In today’s interconnected world, where technology plays a pivotal role in our lives, ensuring the security of our digital assets has become more critical than ever. The prevalence of cyber threats and the potential for devastating consequences have made security testing an indispensable component of software development. In this blog post, we will delve into the importance of security testing, explore five different types of security testings, discuss the six principles of security testing, highlight essential considerations while selecting an external security testings vendor, and provide an overview of the common tools used for security testing.
Why is Security Testing important?
The significance of security testing cannot be overstated. It serves as a proactive measure to identify vulnerabilities, assess risks, and ensure the robustness of a
system’s security posture. Here are some key reasons why security testing is crucial:
- Protecting sensitive data: Security testing helps safeguard sensitive user data, such as personal information, financial details, and login credentials, from unauthorized access, breaches, or theft.
- Maintaining user trust: By conducting thorough security testing, organizations demonstrate their commitment to protecting their users’ data and maintain their trust. A security breach can lead to severe reputational damage and loss of customer confidence.
- Compliance with regulations: Many industries, such as finance, healthcare, and e-commerce, are subject to regulatory requirements that mandate robust security measures. Security testing ensures compliance with these regulations and helps avoid legal consequences.
- Preventing financial losses: Security breaches can result in significant financial losses due to the costs associated with incident response, recovery, legal ramifications, and potential lawsuits. Conducting security testing minimizes the risk of such financial implications.
- Mitigating business disruption: A security incident can disrupt normal business operations, leading to downtime, loss of productivity, and reputational harm. Regular security testing helps identify vulnerabilities and address them before they can be exploited.
4 Basic Types of Security Testings
- Vulnerability Scanning: Vulnerability scanning involves using automated tools to detect known vulnerabilities in software, networks, or systems. It identifies weaknesses that could potentially be exploited by attackers, such as unpatched software, misconfigurations, or weak encryption.
- Penetration Testing: Penetration testing, commonly known as “ethical hacking,” simulates real-world attacks to assess the security of a system. Skilled security professionals attempt to exploit vulnerabilities to gain unauthorized access, providing organizations with valuable insights into potential weaknesses and recommendations for remediation.
- Risk Assessment: Risk assessment involves identifying and evaluating potential risks and their impact on the system’s security. It helps prioritize security measures by quantifying risks based on factors such as the probability of occurrence, potential damage, and mitigation strategies.
- Security Auditing: Security auditing entails a comprehensive evaluation of an organization’s security controls, policies, and procedures. It verifies compliance with security standards, identifies gaps, and provides recommendations for enhancing security posture.
Basic Principles of Security Testings
- Confidentiality: Security testing ensures that sensitive data remains confidential and protected from unauthorized access or disclosure.
- Integrity: It verifies the integrity of data by preventing unauthorized modifications, and ensuring that information remains accurate, reliable, and untampered.
- Availability: Security testing ensures that systems and data are accessible and available to authorized users while defending against denial-of-service attacks and other disruptions.
- Authentication: Security testing verifies the effectiveness of authentication mechanisms to ensure that only authorized individuals can access protected resources.
- Authorization: It assesses the authorization mechanisms to ensure that users have appropriate access rights and privileges, preventing unauthorized actions.
- Non-Repudiation: Security testing verifies that actions or transactions within a system can be traced back to the individuals responsible, preventing denial of involvement.
Security Testings Types:
In addition to the principles and techniques mentioned above, various types of security testing. These types automate different testing approaches and provide insights into potential vulnerabilities. Some widely used security testing types include:
- Static Application Security Testing (SAST): SAST tools analyze source code or compiled binaries to detect security vulnerabilities without executing the software. They help identify issues such as insecure coding practices, known software vulnerabilities, or misconfigurations.
- Dynamic Application Security Testing (DAST): DAST tools examine running applications from the outside, simulating attacks to identify vulnerabilities. They help identify common web application security issues, such as SQL injection, cross-site scripting (XSS), or insecure direct object references.
How to Opt for an External Security Testing Service Provider
When selecting an external security testings vendor, it is crucial to consider the following factors
- Expertise and Experience: Assess the vendor’s expertise in security testing, including their knowledge of industry best practices, certifications, and prior experience in conducting similar assessments. Look for vendors with a strong track record in security testing and a deep understanding of your industry’s specific requirements.
- Methodologies and Approach: Evaluate the vendor’s testing methodologies, frameworks, and tools they employ. Ensure they align with your organization’s specific requirements and adhere to recognized industry standards. A thorough and systematic approach to security testing is essential for identifying potential vulnerabilities comprehensively.
- Reporting and Documentation: Review sample reports from the vendor to assess their clarity, depth, and comprehensiveness. Understand how they communicate findings, recommendations, and potential risks. Clear and actionable reports will help your organization prioritize and address identified vulnerabilities effectively.
Tools Used for Security Testings
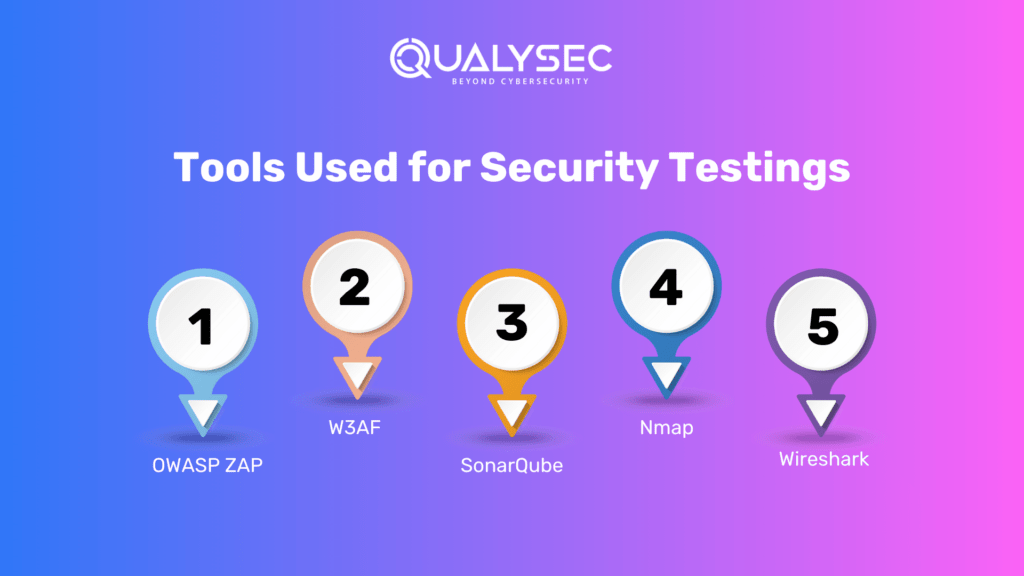
There is a wide range of tools used in security testings, which encompass activities such as vulnerability scanning, code analysis, penetration testing, and security audits. To gain a better understanding of the tools utilized in security testings, we have compiled a list of commonly used tools:
- OWASP ZAP: OWASP ZAP is a tool used for assessing and managing application vulnerabilities in web applications. It is popular among developers for building applications and security teams for conducting internal security assessments.
