In today’s rapidly evolving digital landscape, security is paramount for organizations. As the cloud becomes increasingly prevalent, Amazon Web Services (AWS) stands out as a leading provider. Conducting AWS penetration testing in the USA is crucial to ensure the security of cloud-based assets. In this engaging blog post, we will explore what AWS penetration testing entails, the importance of conducting it, AWS’s stance on penetration testing, and best practices to enhance security. So, let’s dive into the world of AWS penetration testing and uncover the secrets to safeguarding your valuable resources
What is AWS Penetration Testing?
Imagine a digital fortress protecting your organization’s data and applications. AWS penetration testing is like a trial by fire for that fortress. It involves actively assessing the security of your AWS infrastructure by attempting to exploit vulnerabilities, misconfigurations, or weaknesses. By simulating various attack scenarios, you can identify potential risks and ensure the robustness of your security controls.
The Importance of AWS Penetration Testing
With data breaches and cyber threats on the rise, the importance of AWS penetration testing cannot be overstated. It allows you to proactively identify vulnerabilities before malicious actors do, reducing the risk of data breaches, financial losses, and reputational damage. By conducting penetration testing, you gain valuable insights into the strengths and weaknesses of your AWS environment, enabling you to implement effective security measures.
Does AWS Allow Penetration Testing?
Yes, AWS allows penetration testing, but with certain conditions. Organizations must obtain explicit written permission from AWS to conduct penetration testing activities. This permission ensures that the testing is authorized and prevents any legal complications or misunderstandings.
Types of AWS Penetration Testing
- Black Box Testing: In this type, the tester has no prior knowledge of the target infrastructure. It simulates an external attacker trying to gain unauthorized access.
- White Box Testing: In white box testing, the tester has complete knowledge of the target infrastructure. It simulates an insider threat or a privileged user attempting to exploit vulnerabilities.
- Grey Box Testing: Grey box testing strikes a balance between black box and white box testing. The tester has partial knowledge of the target infrastructure, simulating a scenario where an attacker has limited access or insider knowledge.
Traditional Penetration Testing and AWS Penetration Testing
Penetration testing
Traditional penetration testing primarily focuses on assessing the security of on-premises infrastructure, including servers, network devices, and applications hosted within an organization’s own data centers. It involves simulating various attack scenarios to identify vulnerabilities and weaknesses that could be exploited by external or internal threats. Traditional penetration testing often follows a standardized methodology, such as the Open Web Application Security Project (OWASP) or the Penetration Testing Execution Standard (PTES).
AWS Penetration Testing
AWS penetration testing specifically targets the security of resources and services hosted on the Amazon Web Services (AWS) cloud platform. It takes into account the unique challenges and complexities presented by cloud environments. AWS penetration testing aims to identify vulnerabilities, misconfigurations, and weaknesses within AWS services, including EC2 instances, S3 buckets, RDS databases, and IAM roles.
Top 3 Key Differences:
- Infrastructure Scope: Traditional penetration testing focuses on the organization’s internal infrastructure, including physical and virtual assets hosted on-premises. AWS penetration testing, on the other hand, centers around the assessment of AWS-specific resources and services within the cloud environment.
- Shared Responsibility Model: In traditional penetration testing, the organization has full control and responsibility for the entire infrastructure. In AWS, there is a shared responsibility model, where AWS is responsible for the security of the cloud infrastructure, while the customer is responsible for securing their applications and data within AWS services.
- Dynamic Infrastructure: AWS environments are highly dynamic, allowing for elastic scaling and rapid deployment of resources. This dynamic nature requires a different approach to penetration testing compared to the more static infrastructure typically found in traditional environments.
AWS Testing Methodologies
There are several existing methodologies for conducting AWS penetration testing, including:
- AWS Recon: This methodology focuses on discovering information about the target infrastructure and services deployed in AWS.
- AWS Enumeration: Here, the tester identifies and enumerates AWS resources and services to gain a comprehensive understanding of the target environment.
- AWS Exploitation: This phase involves actively exploiting vulnerabilities, misconfigurations, or weaknesses in the AWS infrastructure to assess its resilience.
Preparing for an AWS Penetration Test
Before conducting an AWS penetration test, it is essential to prepare adequately. This involves the following steps:
- Define Prerequisites and Scope: Determine the prerequisites, such as access credentials and permissions, required for conducting the penetration test. Clearly define the scope of the test, including the assets, services, and specific testing methodologies to be employed.
- Establish Rules of Engagement: Collaborate with the relevant stakeholders to establish rules of engagement that outline the testing objectives, limitations, and any specific constraints.
- Gather Information: Collect relevant information about the AWS infrastructure, including architecture diagrams, network maps, and service configurations.
Introduction to AWS Cloud Services
Understanding the various AWS cloud services is essential for effective penetration testing. Familiarize yourself with services such as Amazon EC2, Amazon S3, Amazon RDS, and AWS IAM, as they are commonly targeted by attackers.
Suggested Tools for Performing AWS Penetration Testing: There are several tools that can assist in performing AWS penetration testing. Some popular options include:
- AWS CLI: The AWS Command Line Interface allows you to interact with various AWS services, automate tasks, and perform security assessments.
- Pacu: Pacu is an open-source AWS exploitation framework that aids in reconnaissance, enumeration, and exploitation of AWS resources.
- ScoutSuite: ScoutSuite is a security auditing tool that provides detailed insights into AWS account configurations, helping identify vulnerabilities and misconfiguration.
