Cyber threats are here to stay; no longer a far-fetched risk, it is an everyday occurrence in businesses of all sizes in the USA. With ransomware closing hospitals and machine-learning phishing attacks on financial institutions, attackers are changing more quickly than ever.
As per the IBM Cost of a Data Breach Report 2025, the average cost of a data breach has soared to USD 4.45 million. Meanwhile, MarketsandMarkets projects the global cybersecurity market will reach USD 351.92 billion by 2030. In the USA alone, cybersecurity remains a top priority as U.S.-based businesses account for a significant share of this growth, driven by innovations in technology and an escalating number of attacks targeting enterprises across sectors.
This guide offers a research-based list of the best cybersecurity companies in the USA to enable you to compare vendors in terms of their strengths, applications, and practicality in the real world.
Compared: Top Cyber Security Companies in USA (2026)
The selection of several cyber security firms in the USA may be difficult. This comparison table gives a brief insight into the best vendors on their core competencies, and it becomes simpler to find the right cyber security firms that fits well in your business requirements.
| Company | Best For | Core Strength | Ideal For |
| QualySec | Penetration Testing | Hybrid pentesting + compliance focus | Startups, SaaS, compliance-driven orgs |
| Palo Alto Networks | Enterprise Security | Zero Trust + platform security | Large enterprises |
| Microsoft | Cloud + Identity | Integrated ecosystem security | Microsoft-based enterprises |
| CrowdStrike | Endpoint Security | AI-driven EDR | Advanced threat protection |
| Zscaler | Cloud Security | Zero Trust SASE | Remote/cloud-first orgs |
| Okta | Identity Security | IAM + MFA | Identity-focused security |
| Fortinet | Network Security | High-performance firewalls | Infra-heavy enterprises |
| Rapid7 | Vulnerability + SIEM | Risk prioritization | Mid-size enterprises |
| Tenable | Vulnerability Mgmt | Exposure visibility | Risk-focused teams |
| HackerOne | Bug Bounty | Crowdsourced testing | Tech companies |
Download our 2026 Sample Penetration Testing Report.
Top Cyber Security Companies in USA (2026 Detailed Analysis)
The list of cyber security companies in the USA provided below is selected according to innovation, depth of services, compliance and real-life effectiveness. Every company will be a strength with its own focus on penetration testing and vulnerability management to cloud security, identity protection and AI-powered threat detection.
1. QualySec
Ranked among the best cybersecurity companies in the USA, Qualysec Technologies stands out as a leader in Human-led AI Penetration Testing. This methodology integrates expert-led validation with AI-driven performance and automated coverage. The model assists organizations to detect more fundamental security vulnerabilities, such as business-logic errors and backdoor attack paths that might not be revealed during traditional testing.
Core Services:
Penetration testing for Web, Mobile, API, Cloud, IoT, and AI/ML systems; Source Code Review; and Secure SDLC consulting.
Compliance Focus:
Specialized in making organizations audit-ready for HIPAA, PCI DSS, GDPR, SOC 2, ISO 27001 and FDA.
Strategic Advantage:
The Human-led AI Penetration Testing approach by QualySec increases the level of testing and the speed. Thus, ensures the required attention that is needed to justify the actual risk assessments at the human expertise level. This makes it especially usable in those companies that need technical trust and must adhere to strict global security standards.
Global Impact:
- More than 350 + clients all around the world, both startups and regulated businesses.
- More than 40+ countries served in the fields of healthcare, finance, IT, e-commerce, and government.
- Over 2000 assets are covered by end-to-end penetration testing and consulting.
- 30+ Global partners strengthening cyber resilience in industries.
Need a security assessment? Book a free consultation with our experts to evaluate the right partner for your business.
Talk to our Cybersecurity Expert to discuss your specific needs and how we can help your business.
2. Palo Alto Networks
Best for: Platform Security and Enterprise Zero Trust.
Palo Alto Networks is a leader in cloud-native security solutions and zero-trust frameworks. Their Prisma Cloud secures workloads, while Cortex delivers AI-driven threat detection. Known for next-gen firewalls and serving over 85 Fortune 500 companies, they provide robust network and endpoint protection.
Core Capabilities:
- Next-generation firewalls
- Cloud workload security
- Threat detection and response based on AI.
- Zero Trust Network Access
Strategic Advantage: An integrated platform that lowers the dispersal of security tools.
3. McAfee
Best for: Endpoint and Identity Protection.
