The phrase “cloud security services” refers to a broad range of methods and protocols intended to safeguard data stored in the cloud. Cloud enables businesses to scale at an accelerated pace, go global, and run without a limitation of the infrastructure limitations. The same flexibility, however, presents new security risks.
One open API, lax identity controls, or improperly configured storage options could expose sensitive and important workloads. These risks are more difficult to manage without well-organized security controls as organizations move more and more to AWS, Azure, Google Cloud, and hybrid environments.
Cloud security services are useful to respond to this change. They are created to defend cloud infrastructure, applications, identities, and data, and remain visible in dynamic environments.
Within this guide, we will dissect what cloud security services are, how they operate in various cloud architectures, the types of cloud security services on offer in the market, and the most important solutions that businesses employ to secure the current cloud environments.
What Are Cloud Security Services?
Cloud security services refer to a collection of tools, controls, and managed capabilities that are meant to safeguard cloud-based systems, data, and infrastructures against security risks.
They exist under a joint liability. The responsibility of cloud security of the underlying infrastructure lies with cloud providers, whereas the security of what the organizations build and store on top of their underlying infrastructure, including applications, data, and access rights lie with the organizations.
- Such services normally include:
- Suspicion and threat monitoring.
- Access control and user management.
- Securing data encryption and controls.
- Determining and correcting weaknesses.
- Securing configurations in cloud resources.
- Promoting adherence to business regulations.
The implementation of cloud security services may be in the form of single security solutions or an extensive security network based on the use of the cloud by the organization.
They are not just involved in attack prevention. They also assist in keeping control, provide uniform security practices, and promote safe operations as cloud environments increase in size and complexity.
Why Cloud Security Services Are Necessary?
Clouds are volatile in nature. The creation, modification, and scaling of resources continues to happen, and this makes it more difficult to ensure consistency in security controls.
These environments are risky because of several factors:
- Rapid deployments with the ability to cause configuration gaps.
- Teams are located in different locations and access different systems.
- Excessive use of APIs in communicating applications.
- Servers are running and functioning concurrently.
- Tough regulatory guidelines on data handling.
In the absence of special security measures, all these aspects may result in unauthorized access, data leakage, and operational failures.
Cloud pentesting will solve these constraints through policy enforcement, change tracking, and risk identification once they occur. They offer a streamlined process of controlling security at an infrastructural level, application level, and user access control.
This enables organizations to have control of their environments and still grow and innovate in the cloud.
Don’t stop at knowing why cloud security is important. Know where your cloud stands today with a detailed Cloud Security Gap Assessment.
Qualysec’s cloud pentest gives you results—no endless emails, no digging through PDFs, no guesswork.

Cloud Security Across Different Cloud Models
The used cloud services may have different types of cloud security requirements. Both models exchange the responsibility between the organization and the provider, and this affects the manner in which security is applied directly.
Infrastructure as a Service (IaaS)
In IaaS, the company provides basic infrastructure like virtual machines, storage, and communication. The organization has the duty of ensuring the security of everything constructed on it.
Security focus:
- Cloud operating systems and applications security.
- Network configuration management.
- Installation of patches and updates.
- Monitoring system activity
Platform as a Service (PaaS)
Under PaaS, the provider can be in charge of the infrastructure and runtime environment, permitting the development of applications by the teams.
Security focus:
- Securing application code
- Protecting APIs
- Managing user access
- Governing data interactions.
Software as a Service (SaaS)
In SaaS, the administration of the infrastructure and the application is done by the provider. Learners interact with the program using an interface or through a browser.
Security focus:
- User access control and permission.
- Protecting stored data
- Monitoring user activity
- Setting up the application settings safely.
The models present various security responsibilities. To protect effectively, alignment of the appropriate cloud security services against the usage of the cloud is needed.
