Cybersecurity is the most important worry for every technology executive or business. Hackers are constantly looking for new ways to break into company systems. They scan all known vulnerabilities in business systems.
If your company has a weakness, they can quickly access your network. As a result, protecting your company from cyber threats has become critical. Nowadays, almost every business has a website. Websites, on the other hand, are more vulnerable to hacking. It is now vital to have a solid cybersecurity plan with expert “VAPT assessment.”
What is VAPT?
VAPT, also known as Vulnerability Assessment and Penetration Testing, is a comprehensive security testing method for finding and correcting cyber security flaws. VAPT delivers a detailed study to increase your organization’s cyber security by integrating vulnerability assessment and penetration testing.
In different places of the world, VAPT can refer to a variety of distinct services or a single, unified offering. However, VAPT might include everything from automated vulnerability assessments to human-led penetration testing and red team activities.
Vulnerability Assessment Vs. Penetration Testing: The Key Difference
| Vulnerability Assessment | Penetration Testing |
| It has a greater reach and keeps track of assets and resources in a specific system. | It concentrates on a specific vulnerability and determines the breadth or depth of an attack. |
| It identifies probable flaws in each resource. The purpose is to identify as many dangers as possible. | The aim here is to use the found threat to go to the base of the problem while also testing the sensitive data collected. |
| It is automated, less expensive, and faster. | It is rather expensive and entirely manual. It also needs highly specialized expertise and a longer time frame to accomplish. |
| It provides only a summary of the vulnerabilities and no recommendations for mitigating them. | It displays the complete scope of the exploited threat and ways to reduce the risk. |
| It is more appropriate for non-critical systems or lab conditions. | It is suited for real-time critical systems and physical network design. |
What are the Perks of Conducting VAPT Testing?
Here are the top ways VAPT services can help shield businesses from data breaches:
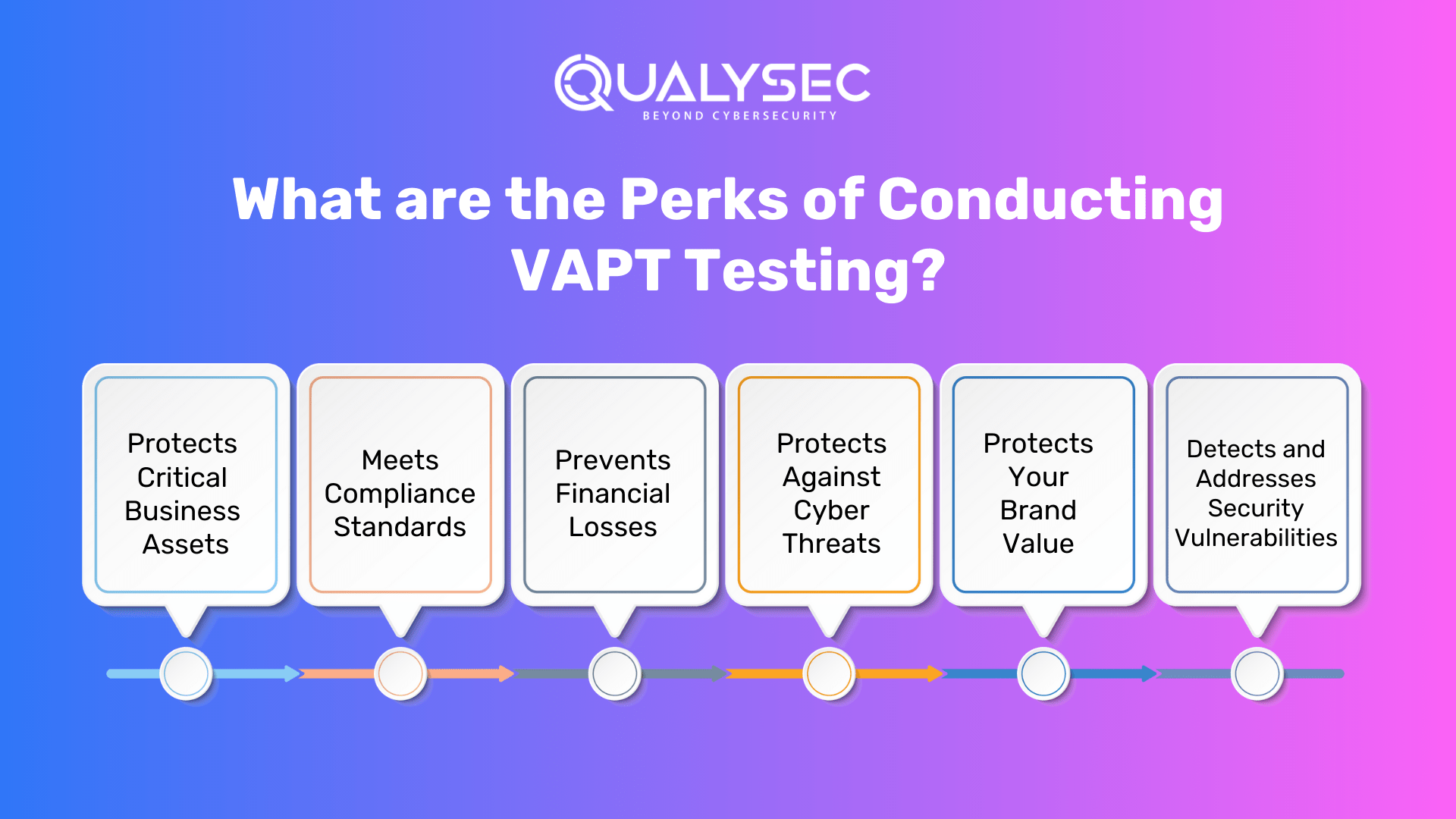
1. Protects Critical Business Assets
One of the key reasons organizations need VAPT is to protect vital assets. By conducting frequent “VAPT security testing,” businesses can identify security faults and vulnerabilities that could jeopardize their assets, such as intellectual property, financial data, and customer data.