McAfee excels in network security, antivirus solutions, and identity theft protection. Its standout product, McAfee Total Protection, provides real-time safeguards against over 22,250 threats detected every minute. Suitable for businesses and individuals, McAfee offers reliability and scalability.
Core Capabilities:
- Antivirus and endpoint protection.
- Identity theft protection
- Data loss prevention
- Threat intelligence
Strategic Advantage: It is popularly used by both enterprises and individuals.
4. Microsoft
Best for: Integrated Enterprise and Cloud Security
Microsoft integrates cutting-edge innovations through its enhanced Microsoft Defender and RiskIQ for comprehensive threat detection. Renowned for its developments in cloud security and endpoint protection, Microsoft serves as a pivotal player in the cybersecurity landscape.
Core Capabilities:
- Microsoft Defender suite
- Azure Security Center
- Microsoft Sentinel (SIEM)
- Entra ID (identity security)
Strategic Advantage: Intimate connection with the enterprise infrastructure and powerful AI-based threat-detection.
5. CrowdStrike
Best for: AI-Driven Endpoint Detection and Response.
CrowdStrike is known for its Falcon platform, which excels in endpoint detection and ransomware blocking. Recognized for proactive defense strategies in MITRE MSSP evaluations, CrowdStrike remains a trusted partner for securing critical assets against advanced threats.
Core Capabilities:
- Endpoint detection and response (EDR).
- Managed detection and response (MDR).
- Threat intelligence
- Cloud workload protection
Strategic Advantage: Does an excellent job of preventing ransomware and advanced threats prior to execution.
6. Deepwatch
Best for: Managed Detection and Response (MDR)
Deepwatch delivers continuous threat monitoring and bespoke cybersecurity operations. By creating customized teams for each client, they ensure high-touch, tailored approaches to evolving security needs, making them a preferred partner for specialized organizations.
Core Capabilities:
- Threat monitoring continuously.
- SIEM management
- Threat hunting
- Incident response
Strategic Advantage: “Squad model” guarantees personalized security operations.
7. Rapid7
Best for: Vulnerability Management and Security Operations
Rapid7 simplifies compliance and risk management with contextual threat analysis and unified visibility. Their solutions cover mobile, cloud, and on-premise infrastructures, helping businesses streamline their security operations.
Core Capabilities:
- InsightVM (vulnerability management)
- InsightIDR (SIEM and analytics)
- Security automation processes.
- Penetration testing
Strategic Advantage: Priority in decision-making is facilitated by contextual risk prioritization.
8. knowBe4
Best for: Human Risk and Security Awareness.
KnowBe4 focuses on enhancing human-centric security through phishing simulation and employee training. Their innovative solutions help businesses reduce risks related to social engineering attacks and foster a culture of cyber awareness.
Core Capabilities:
- Phishing simulations
- Awareness training on security.
- Artificial intelligence-based behavioral coaching.
- Compliance training
Strategic Advantage: Enhances the human aspect of cybersecurity.
9. Zscaler

Best for: Cloud Security and SASE.
Zscaler is a pioneer in cloud-first Secure Access Service Edge (SASE) solutions. Their services support digital transformation with streamlined, scalable, and secure solutions tailored to enterprise environments.
Core Capabilities:
- Secure web gateway
- Cloud access security broker (CASB).
- Data loss prevention
- Threat intelligence
Strategic Advantage: Ridley does not use old-fashioned VPNs.
10. Ping Identity
Best for: Identity and Access Management
Ping Identity specializes in advanced Single Sign-On (SSO), multi-factor authentication, and AI-powered threat detection. Their solutions are trusted for secure, seamless access management across modern enterprises.
Core Capabilities:
- Single sign-on (SSO)
- Multi-factor authentication (MFA).
- Identity governance
- Zero Trust integration
Strategic Advantage: Strikes the right balance between user experience and high security.
11. Duo Security
Best for: Authentication and Zero Trust Access.
Duo Security, a leader in two-factor authentication (2FA), is celebrated for securing seamless and reliable user access. Their approach fortifies endpoint protection, making security accessible and user-friendly.
Core Capabilities:
- Multi-factor authentication
- Device visibility
- Adaptive access policies
- Compliance support
Strategic Advantage: Easy and scalable identity protection.
12. Fortinet
Best for: Network security and Firewalls
Fortinet is renowned for FortiGate Firewalls and expanded offerings in intrusion prevention and endpoint security. Their innovative solutions span from on-premise environments to edge infrastructures.
Core Capabilities:
- FortiGate firewalls
- Secure SD-WAN
- SIEM and analytics
- Zero Trust access
Strategic Advantage: Scalability and high performance.