Types of Cloud Security Services
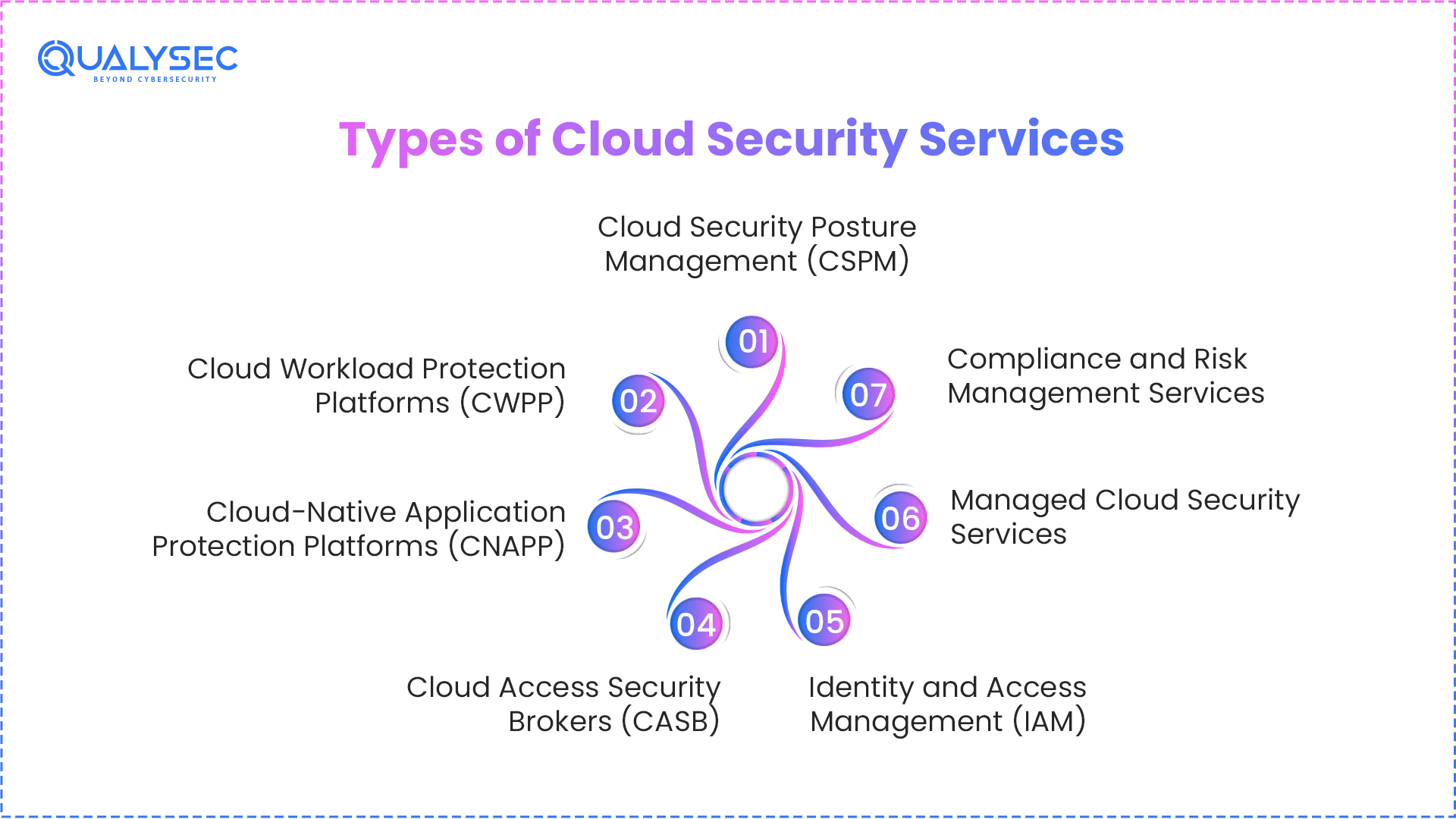
There are numerous levels of protection that are needed in cloud environments. That is why different organizations use various types of cloud security services, and each of them is aimed at mitigating particular risks of cloud infrastructure, application, and data.
With these services in mind, businesses will be able to select the appropriate mix of cloud security services according to their setting and their security requirements.
1. Cloud Security Posture Management (CSPM)
CSPM is dedicated to the detection and resolution of misconfigurations in the clouds.
It helps organizations:
- Identify uncovered storage, open ports, and dangerous environments.
- Keep AWS, Azure, and GCP in a safe configuration.
- Stick to the industry standards.
The prevention of one of the most frequent causes of cloud breaches, i.e., misconfiguration, is necessary with CSPM.
2. Cloud Workload Protection Platforms (CWPP)
CWPP provides the security of virtual machines, containers, and serverless functions.
- Runtime threat detection
- Malware protection
- Vulnerability monitoring
This kind of service provides the protection of workloads even after deployment.
3. Cloud-Native Application Protection Platforms (CNAPP)
CNAPP is an integrated platform that integrates several security features.
It typically includes:
- CSPM
- CWPP
- Identity and risk analysis
CNAPP offers a unified picture of cloud security and assists organizations with risk management in a multifaceted environment.
