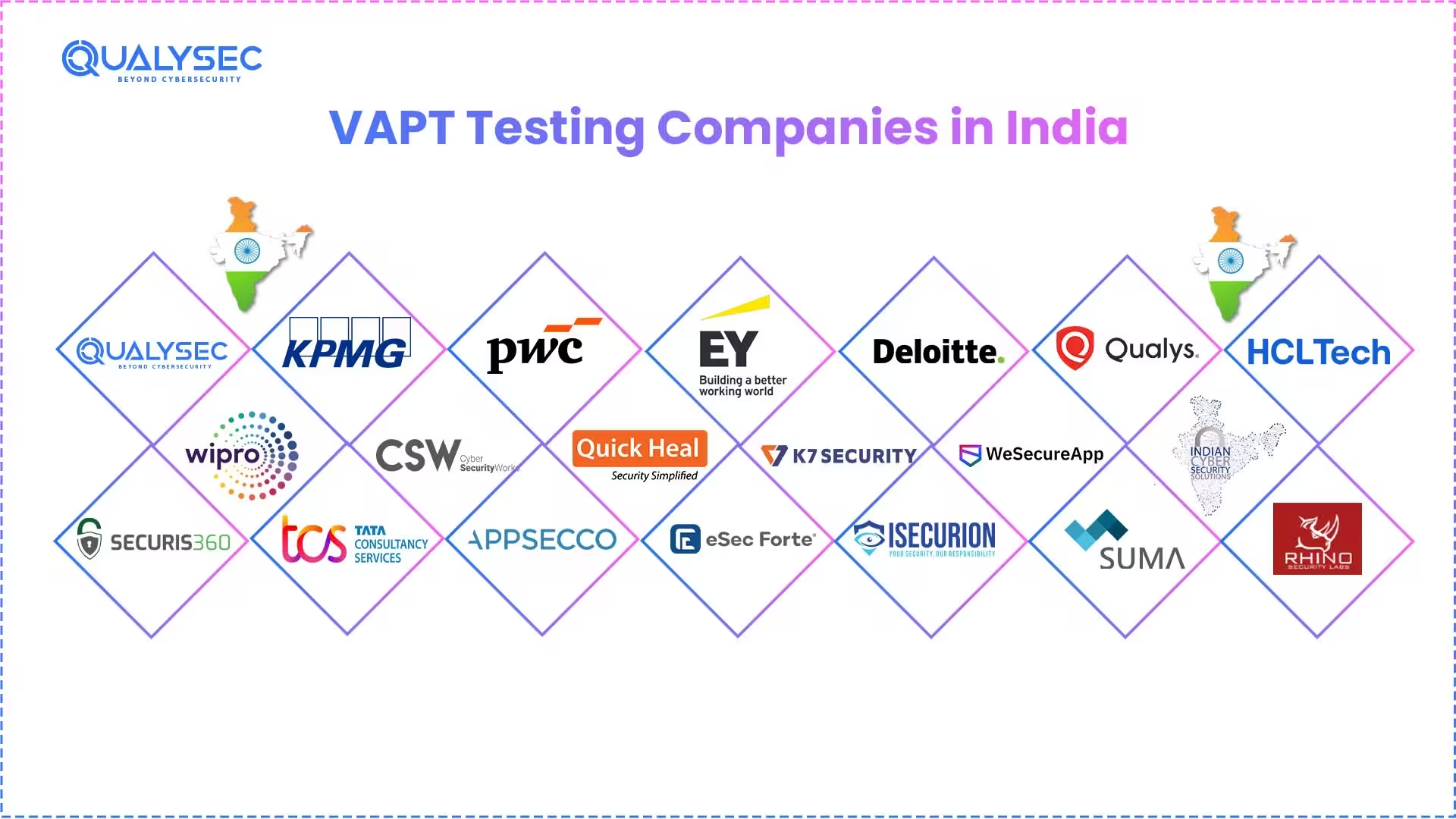
Top 20 VAPT Testing Companies in India (2026)
1. QualySec Technologies
Trust Signals: SOC 2 | ISO 27001 | PCI-DSS | HIPAA | DPDP Act
Aligned Clutch Rating: 4.9 out of 5
Qualysec, the only India-based VAPT service provider, has officially included AI/ML system penetration testing and DevSecOps CI/CD security as main service lines not as upsells. One idea underpins their human-led, AI-powered approach: every important flaw should be shown to be exploitable, not just noted by a scanner.