13. Cisco
Best for: Network and Infrastructure Security
With a legacy dating back to the 1980s, Cisco has established itself as an industry leader in DDoS protection and robust firewalls. Excelling in hybrid and multi-cloud environments, they continue to redefine cybersecurity frontiers.
Core Capabilities:
- Cisco SecureX platform
- SASE architecture
- DNS-layer security
- Talos threat intelligence
Strategic Advantage: Worldwide perspective of the threat environment.
14. Trend Micro

Best for: Cloud and XDR Security
Trend Micro protects over 500,000 organizations worldwide. With specialized solutions for cloud, endpoint, and IoT security, they remain a global frontrunner in detecting and preventing threats across industries.
Core Capabilities:
- XDR platform (Vision One)
- Cloud workload security
- Email and IoT protection
- Data loss prevention
Strategic Advantage: Threat intelligence with a high level of research.
15. Okta
Best for: Identity and Access Management (IAM)
Okta offers comprehensive identity and access management tools, enabling secure integration with modern applications. Their API-driven services provide flexibility and security for evolving enterprise needs.
Core Capabilities:
- Single sign-on (SSO)
- Multi-factor authentication (MFA).
- The lifecycle of identity management.
- Data, privileged access.
Strategic Advantage: API-driven architecture, which is very flexible and easy to integrate with contemporary applications.
16. OneTrust
Best for: Privacy, Compliance, and Data Governance.
OneTrust leads in privacy, compliance, and governance software, assisting organizations in navigating emerging regulations. Their automated tools simplify data protection and regulatory adherence.
Core Capabilities:
- Management, privacy and compliance.
- Information management and risk evaluation.
- Third-party risk monitoring
- Regulatory standards (GDPR, HIPAA, CCPA).
Strategic Advantage: Assists organizations in making compliance operational instead of a check.
17. Proofpoint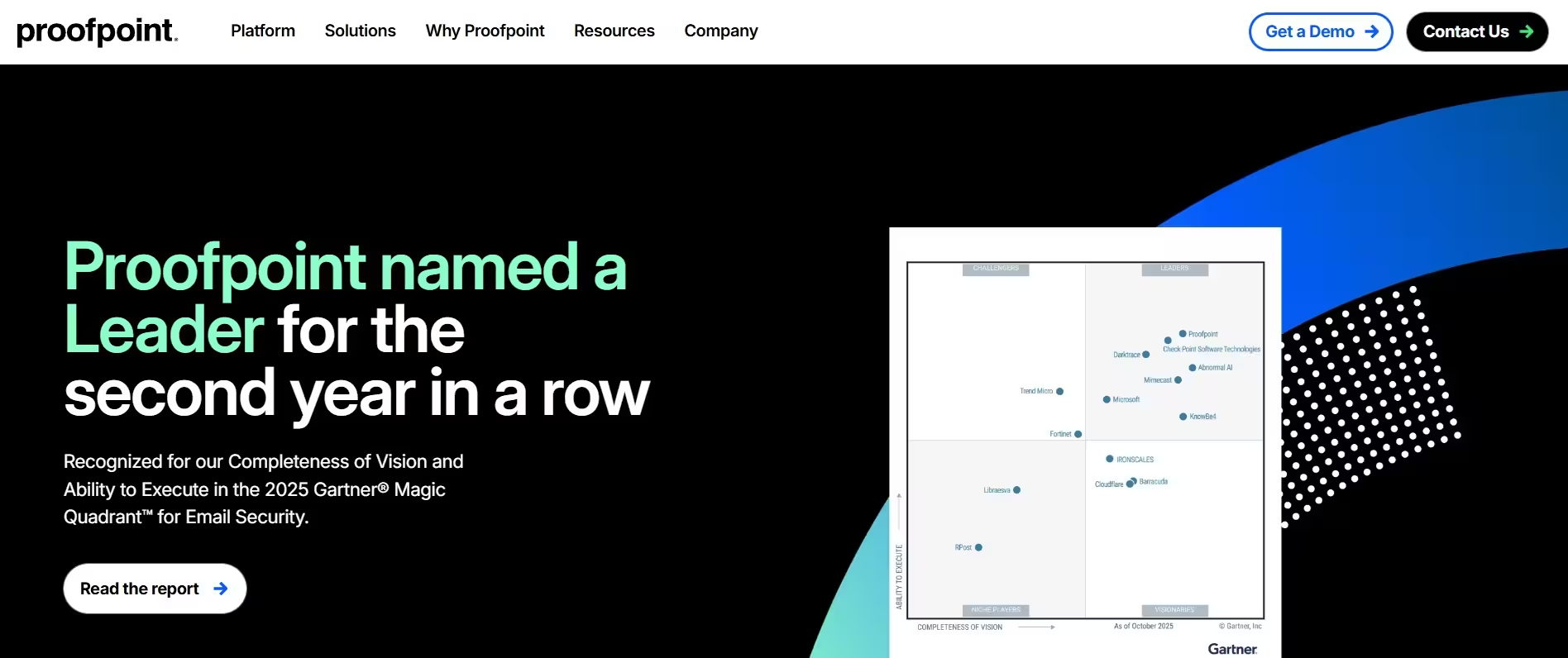
Best for: Email Security and Human-Centric Threat Protection
Proofpoint delivers industry-leading email security, phishing protection, and compliance solutions. Designed for SaaS environments, their products are tailored to safeguard businesses from evolving cyber threats.
