© 2024 Qualysec.com Disclaimer Privacy Policy Terms & Conditions

In 2004, the payment card industry’s titans (VISA, Master Card, American Express, JCB International, and Discover Financial) banded together to establish a security standard to safeguard the data integrity of user card information. This paved the way for what we now know as the PCI-DSS compliance framework. Pentesting is ethical hacking that involves simulating a network and its target systems. PCI DSS Penetration testing is more than just running an automated vulnerability scanner; security specialists conduct tests and dig deep into the system.
PCI DSS penetration testing for your security networks, public devices, apps, databases, and other structures that store, process, or distribute cardholder data entails attempting to uncover flaws before attackers do. In this blog, we’ll cover all about PCI DSS compliance, why it is required, PCI DSS pentesting, its requirements, and strategies. We’ll also look into how to choose a service provider, so keep reading.
“The Payment Card Industry Data Security Standard (PCI DSS) is an international proprietary information security standard created by the PCI Security Standards Council for organizations that handle cardholder data for the world’s largest card schemes, including American Express, Discover, JCB, MasterCard, and Visa.”
Companies must be PCI DSS compliant to take credit card payments over the phone, in person, or online. PCI DSS secures all the information on a customer’s payment card, including the primary account number (PAN), cardholder name, credit card expiration date, and service code.
While not legally compulsory, Companies must comply with PCI DSS as part of their contractual commitments to card issuers and financial institutions, including banks. Failure to comply has serious consequences: banks might permanently terminate their partnership with an organization and add offenders to the Merchant Alert to Control High-Risk (MATCH) list, preventing them from ever processing card payments again.
Note: Noncompliance with PCI DSS can result in fines of up to $100,000 monthly and additional transaction costs. You won’t want that, do you?
If you’re a business that wants to comply with the PCI DSS framework and needs to know how to do so, Here’s a legitimate solution: PCI DSS penetration testing service. Schedule a call for FREE to learn more.
The Purpose of PCI DSS Compliance
The fundamental purpose of PCI DSS is to protect and improve the security of sensitive cardholder data, such as credit card numbers, expiration dates, and security codes. The standard’s security measures assist organizations in reducing the risk of data breaches, fraud, and identity theft.F
Compliance with PCI DSS also assures that firms use industry best practices when processing, storing, and transferring credit card information. As a result, PCI DSS compliance builds confidence among consumers and stakeholders.
PCI DSS Penetration testing is the practice of identifying security flaws in an application that is in development. It is fundamentally about detecting and fixing security issues in apps. Data security is an ever-changing landscape.
There are new hazards to consider, new laws to follow, new testing items, and new technology to understand. It’s hardly surprising that security staff might feel overwhelmed. While a penetration test cannot replace a full-scale audit, it may assist a company in assessing the security of its apps or websites and identifying possible risks and concerns.
PCI compliance standards, such as the DSS, assist in reducing risks to sensitive card payment data, such as cardholder data (CHD) and sensitive authentication data (SAD). Furthermore, PCI DSS compliance contains recommended practices that firms may use to safeguard card payments and their overall IT infrastructure, reducing the risk of cyberattacks.
The PCI DSS compliance procedure involves:
Partnering with an experienced PCI DSS framework compliance specialist and managed security services provider (MSSP) will assist your firm in achieving and implementing these components.
We at Qualysec offer the best comprehensive pentest report that can guarantee you PCI DSS compliance. Click here to download our sample report!
Is Penetration Testing Required for PCI DSS?
Yes, PCI DSS requires penetration testing twice a year – or whenever a big change happens in your environment.
Before we go any further, there is some complexity to this. Your application encompasses any aspect of your company that processes credit card information.
“What is important to one firm may not be significant to another. However, in general, OS updates, the replacement of firewalls or important security devices, the implementation of a new payment acceptance method, and the migration of sections or the entire environment to a cloud-hosted environment would all be considered substantial changes.”
