iOS vs Android security is one of the most searched questions in mobile cybersecurity. Most answers focus on which operating system has better features. That framing is useful for buying a phone. It is less useful for understanding where mobile security actually breaks down.
The more accurate framing is as follows: the OS provides a security foundation. The app sitting on top of that foundation is where most real attacks happen. A 2025 study involving more than 156,000 mobile applications found that 71% of them contained at least one hardcoded secret, such as API keys, cloud credentials, or encryption keys. Most of the aforementioned applications passed both the App Store’s review process and Google Play Protect. The platform did not identify these applications as having hardcoded secrets embedded in their code because the platform was never designed to catch mistakes at the application layer (errors made by developers).
That does not make the iOS vs Android comparison unimportant. For device policy, enterprise deployments, and compliance decisions, platform-level security matters significantly. But the comparison needs to be honest about what the OS actually controls and what it does not.
This guide covers both layers: what iOS and Android each get right and wrong at the platform level, and what that means relative to where mobile security services actually break in practice.
Key Takeaways
- Apple has a consistent, default security edge across all its iPhone products because it manages both the hardware and software design for these devices.
- On the Pixel and flagship Samsung phones, Android devices are either equal to or better than iOS devices. Android, however, is highly fragmented because it runs on many low-priced devices.
- According to Malwarebytes (2025), malware threats to Android devices grew 151% between April and May of 2025, and also SMS-based malware grew a staggering 692%.
- A recent (2025) study showed that 71% of 156,000 mobile applications contained hard-coded secrets (API keys and credentials), regardless of platform type.
- The OS debate is important when it comes to establishing policies regarding mobile device usage; however, it’s not nearly as impactful as the security of an application’s code when it comes to data breaches.
- Both operating systems are equally ineffective at passing penetration testing for the same reasons at the application layer.
Why iOS vs Android Security Starts With How Each Platform Is Built
The structural difference between iOS and Android explains almost everything else in this comparison.
- The iOS offered by Apple is designed to be a vertically integrated, closed system. The company creates the operating system and processor, and distributes apps exclusively through the App Store to provide users with a consistent experience. Apple makes one decision that uniformly applies to all supporting phones worldwide.
- Android is open source. Google writes the base OS, but it then passes through each manufacturer’s customization layer before reaching devices. A patch Google releases today might reach a Pixel device tomorrow, a Samsung Galaxy flagship in a few weeks, and a budget Android device from a smaller manufacturer. The security update is real. The delivery is not guaranteed.
This is the core reason iOS has a default platform-level security advantage. It is not that Apple’s engineers write better code than Google’s. Apple’s centralized control eliminates fragmentation by design.
iOS Security vs Android: What iOS Gets Right and Where It Falls Short

iOS has developed its reputation for offering a secure operating system through well-thought-out architectural choices, as opposed to relying on marketing techniques. However, every platform has vulnerabilities, including at the application layer in iOS application security. To understand both sides, one must take into consideration that information is often presented in a manner that is one-sided, providing a classic example of biases in reporting.
Strengths
1. The Secure Enclave
All modern-day iPhones utilize a dedicated security chip that performs all security functions independently from the main processor/CPU. The chip manages the encryption keys as well as providing encryption for biometric data such as Face ID and Touch ID. The Secure Enclave prevents attackers from being able to access sensitive data that is protected by the Secure Enclave on iPhones, even if the attackers have been able to gain access to the primary processing unit of the phone. All iPhones currently supported by Apple have the same degree of hardware security through the Secure Enclave.
2. Secure Boot Chain
The iPhone performs a verifiable boot (startup) sequence at every level of the iOS boot process against Apple-signed code. Therefore, rootkits and malware cannot install at the firmware or kernel level because the iPhone will only execute valid signed code. Consequently, the Secure Boot process eliminates a whole area of low-level attacks that are common on less-secure platforms.
3. Consistent and immediate security updates
When Apple has found and/or patched vulnerabilities on iPhone’s iOS operating systems, these patches will be pushed to all supported iPhones in a matter of days. There are no added delays waiting for OEMs, and no added delays waiting for Carriers to approve the patch. As a result, the window of opportunity to exploit the vulnerability will be significantly shortened due to the speed and consistency in the delivery of security patches from Apple to iPhone end-users.
4. App Tracking Transparency
As of iOS 14.5, applications now require explicit permission from the user to track their activity across other applications and websites. Many people choose to deny this type of tracking. The effect of this is that third-party tracking numbers are not as readily available because the operating system’s platform enforces this requirement, rather than allowing individual application developers to decide whether or not they want to implement it.