Core Capabilities:
- E-mail protection and anti-scam.
- Threat intelligence
- Data loss prevention
- Awareness training on security.
Strategic Advantage: Excellent prevention of phishing attacks and social engineering attacks.
18. Tenable
Best for: Vulnerability and Exposure Management
Tenable’s cloud-based solutions are anchored by Nessus technology, providing top-tier vulnerability management. Their insights ensure businesses stay ahead of risks in diverse environments.
Core Capabilities:
- Vulnerability scanning
- Exposure analytics
- Compliance monitoring
- Cloud security assessments
Strategic Advantage: Gives profound insight into weaknesses within the IT, cloud, and OT landscape.
19. Check Point
Best for: Sophisticated Threat Prevention
Check Point excels in multi-layered threat prevention with advanced data security solutions. Operating in over 70 countries, they are trusted by enterprises for robust defense against modern threats.
Core Capabilities:
- Next-generation firewalls
- Sandboxing and threat prevention.
- Cloud security (CloudGuard)
- Endpoint protection
Strategic Advantage: Well-developed prevention-first solution to advanced cyber threats.
20. Trellix
Best for: Extended Detection and Response (XDR)
Trellix, formed from the merger of FireEye and McAfee Enterprise, offers exceptional XDR platforms combining detection and response. Their unified approach effectively combats dynamic cyber challenges.
Core Capabilities:
- XDR platform
- Network and endpoint security.
- Integration of threat intelligence.
- Automated response
Strategic Advantage: Integrated environment for detection, analysis, and response.
21. RSA Security
Best for: Identity Security and Fraud Prevention.
RSA Security is synonymous with robust encryption and identity protection. Their signature product, SecurID, provides an essential toolset for enterprises prioritizing secure access and risk management.
Core Capabilities:
- Multi-factor authentication
- Identity governance
- Fraud detection
- Risk-based authentication
Strategic Advantage: Excellent banking and financial services.
22. HackerOne
Best for: Bug Bounty Programs and Ethical Hacking
HackerOne stands out for its ethical hacking and bug bounty programs, having distributed over $230M in rewards globally. Their solutions identify vulnerabilities and foster proactive security cultures.
Core Capabilities:
- Bug bounty programs
- Disclosure programmes on vulnerability
- Intrusion testing
- Service Penetration Testing
Strategic Advantage: There is access to a worldwide pool of white hat hackers to discover a vulnerability more quickly.
23. Imperva
Best for: API and Application Security
Imperva specializes in API and web application protection. They combine automated responses with comprehensive threat analysis to deliver proactive, effective security for critical platforms.
Core Capabilities:
- Web application firewall (WAF).
- API security
- DDoS protection
- Bot management
- Database security
Strategic Advantage: Excellent security of applications which consume large amounts of data or customer-facing applications.
24. Darktrace
Best for: AI-Driven Threat Detection
Darktrace leverages AI to detect anomalies and predict threats with unparalleled precision. Their self-healing technology ensures robust security across data ecosystems with minimal manual intervention.
Core Capabilities:
- AI-based threat detection
- Independent reaction (Autogenous)
- Behavioral analytics
- Cloud and SaaS protection
Strategic Advantage: Anomaly-based detection of threats through anomaly detection.
25. Cybereason
Best for: Endpoint and XDR Security
Cybereason integrates signature-based detection with behavioral analytics to counter advanced persistent threats. Their proactive stance secures digital assets while adapting to sophisticated attack vectors.
Core Capabilities:
- Endpoint detection and response (EDR).
