From the past few decades, the world of information technology is advancing with lightening fast pace. One of such advancements is the cloud technology. Cloud technology turned the traditional way of serving the consumers with a information technology product all the way around! With cloud technology, came the rise of SaaS based applications and software. SaaS in the market right now do not satisfy the consumers. Moreover, current SaaS based tech does not satisfy the purpose and need of consumers as well. So, here we are with another blog for the day. Namely, SaaS application penetration testing guide!
But before we begin with procedure for SaaS app testing, let us give a brief about SaaS technology.
What is SaaS Application Penetration Testing ?
SaaS is an abbreviation. It stands for ‘Software as a Service’. SaaS technology is a software distribution scheme which is heavily dependent upon the cloud computing technology. It was initially launched by Salesforce company for their CRM (Customer Relationship Management) platform around late 90’s. Even though, SaaS became popular in the information technology market around the early or mid 2000’s.
SaaS technology is essentially a use over the internet product. Mostly, with a monthly charge for access. SaaS products are usually available to use from mobile application or desktop software or website access. With SaaS technology, the users no longer are required to install and run the software or applications on their devices. They can directly access the services over the internet.
SaaS technology based services will work as long as there is internet connectivity to the device accessing the information through SaaS company/product.
So now let us begin with the SaaS application penetration testing.
How to start the SaaS Application Penetration Testing?
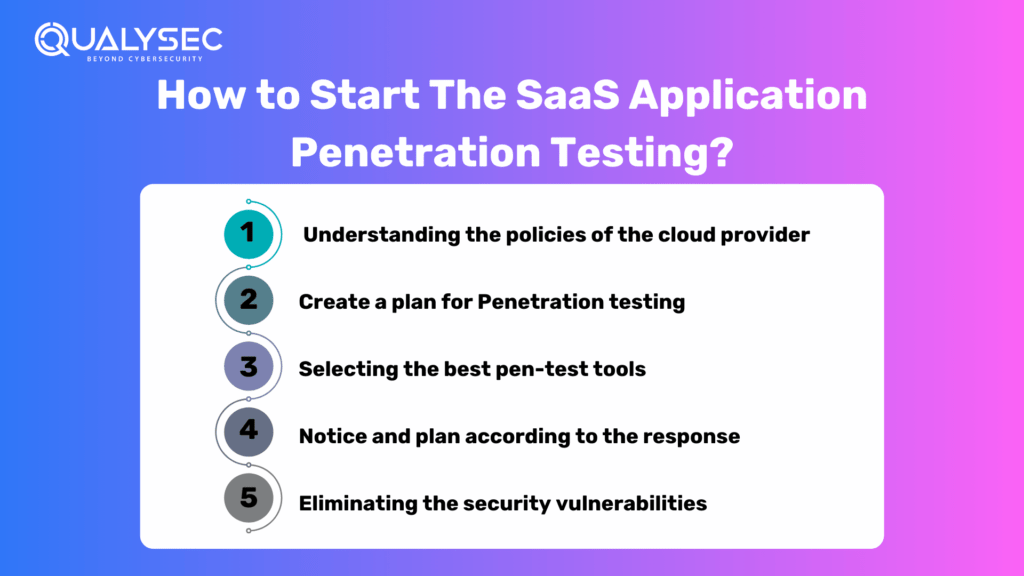
1) Understanding the policies of the cloud provider-
Notifying the provider about a penetration test is a must in many cases. So, it places a restriction on what actually can be done while pen-testing. So, if an application is running on public cloud and you want to pen-test it, you will have to conduct some research regarding the cloud provider’s recommendations. Otherwise, sometimes not following these recommendations can cause trouble. Moreover, your pen-test can even look like a DDoS attack, so it may shut down your account. Every cloud provider usually check for any abnormalities in their infrastructures. Moreover, in many instances, the cloud service has automated systems to shut down the system without any warning if it perceives a DDoS attack.
Moreover, you penetration test can eat up a lot of resources, so and so, that it can affect others on the cloud. Public clouds are multitenant. And therefore all resources between the tenants should be managed appropriately. Hence, if your pen-testing is affecting the other users on the cloud, you might receive some form of backlash. Therefore, you have to understand the policies of the public cloud provider thoroughly before conducting any such procedures.
2) Create a plan for Penetration testing-
A SaaS application penetration testing plan must include the following parameters:
a) User interfaces: Identify and include user interfaces in the specific application
b) Network access: Examine how well the network safeguards the application and data
c) Data: Check how the testers will test the data as it passes through the application and into the database
d) Virtualization: Determine how well virtual machines can separate your workload
e) Automation: Select automated tools
f) Regulation: Know the laws and regulations you need to adhere to within the application or database
g) Approach: Decide if the inclusion of the application admins is necessary or not.
3) Selecting the best pen-test tools-
An abundance of penetration testing tools are available in the testing market. It is common to use tools you haven on your campus, but now testing tools based on cloud services are also cloud-enabled. These cloud-based testing tools are more cost efficient and easily available for portable access and use. Moreover, these cloud-enabled testing tools do not require a huge amount of hardware. So it can directly be used for its main purpose i.e., imitate a real-time, actual cyber-attack.
4) Notice and plan according to the response-
While execution of penetration testing, observe the following parameters:
a) Human response- Don’t inform the admin and users about the test, Then, observe their response to the test. This way, the response will be more interesting and insightful. Many may react by just shutting the system down, while others may diagnose the issue first, before identifying and elevating the threat.
b) Security system’s automated response- Observe how the security systems of the cloud responds to the penetration test. The actions of the security should be varied. From merely blocking the IP address of pen-test origin to shutting the entire application down: every action will have their significance in the protection from possible future attack.
Therefore, observing the human and automated responses is a must. This way, you can get a more clear image of the security loopholes and defecta in the cloud’s system.
5) Eliminating the security vulnerabilities-
Vulnerabilities found while pen testing cloud-based applications are mostly from the following:
a) XXXXX API based access to application
b) API access after 8-12 attempts
c) Improper isolation of workload by VM
d) Automated passwords generation cracking the app passwords
e) DNS disabling enables VPN access to the cloud
f) Incompliance of encryption with new regulations
and more.
Therefore, look for clear indication of security issues and document and solve them ASAP!
Conclusion
Finally, we end with our blog for SaaS application penetration testing guide. We sincerely hope that we were useful to you for understanding this topic!
We at QualySec conduct penetration’s testing for mobile applications, SaaS application and many more; with our expert teams and state of the art pen-testing tools.
With QualySec, you can achieve all the above mentioned benefits and much more. QualySec is India’s best QA and pen-testing service provider.



















































































































































































































































































































































































































































































































































































































































































































0 Comments