Common AWS penetration testing techniques
AWS Security Token: AWS Security Token Service (STS) enables you to grant temporary access to AWS resources to perform testing without compromising the long-term security of your account.
External Reconnaissance: External reconnaissance involves gathering information about the target AWS infrastructure from publicly available sources, such as DNS records, public IP addresses, and open ports.
Local Filesystem: Testing the local filesystem on AWS instances involves assessing file permissions, sensitive information exposure, and potential misconfigurations that could lead to unauthorized access.
AWS’s Stance on Penetration Testing
Now, you might wonder if AWS even allows penetration testing. The answer is a resounding “yes!” AWS recognizes the importance of penetration testing and permits it. However, it comes with a caveat. To conduct AWS penetration testing in the USA, you must obtain explicit written permission from AWS. This permission ensures that your testing activities are authorized, preventing any legal complications or misunderstandings.
Best Practices for AWS Penetration Testing
Now that we understand the importance and permission aspect, let’s explore the best practices for AWS penetration testing in the USA:
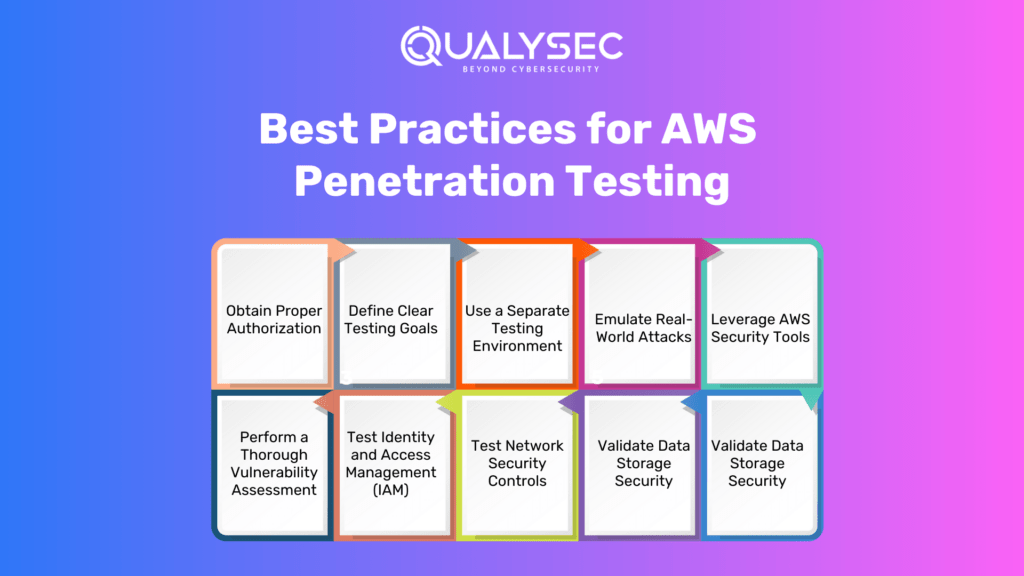
Obtain Proper Authorization
Before embarking on your AWS penetration testing journey in the USA, it’s crucial to obtain explicit written permission from AWS. This step ensures that you are authorized to assess the security of your own infrastructure, paving the way for a smooth and legitimate testing process.
Define Clear Testing Goals
Clear goals are essential for any successful endeavor. Similarly, in AWS penetration testing, clearly define the scope and objectives of your testing engagement. Identify the specific AWS assets and services you want to test, such as EC2 instances, S3 buckets, or RDS databases. This focused approach helps ensure comprehensive coverage and efficient resource utilization.
Use a Separate Testing Environment
To prevent any unintended damage or disruption to critical systems, always conduct penetration testing in a separate environment rather than testing directly on production resources. AWS provides tools like Amazon Virtual Private Cloud (VPC) and AWS Organizations, enabling you to create isolated testing environments with controlled access. This way, you can unleash your testing prowess while keeping your live environment unscathed.
Emulate Real-World Attacks
To truly gauge the effectiveness of your AWS security measures, approach penetration testing from the perspective of a potential attacker. Think like a cunning hacker and consider a variety of attack vectors such as network-based attacks, application-level vulnerabilities, or even social engineering techniques. This approach helps identify weaknesses that might be overlooked by traditional security measures.
Leverage AWS Security Tools
AWS offers a treasure trove of security services and tools to fortify your AWS penetration testing efforts. These tools act as your trusty sidekicks throughout the testing process. For instance, AWS CloudTrail provides detailed logs of API activity, AWS Config helps assess resource configurations, and AWS GuardDuty identifies potential malicious activities. By integrating these tools into your testing process, you gain deeper insights and enhance your security posture.
Perform a Thorough Vulnerability Assessment
A robust AWS penetration testing strategy involves conducting a comprehensive vulnerability assessment. This entails using automated scanning tools like AWS Inspector, open-source tools like OWASP ZAP or Nmap, or even commercial vulnerability scanners. Regularly update these tools to stay ahead of the ever-evolving threat landscape and identify common vulnerabilities and misconfigurations.
Test Identity and Access Management (IAM)
IAM is the backbone of AWS security. As you embark on your AWS penetration testing in the USA, it’s crucial to assess IAM roles, policies, and permissions. Verify that users have the appropriate access levels and adhere to the principle of least privilege. Weak or misconfigured IAM settings can open doors to unauthorized access and potential data breaches.
Test Network Security Controls
Your AWS infrastructure’s network security controls play a vital role in preventing unauthorized access and data exfiltration. During penetration testing, assess the effectiveness of security groups, network ACLs, and AWS Web Application Firewall (WAF). Look for misconfigurations or gaps that could potentially expose your resources. Regularly review and update these controls to align with the changing threat landscape.
