Web applications remain a cornerstone of modern business operations, enabling critical functionalities and services for users. However, their exposure to the internet makes them prime targets for cyberattacks. Web application penetration testing continues to be a vital process for identifying vulnerabilities, ensuring robust security, and safeguarding sensitive data. This updated guide incorporates the latest advancements and practices in 2025 while retaining the foundational knowledge from previous years.
What is Web Application Penetration Testing?
Web application penetration testing, often called web app pen testing, is a systematic process of evaluating the security of a web application by simulating real-world attacks. The goal is to uncover vulnerabilities, weaknesses, and misconfigurations that malicious actors could exploit to compromise the application or its infrastructure.
Key Aspects of Web App Penetration Testing in 2025:
- Scoping: Define the scope of the test, including target applications, functionalities, and potential entry points. In 2025, scoping has become more dynamic, often incorporating AI-driven tools to identify high-risk areas.
- Reconnaissance: Gather information about the target, such as technologies used, architecture, and potential attack vectors. Advanced reconnaissance now includes analyzing AI/ML-driven components and API ecosystems.
- Vulnerability Assessment: Identify security weaknesses like SQL injection, cross-site scripting (XSS), insecure APIs, and misconfigurations. In 2025, vulnerabilities in AI/ML models and serverless architectures are also prioritized.
- Exploitation: Safely exploit vulnerabilities to assess their impact and validate their existence. Modern exploitation techniques now account for zero-day vulnerabilities and advanced persistent threats (APTs).
- Reporting: Document findings, risks, and remediation steps in a comprehensive report. Reports in 2025 often include interactive dashboards and AI-generated remediation recommendations.
Explore our Vulnerability Assessment Services here!
Importance of Web Application Penetration Testing in 2025
Web app penetration testing remains critical for several reasons:
- Security Assurance: Ensures web applications are developed and maintained with security in mind, reducing the risk of data breaches and cyberattacks.
- Compliance: Mandated by regulations like PCI DSS, GDPR, and newer frameworks like the Global Cybersecurity Compliance Act (GCCA) introduced in 2024.
- Risk Mitigation: Proactively identifying vulnerabilities minimizes financial and reputational damage from attacks.
- Continuous Improvement: Provides actionable insights to enhance the security posture of web applications over time.
- AI and Automation Integration: With the rise of AI-driven applications, penetration testing now includes evaluating AI model security and ensuring ethical AI usage.
Preparation for Web Application Penetration Testing in 2025
Preparation remains a cornerstone of effective penetration testing. Here’s how the process has evolved:
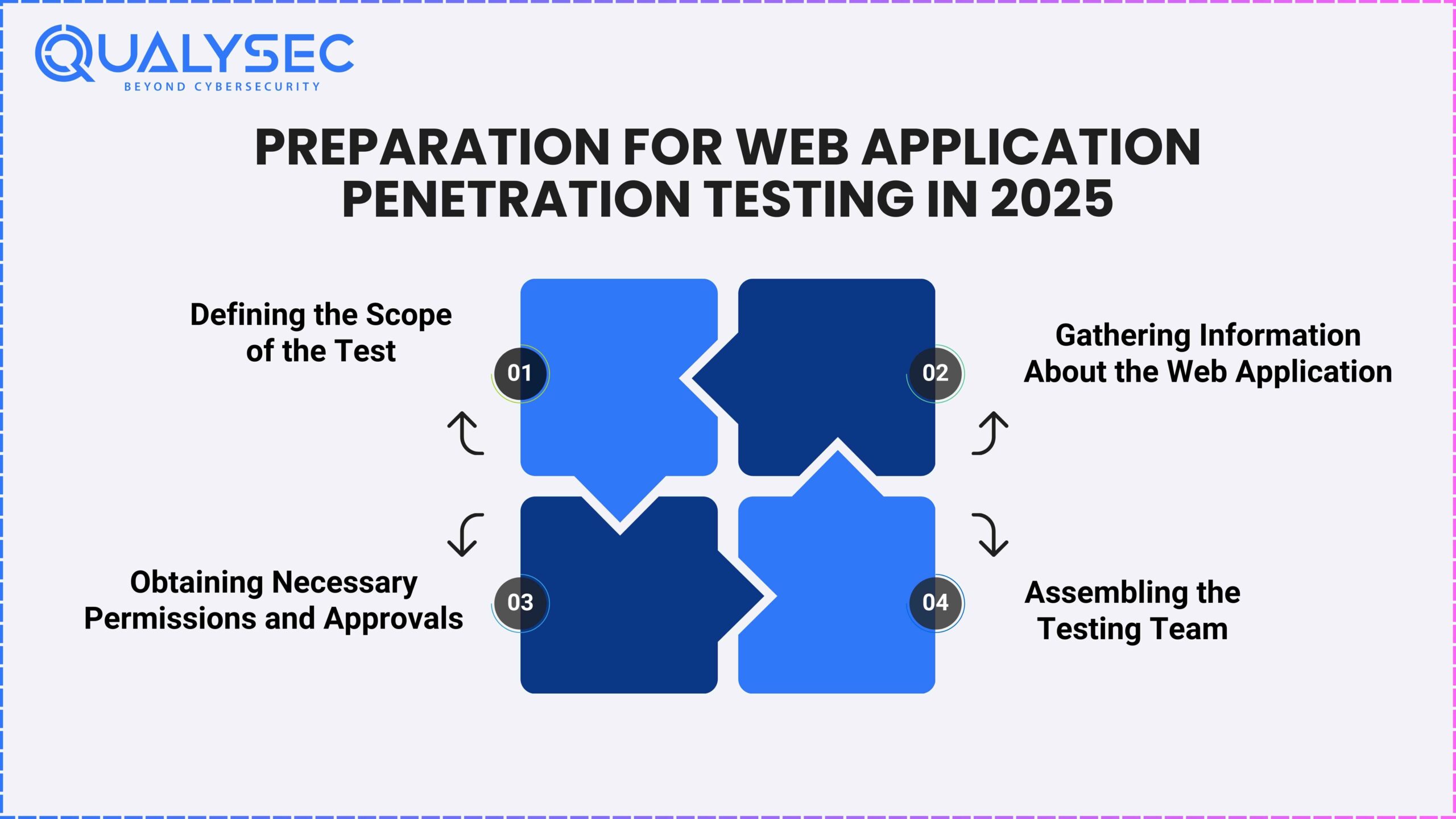
1. Defining the Scope of the Test
- Scope Definition: Clearly outline objectives, target applications, and testing depth (black-box, gray-box, or white-box). In 2025, scoping often includes AI-driven risk assessment tools to prioritize high-impact areas.
- Legal and Ethical Considerations: Ensure compliance with updated laws like the Cybersecurity Transparency Act (CTA) and ethical guidelines for AI testing.
2. Gathering Information About the Web Application
- Reconnaissance: Use advanced tools to identify technologies, APIs, and AI/ML components. In 2025, reconnaissance includes analyzing serverless architectures and edge computing setups.
- Vulnerability Scanning: Leverage AI-powered scanners to detect vulnerabilities in real-time, including those in AI models and APIs.
“Related Content : Read our guide to What Is Vulnerability Scanning in Cyber Security?”
3. Obtaining Necessary Permissions and Approvals
- Legal Authorization: Secure written approval from stakeholders, ensuring compliance with global and regional cybersecurity laws.
- Communication: Establish clear communication channels and incident response protocols, especially for AI-driven applications.
4. Assembling the Testing Team
- Skillset: Include experts in AI/ML security, API testing, and cloud-native architectures.
- Tools and Resources: Equip the team with advanced tools like AI-driven penetration testing platforms and cloud security assessment tools.