VAPT Services:
- Web application VAPT (OWASP Top 10 plus business logic testing)
- Mobile VAPT: runtime analysis, binary reversing on iOS and Android
- API Security Testing (OWASP API Top 10 2023)
- Cloud VAPT – AWS, Azure, GCP (CIS Benchmark aligned)
- Reviews of Configuration and Network VAPT
- Security of Embedded Systems and IoT
- Testing AI/ML Systems’ Penetration
- CI/CD Pipeline Security and DevSecOps
6-Phase Approach for Engagement:
- Manual plus automated vulnerability evaluation
- Manual exploitation using proof-of-concept
- Chained attack simulation, lateral movement mapping
- Risk-based reporting: enterprise impact, not only CVSS.
- Remediation directives (code-level plus configuration)
- Post-remediation validation plus complimentary retest
VAPT Deliverables: Executive heatmap dashboards | Step-by-step PoC technical reports | Compliance traceability matrices | JIRA, ServiceNow, and Azure Boards-ready exports
Sectors Served: BFSI (PCI-DSS, RBI) | Healthcare (HIPAA, DPDP) | SaaS | E-commerce | Government
Ideal For: Startups and mid-market companies needing audit-ready compliance papers, zero-false-positive reporting, and manual-first penetration depth would find a great match in.
Pros:
- Manual-first, (AI)-powered testing
- Free post-remediation retesting
- AI/LLM security testing included
Considerations:
- Currently expanding global reach
- Requires advance booking schedule.
- Rapidly growing enterprise portfolio
Your automated scan results can no longer be estimated for their accuracy in detecting critical breach paths. Get a manual security assessment that simulates an actual attacker.
Get Your Free Security Assessment
Contact Us Today2. KPMG
Trust Signals: RBI Empanelled SEBI, IRDAI, CERT-In
KPMG combines VAPT straight into its GRC advising division and regulatory compliance work. Every contact creates acceptable audit evidence. KPMG creates reports especially for annual IRDAI assessments and RBI cyber resilience reviews. Testing gives compliance results precedence over thorough technological exploitation.
VAPT Consulting:
- Infrastructure and network penetration testing
- Mobile and web application security evaluation
- Reviews of cloud security
- Mapped regulatory compliance VAPT reporting
- Red team evaluations of Tier-1 SEBI-regulated companies
Best suited for: Companies on the list and financial institutions (BFSI) that need board-level audit signatures. KPMG offers an institutional reputation that stand-alone security companies cannot equal.
Pros:
- Strong regulatory audit credibility
- Multi-sector compliance expertise
- Board-level reporting standards
Cons:
- Premium engagement pricing tiers
- Compliance-first testing orientation
- Longer onboarding timelines typically
3. PwC
Trust Signals: ISO 27001, DPDP Advisory, SOX, GDPR
PwC converts VAPT results straight into corporate risk registers. CISOs use PwC reports to present security posture alongside financial risk metrics at board meetings. India’s PwC has consistently performed well in healthcare, telecommunications, and BFSI domains.
VAPT Service:
- Enterprise-wide penetration testing and vulnerability evaluation
- Web, mobile, and thick client application security testing
- Cloud security posture evaluation
- Threat analysis and architectural review
- VAPT integration’s security program maturity evaluation
Industries Served: telecom, healthcare, manufacturing, and worldwide businesses, as well as BFSI.
Most Appropriate For: Companies whose framework for managing business risk includes VAPT. When the CISO has to defend security spending to the CFO, PwC shines.
Pros:
- Enterprise risk integration strong
- Multi-framework compliance coverage
- Global methodology and resources
Cons:
- Enterprise-focused pricing structure
- Advisory-led engagement model
- An extended procurement cycle is involved
4. EY India
Trust Indicators: ISO 27001; GDPR; SOC 2; Threat-Led Penetration Testing
Every testing assignment at EY includes worldwide threat intelligence. Active adversary TTPs direct the team’s penetration tests. This method goes above fixed compliance lists. EY India gathers threat information straight from EY’s worldwide cybersecurity hubs.
VAPT services:
- Threat-led penetration testing (CBEST/TIBER-aligned approach)
- Pen testing for web and mobile apps
- Evaluation of cloud security
- Purple and red group activities
- Cyber resilience evaluation combined with VAPT
Industries Served: Large companies, digital transformation initiatives, and companies under various regulatory frameworks serve sectors.
Best For: Companies looking for testing guided by actual enemy behavior. EY suits companies juggling SOC 2, GDPR, and ISO 27001 compliance at once.