2. Meets Compliance Standards
Businesses must follow unique data security and privacy laws established by various sectors and regulatory organizations. Furthermore, companies may benefit from VAPT’s support in ensuring that their IT infrastructure and security measures meet compliance requirements.
Learn more on Data Security Compliance.
3. Prevents Financial Losses
Cyberattacks and data breaches may result in massive financial losses for corporations. Furthermore, VAPT can aid firms in averting these losses by identifying vulnerabilities and implementing the appropriate security solutions.
4. Protects Against Cyber Threats
Businesses are continually worried about cyber threats, and VAPT may assist in giving protection. VAPT examinations can also help identify “vulnerable applications” that hackers may exploit to get unauthorized access to sensitive company data.
5. Protects Your Brand Value
Gives your industry regulators, consumers, and shareholders due diligence and compliance. Noncompliance can lead to your company losing customers, paying huge penalties, gaining negative press, or finally collapsing.
6. Detects and Addresses Security Vulnerabilities
VAPT is critical in discovering and addressing security vulnerabilities that bad hackers might exploit. Furthermore, businesses may discover gaps in their apps, networks, and systems by undertaking a thorough vulnerability assessment.
See how our penetration testing solutions protected businesses from real cyber threats. Read our case studies.
What Are the Different Penetration Testing Approaches?
Penetration testing differs in its technique as well as the holes it seeks to attack. However, the pen tester’s strategy and the project scope will be determined by the degree of information supplied to them. Among the several ways of penetration testing are:
1. Black Box
Black-box testing is a type of software testing that assesses an application’s functioning without delving into its underlying structures or workings. This test approach may be used at all levels of software testing, including unit, integration, system, and acceptance.
2. White Box
White box testing is a type of application testing in which the tester is given entire knowledge of the program under test, including access to source code and design papers. Because of this enhanced visibility, white box testing can detect flaws that gray and black box testing cannot.
3. Grey Box
Grey box testing, also known as gray box testing, is a software testing approach used to evaluate a software product or application with just a limited understanding of its underlying structure. The goal of grey box testing is to look for and detect faults caused by poor code structure or application use.
The Working Process of VAPT: A Guide
“VAPT testing companies in USA” often follow a standardized approach. Here’s a step-by-step guide for understanding the in-depth Vulnerability Assessment and Penetration Testing process.
1. Pre-Test Interaction
Before a penetration test, the testing team and the company must establish clear communication and collaboration. This also includes establishing the test’s scope, aims, and objectives and gaining the necessary authority to execute the test.
2. Reconnaissance
In the initial stage of VAPT, an attacker identifies tools to detect live hosts on a network. During this phase, it is critical to map all running devices and find active IP addresses that extend beyond the organization’s boundary.
3. Threat Modeling
During this step, testers examine the collected data to identify possible risks and rank them based on their likelihood and potential effect. This procedure enables testers to concentrate their attention on the most critical hazards.
4. Vulnerability Analysis
Testers use various tools and methodologies to scan the target environment for known vulnerabilities and security flaws. Furthermore, this step gives an in-depth look at any vulnerabilities that might be exploited during the test.
5. Exploitation
During this step, active attempts are made to exploit the discovered vulnerabilities in order to obtain unauthorized access, escalate privileges, or disrupt services. The purpose is to imitate real-world cyberattacks and see how the target environment responds.
6. Post-Exploitation
Following successful exploitation, testers assess the impact of the attack and collect further information to determine the scope of the breach. This might involve retrieving sensitive data or finding new weaknesses that can be exploited in future assaults.
7. Reporting
At the end of the process, the security testing team prepares a complete report summarizing the test findings, including exploited vulnerabilities, potential threats, and recommended repair procedures. This report is a helpful resource for the organization’s security posture improvement.
8. Retesting
Once the vulnerabilities have been addressed, businesses may decide whether to retest systems to check that the fixes were successful and to determine whether any new vulnerabilities were introduced as a result of the remediation.
Get a sample VAPT Report now!
Latest Penetration Testing Report

What are the Tools Used for VAPT?
There are several VAPT tools open source on the market. However, we have only included the greatest tools. The majority of these tools are solely used to scan your network. For the penetration testing process, you will still want the services of a competent, ethical hacker.
There will still be certain tools used for penetration testing. However, highly skilled experts who can effectively use PT tools are required. The following are some of the most effective VAPT tools:
- Nmap
- Metasploit
- BurpSuite
- Netsparker
- Wireshark
VAPT Security Testing Trends
Here are some of the emerging trends of VAPT in cybersecurity you should be aware of:
1. Internet of Things (IoT)
As the Internet of Things (IoT) expands, VAPT for IoT devices and networks becomes increasingly important. Keeping networked devices secure aids in the prevention of large-scale vulnerabilities.
2. Cloud Security Evaluations
With the cloud migration, enterprises must perform VAPT on their cloud infrastructure in order to detect and mitigate security risks associated with cloud-based services.
3. VAPT AI and Machine Learning
VAPT’s combination of AI and machine learning enables more advanced threat detection and automated vulnerability assessments, allowing enterprises to respond to new threats more effectively.