5. No sideloading
Sideloading is not permitted on the iOS ecosystem. In order for an application to be installed from outside the App Store, the application must first be “jailbroken.” Thus, sideloading cannot be used as a means of attacking a device (as is the case with Android). A significant amount of the malware infections that occur on Android devices occur via malicious APKs being installed from SMS links or other websites. This form of attack simply does not exist on a stock iOS device.
Weaknesses
1. High-value target for sophisticated attackers
The app review process for the App Store does identify a large number of malicious apps; however, it does not identify mistakes made by legitimate developers at the application layer regarding system security. Legitimate developers will continue to submit applications with hard-coded credentials, insecure storage, broken certificate pinning, and poor authentication logic, and all of these types of application errors will pass the App Store review.
2. Zero-day exposure window
Apple patches quickly once vulnerabilities are discovered. The problem is the time before discovery. iOS zero-days are actively bought and sold. CISA’s Known Exploited Vulnerabilities catalog regularly includes actively exploited iOS flaws. The Rapid Security Response update mechanism Apple introduced has reduced this window, but has not closed it.
3. Reduced security testing visibility
With modern iOS versions, Apple has eliminated the last reliable method for security researchers to perform deep runtime analysis on iOS apps on real devices. Simulators cannot replicate Secure Enclave behavior or hardware memory protections accurately. This makes it harder for security teams to verify whether their own iOS apps are actually secure, not just whether they appear secure in code review.
4. App-layer vulnerabilities pass App Store review
The app review process for the App Store does identify a large number of malicious apps; however, it does not identify mistakes made by legitimate developers at the application layer regarding system security. Legitimate developers will continue to submit applications with hard-coded credentials, insecure storage, broken certificate pinning, and poor authentication logic, and all of these types of application errors will pass the App Store review.
Android vs iOS Security: Strengths, Weaknesses, and the Real Gaps
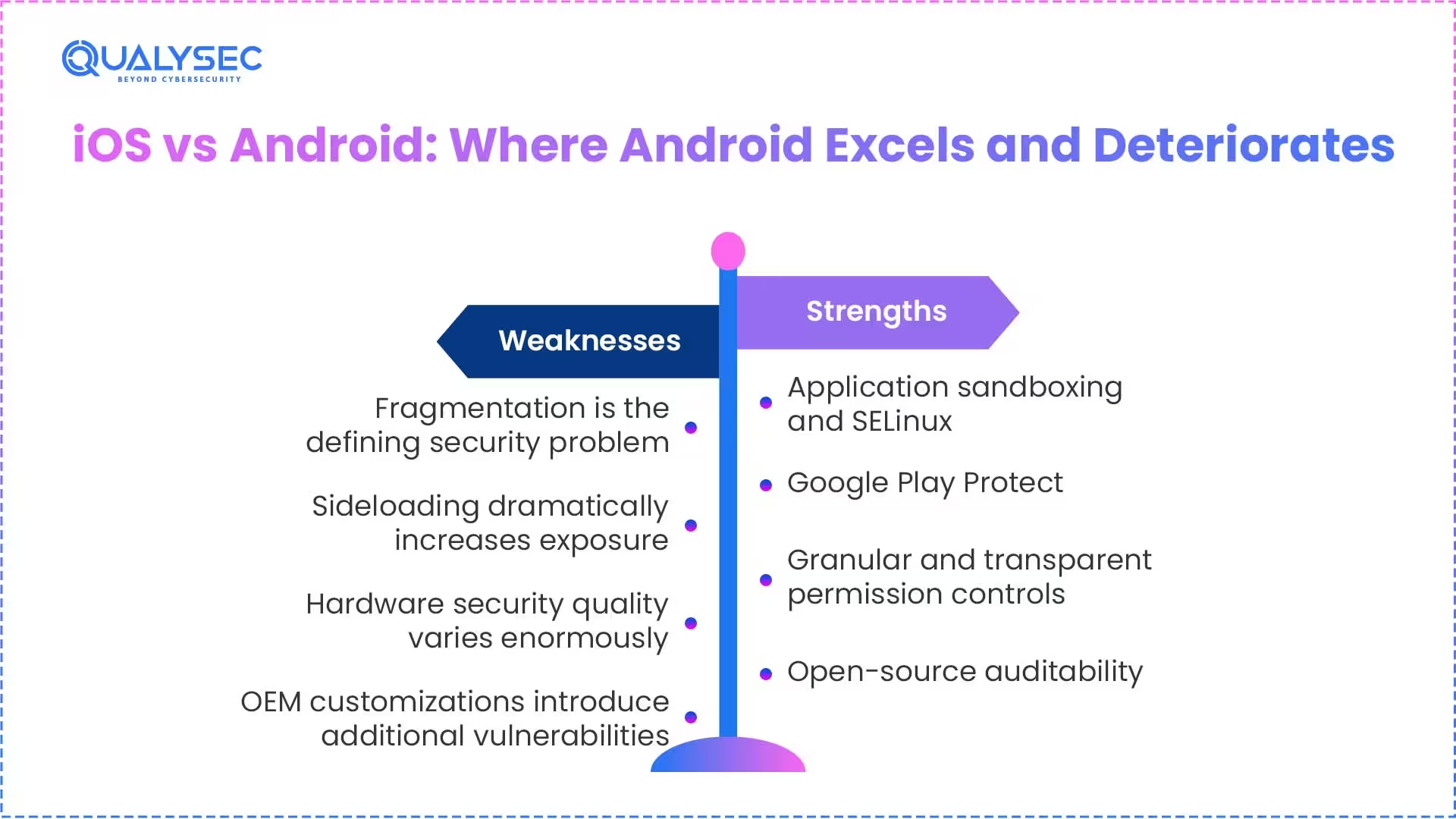
While the general belief about Android phones is that they are a less secure option than iPhones, that sentiment is not totally accurate. In reality, it depends on the model of Android phone and how that phone is managed. This also extends to Android application security, where app quality, permissions, and implementation practices play a major role in overall risk. Below is a fair assessment of both the areas in which Android shines and the areas in which it consistently performs poorly.
Strengths
1. Application sandboxing and SELinux