Pros:
- Threat-led testing methodology
- Global threat intelligence access
- Multi-compliance simultaneous coverage
Cons:
- Enterprise-tier pricing model
- Structured procurement process required
- Large-enterprise engagement focus
5. Deloitte India
Trust pointers: SOC 2, SOX, GDPR, HIPAA
Deloitte manages, among the top four globally, one of the largest and most sophisticated cyber-risk departments. VAPT data directly feeds into business risk dashboards. Deloitte simultaneously supports Fortune 500 subsidiaries and MNC India operations, handling international compliance demands.
VAPT Services:
- Business penetration testing covers the network, application, and cloud.
- Adversarial simulation and red team
- OT and IoT security evaluation
- Review of safe code
- For multi-framework contexts, compliance-integrated VAPT
Industries served: pharmaceutical, MNC India operations, Fortune 500 departments, BFSI, and technology companies.
Best For: Global corporation divisions needing one VAPT supplier covering several locations and compliance systems.
Pros:
- Global multi-location coverage
- Fortune 500 subsidiary expertise
- Comprehensive risk consulting integration
Cons:
- Enterprise-scale pricing applies
- Structured onboarding process required
- Most appropriate for bigger companies.
6. Qualys
Trust Signals: NIST, FedRAMP Authorized, PCI-DSS
Qualys runs a VAPT platform built for the cloud. The VMDR system provides ongoing asset discovery and vulnerability ranking. Organizations that handle a lot of fast-moving asset inventories benefit the most from Qualys. Through one dashboard, the platform addresses hybrid, on-premise, and cloud settings.
VAPT Consulting
- Ongoing vulnerability management (VMDR)
- WAS for web applications
- Management of cloud security posture
- Supervision of policy adherence
- inventory and finding of assets
Industries Served: Technology, BFSI, healthcare, government, and any company with more than 500 digital assets are among the industries served.
Most appropriate for: Companies seeking ongoing automatic vulnerability management on a big scale. In vast settings, Qualys shines in vulnerability monitoring and asset discovery.
Pros:
- Continuous automated vulnerability management
- Strong asset discovery capabilities
- Cloud-native scalable platform
Cons:
- Platform-centric delivery model
- Automation-focused testing approach
- Requires manual testing supplement
7. HCL Technologies (HCLSec)
Trust Signals: ISO 27001 ICS/SCADA Competence
The security division of HCL provides real IT/OT convergence testing. Not many Indian companies test industrial control systems together with IT networks. HCL covers cloud environments, SCADA systems, and IT networks in integrated interactions. For energy, utility, and manufacturing businesses, this capacity is quite important.
VAPT Support Services:
- Testing of the IT network penetration
- Evaluation of OT, ICS, and SCADA security
- Testing mobile and web applications
- Cloud security evaluation (AWS, Azure)
- Evaluation of IoT device security
Industries Served: Manufacturing, energy, utilities, automotive, and major corporations with Industry 4.0 projects are among the sectors served.
Best for: Big companies that include VAPT in their Industry 4.0 and OT security plans. HCL addresses the IT/OT barrier most security companies overlook.
Pros:
- IT/OT convergence testing expertise
- SCADA/ICS assessment capability
- Large-scale enterprise delivery capacity
Cons:
- Enterprise-oriented engagement model
- Broader IT services focus
- Best suited for large-scale projects
8. Wipro CyberDefence
Trust Signals: ISO 27001, SOC 2
Wipro incorporates VAPT into a more general MSSP (managed security services) framework. Wipro’s worldwide security operations centers use the results of penetration testing. This combination lets one continually monitor after the test involvement is finished.
VAPT Services:
- Network and infrastructure penetration testing
- Testing applications for security flaws
- Evaluation of cloud security
- Ongoing management of weaknesses
- Organized response and detection integration
Industries Served: International companies, telecoms, BFSI, and groups outsourcing security operations.
Ideal For: Companies around the world looking to include VAPT with controlled security services. Companies looking for one supplier for testing and monitoring fit Wipro.
Pros:
- Integrated MSSP plus VAPT
- Continuous post-test monitoring
- Global SOC infrastructure support
Cons:
- Bundled service delivery model
- Broader managed services focus
- Enterprise-scale engagement typically
9. Cyber Security Works (CSW)
Trust Signals: CVE Numbering Authority (CNA)
CSW is the designated CVE Numbering Authority. This substantiates a real original vulnerability research capacity. Live threat intelligence data is used in CSW’s VAPT assignments. The team gives top priority to vulnerabilities that attackers actually use in the wild.