Process of Web Application Penetration Testing in 2025
The testing process has evolved to address modern threats and technologies:
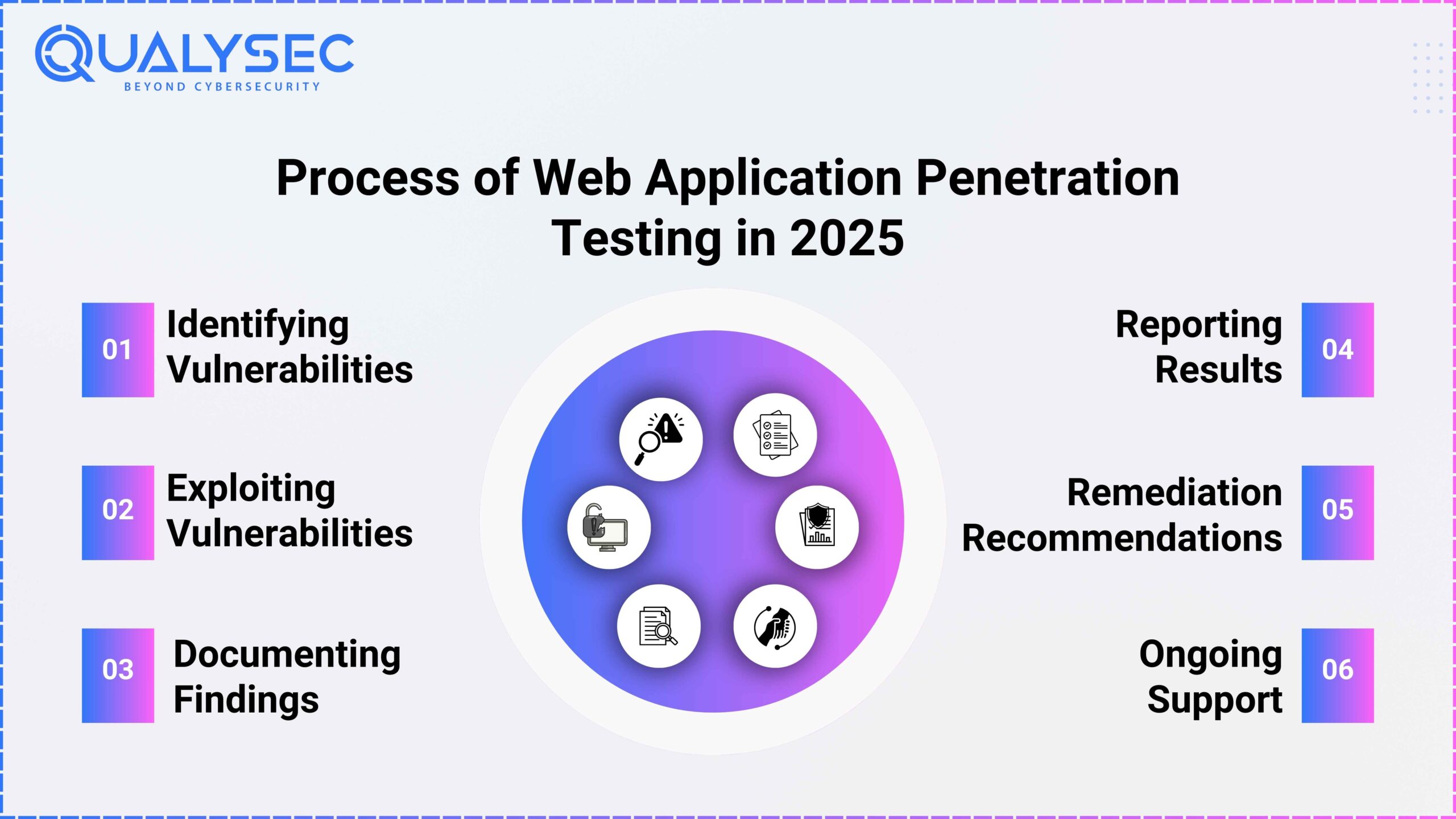
1. Identifying Vulnerabilities
- Manual Testing: Simulate real-world attacks, focusing on AI/ML model vulnerabilities, API security, and serverless architectures.