In regard to the Android operating system, each app operates inside of its own restricted environment through kernel-level Security-Enhanced Linux to ensure that no apps have direct access to the data or processes of other apps, no matter what form or what means the compromise occurs.
2. Google Play Protect
Google Play Protect provides an ongoing protection mechanism by continuously scanning the applications in the Play Store for policy violations prior to installation and for behavioral violations after installation. In 2023, Google Play Protect blocked in excess of 2.28 million policy-violating apps from being installed on users’ devices; therefore, Google Play Protect does not provide users with a guarantee of protection, but it does provide substantial ongoing protection.
3. Granular and transparent permission controls
Android shows users exactly which apps have access to which sensors and data. One-time permissions, auto-revoke for unused apps, and a centralized Privacy Dashboard give technically engaged users more visibility into their device’s data flows than iOS provides.
4. Pixel devices and the Titan M2 chip
Google’s own Pixel 8 and later devices receive 7 years of security updates, deploy the Titan M2 security chip (comparable to Apple’s Secure Enclave), and receive patches at the same speed as iOS. On Pixel hardware specifically, the Android security story is genuinely strong.
5. Open-source auditability
The Android codebase is publicly auditable. Security researchers worldwide can inspect it for vulnerabilities. This collaborative scrutiny has real benefits and sometimes catches vulnerabilities faster than closed-source systems, where only internal teams can review the code.
Weaknesses
1. Fragmentation is the defining security problem
A patch Google releases today takes weeks to reach Samsung flagships, months to reach mid-range devices, and never reaches many budget phones. This creates a permanent population of Android devices running known, publicly documented vulnerabilities. The attack surface this creates is not theoretical. Exploit kits actively target unpatched Android vulnerabilities because the attack window on affected devices can be measured in years.
2. Sideloading dramatically increases exposure
Android’s native support for installing apps from outside the Play Store is useful for legitimate purposes and is exploited heavily by attackers. SMS-based malware, which grew 692% on Android in 2025, is primarily delivered through links that trigger sideloaded APK installation. This attack vector does not require any OS vulnerability. It only requires the user to tap a link.
3. Hardware security quality varies enormously
A Pixel 8 and a budget Android device from a lesser-known manufacturer both run Android 14. Their hardware security baselines are not remotely comparable. The Pixel has dedicated security hardware. The budget device may have no equivalent protection at all. Both are counted as “Android devices” in any market comparison.