- Extended detection and response (XDR)
- Threat intelligence
- Incident response
Strategic Advantage: Well-developed emphasis on identifying the work of advanced persistent threats (APTs).
Ready to find vulnerabilities before attackers do? Request a free quote now!
Best Cyber Security Companies by Use Case
1. Best for Startups and SaaS Companies
- QualySec
- HackerOne
- Rapid7
Why: Low cost, flexible and application security oriented.
2. Best for Enterprises and Large Organizations
- Palo Alto Networks
- Microsoft
- Cisco
Why: Global threat intelligence, scalable platforms and enterprise-grade security.
3. Best for Cloud-First Businesses
- Zscaler
- Trend Micro
- Microsoft
Why: CN security and Zero Trust architecture.
4. Best for Identity and Access Management
- Okta
- Ping Identity
- Duo Security
Why: Identity has become the new main attack surface in contemporary security.
5. Best for Threat Detection and Response
- CrowdStrike
- Darktrace
- Cybereason
Why: High-tech AI-based detection and real-time response.
6. Best for Compliance and Risk Management
- QualySec
- OneTrust
- Tenable
Why: Good compliance with regulatory frameworks and readiness to audit.
Expert Insight
The majority of businesses that seek the services of cyber security companies in the USA do not find one vendor. They are instead attempting to create a security stack.
An average contemporary installation consists of:
- A single provider of platforms (Microsoft or Palo Alto)
- A single detection solution (CrowdStrike or Darktrace).
- A single researcher (QualySec or HackerOne).
This multidimensional approach makes it more resilient and less susceptible to single-point failure.
Types of Cyber Security Companies in USA
The services provided by not every cyber security company in the USA are the same. The cybersecurity environment is highly niche as various vendors specialize in certain fields of protection. With this knowledge of these categories, you will select the appropriate cyber security company in the USA depending on the security requirements of your organization.
The key categories of cyber security firms that are active in the U.S. market include:
1. Endpoint Security Companies
These corporations specialize in securing their devices, including laptops, servers, and mobile systems, against malware, ransomware, and unauthorized access. They apply high-tech detection solutions such as EDR and XDR to respond to and track threats in real time.
Best for: Companies that require securing employee devices as well as averting endpoint-based assaults.
2. Cloud Security Providers
Cloud security vendors focus on securing the cloud infrastructure, e.g., AWS, Azure, and Google Cloud. They contain their solutions of misconfiguration detection, workload protection, and identity-based access control.
Best for: Organizations that are in the cloud or hybrid environments.
3. Penetration Testing and VAPT Companies
These cybersecurity companies in the USA attempt real-world cyberattacks to find vulnerabilities prior to their exploitation by the attackers. Services are provided as web, mobile, API, and network penetration testing.
Best for: Companies that are about to undergo compliance audits or enhance their application security.
4. Identity and Access Management (IAM) Providers
The US-based cybersecurity companies specializing in IAM are used to dealing with user identities, access control, and authentication. The solutions they adopt include multi-factor authentication (MFA), single sign-on (SSO), and zero-trust access.
Best for: In organizations with high user numbers and those who work remotely.
5. Managed Detection and Response (MDR) Providers
MDR companies provide 24/7 monitoring services, threat detection, and incident response services. Such providers will integrate the human element and AI-based capabilities to detect and prevent threats in real-time.
Best for: Companies that lack an in-house security operations center (SOC).
6. Network and Infrastructure Security Companies
These companies are preoccupied with the security of enterprise networks by firewalls, intrusion detection systems, and secure access models. They are useful in securing network traffic both in and out.
Best for: Enterprise with sophisticated IT infrastructure and a high network flow.
7. Compliance and Risk Management Providers
The USA is home to some of the best cybersecurity firms that are in the business of assisting organizations to comply with regulatory standards like HIPAA, GDPR, SOC 2, and PCI DSS. They offer audits, risk evaluations and governance models.
Best for: Controlled markets such as healthcare, finance, and SaaS.
8. Security Awareness and Human Risk Management Companies
One of the most common causes of breaches is human error. Company areas that these firms concentrate on include training their employees, phishing tests, and behavioral analytics to minimize the human factor risks.
Best for: Organizations that are seeking to enhance their human security layer.
These categories allow seeing how various cybersecurity companies can be assessed and select a provider that best fits your business model, infrastructure, and risk exposure.
How to Choose the Right Cyber Security Company in USA
In the USA, there are hundreds of cyber security companies that provide such services, which is why it is necessary to choose a partner in a strategic way. The most appropriate option will be determined by your risk exposure, risk business model and business compliance needs.