- W3AF: W3AF is a framework specifically designed for web application attack and audit purposes. It offers extensibility through modules that are easily configurable and extendable. The framework can be used both manually and in an automated manner using its Python API.
- SonarQube: SonarQube, developed by SonarSource, is an open-source platform that facilitates continuous code quality inspection. It conducts automatic reviews with static code analysis to identify bugs, code smells, and security vulnerabilities across over 20 programming languages.
- Nmap: Nmap is an open-source network administration tool primarily used for monitoring network connections. It allows the scanning of large networks and aids in auditing hosts, services, and intrusion detection.
- Wireshark: Wireshark is a network traffic analyzer and monitoring software that provides visibility into the flow of network traffic within your system.
These tools serve as valuable assets in the security testing process, enabling professionals to identify and address potential vulnerabilities in software applications and network infrastructure.
Qualysec, The best Service provider for Security Testing
Security Testing requires expertise and experience to deliver accurate and reliable results. At Qualysec, we stand out as a leader in the field of penetration testing. Qualysec’s team comprises highly skilled professionals with advanced certifications and a proven record of accomplishment. We combine our deep knowledge of cybersecurity with innovative tools and methodologies to provide comprehensive testing services. By choosing Qualysec, you can be confident in receiving top-quality penetration testing that meets your specific needs.
Qualysec follows a comprehensive methodology that involves a combination of manual and automated testing techniques to ensure maximum coverage of vulnerabilities. They also provide detailed reports that include a prioritized list of vulnerabilities, along with recommendations for remediation.
They work closely with organizations to understand their unique needs.
Qualysec offers numerous services which include:
- Web App Pentesting
- Mobile App Pentesting
- API Pentesting
- Cloud Security Pentesting
- IoT Device Pentesting
- AI /ML Pen-testing
The methodologies offered by Qualysec are particularly beneficial for businesses that must adhere to industry rules or prove their dedication to security to clients and partners. So, by opting for Qualysec as a Security Testing Service provider, businesses can ensure the safety of their Network and Applications
Hence, choose Qualysec for a comprehensive and reliable vulnerability scanning report. Also, their penetration testing guide will help you make informed decisions and understand the various factors that impact the cost. Hence, protect your assets and enhance your security posture by choosing us.
Key Features
- Over 3,000 tests to detect and root out all types of vulnerabilities.
- Capable of detecting business logic errors and gaps in security.-
- Ensures zero false positives through manual pen testing.
- Compliance-specific scans for SOC2, HIPAA, ISO27001, and other relevant standards.
- Provides in-call remediation assistance from security experts
Conclusion
Security testings plays an integral role in safeguarding digital assets. Protecting sensitive data, and mitigating the risks associated with cyber threats. By embracing different types of security testing, adhering to fundamental principles, and leveraging appropriate tools. Organizations can fortify their security posture and foster user trust.
Ensuring the security and performance of your application is crucial, and security testing plays a vital role in achieving that. While many software companies and testers perceive it as a complex undertaking, adopting the right approach can lead to success. Qualysec’s primary objective is to simplify security for you. Connect with us, and we will ensure your protection against hackers.
Check out our recent blog on What is Web Application Security Testing
Frequently Asked Questions
Q: What is security testing?
A: It is a process of assessing the vulnerabilities and weaknesses in a system to ensure its resilience against potential threats and attacks.
Q: Why is security testing important?
A: It helps identify and address security flaws, protecting systems from unauthorized access, data breaches, and other cyber threats. It ensures the confidentiality, integrity, and availability of sensitive information.
Q: What are the common types of testing?
A: Common types of security testing include penetration testing, vulnerability scanning, security code reviews, security audits, and risk assessments.
Q: What is the goal of security testings?
A: The goal is to uncover vulnerabilities, assess their potential impact, and provide recommendations to improve the security posture of a system or application.
Q: Who performs security testings?
A: It is typically conducted by specialized security professionals, such as ethical hackers, security consultants, or dedicated security teams within organizations.

















































































































































































































































































































































































































































































































































































































































































































0 Comments