4. OEM customizations introduce additional vulnerabilities
Sometimes, when companies put their own software on the Android system, they create security risks that weren’t already in the stock Android. Along with proprietary software applications, system interfaces designed by the manufacturers, and manufacturer-specific services, these apps have resulted in numerous security incidents over the years.
iOS vs Android Security: Feature-by-Feature Comparison
Evaluating the strengths and weaknesses across all platforms produces a side-by-side comparison that allows you to assess your situation, be it personal and device selection, business deployment, or application development, depending on your own criteria as to what is important to you personally or to your business.
| Security Aspect | iOS | Android |
| Hardware security chip | Secure Enclave on all modern iPhones | Titan M2 on Pixel; varies widely elsewhere |
| Boot integrity | Cryptographically verified on every startup | Verified Boot; OEM implementation varies |
| App distribution | App Store only; no sideloading | Google Play Plus native sideloading |
| Security update delivery | Immediate, global, simultaneous | Fragmented; depends on OEM and carrier |
| Malware exposure | Lower; no sideloading allowed | Higher; sideloading creates significant exposure |
| Privacy defaults | ATT enforced; on-device processing | Privacy Dashboard; controls need active setup |
| Enterprise MDM | Apple Business Manager; straightforward | Android Enterprise: more overhead required |
| Biometric security | Secure Enclave is backed on every iPhone | Varies significantly by manufacturer |
| Update support lifespan | 5 to 6 years | 7 years on Pixel 8+; 1 to 4 years on most others |
| Security testing visibility | Reduced significantly with the modern iOS version | Easier; root access is more accessible |
Is your mobile app as secure as your platform? The OS provides the foundation. The app is where most attacks happen. Get a consultation with QualySec today and protect your iOS and Android applications against threats tomorrow.
Talk to our Cybersecurity Expert to discuss your specific needs and how we can help your business.
iPhone vs Android Security Updates: How Long Does Protection Actually Last?
Security update lifespan is one of the most underappreciated factors in the iOS vs Android security debate. A device that stops receiving patches becomes a permanently exposed target, regardless of how strong its original security architecture was. Here is how the two platforms compare across device tiers.
| Device Type | Security Update Support | Rollout Speed |
| iPhone (any supported model) | 5 to 6 years minimum | Immediate and global |
| Google Pixel 8 and later | 7 years | Immediate and global |
| Samsung Galaxy flagship | 4 to 5 years | Fast, occasionally staged |
| Samsung Galaxy mid-range | 3 to 4 years | Moderate |
| Xiaomi, OnePlus flagship | 3 to 4 years | Variable by region |
| Budget Android (most brands) | 1 to 2 years, often less | Frequently absent |
The practical implication of this table: a three-year-old iPhone 14 is still receiving current security patches. A three-year-old budget Android from a smaller manufacturer is almost certainly running an OS with multiple known, unpatched vulnerabilities. This gap affects millions of real devices actively used today.
Android vs iOS Comparison: Which Platform Protects Your Data by Default?
Privacy and security are related but distinct concerns. Privacy governs what data is collected and shared. Security governs whether that data can be accessed without authorization. Both matter, and the two platforms approach privacy differently at the default level.
| Privacy Feature | iOS | Android |
| Cross-app tracking consent | Mandatory opt-in via App Tracking Transparency | Available but less uniformly enforced |
| Location precision options | Precise or approximate; one-time permission | Same options available |
| Email privacy | Hide My Email (iCloud+) | Not built in |
| On-device AI processing | Siri mostly on-device | Google Assistant uses the cloud by default |
| Clipboard access alerts | Apps notify when reading the clipboard | Requires Android 12+ |
| Selective photo access | Limited library permission without full access | Similar controls were added in Android 13 |
| Permission audit | Privacy Report in Settings | Privacy Dashboard |
Apple’s approach is privacy-on by default. Most protections are active without any user configuration. Android’s approach is privacy-configurable, meaning the controls exist but require the user to actively set them up.
For a user who will not configure their settings, iOS provides meaningfully stronger default privacy. For a technically knowledgeable user willing to actively manage their device, Android can achieve comparable or stronger privacy with the right setup.
If your organization is building a mobile application and needs to understand its security posture before shipping, a mobile application penetration test is the most direct way to find out. Learn more about mobile app security testing.