These are the main aspects to be taken into consideration during the process of assessing a cyber security company in USA:
1. Industry Experience
Cyber security companies are not equally effective in all industries. The risk profile and compliance needs of healthcare, fintech, SaaS, and government are different.
Select a provider that has a record of dealing with your industry to provide relevant coverage of threats and regulatory fit.
2. Compliance and Regulatory Expertise
Several frameworks have to be adhered to by many organizations like:
- HIPAA
- PCI DSS
- GDPR
- SOC 2
The most effective cybersecurity firms in the USA do not restrict security and assist in making your systems audit-ready.
This is particularly relevant to a start-up and SaaS organization that grows rapidly.
3. Breadth of Services
Contemporary cybersecurity demands a multi-layered strategy. Search among companies which offer:
- Penetration testing
- Managed detection and response (MDR).
- Cloud security
- Identity and access control.
- Awareness training on security.
Do not use one tool or vendor.
4. Reporting Quality and Transparency
A good cyber security company must not only identify weaknesses but also offer:
- Clear, actionable reports
- Risk prioritization
- Remediation guidance
Among the least known threats to cybersecurity is poor reporting.
5. Certifications and Expertise
Search certifications include:
- OSCP
- CISSP
- CEH
- CISA
These refer to the fact that the company adheres to accepted security standards.
6. Scalability and Support
The security needs of your business will change as your business expands. Choose a provider that can:
- Grow with your infrastructure.
- Provide ongoing support
- Adapt to new threats
Cybersecurity Trends in 2026
The Cybersecurity environment develops faster, and companies that cooperate with cyber security organizations in the USA need to remain at the forefront of the emerging threats and technologies. By 2026, the emphasis has moved away from the reactive defense approach and towards the more proactive and intelligence-driven security approaches.
The major trends which define the future of cybersecurity companies in USA and the methods used by organizations to guard their online resources are as follows:
1. Rise of AI-Powered Cyber Attacks
Artificial intelligence is increasingly being used by cybercriminals to automate attacks and thereby making them more difficult to detect. Highly convincing phishing emails are being created using AI, traditional security systems are being bypassed, and adaptive malware is being launched.
To counter this, the most popular cyber security firms are implementing AI-powered defense mechanisms to identify anomalies and prevent threats in real time.
2. Widespread Adoption of Zero Trust Architecture
The ” trust but verify model is no longer effective. Organizations are moving towards zero trust (2026), in which no user or device will be trusted by default.
This model has a major influence on minimizing the chances of insider threats and internal network movement.
3. Cloud-Native Security Becomes the Standard
With the migrations of businesses to multi-cloud and hybrid environments, traditional security tools are going out of fashion. The current trend in cybersecurity businesses within the USA is the provision of cloud-native security that offers visibility to the distributed systems.
The issue of cloud security is no longer an optional feature.
4. Identity as the New Security Perimeter
Identity has become the most important surface of attack with remote work and the adoption of SaaS. The number of attackers who focus on user credentials rather than infrastructure is rising.
It has become very important that every organization has a strong identity and access management (IAM).
5. Growth of Managed Detection and Response (MDR)
Most organizations do not have the strength to afford in-house security teams. Consequently, MDR services are emerging as a new product of our group of cybersecurity companies.
MDR enables companies to get the level of security of an enterprise without developing a complete SOC.
6. Continuous Security Testing and Offensive Security
Organizations are evolving from non-periodical testing to non-stop security checking. These are penetration testing, bug bounty, and real-world attack simulations.
The trend here is led by specialized cyber security firms in the USA, like QualySec.
Proactive testing is used to detect vulnerabilities before hackers can use them.
7. Increased Focus on Human Risk Management
One of the largest causes of security breaches is human error. Companies are putting increased investment in training and awareness of employees in 2026.
Strengthening the human layer is as important as securing technology.
8. Platform Consolidation in Cybersecurity
Organizations are shunning the need to handle dozens of detached tools. They would instead opt to use the consolidated services of major cyber security firms.
Security is made simpler and more visible through platform-based security.
Don’t leave your 2026 security posture to guesswork. Schedule a call with our US-market experts today.
Local Cybersecurity Expertise Across the USA
Finding a cybersecurity partner that understands your local regulatory environment and business landscape is critical. While the firms listed above provide nationwide services, we have curated specialized guides for major technology hubs to help you find local penetration testing and security compliance experts.
Explore Top Firms by Region:
- West Coast: Home to the world’s leading tech innovators. See our rankings for California and Washington.