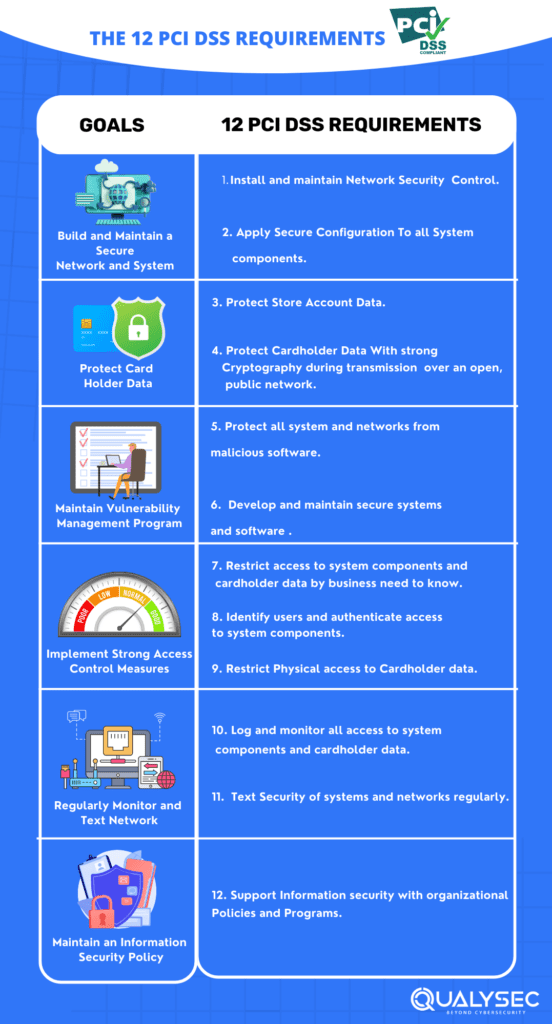
The 12 PCI DSS standards correspond to 6 fundamental concepts of PCI DSS compliance, which are:
If these prerequisites are satisfied, the cardholder data environment and services within scope are PCI compliant.
The PCI DSS criteria increase the cardholder data environment (CDE) and a company’s overall security posture. Here are the 12 PCI DSS requirements you should know about:
Often, network devices and equipment are pre-configured with default passwords and settings. Most network devices’ default passwords and settings are commonly known, making it easy for hackers to access them. The PCI DSS mandates enterprises to avoid default passwords and update them before deploying a system on their network.
Today, many transactions take place remotely via the Internet and e-commerce. Without sufficient security, unauthorized people can get access to payment system networks. Furthermore, firewalls manage network traffic and prevent unwanted access to data, ensuring that cardholder data is only exchanged with trusted connections.
To meet this requirement, firms must install and configure firewalls and develop rules governing what types of traffic are permitted on the network. Requirement 1 also requires enterprises to evaluate configuration rules every six months, which include extra network security restrictions.
This criterion specifies what procedures firms must take to secure cardholder data, whether printed, kept locally, or in a database. Cardholder data can include any information on a credit card, such as PINs, PAN data, and sensitive authentication data. The PCI DSS specifies what you can and cannot store following authorization of cardholder data.
The regulation also states that firms should only keep card data required to satisfy their business purposes. Any data you save should be secured with industry-standard encryption methods such as AES-256-bit encryption.
This rule is designed to secure cardholder data while sending it over open public networks such as the Internet. When cardholder data must be transferred over open public networks, firms should employ robust encryption technology to protect it from illegal access. The PCI DSS also stipulates that enterprises should never send unprotected PAN over end-user messaging, such as email, instant message, SMS, or chat.
Malicious software (malware) can infiltrate a network via email, social engineering, malicious file installation, or other online actions. Furthermore, anti-virus software must be installed and updated regularly to safeguard cardholder data from such attacks. This criterion details the particular procedures enterprises must take to safeguard against malware, including:
This requirement ensures you have a mechanism to manage the software within your CDE. This criterion applies to all in-scope apps in your environment. PCI DSS also mandates firms to deploy security fixes on time to secure cardholder data. The criterion also includes controls for software development best practices that avoid vulnerabilities.
The PCI DSS also requires firms to issue a unique ID to each employee with access to system components. This enables the company to track which people accessed different parts of cardholder data or linked systems in the case of a data breach. This need also necessitates multi-factor authentication and password encryption to better secure user accounts.