4. Cloud Access Security Brokers (CASB)
CASB solutions give visibility and control to SaaS applications.
They help:
- Monitor user activity
- Prevent data leakage
- Enforce access policies
- Detect shadow IT usage
CASB is particularly relevant to those organizations that utilize several SaaS tools.
5. Identity and Access Management (IAM)
IAM determines access, restricting who is allowed access and what they are allowed to do.
Key functions include:
- Role-based access control
- Multi-factor authentication
- Privileged access
Effective IAM minimizes the chances of loss of credentials and unauthorized access.
6. Data Security and Encryption Services
These solutions secure confidential information kept and transferred in the cloud.
They include:
- Data encryption
- Key management
- Data loss prevention
Data security services would guarantee that, in case data is accessed, it is not easily exploited.
7. Managed Cloud Security Services
A large number of organizations prefer cloud security as a service, where security is carried out by outsourced specialists.
These services offer:
- Continuous monitoring
- Detection and response to threats.
- Security assessments
- Incident management
Managed services are best suited to companies that do not have experienced security personnel within their organization.
8. Compliance and Risk Management Services
These services assist the organizations in satisfying the regulatory requirements and controlling risk.
They provide:
- Compliance monitoring
- Audit support
- Risk assessments
- Policy enforcement
Particularly, this applies to the industries where sensitive information is involved, like healthcare and finance.
Summary Table of Different Cloud Security Services
Type of Service | Purpose | Best For |
CSPM | Detect misconfigurations | Multi-cloud environments |
CWPP | Protect workloads | VMs, containers |
CNAPP | Unified cloud security | Complex cloud setups |
CASB | Control SaaS usage | SaaS-heavy organizations |
IAM | Manage access | Identity security |
Data Security | Protect sensitive data | Compliance and privacy |
Managed Services | Outsourced security | Limited in-house teams |
Compliance Services | Meet regulations | Regulated industries |
Through integration of these various cloud security solutions, companies can develop a robust, multi-layered security approach. The services deal with one risk each and, when combined, form an overall cloud security platform.
Watch the Client Testimonial to see how Qualysec helped a client secure their cloud environment
Key Cloud Security Solutions in Practice
The use of cloud security services takes practical solutions that are used continuously pertaining to the environment. These solutions assist organizations in identifying problems, implementing controls, and securing scalable operations.
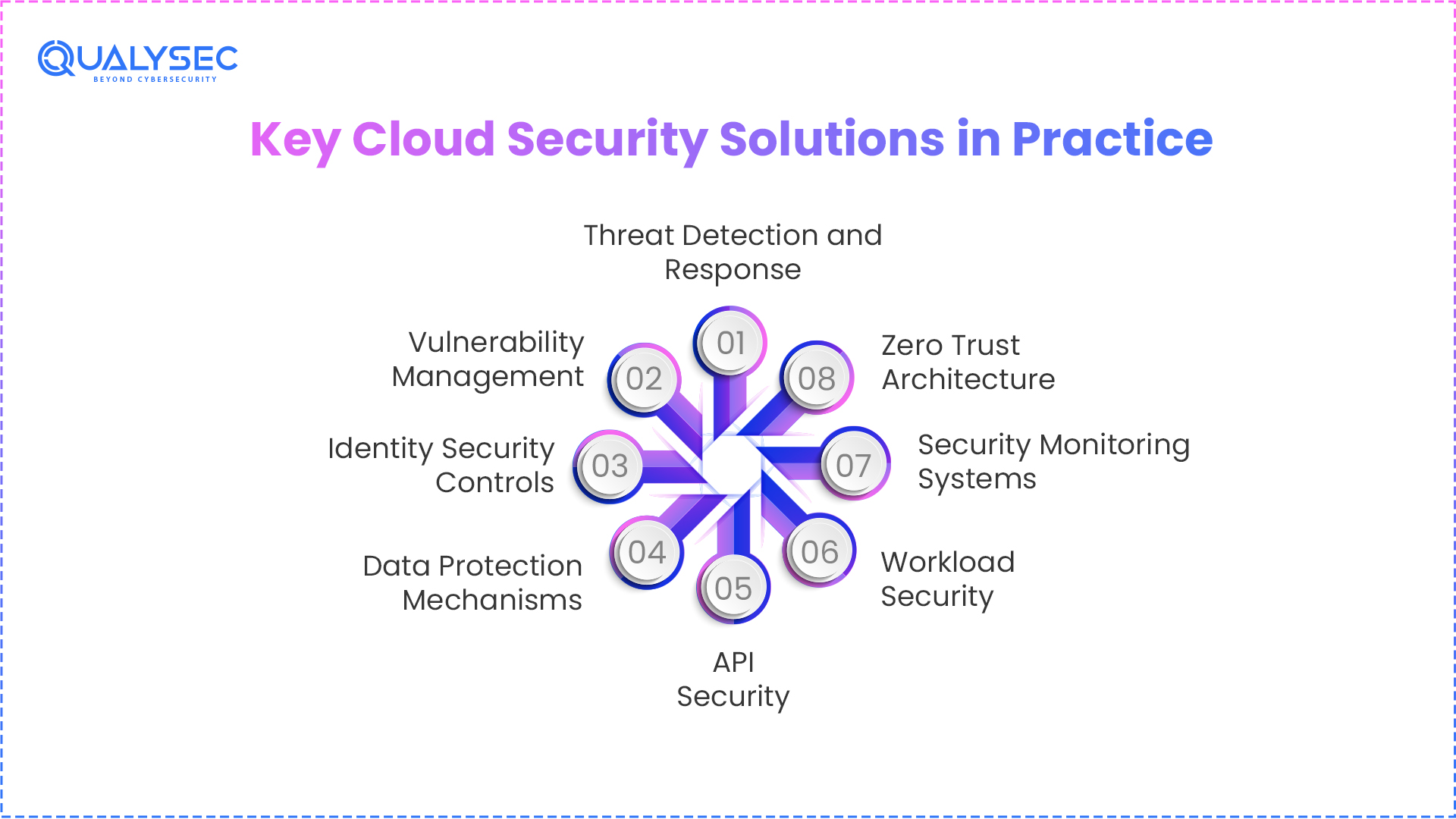
1. Threat Detection and Response
Monitors cloud activity to detect abnormal behaviour and threats. It allows prompt response to security breaches and solves them.
2. Vulnerability Management
Performs consistent scans of the systems and elements to find vulnerabilities. It aids in the priority and monitoring of remediation action to limit exposure.