- The South & East Coast: From financial hubs to government contractors. Explore the top providers in New York, Virginia, Florida, and Philadelphia.
- Emerging Tech Hubs: Massive growth in security is happening in the midwest and southern corridors. Check out experts in Texas, Chicago, Atlanta, Colorado, and Raleigh, NC.
Final Thoughts
The process of selecting the appropriate cyber security firms in the USA is not likened to one picking the largest. It concerns choosing the partner that fits your business objectives, riskiness and compliance requirements.
The best organizations in 2026 will not have been dependent on one vendor. They are developing a layered security system that includes cloud protection, identity security, threat detection, and continuous testing.
Although big sites offer scale and visibility, the more specialized companies, such as QualySec, can offer more insight due to Human-led AI Penetration Testing that businesses gain an in-depth understanding of the reality of threats that are only revealed by humans and not automated devices.
The key is simple. Select a cyber security company in the USA that provides both the defense of your systems and enhances your resilience in the long-term.
Frequently Asked Questions (FAQ)
Q: Which is the best company for cyber security?
Ans: The strongest cyber security agencies rely on your business requirements. Such companies as QualySec, Palo Alto Networks, and CrowdStrike are regarded as highly trustworthy as these companies are able to combine innovation, expertise on compliance, and practical defense approaches. A safe cybersecurity firm is the one that protects your information and fits in your sector.
Q: What are the top 10 cyber security companies?
Ans: QualySec, Palo Alto Networks, Microsoft, CrowdStrike, Cisco, McAfee, Fortinet, Zscaler, Proofpoint and Rapid7 are the best cybersecurity companies in the USA. These cyber security companies are at the forefront in penetration testing, endpoint protection, cloud protection and compliance preparedness.
Q: Who is the largest cyber security firm?
Ans: Various computer security firms such as Palo Alto Networks, Cisco and Microsoft are some of the largest companies in the world in terms of revenue and reach. These giants are regarded in the U.S. as the most reputable cyber security IT firms and they are relied upon by the Fortune 500 companies to use their services in providing scalable and enterprise level cyber security services.
Q: What does a cybersecurity firm do?
Ans: Such services provided by a cybersecurity company include penetration testing, managed detection and responding, exposure audits on clouds, and compliance consultancy services. These cyber security services companies are arranged to assist in locating its vulnerabilities, fight against attacks as well as maintain any business audit-worthy across all industries.
Q: What should I look for when choosing a cybersecurity company in the USA?
Ans: In assessing cyber security firms in the USA, look at industry-specific experience, certifications, reporting quality and service scope. Probably the most effective cybersecurity providers are those who offer proactive testing along with consulting, which provides you with both defense and alignment to compliance, and is specific to your business.





















































































































































































































































































































































































































































































































































































































































































































0 Comments