Validate Data Storage Security
As data is the lifeblood of your organization, evaluating the security of your data storage services is paramount. During AWS penetration testing, scrutinize data storage services like Amazon S3 or Amazon RDS. Verify that data encryption is properly implemented, both in transit and at rest. Additionally, check for any publicly accessible resources and validate the integrity of access controls and permissions to prevent unauthorized data exposure.
Document and Remediate Findings
Document all findings, vulnerabilities, misconfigurations, and potential risks discovered during AWS penetration testing. Assign severity levels to each issue and prioritize remediation efforts accordingly. Develop a comprehensive plan of action to address the identified issues. Remember, the testing journey doesn’t end with documentation; it’s essential to regularly review and retest security controls to ensure fixes have been properly implemented.
Tools Used in AWS Testing
Several tools can aid in AWS penetration testing, including:
- AWS Inspector
- OWASP ZAP
- Nmap
- Nessus
- Burp Suite
- BeEF
- Metasploit Framework
AWS Penetration Testing Provider – Qualysec
Qualysec, A Cybersecurity company founded in 2020 is a leading cybersecurity provider. Qulaysec is also known for its renowned cutting-edge technology and expertise in cybersecurity assessments. With a team of skilled professionals, Qulaysec offers a comprehensive range of services, including various vulnerability assessments and penetration testing.
What sets Qulaysec apart is its commitment to staying ahead of the curve in terms of emerging threats and advanced hacking techniques. They employ state-of-the-art tools and methodologies to ensure thorough and accurate assessments. Qulaysec’s team of experienced professionals brings a wealth of knowledge and a human touch to their engagements. This in turn helps foster collaboration and deliver actionable insights.
Technicians at Qualysec can detect flaws that fraudsters could abuse. After these flaws have been found, Qualysec collaborates with the organization to establish a plan to address them and boost the company’s overall security posture. Among the several services available are:
- Web App Pentesting
- Mobile App Pentesting
- API Pentesting
- Cloud Security Pentesting
- IoT Device Pentesting
- AI /ML Pen-testing
Hence, choose Qualysec for comprehensive and reliable Cloud Penetration Testing in India. Also, their penetration testing guide will help you make informed decisions and understand the various factors that impact the cost. Hence, protect your assets and enhance your security posture by choosing us.
Key Features
- Over 3,000 tests to detect and root out all types of vulnerabilities.
- Capable of detecting business logic errors and gaps in security.
- Ensures zero false positives through manual pen testing.
- Compliance-specific scans for SOC2, HIPAA, ISO27001, and other relevant standards.
- Provides in-call remediation assistance from security experts
Qualysec is a recognized AWS penetration testing provider. They offer comprehensive penetration testing services tailored specifically for AWS environments, ensuring the security of your cloud infrastructure and applications. Their expertise, tools, and methodologies can help organizations identify vulnerabilities and implement effective security measures.
Conclusion
AWS penetration testing in is an essential practice to identify and mitigate potential security risks within your cloud infrastructure. By following the best practices mentioned above, obtaining proper authorization, defining clear goals, simulating real-world attack scenarios, and leveraging AWS security tools, you can enhance the security of your AWS resources and protect your valuable data. Remember, AWS penetration testing is an ongoing process. Stay vigilant, adapt to the evolving threat landscape, and continuously test, assess, and strengthen your AWS security to safeguard your organization’s digital assets.
Qualysec has a successful track record of serving clients across a range of industries such as IT. Their expertise has helped clients identify and mitigate vulnerabilities, prevent data breaches, and improve their overall security posture.
When it comes to comprehensive cloud penetration testing Qualysec is the organization to go with. Their cost of VAPT guide helps clients make informed decisions by understanding the various factors that affect the cost by clicking here.












































































































































































































































































































































































































































































































































































































































































































0 Comments