What iOS vs Android Security Cannot Protect Against: The Application Layer
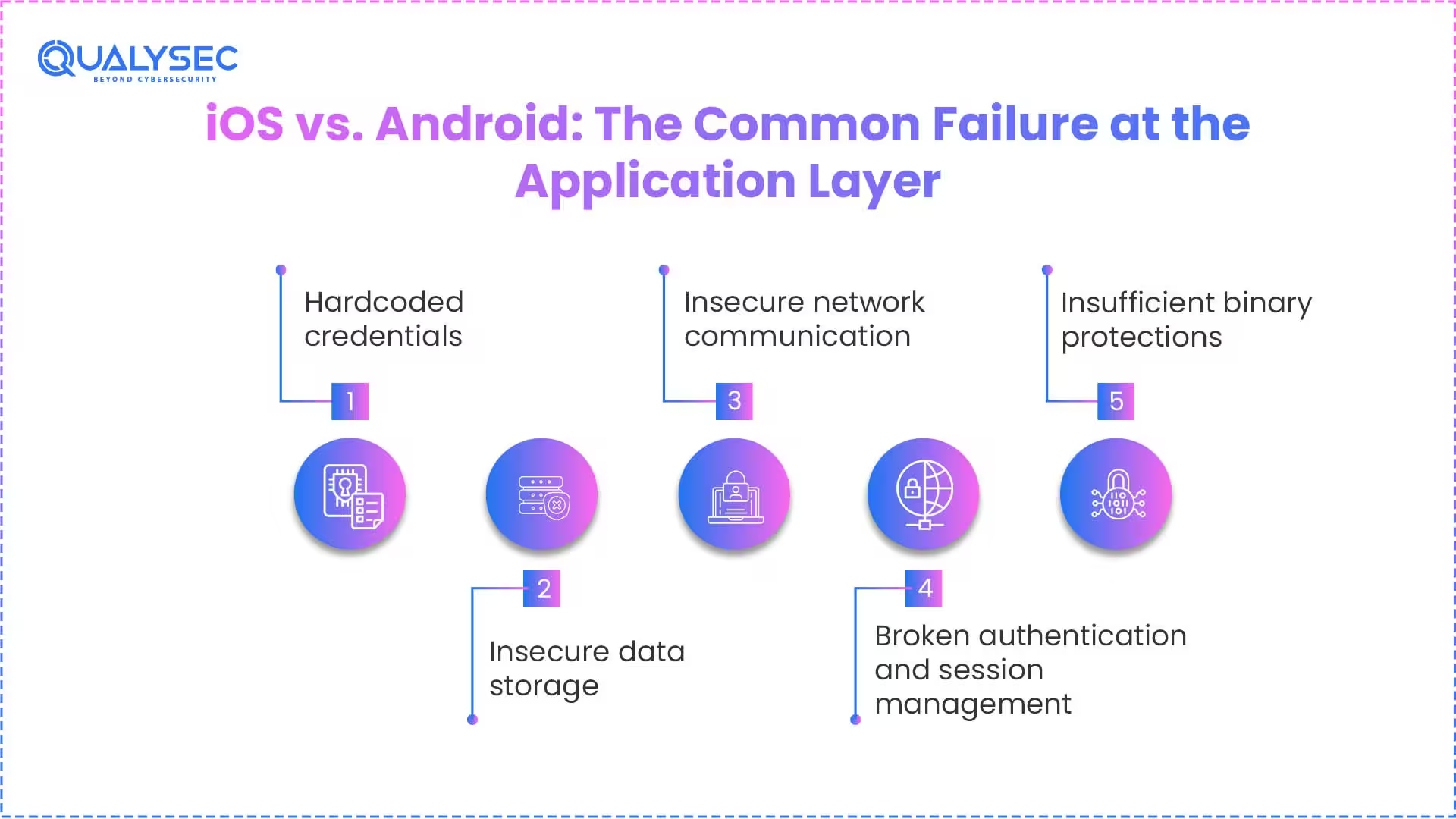
This is the section that most iOS vs Android comparisons skip entirely.
The OWASP Mobile Top 10 (2024) documents the vulnerabilities most commonly found and exploited in real mobile apps. These are worth understanding because they appear at comparable rates in iOS and Android apps, regardless of which platform’s OS-level security is stronger.
Hardcoded credentials
API keys, passwords, and encryption keys embedded directly in app code are among the most common findings in mobile security assessments. A 2025 study of 156,000+ apps found 815,000 unique secrets embedded in apps, many linked to live production systems. These passed both App Store review and Google Play Protect. No OS-level security control catches a developer who hardcoded an AWS key in the binary.
Insecure data storage
Sensitive data written to unencrypted local databases, log files, or insecure storage locations is extremely common on both platforms. iOS’s Secure Enclave protects biometric data. It does not protect an app that stores session tokens in an unencrypted SQLite file because the developer did not know better.
Insecure network communication
Despite HTTPS being the default requirement on both platforms, many apps accept weak TLS configurations, skip certificate pinning, or pass sensitive data in URL parameters. This leaves them vulnerable to traffic interception on any network, regardless of which OS the device runs.
Broken authentication and session management
Weak authentication logic, long-lived session tokens that never expire, and missing re-authentication for sensitive actions are common on both platforms. These are design decisions, not OS vulnerabilities. No platform-level protection compensates for them.
Insufficient binary protections
Apps on both platforms are often shipped without basic hardening: no root or jailbreak detection, no anti-tampering measures, no code obfuscation. Attackers reverse-engineer these apps to extract secrets, understand business logic, and construct targeted attacks.