3. Identity Security Controls
Imposes authentication, access control, and accountability functions to make sure that only authorized users can access cloud resources.
4. Data Protection Mechanisms
Ensures the safety of data by encryption and access controls. It will make sure that sensitive information is not exposed in the course of storage and transmission.
5. API Security
Secures application interfaces through monitoring traffic, authentication, and blocking unauthorized interactions among the services.
6. Workload Security
Clusters Containers, virtual machines, and cloud-native applications in their lifecycle.
The security monitoring systems, as before, have a direct relation to state security and the rule of law.
7. Security Monitoring Systems
Gathers and examines logs across various sources to identify patterns, investigate, and keep visibility across systems.
8. Zero Trust Architecture
Adopts a system of verifying each access request prior to being allowed. It imposes a default of trust and puts up stringent
These solutions can be used together to ensure consistency in coverage of protection in a dynamic cloud environment, to ensure that security controls are not disabled by the scale and evolution of systems.
How to Choose the Right Cloud Security Service Provider
Selection of the appropriate provider is an important task in creating a successful cloud security policy. Organizations have so many choices and must consider providers depending on the environment, risk profile, and business objectives of their cloud environment.
A right cloud security service provider must effectively provide good protection and be able to fit within your business requirements and long-term scalability.
Understand Your Cloud Environment
To begin with, evaluate your existing configuration:
- Single or Multi-cloud?
- Do you use IaaS, PaaS, SaaS, or both?
- What sort of information are you dealing with?
Diverse environments demand varying cloud computing security services and, therefore, this aspect needs to be clarified.
Evaluate Security Capabilities
An effective provider must be able to provide a broad spectrum of cloud security solutions, such as:
- Detection and response to threats.
- Vulnerability assessment
- Access control and identity management.
- Configuration monitoring
- Data protection
Ensure that their services are both preventive and reactive.
Check Compliance Support
In the case that your business is in a regulated industry, compliance cannot be compromised.
Seek providers that accommodate:
- GDPR
- HIPAA
- ISO 27001
- PCI-DSS
A good cloud-based security service must assist you in meeting compliance requirements and ease the audit.
Assess Visibility and Monitoring
Cloud environments are dynamic, and hence, real-time visibility is essential. Make a selection of a provider who provides:
- Continuous monitoring
- Centralized dashboards
- Alerting and reporting
This will guarantee that you are able to identify and act upon threats promptly.
Consider Scalability
The bigger your business, the greater your security needs will be.