VAPT Services:
- Threat intelligence-related penetration testing
- API security testing
- Testing web and mobile app penetration
- CVE examination and vulnerability studies
- Managing the attack surface
Services for: Tech companies, SaaS platforms, products with lots of APIs, and companies that are good at cybersecurity.
Good For: Technology firms and API-heavy platforms seeking threat intelligence to guide their penetration testing priorities.
Pros:
- CVE Numbering Authority status
- Threat intelligence-driven prioritization
- Strong API security focus
Cons:
- Specialized niche focus area
- Research-oriented service model
- Selective industry vertical coverage
10. Quick Heal Technologies
Signals of Trust: ISO 27001; CERT-In
Quick Heal’s manual VAPT integrates threat information from its massive Indian endpoint network. The broad local backing Quick Heal receives in India makes it sensible for small and medium-sized businesses. For smaller businesses, open pricing and easily understandable scope descriptions help to lower procurement costs.
VAPT Services:
- Penetration testing and network vulnerability analysis
- Testing of web application security
- Endpoint Security Evaluation
- Email security evaluation
- Reporting based on VAPT compliance
Sectors Served: mid-sized businesses throughout India, governmental organizations, educational institutions, and SMEs.
Best For: Small- and medium-sized companies looking for their first official VAPT involvement. Outside of major cities, Quick Heal provides reasonable prices and great local help.
Pros:
- Affordable SME-friendly pricing
- Strong local India support
- Endpoint threat intelligence integration
Cons:
- Endpoint-focused heritage primarily
- Evolving enterprise service portfolio
- Growing compliance framework coverage
11. K7 Computing
Trust Signals: CERT-In Registered ISO 27001
Deep understanding of endpoint and malware resilience testing comes from K7. The Chennai-based firm concentrates particularly on attacks where endpoint compromise starts the attack chain. Among the most affordable entry-level VAPT costs in the Indian market, K7 gives them.
VAPT Service:
- Review of endpoint security evaluation and tightening
- Evaluation of network vulnerability
- Testing web application security
- Testing for malware resistance
- Phishing and email simulation
Sectors Served: Governments, companies emphasizing endpoint security, SMEs, and educational institutions.
Ideal For: Organizations for which endpoint compromise is the most often used threat vector. Companies looking for reasonably priced compliance-oriented VAPT analyses will find K7 appropriate.
Pros:
- Very affordable entry-level pricing
- Strong endpoint malware expertise
- CERT-In registered auditor status
Cons:
- Endpoint-centric service heritage
- Expanding cloud testing capabilities
- Growing enterprise service portfolio
12. WeSecureApp
Trust Signals: India-based CERT-In Empanelled
WeSecureApp uses a hybrid approach that mixes automated scanning with focused human exploitation. The business stresses remediation reports that are developer-friendly. Product teams lacking their own security staff find WeSecureApp’s fix recommendations particularly useful.
VAPT Services:
- Web app penetration testing
- Mobile application security testing (iOS and Android)
- API security testing
- Evaluation of cloud security
- DevSecOps integration and safe code review
Sectors catered to: Companies driven by products, e-commerce, healthtech, SaaS, and fintech among others are catered to.
Most suitable for: Product teams looking for VAPT reports that their engineers can actually act on. Our system bridges engineering procedures and security results.
Pros:
- Developer-friendly remediation reports
- Hybrid manual-automated approach
- Strong SaaS product focus
Cons:
- Product-security focused primarily
- Growing infrastructure testing portfolio
- Expanding compliance framework coverage
Download a sample pentest report and see how your vulnerabilities would be exposed.
Get a Free Sample Pentest Report
Download Now
13. Indian Cyber Security Solutions
Trust Indicators: included in national IT media
For companies doing their first official security evaluation, ICSS offers readily available VAPT services. The business has a solid presence outside of metropolitan areas throughout India. Entry-level rates from ICSS include mobile VAPT, network, and web application.
VAPT Services:
- Evaluation of web application vulnerabilities
- network penetration examination
- Mobile application security check
- Evaluation of Wi-Fi security
- Instruction on security consciousness
Industries served: include local authorities, startups beyond Tier-1 cities, educational institutions, and small to mid-sized firms.
Ideal for: Perfect for businesses starting their first VAPT initiative. ICSS offers an easily accessible beginning point because of its affordable pricing and local availability.