- Automated Scanning: Use AI-driven tools to detect vulnerabilities in real-time, including zero-day threats.
2. Exploiting Vulnerabilities
- Controlled Exploitation: Safely exploit vulnerabilities, ensuring no disruption to live systems. In 2025, this includes testing AI model robustness and API integrity.
- Impact Assessment: Evaluate the potential impact on data confidentiality, integrity, and availability, considering AI-driven decision-making processes.
3. Documenting Findings
- Comprehensive Documentation: Record vulnerabilities with detailed technical descriptions, visual evidence, and AI-generated risk assessments.
- Risk Assessment: Use updated CVSS v4.0 for scoring vulnerabilities, incorporating AI-specific risk factors.
4. Reporting Results
- Formal Report: Include an executive summary, technical findings, and AI-driven remediation recommendations.
- Prioritization: Highlight critical vulnerabilities, especially those in AI/ML models and APIs.
Download a sample pen test report here!
5. Remediation Recommendations
- Provide actionable steps for fixing vulnerabilities, including code fixes, configuration changes, and AI model retraining.
6. Ongoing Support
- Collaborate with development teams to validate fixes and retest applications, ensuring long-term security.
Types of Web Application Pen Testing
Web application penetration testing can be categorized into three main types: black box testing, white box testing, and gray box testing. Each type has its own approach, advantages, and limitations. Here’s an overview of each type and a comparison of their characteristics:
1. Black Box Testing:
Approach:
- No Prior Knowledge: Testers have no prior knowledge of the internal workings, architecture, or source code of the web application.
- Simulates External Attacks: This approach simulates how an external attacker with no inside information would attempt to compromise the application.
- Focus on Behavior: Testers focus on identifying vulnerabilities by interacting with the application, examining inputs, and analyzing responses.
Advantages:
- Realistic Simulation: It mimics the perspective of an external attacker, providing a real-world assessment.
- Independence: Testers do not rely on internal documentation or source code access, making it suitable for security assessments by external parties.
- Objectivity: Assessments are unbiased, as testers approach the application without preconceived notions.
Limitations:
- Limited Visibility: Testers may miss certain vulnerabilities that require knowledge of the application’s internal structure.
- Incomplete Assessment: The scope of the test may be limited, and some vulnerabilities may go undetected.
Read our guide to Black Box Penetration Testing.
2. White Box Testing:
Approach:
- Full Knowledge: Testers have complete access to the internal architecture, source code, and database schema of the web application.
- In-Depth Analysis: Testers can perform code review, architecture analysis, and design review to identify vulnerabilities.
- Thorough Examination: Assessors can pinpoint the exact location of vulnerabilities and assess their potential impact.
Advantages:
- Comprehensive Assessment: Testers can identify vulnerabilities that are difficult to find with other testing approaches.
- Precise Remediation: Vulnerabilities can be precisely located, enabling developers to fix issues efficiently.
- Code Review: Helps in identifying security issues related to coding practices and logic flaws.
Limitations:
- Resource-Intensive: Requires access to source code and significant time and expertise for an in-depth analysis.
- May Not Simulate External Threats: While it assesses the application thoroughly, it may not reflect the tactics of external attackers.
Read our guide to White Box Penetration Testing.
3. Gray Box Testing:
Approach:
- Partial Knowledge: Testers have limited information about the web application, typically a combination of external knowledge and some internal insights.
- Balanced Perspective: Combines elements of both black box and white box testing, striking a balance between external and internal viewpoints.
- Targeted Assessment: Testers focus on areas of the application where vulnerabilities are likely to occur.
Advantages:
- More Realistic Than White Box: Offers a more realistic assessment compared to white box testing while providing some internal context.