The thread connecting all of these: they are application-layer issues. They exist independently of the OS. The platform provides a security foundation. The app determines whether that foundation means anything.
71% of mobile apps have hardcoded secrets. Is yours one of them?
Hardcoded API keys, broken certificate pinning, and insecure storage pass app store review every day. A manual penetration test finds what automated scanners miss. Get a Mobile App Pentest Quote
Android vs iOS Security for Enterprise: Compliance, MDM, and Regulated Industries
For organizations subject to HIPAA, PCI DSS, SOC 2, GDPR, or ISO 27001, the platform choice has direct compliance implications.
iOS in regulated environments
iOS is the standard recommendation in most regulated industries because consistent update delivery reduces compliance gaps, Apple Business Manager simplifies MDM enforcement, and the Secure Enclave provides hardware-backed key storage that security auditors recognize. App Tracking Transparency also reduces accidental data leakage through third-party analytics SDKs that compliance frameworks increasingly flag.
One important clarification: iOS compliance is not automatic. A healthcare app that stores patient records in unencrypted local storage fails HIPAA regardless of which device it runs on.
Android in regulated environments
Android Enterprise with Work Profiles provides genuine capability for separating personal and corporate data on BYOD devices. Samsung Knox adds hardware-backed security on Samsung devices specifically. These are real, defensible capabilities.
The challenge is consistency. Allowing any Android device into a regulated environment means maintaining MDM policies that account for significant security variation across hundreds of device models. On a defined list of approved devices (Pixel and Samsung flagship), this is manageable. With an open BYOD policy allowing any Android device, it becomes very difficult to maintain a defensible compliance posture.
Need a pentest report your auditors will actually accept?
Qualysec delivers VAPT reports accepted by HIPAA, PCI DSS, SOC 2, ISO 27001, and GDPR auditors. 350+ clients. 38 countries. Compliance-ready documentation. Download a Sample Pentest Report.
Get a Free Sample Pentest Report
iOS vs Android Security and Privacy: 5 Misconceptions Worth Correcting
A number of widely repeated claims about iOS and Android security are either partially wrong or missing important context. Clearing these up prevents decisions being made on faulty assumptions.
Misconception 1: iPhones cannot get malware.
The closed ecosystem dramatically reduces mass malware infections. It does not prevent targeted attacks. The Pegasus spyware used zero-click iOS exploits that required no user interaction. Apple actively patches exploited iOS vulnerabilities on an ongoing basis.
Misconception 2: Android is fundamentally insecure.
A current Pixel 8 with up-to-date software, no sideloaded apps, and Play Protect active is a genuinely secure device. The Android security problem is fragmentation and sideloading behavior, not the core OS engineering.
Misconception 3: App stores guarantee safety.
Both the App Store and Google Play have had malicious apps bypass their review processes. In 2025, researchers found 815,000 unique secrets embedded in apps that had passed app store review. Review processes catch policy violations and obvious malware. They do not catch implementation security mistakes.
Misconception 4: The newest device is always the most secure.
A new iPhone running an app with broken authentication is less secure than an older device running a well-audited app. Device security and application security are separate problems that require separate solutions.
Misconception 5: Biometrics make a device fully secure.
Biometrics protect local device access. They do not protect against network attacks, phishing, API vulnerabilities, or any application-layer issue. A biometric lock on a front door does not protect a house with open windows.
Security Best Practices for iOS and Android Users
These apply regardless of which OS you use. Use a strong alphanumeric passcode rather than a 6-digit PIN. Enable biometric authentication as a convenient second factor. Install OS and app updates as soon as they are available. Review app permissions regularly and revoke access that no longer has a clear purpose. Use an authenticator app for two-factor authentication rather than SMS, which is vulnerable to SIM-swapping. Avoid connecting to public Wi-Fi without a VPN.
- For Android users specifically: keep the “Install unknown apps” setting disabled for all sources. Prioritize devices with longer update support, particularly Pixel and Samsung flagship models. Check when your device last received a security patch and how long support is expected to continue.
- For organizations: implement MDM regardless of platform. Enforce encryption, remote wipe capability, screen lock requirements, and app allowlisting across all managed devices. Require security testing for any mobile application that handles sensitive user data before it ships.
iOS vs Android Security in 2026: The Verdict
iOS has a genuine and meaningful default security advantage over Android. Apple’s control of both hardware and software means updates reach all supported devices immediately, the Secure Enclave provides consistent hardware-backed security across every iPhone, and the absence of sideloading eliminates a major attack vector. For device policy decisions and regulated enterprise environments, iOS is the lower-risk default.