Pros:
- Accessible Tier-2 city presence
- Budget-friendly first-time VAPT
- Broad basic service coverage
Cons:
- Growing advanced testing portfolio
- Expanding certification portfolio currently
- Building national scale presence
14. Securis360
Reliable Signals: Ethical hacking area of expertise
Securis360 runs out of Ahmedabad and has a big presence in western India and Gujarat. Local governments, Tier-2 city businesses, and manufacturing industry customers are among those the company serves. Securis360 has geographically accessible security alliances.
VAPT Services:
- Testing network infrastructure penetration
- Evaluation of web application security
- Phishing simulation and social engineering
- Security testing for wireless networks
- Compliance evaluation and security audit
Sectors Served: Among the fields covered are local government, educational institutions, industry, and SMEs in western India.
Perfect For: Companies in tier 2 cities who would rather have a security partner close by. Securis360 provides on-site testing using locally experienced knowledge.
Pros:
- Strong Western India presence
- On-site testing is locally available
- SME manufacturing sector expertise
Cons:
- Regional specialization focus currently
- Growing national service footprint
- Expanding industry vertical coverage
15. TCS Cyber Security Practice
Trust Signals: Government-Empaneled CERT-In
Among Indian IT services firms, TCS has the biggest cybersecurity practice. Government of India projects and public sector companies rely on TCS for countrywide VAPT assignments. Few providers have the institutional reputation TCS brings.
VAPT Services:
- Network penetration testing across the company
- Evaluation of mobile and web application security
- Assessment of cloud security posture
- Evaluation of SCADA/ICS security
- For governmental frameworks, VAPT is mapped for compliance.
Industries Served: Government of India initiatives, public sector businesses, defense, and national digital infrastructure projects in various sectors.
Best For: Government initiatives and PSUs requiring VAPT with the most institutional legitimacy. TCS manages projects on a national level that many small businesses cannot assist.
Pros:
- Highest institutional government credibility
- National-scale project delivery
- CERT-In government-panneled auditor
Cons:
- Structured enterprise engagement process
- Government/PSU primary focus area
- Formal onboarding procedures required
16. Appsecco
Trust Signals: BFSI and Healthcare Trust Signals
Appsecco incorporates VAPT right into the process of software development. The business combines developer training, secure code review, and penetration testing. Appsecco designs security into engineering methods rather than adding it after implementation.
VAPT Support:
- Application penetration testing, including mobile, web, and API.
- Safe code review
- Cloud platform security evaluation
- DevSecOps advising and application
- Development teams’ security training
Sectors served: product engineering teams, healthtech, BFSI, and SaaS businesses.
Best For: SaaS businesses seeking security incorporated into design from day one will find this ideal. Appsecco is adept at moving security left across the development process.
Pros:
- Security-into-SDLC integration strong
- Developer security training included
- DevSecOps consulting expertise present
Cons:
- Application-security focused primarily
- Boutique-scale operation model
- Development-centric service orientation
17. eSec Forte Technology
Trust Signals: ISO 27001, GDPR Breach Simulation Capacity
eSec Forte goes beyond simple VAPT into a complete kill-chain simulation. Post-exploitation persistence, lateral movement, and data exfiltration paths are modeled by the firm. This method looks at technical flaws together with how well a company can find and fix problems.
Vapt Solutions:
- Application and network penetration testing
- Adversary simulation and red team
- Breach and attack modeling (BAS)
- Social engineering evaluation
- computer forensics and incident response
Areas Served: government, defense, telecommunications, companies having mature security policies, and BFSI.
Best for: Companies that conduct technical penetration testing in conjunction with incident response tabletop drills. eSec Forte assesses your team’s capacity to spot and react to a genuine attack.
Pros:
- Full kill-chain attack simulation
- Red team breach expertise
- Incident response capability included
Cons:
- Advanced simulation focused primarily
- Specialized engagement model used
- Best for mature security teams
18. iSecurion
Trust Signals: ISO 27001:2013 Certified research-driven approach
For penetration testing, iSecurion uses a research-driven methodology. The Bangalore-based business concentrates on sophisticated testing of network infrastructure. iSecurion manages non-standard architectures and older networks where automated tools generate erroneous findings.
Services for VAPT:
- Network infrastructure penetration testing
- Evaluation of application security
- Testing of wireless security
- Review of source code
- Review of security design
Industries Served: Companies using outdated infrastructure, BFSI, and telecom, and those with complicated network configurations.
Most Suitable for: Companies having old networks or odd designs. iSecurion takes care of the complexity that general VAPT companies find challenging.