The provider should:
- Support scaling workloads
- Adapt to multi-cloud environments
- Handle increasing data and users
Cloud computing guarantees scalable cloud security services that protect against the need to restructure continuously.
Look for Integration Capabilities
Your tools of security ought to be integrated. See whether the provider can be integrated with:
- AWS, Azure, Google Cloud
- DevOps and CI/CD pipeline
- Available security solutions such as SIEM or SOAR.
The complexity is minimized through good integration, and efficiency is enhanced.
Evaluate Expertise and Support
The issue of security does not simply concern tools. Expertise matters. A trustworthy supplier is expected to provide:
- Security consulting
- Incident response support
- Ongoing guidance
This will be necessary, particularly when your organization does not have in-house expertise in security.
Compare Cost and Value
The cost ought to be assessed in comparison to the value offered. Alternatively, to select the lowest cost, take into consideration:
- Coverage of services
- Quality of support
- Risk reduction benefits
Costly breaches can be averted by investing in the appropriate cloud security service in the future.
Quick Checklist
Before securing a provider, inquire:
- Do they support your cloud platforms?
- Do they provide comprehensive security coverage?
- Are they useful in meeting compliance requirements?
- Do they offer all-time follow-up and care?
- Can their services be expanded in the future?
The selection of the appropriate provider is not only a matter of features. It is related to identifying a partner capable of assisting you to get your cloud environment succinctly whilst aiding your business expansion.
Choosing the right provider also means understanding the cost. Explore our pricing!
Benefits of Professional Cloud Security Services
With the increased complexity of the cloud environment, simple approaches to security are no longer sufficient. Professional cloud security services offer the skills, tools, and constant monitoring required to secure contemporary cloud systems.
These are the main advantages of embracing these services by businesses.
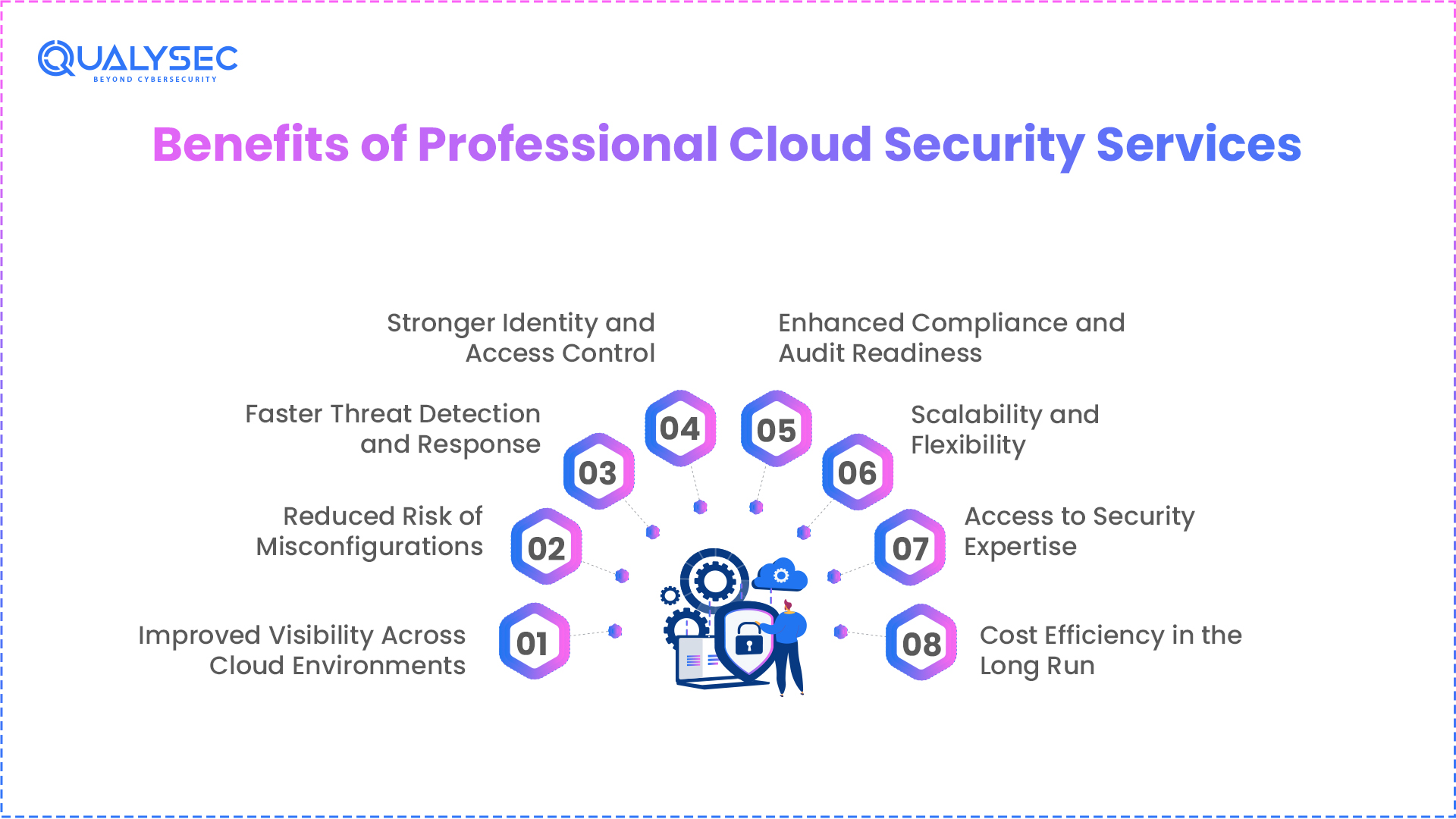
I. Improved Visibility Across Cloud Environments
Lack of visibility is one of the largest issues in cloud security. Having a variety of services, users, and workloads at the same time, it turns out to be inconvenient to trace everything.
The professional cloud-based security services offer:
- Centralized monitoring
- Live monitoring of cloud operation.
- Improved risk and asset knowledge.
This assists organizations in identifying problems at an early stage and in controlling their environments.
II. Reduced Risk of Misconfigurations
Among the top reasons that result in cloud breaches are misconfigurations. Azure and AWS cloud security services are beneficial in assisting:
- Find configuration errors continuously.
- Determine open storage, open ports, and dangerous environments.
- Fixes that should be recommended to prevent exploitation.
These problems can be prevented by taking action. Therefore, businesses can also decrease their surface of attack considerably.
III. Faster Threat Detection and Response