4. DevSecOps
It is extremely advantageous for testers since it uses the power of agile approaches to seamlessly include security tests into the development process. If your firm is hesitant to implement DevOps, it provides an opportunity to adapt and remodel.
How to Choose a VAPT Testing Companies?
When deciding on the finest cyber security VAPT provider for you, several variables must be considered. Consider the future, the present, the short term, and the long term. Most of the time, the finest provider for you is the one with whom you feel at ease and in whom you have faith.
However, there are additional considerations. Take your time in locating the ideal one for you. To make things easier, here are some considerations to ponder when selecting a VAPT solution.
- VAPT solution cost.
- Third-party VAPT provider experience.
- Employees who are professional and expert.
- Quality of the VAPT report.
How Can QualySec Aid Your Business With VAPT?
Qualysec is one of the top-rated “VAPT companies.” Our Vulnerability Assessment and Penetration Testing (VAPT) service is intended to assist you in identifying cyber security flaws in your infrastructure and developing a strategy to address them.
The VAPT scan performed by our expert penetration testers will be for the whole application as well as its underlying infrastructure, including all network devices, management systems, and other components. It’s a thorough examination that assists you in identifying security flaws so you can address them before a hacker can.
One of our primary assets is deep penetration testing skills, in which our specialists conduct extensive and sophisticated examinations to uncover weaknesses in a company’s digital infrastructure. These tests go beyond surface-level scans, digging deep into the system for flaws.
Our unwavering dedication to accuracy distinguishes us with an astounding zero-false positive report record. After rigorous testing, we give clients a thorough and informative report, accurately finding flaws and potential exploits.
We go above and beyond by partnering with developers to help them through the bug-fixing process, ensuring that reported vulnerabilities are resolved as soon as possible. Businesses obtain a cyber security certificate at project completion as a final stamp of security, establishing trust in our cybersecurity procedures and boosting their defenses against prospective threats.
Book a meeting with our cybersecurity specialists today to discuss your requirements.
Talk to our Cybersecurity Expert to discuss your specific needs and how we can help your business.
Conclusion
Companies are looking for innovative ways to safeguard their data as data breaches increase. The internet is brimming with information on how businesses can safeguard their data. To protect their data, organizations of all sizes must have an appropriate VAPT solution.
We’ve spoken about the necessity of a VAPT solution and how it may help defend your business against malicious assaults in our blog article. The best thing is that it is reasonably priced for all enterprises.
Take a look at Qualysec’s ratings and reviews on Clutch to see how we help businesses secure their data. Book a free live consultation to learn more.
FAQs:
1. What is the significance of vulnerability assessment in cybersecurity?
A vulnerability assessment investigates the security weaknesses of an information system carefully. It assesses whether the system is vulnerable to any known vulnerabilities, assigns severity ratings to those vulnerabilities, and recommends appropriate remediation or mitigation.
2. What are the three cybersecurity objectives?
The CIA triad is supported by confidentiality, integrity, and availability. Also, People, Processes, and Technology work together to achieve these cybersecurity goals and maintain successful security systems.
3. What are the five common vulnerabilities found?
Numerous vulnerabilities are found while testing an application or website. However, the most common are unauthorized access, credential theft, unpatched software, misconfiguration, and remote code execution. Businesses need to look mainly over these while securing their apps and APIs.
4. What is the most recent vulnerability in 2023?
CVE-2023-27350 is the top vulnerability for 2023, representing the most severe danger of the year. The QDS for this CVE is 100, and the severity score is 9.8. It also affects the widely used print management software PaperCut and offers an immediate and severe danger to network security in many enterprises.
5. What is cybersecurity phishing?
Phishing is the technique of delivering false communications that appear to be from a valid and trustworthy source, typically by email and text messaging. The attacker aims to steal money, get sensitive data and login credentials, or implant malware on the victim’s device.



















































































































































































































































































































































































































































































































































































































































































































0 Comments