Pros:
- Research-driven testing methodology
- Legacy network architecture expertise
- Strong network infrastructure testing
Cons:
- Infrastructure-focused specialization primarily
- Boutique-scale delivery model
- Expanding cloud service portfolio
19. Suma Soft
Trust Signals: IT solutions Cloud + Digital Forensics
Within one interaction model, Suma Soft integrates digital forensics, VAPT, and cloud security. The Pune-based business caters to mid-sized businesses needing both proactive testing and reactive forensics capability from a single source.
Services for VAPT:
- Assessment of cloud security (AWS, Azure)
- Testing of applications and networks Penetration
- Investigation of events and forensic digital
- Examination of SOC 2 and ISO 27001 Compliance
- Structured safety solutions
Sectors Served: Among the industries served are healthcare, IT businesses, small to medium enterprises, and organizations creating incident response capacity.
Ideal For: Ideal for medium-sized firms needing proactive penetration testing and post-incident forensic capabilities. Elimination of the need for autonomous forensic organizations and VAPT is made possible by Suma Soft.
Pros:
- Combined VAPT plus forensics
- Single-vendor testing and response
- Reasonable mid-market pricing
Cons:
- Broader IT services orientation
- Growing dedicated security practice
- Expanding advanced testing capabilities
20. Rhino Security Labs (Global Strategic Partner)
Trust Signals: AWS Security Competency Partner Original Cloud Research (Pacu)
Seattle, United States (serving Indian companies with worldwide cloud footprints)
Though based in the US, Rhino is listed since Indian security teams depend on the original AWS privilege escalation research it provides. Indian SaaS firms growing in the US market turn to them as their first choice since they need in-depth testing of sophisticated multi-account AWS environments, which regular local auditors often miss.
Ideal For: Indian cloud-native companies with US-based subsidiaries or sophisticated AWS EKS/Lambda deployments needing worldwide research-level depth.
Pros:
- AWS research-level cloud expertise
- Original Pacu tool creators
- Deep multi-account AWS security testing
Cons:
- US-based engagement pricing applies
- AWS-specialized focus primarily
- Remote delivery model for India
Quick Comparison Table for the Top 6 VAPT Testing Companies in India
Company | Engagement Model | Compliance Mastery | Best For |
QualySec | Human- Led AI Powered | DPDP, RBI, HIPAA, SOC2 | SaaS, Fintech & Startups |
KPMG India | Risk & Audit Advisory | RBI, SEBI, IRDAI | BFSI & Public Listed Corps |
PwC India | Enterprise Risk (ERM) | GDPR, SOX, DPDP | Large Scale MNC Operations |
EY India | Threat-Led Pentesting | SOC2, ISO 27001 | Digital Transformation Programs |
Deloitte India | Global Risk Consulting | HIPAA, SOX, Global Frameworks | Fortune 500 Subsidiaries |
Qualys | Automated / Cloud-Native | FedRAMP, PCI-DSS | Continuous Asset Discovery |
Did You Know? IBM’s 2025 Cost of a Data Breach Report found that Indian companies using AI-driven security automation shortened their breach lifecycle by more than 100 days and saved an average of 13 crore as opposed to those without it. Building that detection capacity depends on proactive security testing, including VAPT.
How We Evaluated These VAPT Service Providers: 7-Point Checklist
Marketing-led cybersecurity decisions cause compliance violations and neglected weaknesses. Here are some baseline suppliers against deliverables-oriented norms meant to differentiate expert penetration testing from automated scanning. Use this seven-point checklist to confirm any VAPT vendor’s technical depth and regulatory readiness.
- Verify CERT-In Empanelment. Verify at cert-in.org.in. This is a legal requirement for controlled sectors, not a taste.
- Demand a PoC report sample. A real penetration test consists of step-by-step reproduction paths and proof-of-concept exploit code. Should the sample report seem like a Qualys or Nessus scan export, you are paying penetration test rates for a vulnerability scan.
- Question the artificial intelligence/LLM. Do you look for the OWASP LLM Top 10? This distinguishes present suppliers from those using 2023 techniques by simulating paths for prompt injection attacks.
- Check the compliance report format compatibility. Demand examination of a sample report mapped to your own regulatory mandate—that of the RBI framework, IRDAI audit template, or PCI-DSS ROC. Often falling short, generic ISO 27001 documentation usually fails the severe inspection of industry-specific audits.
- Check the contract retest policy. Free retesting following remediation should be a contract deliverable rather than a tacked-on charge at typical day rates.