This criterion aims to restrict physical access to cardholder data or systems that affect cardholder data to workers who require access to the systems to fulfill their duties. The PCI DSS requires firms to properly differentiate on-site staff from visitors, such as using ID badges. This requirement further specifies what efforts firms must take to safeguard media, which includes any paper or electronic medium containing cardholder data. This involves storing media backups in a secure, off-site place and discarding material no longer required.
Access controls enable a company to establish which users have permission to access cardholder data or systems that may affect cardholder data. As a general rule, PCI DSS recommends that authorization be issued on a need-to-know basis. Furthermore, according to this requirement, a company should limit access to cardholder data to workers who require it to execute their duties.
This requirement focuses on creating logs and being able to trace actions back to a specific account. This allows a firm to rapidly determine the source of a malicious request or attack. Furthermore, businesses must build automatic audit trails that monitor certain occurrences and deliver notifications to employees for daily inspection. Businesses must also protect audit trails so that they cannot be manipulated.
This requirement aims to ensure the continued security of internal and external systems through frequent testing. These assessments also include quarterly network vulnerability checks and an annual penetration test. Network intrusion detection or prevention methods must also be used to detect or prevent network intrusions.
The last criterion of PCI DSS is for firms to develop and maintain an information security policy that influences security practices throughout the company. This criterion compels businesses to:
PCI DSS penetration testing is critical to attaining PCI DSS compliance because it assists firms in identifying and addressing security vulnerabilities in their internal and external networks and systems.
The penetration testing technique extends beyond vulnerability scanning, which identifies possible security flaws by actively attacking security mechanisms to get beyond them. Furthermore, to guarantee impartiality and technical knowledge, the penetration tester should be an external resource not involved in developing or managing the cardholder data environment’s systems.
Regular penetration examinations offer various benefits to organizations:
PCI DSS penetration testing strategies are designed to assist you in better safeguarding your data from potential assaults. The following recommendations can be used more holistically to maintain adaption approaches together. These strategies are essential components of the PCI Data Security Standards.
Defining your organization’s PCI DSS scope entails identifying the people, procedures, and technology that influence or may affect cardholder data security. These elements are under the scope of PCI DSS and are subject to its criteria. Furthermore, network devices, servers, programs, and workstations are all system components that may be relevant to your surroundings.
One of the most effective ways to assist your organization in achieving PCI compliance is to avoid storing sensitive data. Consider if information has to be saved at each step in the cycle while analyzing the systems as part of the PCI. Choose a system that does not need you to maintain data in real-time after clients have been charged.
The amount of effort required to guarantee PCI DSS compliance varies depending on the breadth of the PCI DSS. PCI applies solely to your company’s servers, network devices, and apps that handle, store, or send cardholder data. Furthermore, using this program reduces the breadth of your PCI processes. It also implies you’ll spend less time and money achieving PCI compliance through network segmentation.
Compliance with PCI DSS also serves as a solid basis for an enterprise security strategy, allowing you to find methods to improve the overall efficiency of your client’s IT infrastructures. Choose a supplier who fulfills PCI compliance criteria to guarantee that your and your customer’s data is properly addressed and safeguarded from possible breaches.
To achieve PCI DSS compliance, run distinct security checks in your environment. Network vulnerability scanning and penetration testing are all necessary tests. Furthermore, network vulnerability and penetration testing can be performed utilizing 3rd-party resources. If you utilize 3rd-party resources, ensure they know security testing methods and are not directly engaged in the overall PCI DSS evaluation.
PCI DSS compliance offers both advantages and disadvantages.
Compliance with PCI DSS provides several benefits to firms regarding data protection and improving their reputation as security-conscious enterprises. Benefits include the following:
PCI DSS compliance also presents issues for enterprises, including the following:
It is recommended that businesses should conduct PCI DSS penetration testing from a 3rd-party service provider. These providers can help you in many ways to comply with PCI DSS, but here are a few things to consider when choosing the service provider:
While certifications are not necessarily required, they demonstrate the expertise level and competency of a vendor’s penetration testing team. One of the most prevalent penetration testing credentials is Certified Ethical Hacker (CEH).