The current cloud security applications rely on automation and analytic procedures to identify threats instantly.
This enables:
- Rapid detection of suspicious behavior.
- Faster incident response
- Less severe effects of security attacks.
The primary factor in reducing the damage in the form of an attack is speed.
IV. Stronger Identity and Access Control
Access management in clouds is not easy, particularly in remote teams and multiple systems. Cloud security services offer:
- Role-based access control
- Multi-factor authentication
- Monitoring of user activity
This will minimize the unauthorized access and abuse of credentials.
V. Enhanced Compliance and Audit Readiness
Strict regulations have to be adhered to by organizations that deal with sensitive data.
Helps in professional cloud computing security services:
- Keep track of compliance requirements.
- Prepare audit-ready reports.
- Make sure that it is aligned with standards, including GDPR, HIPAA, and ISO 27001.
This makes the regulation easier, and there are fewer chances of punishment.
VI. Scalability and Flexibility
Cloud environments of businesses increase along with the growth of businesses. Cloud security services are expected to:
- Scale as workloads increase.
- Emulate multi-cloud and hybrid.
- Assistance in transforming business requirements.
This will guarantee uniform protection without undertaking significant security architecture modification.
VII. Access to Security Expertise
Not every organization manages to have its own in-house security teams. By using cloud security as a service, it is possible to access:
- Seasoned security personnel.
- Industry best practices
- Constant encouragement and mentoring.
This enhances general security posture without adding an extra burden on internal resources.
VIII. Cost Efficiency in the Long Run
Although it may appear expensive in the short term, one will be able to spend money on security and prevent losing lots of money due to data breaches, downtime, and compliance weaknesses.
Cloud security services provided by professionals:
- Minimize the risks of expensive accidents.
- Maximize security operations.
- Give superior payback in the long run.
Why These Benefits Matter
Not preventing attacks is not all that is involved in cloud security. It is concerned with helping businesses to run safely, scale without fear, and keep the customer trust.
Through the utilization of the appropriate cloud security services, organizations are able to enhance their security, increase efficiency, and remain adaptable to the emerging cyber threats.
Common Challenges in Cloud Security

Although there is flexibility and scalability in cloud adoption, it presents some security issues. These problems may result in vulnerabilities, data exposure, and compliance risks without the appropriate cloud security services.
The knowledge of these concerns is the primary step towards the development of a more formidable cloud security strategy.
I. Lack of Visibility
Cloud environments are extremely dynamic, and resources are continuously being added, changed, and deleted. This complicates the process of having a clear sight of everything that is involved in assets and activities.