- Test the chronology’s sanity. Any provider offering a full VAPT on a mid-complexity program in less than five working days is providing automated scanning. Manual penetration testing of an actual application calls for at least seven to ten working days.
- Review connection to ticketing systems. Can results be immediately exported to JIRA, ServiceNow, or Azure Boards? Engineers in teams who are ready to integrate their work cut the typical time for remediation by 40%.
How Much Does India’s VAPT Cost?
India’s VAPT testing expense is the most often searched but least honestly answered query in this field. The whole 2026 breakdown is available here.
Engagement Type | Scope | Price Range (INR) | Duration |
Single Web App VAPT | 1 domain, up to 50 APIs | ₹25,000 – ₹75,000 | 5–10 days |
Mobile App VAPT | iOS or Android | ₹30,000 – ₹80,000 | 5–10 days |
API Security Testing | Up to 100 endpoints | ₹20,000 – ₹60,000 | 3–7 days |
Network VAPT | Up to 50 IPs | ₹40,000 – ₹1,20,000 | 7–14 days |
Cloud Configuration Review | Single account (AWS/Azure/GCP) | ₹50,000 – ₹2,00,000 | 7–14 days |
Full Enterprise VAPT | Web + Mobile + API + Network + Cloud | ₹2,00,000 – ₹15,00,000 | 3–8 weeks |
AI/LLM Security Assessment | LLM app, API, model endpoints | ₹75,000 – ₹3,00,000 | 7–14 days |
Red Team Engagement | Full adversarial simulation | ₹5,00,000 – ₹35,00,000 | 4–12 weeks |
Big Four VAPT | Enterprise + full compliance audit | ₹20,00,000+ | 6–16 weeks |
The Hidden Cost Most Neglects
A $50,000 VAPT that provides a scanner-generated PDF without corrective direction, compliance mapping, or retesting will run you more if you need a second supplier to understand the report, a third to address the problems, and a fourth to retest. Always assess ownership’s Full Cost: Is remedial help built into the cost? Re-examination at no charge? Deliverables tracked for compliance? Integration with your ticket system?
Avoid unexpected costs with a fixed-fee quote based on your actual assets. Request a custom pricing detail for your compliance and technical needs.
See our pricing, then talk with an expert to choose the best solution for your organization.
Explore Pricing
India Compliance & Regulatory Mandate Matrix 2026
Regulatory Body | Framework | Who Is Covered | VAPT Requirement | Penalty / Consequence |
DPDP Act 2023 | Data Protection by Design | All data fiduciaries processing Indian citizen data | Reasonable security safeguards (VAPT as primary evidence) | Up to ₹250 crore per violation |
RBI | Cyber Security & IT Framework | Banks, NBFCs, Payment Aggregators, Fintech | Annual VAPT minimum; continuous monitoring for critical systems | Licence review; regulatory action |
CERT-In | IT Act + 2022 Amendment | All significant digital infrastructure | CERT-In empanelled auditor mandatory; 6-hour breach reporting | Legal action under IT Act |
NPCI | Payment Security Standards | UPI, NACH, IMPS, BBPS participants | Continuous scanning; periodic VAPT | Suspension from payment network |
IRDAI | Cyber Security Guidelines 2023 | All licensed insurance companies | Annual VAPT mandatory | Licence suspension; financial penalties |
SEBI CSCRF | Cybersecurity & Cyber Resilience Framework 2024 | Stockbrokers, depositories, and MIIs | Annual VAPT; Red Team assessment for Tier-1 entities | Regulatory censure; fines |
Real Security Starts Where Compliance Ends
Audit tiredness is harming India’s cybersecurity environment. Many businesses purchase VAPT services only to satisfy a compliance box, therefore building a hazardous false sense of security. Modern security regulations call for a transition from passing the audit to real threat resilience.
Organisations must insist on exploitability engineering over automatic volume when assessing a VAPT provider in 2026. Actively assisting internal engineering teams, the ideal security partner should provide precise replication paths, weed out false positives, and map vulnerabilities right to corporate logic.
QualySec Expert Insights: The Reality Check
Following a zero high-risk findings automated scan, we manually VAPT’d a Series B fintech platform in Q1 2026.
The Blind Spot: Their automated system detected an API endpoint with an Insecure Direct Object Reference (Informational IDOR). It could not connect this with a misconfigured AWS IAM role, though.
The Manual Breakthrough:
- Chain: Our testers physically altered the API metadata in order to get a temporary security token.