With penetration testers who are specialists in their industry, cooperating to repair vulnerabilities is simple. There are many service providers on the market, but you must ensure that they are experienced in offering this service to you.
Before hiring a service provider, look into their reputation and reviews. Look into their prior work and speak with previous or current clientele.
Ensure the organization does continuous scans to ensure that any vulnerabilities introduced by new features or updates are discovered as soon as possible. Continuous scanning is also necessary to ensure compliance with regulatory requirements such as PCI-DSS and HIPAA.
Certifications cannot replace the skills and knowledge obtained through years of experience. As a result, an organization must conduct due diligence to determine whether a prospective vendor has past expertise. Furthermore, it may be beneficial to determine whether a vendor has previously dealt with a company in your market area.
Qualysec distinguishes itself as a leading process-based penetration testing provider, assisting organizations in achieving PCI DSS penetration testing strategies with exceptional competence. As a reputable third-party supplier, we provide comprehensive penetration testing services, including careful evaluations that adhere to industry norms and laws. Our services include:
Qualysec specializes in creating extensive penetration test reports, ensuring that firms are prepared to satisfy compliance regulations such as PCI DSS, HIPAA, SOC 2, ISO 27001, and GDPR. With a particular focus on security, we use hybrid approaches to find vulnerabilities, analyze risks, and strengthen your enterprises’ security postures.
Our success is in our dedication to providing actionable insights beyond basic compliance. Businesses can have a strategic edge in securing sensitive data and consumer information and building a strong security environment with our expertise and experience. Whether dealing with the complexity of PCI DSS or other regulatory frameworks, our penetration testing findings provide a road map for improving security measures and guaranteeing continuing compliance.
In an era where cyber threats are constantly evolving, Qualysec’s expertise as a penetration testing leader has become a cornerstone for organizations seeking compliance and resilience in the face of an ever-changing threat environment.
Fill out this form to get in-depth insights on PCI DSS penetration testing.
Penetration testing is best to defend your organization from cybercriminals and hackers. A hacking effort might have disastrous consequences for your company’s reputation. A good penetration test can assist you in identifying and addressing these vulnerabilities before others do.
You’ve worked hard to create your firm and safeguard your clients, so don’t let a blunder result in significant financial losses or public disgrace. If you need assistance with PCI DSS penetration testing strategies, contact us.
PCI DSS (Payment Card Industry Data Security Standard) applies to enterprises that manage cardholder data. It defines security standards for securing sensitive payment information during processing, storage, and transfer to avoid data breaches and ensure secure payment transactions.
PCI DSS applies to any entity that processes, stores, or transmits payment card data. This comprises retailers, financial institutions, and service providers who handle credit and debit card transactions.
Vulnerability scanning, penetration testing, and self-assessment questionnaires are used to evaluate PCI DSS criteria. These approaches assist in identifying and addressing security weaknesses, hence assuring standard compliance.
PCI DSS is essential to safeguard sensitive payment card information and prevent data breaches. Compliance promotes client trust, lowers the risk of financial losses, and maintains a safe environment for processing electronic transactions, all contributing to the payment card industry’s integrity.
The official PCI compliance standards declare unequivocally that PCI DSS compliance is not required; rather, it is a way to assure that your company can handle card transactions without paying high transaction rates to banking institutions and payment industry giants.
PCI DSS compliance levels are categories that specify the level of compliance standards that a business must adopt to become PCI DSS compliant. Furthermore, these levels are determined by the number of transactions, the nature of the risk, and the organization’s previous experience with security breaches.





Plot No:687, Near Basudev Wood Road,
Saheed Nagar, Odisha, India, 751007
No: 72, OJone India, Service Rd, LRDE Layout, Doddanekundi, India,560037
© 2024 Qualysec.com Disclaimer Privacy Policy Terms & Conditions


No: 72, OJone India, Service Rd, LRDE Layout, Doddanekundi, India,560037
© 2024 Qualysec.com Disclaimer Privacy Policy Terms & Conditions