Without proper visibility:
- Hidden risks may not be detected by security teams.
- Illegal modifications may pass unnoticed.
- The threats might not be detected in time.
That is why the current cloud security systems are concerned with real-time monitoring and centralized visibility to a great extent.
II. Misconfigurations
One of the most common causes of security incidents is due to misconfigured cloud settings.
Examples include:
- Publicly visible storage buckets.
- Ports and services that are open and not secured.
- Excessive permissions
Minor configuration mistakes can result in significant violations unless they are targeted within a short period.
III. Identity and Access Risks
Identities in the cloud are incredibly not easy to manage owing to several users, roles, and services.
Common issues include:
- Overprivileged accounts
- Ineffective authentication measures.
- Weak access control policies.
In the absence of robust identity management, attackers can use the credentials to unlawfully enter.
IV. Insecure APIs
Cloud communication requires APIs, which are, however, vulnerable points to attackers when they are not secured.
Risks include:
- Unauthorized API access
- Data manipulation
- Absence of authentication.
API security is an important aspect of cloud computing security services.
V. Multi-Cloud Complexity
It is common to have several cloud providers in many organizations, and this complicates things.
Challenges include:
- The control of various security settings.
- Being consistent in policies across the platforms.
- Integrating multiple tools
This complexity may result in security lapses if it is not managed well.
VI. Compliance and Regulatory Pressure
Strict regulations have to be adhered to by organizations that deal with sensitive data.
Challenges include:
- Adapting to new regulations.
- Stable cross-environmental compliance.
- Preparing for audits
In the absence of adequate cloud-based security services, compliance maintenance may be daunting.
VII. Skill Shortage
The security of the cloud necessitates expertise, and this is not possessed by all organizations.
This leads to:
- Delayed threat response
- Poor configuration management.
- Greater dependence on small in-house departments.
This is among the reasons why a great number of businesses outsource cloud security to seek out the services of expert assistance.
VIII. Evolving Threat Landscape
There is a continuous development of cyber threats, and cyber attackers are consistently attacking cloud environments.
Challenges include:
- Sophisticated persistent threats.
- Zero-day vulnerabilities
- Automated attacks
To be secure, organizations require constant surveillance and dynamic cloud security data on cloud computing.
Why These Challenges Matter
Such problems outline why cloud security cannot be seen as a one-time configuration. It needs to be constantly monitored, evaluated on a timely basis, and combine the appropriate tools and knowledge.
The use of appropriate cloud security services can help businesses minimize risk and enhance resilience, and have secure cloud operations.
Look at real-life case studies and understand the practical approaches for solving cloud security challenges.
Why Choose Qualysec for Cloud Security Services
Although tools and platforms are significant, expert services in terms of cloud security are still in demand by many organizations because they need to be able to identify actual risks, confirm configurations, and enhance their overall security posture.
Qualysec specializes in applied and analysis-based cloud security, which assists businesses in knowing their areas of vulnerability and how to remedy them practically.
Expert-Led Cloud Security Assessments
Qualysec focuses on the detection of actual security lapses and not just scanning with automation.
This includes:
- Reviews on the cloud configuration.
- Detection of risk among cloud resources.
- Environment-specific security assessments.
This method assists organizations in discovering problems that would not have been identified.
Focus on Actionable Remediation
Locating vulnerabilities is not the only problem in cloud security, but a proper fix to the problem is also one of the most important factors.
Qualysec provides:
- Facts, practical recommendations.
- Prioritized risk insights
- The applied remediation advice.
This makes it possible to provide security improvements with minimal efficiency.
Support for Modern Cloud Environments
Cloud systems are highly complex, multisource, or hybrid systems. The cloud-based security services offered by Qualysec are aimed at:
- Adjustment to changing environments.
- Support various cloud models.
- Manage emerging security threats.
This renders it appropriate for companies at varying levels of cloud adoption.
Helping Improve Security Maturity
In addition to the identification of problems, Qualysec also assists organizations in improving their long-term security posture.
This includes:
- Enhancing visibility in the cloud environments.
- Improving security measures.
- Promoting compliance preparedness.
A Practical Approach to Cloud Security
Qualysec does not just look at tools but takes a broader perspective on cloud computing security services, integrating advanced solutions like a cloud security scanner with deep technical expertise and real-world risk analysis.
To organizations that want to go beyond simple security implementations, such a solution can be used to create a more resilient and well-managed cloud environment.