- Development: That token exposed the IAM role given ListBucket permissions on an insecure S3 bucket.
- Within six hours, 2.1 million transaction records were given read access.
Buyers’ Lesson: The automatic scan revealed two low-risk spots. Our manual examination found the attack path connecting them. If your provider can’t demonstrate how personal shortcomings connect to a serious exploit, they are scanning you rather than doing a penetration test. This variation stops an excellent audit from becoming a major violation news story.
Watch how we discovered a 2.1 million record data leak that automated tools missed. Check out our client success stories.
Conclusion
The best VAPT testing company in India is the one with the approach that fits your actual attack surface in 2026, the report format that meets your particular regulator’s needs, and the engagement model that offers remediation support that turns discoveries into closed vulnerabilities, not the one with the most clients.
Using the intent clusters, pricing table, 7-point checklist, and artificial intelligence/LLM litmus test in this guide will help you to boldly shorten it. A real penetration test is like real security, which is different from a $50,000 vulnerability scan in the same way that real security is different from a certificate.
Schedule a meeting to discuss your security needs and get expert guidance.
Talk to our Cybersecurity Expert to discuss your specific needs and how we can help your business.
Schedule a CallFAQS
Q: What is VAPT testing?
VAPT is a mix of penetration testing, whereby a competent ethical hacker seeks to use those flaws to determine their possible real-world use, and vulnerability assessment, in which a computer program automatically hunts for bugs. Between their efforts, your auditors receive the compliance sign-off proof they need and a full picture of your security stance.
Q. Which is the best VAPT company in India?
Because of its human-led, artificial intelligence-powered approach, which offers more security insights than a typical automated scan, many consider QualySec to be the best.
Q. Who does VAPT testing?
Certified ethical hackers, dedicated cyber security companies, and CERT-In-empanelled auditors execute VAPT. These experts aggressively look for and exploit system flaws using a methodical combination of human-led hand methods and modern automated tools.
Q: What is VAPT’s present price environment in India for 2026?
One online app, VAPT, costs Rs. 25,000 to begin. Full corporate engagement ranges from Rs. 2 lakh to Rs. 15 lakh across web, mobile, API, cloud, and network. Training for red teams starts at Rs. 5 lakh. Projects starting at Rs. 20 lakh at the Big Four consulting level. Always look for free retesting availability.
Q: How often should a business conduct VAPT?
At least once a year, VAPT is needed; quarterly assessments for vital systems are required in the fintech and cloud-native industries. Following significant infrastructure modifications, software launches, or acquisitions, mandatory testing is used to get rid of security holes. Moreover, NPCI-governed institutions and RBI should precisely stick to their stated required testing frequency.
Q: What new threats should VAPT cover in 2026?
Three things are totally vital: penetration testing of artificial intelligence/LLM (OWASP LLM Top 10), CI/CD pipeline security testing (supply chain attack vectors), and deepfake social engineering simulation. Providers who neglect these are judging your 2026 infrastructure against a 2023 threat model.























































































































































































































































































































































































































































































































































































































0 Comments