Android has closed the gap significantly on Pixel and Samsung flagship hardware. With proper MDM, an approved device list, and active Play Protect, a well-managed Android environment is a defensible security posture. The problem is that most Android deployments are not that controlled, and fragmentation ensures they never will be uniform.
But here is what the OS comparison cannot tell you: how secure is the app running on that device?
A well-built Android app is more secure than a poorly built iOS app. A weak app on a strong platform is still a weak app. OS-level protections are the foundation. The application determines whether that foundation means anything for the people whose data depends on it.
If you are making a device policy decision, iOS is the conservative, lower-risk choice. If you are building or shipping a mobile application, the platform is the starting point. Application security testing is the rest of the work.
Discuss your mobile application protection testing needs with engineers at QualySec to identify latent threats and make your applications resistant to actual cyber attacks.
Secure Your iOS & Android Applications
Strengthen Mobile App Security with Expert Testing.
Frequently Asked Questions
1. Is iOS more secure than Android?
By default, yes. iOS provides more consistent updates, a tighter app ecosystem, and hardware-level security that is uniform across all modern iPhones. Android matches this on Pixel hardware but fragments significantly across most other devices.
2. Which mobile OS is most secure for business use?
For regulated industries like healthcare, finance, and government, iOS is the standard recommendation due to updated consistency, Secure Enclave-backed storage, and simpler MDM integration. Android Enterprise on Pixel or Samsung Knox devices is a strong alternative with the right management infrastructure.
3. Is iPhone more secure than Android in 2026?
On default settings with a typical user’s behavior, yes. The gap has narrowed but not closed, particularly for users on non-Pixel, non-Samsung Android devices, where fragmentation remains a real problem.
4. Which platform offers better privacy?
iOS provides better out-of-the-box privacy with App Tracking Transparency enforced at the OS level, on-device Siri processing, and Hide My Email. Android offers more granular user-configurable privacy controls but requires active configuration to achieve comparable protection.
5. Does platform choice matter more than app security?
No. For organizations building or deploying mobile apps, application-layer security determines actual risk more than OS choice. Both iOS and Android apps fail security testing for the same application-layer reasons at comparable rates.
6. What are the most commonly exploited vulnerabilities in mobile apps?
The OWASP Mobile Top 10 covers the most frequent findings: hardcoded credentials, insecure local data storage, weak or missing certificate pinning, broken authentication and session management, and insufficient binary protections. These vulnerabilities appear in apps on both platforms.
7. How long do iOS and Android devices receive security updates?
iPhones typically receive updates for 5 to 6 years. Google Pixel 8 and later devices receive 7 years. Samsung Galaxy flagships receive 4 to 5 years. Most other Android devices receive 1 to 3 years, with many budget models receiving even less.























































































































































































































































































































































































































































































































































































































































































































0 Comments