Conclusion
The adoption of cloud keeps on increasing, and the risks associated with it are also increasing. Between lack of configuration and identity and challenges of a developing cyber threat, cloud environments’ security is now a serious concern among businesses of any size.
The cloud security services are critical in this. They offer the visibility, control, and protection required to ensure security of data, applications, and infrastructure in contemporary cloud environments. Organizations can lower the risk and enhance resilience and compliance by integrating the appropriate kind of cloud security services with efficient cloud security solutions.
Cloud security does not have a universal methodology. Each organization possesses various infrastructure, exposure risk, and business demands. This is why it is vital to select the appropriate balance between cloud computing security services and professional assistance and create a more powerful security posture.
To businesses that want a cost-effective and expert-initiated service, Qualysec could assist in evaluating cloud risks, detecting security vulnerabilities, and offering practical advice to enhance overall cloud security. With the right tactics, tools, and guidance, companies can defend their cloud setups with greater confidence.
Looking to strengthen your cloud security posture? Connect with Qualysec to explore expert-led cloud security services tailored to your business needs.
FAQs
1. What are cloud security services?
Cloud security services are the solutions and specialist practices that help to safeguard cloud infrastructure, applications, and data against cyber threats. They assist companies to have better visibility, access management, risk detection, and sustainability.
2. What is cloud security as a service?
Cloud security service refers to the provision of cloud protection on a subscription or managed basis. It enables companies to employ the services and resources of other companies without developing the whole security capability internally.
3. What are the types of cloud security services?
Typical ones are CSPM, CWPP, CNAPP, CASB, IAM, data security, managed cloud security, and compliance services. All of them are devoted to another aspect of cloud environment security.
4. What are cloud computing security services?
Cloud computing security service is meant to safeguard cloud-based structures, which include virtual machines, storage, applications, and networks. They promote security in IaaS, PaaS, and SaaS environments.
5. How do cloud security solutions work?
Cloud security solutions operate by monitoring the environments within the clouds, detecting and stopping threats, imposing policies, and assisting in responding to any risks. They tend to automate, analyze, encrypt, and control access to minimize the risk.
6. How do I choose the right cloud security service provider?
Select a provider depending on your cloud infrastructure, security provisions, compliance provisions, scalability, and support services. A powerful protection should be provided by the appropriate provider that should align with your business objectives and infrastructure.
7. What is the difference between cloud security services and cloud security tools?
Cloud security solutions are a single product to be employed in a specific process, such as scanning or monitoring. The services of cloud security are more comprehensive and can encompass those tools as well as professional advice, evaluations, and maintenance.
8. Why are cloud security services important?
Cloud security services have value in that they aid in preventing breaches, minimizing misconfigurations, sensitive data, and providing compliance support. They provide businesses with the security they require to venture safely in the contemporary clouds.












































































































































































































































































































































































































































































































































































































































































































0 Comments