- Efficient Assessment: Allows testers to focus on areas of the application that are more likely to be vulnerable.
- Cost-Effective: Generally more cost-effective than full white box testing.
Limitations:
- Limited Internal Knowledge: Testers may still miss vulnerabilities that require deeper internal understanding.
- Scope Can Vary: The level of internal knowledge can vary, making it important to clearly define the scope.
Read our guide to Gray Box Penetration Testing.
Comparison of the Three Types:
|
Criteria |
Black Box Testing |
White Box Testing |
Gray Box Testing |
|---|---|---|---|
|
Prior Knowledge |
None |
Full |
Partial |
|
Perspective |
External Attacker |
Internal Assessment |
Balanced |
|
Scope |
Limited |
Comprehensive |
Variable |
|
Detection Efficiency |
Moderate |
High |
Moderate to High |
|
Resource Requirements |
Low |
High |
Moderate |
|
Realism |
Realistic (External) |
Realistic (Internal) |
Balanced Realism |
The choice of which type of web application penetration testing to use depends on factors such as the goals of the assessment, available resources, and the desired level of insight into the application’s security. In many cases, organizations may opt for a combination of these testing types to achieve a more holistic view of their web application’s security posture.
Best Web Application Penetration Testing Service Provider
Qualysec Technologies
Qualysec is a cybersecurity company founded in 2020 that has quickly become one of the most trusted names in the industry in Los Angeles. The company provides services such as VAPT, security consulting, and incident response.
Although Qualysec’s Oppressional office is not situated in Los Angeles, Qualysec’s extensive knowledge and expertise in cybersecurity testing services have earned a reputation among the best Web Application Penetration Testing Service Provider.
Technicians at Qualysec can detect flaws that fraudsters could abuse. After these flaws have been found, Qualysec collaborates with the organization to establish a plan to address them and boost the company’s overall security posture. Among the several services available are:
- Web App Pentesting
- Mobile App Pentesting
- API Pentesting
- Cloud Security Pentesting
- IoT Device Pentesting
- AI /ML Pen-testing
The Qualysec team is made up of seasoned offensive specialists and security researchers who collaborate to give their clients access to the most recent security procedures and approaches. They provide VAPT services including web application VAPT using both human and automated equipment.
In-house tools, adherence to industry standards, clear and simple findings with reproduction and mitigation procedures, and post-assessment consulting are all features of Qualysec’s offerings.
The solution offered by Qualysec is particularly beneficial for businesses that must adhere to industry rules or prove their dedication to security to clients and partners. So, by doing routine penetration testing, businesses may see weaknesses and fix them before thieves attack them.
As a result, Qualysec is rated as the best of the best Web Application Penetration Testing Service Provider.
What Are the Best Tools for Web App Pentesting?
Web application penetration testing relies on a variety of tools to identify vulnerabilities and assess the security of web applications. These tools assist in tasks such as scanning, vulnerability assessment, exploitation, and reporting. Here’s an overview of popular tools, guidance on choosing the right tool for the job, and examples of tool usage:
Overview of Popular Tools Used During Website Penetration Testing:
1. Burp Suite:
- Category: Proxy and Scanner
- Description: Burp Suite is a comprehensive web vulnerability scanner and proxy tool. It helps testers intercept, analyze, and modify HTTP requests and responses. It also provides automated scanning for common web application vulnerabilities.
2. OWASP ZAP (Zed Attack Proxy):
- Category: Proxy and Scanner
- Description: OWASP ZAP is an open-source security tool for finding vulnerabilities in web applications during development and testing. It offers automated scanners and various tools for manual testing.
3. Nessus:
- Category: Vulnerability Scanner
- Description: Nessus is a powerful network vulnerability scanner that can also scan web applications for vulnerabilities. It provides detailed reports and helps identify weaknesses in both the web server and application code.
4. Nmap:
- Category: Network Scanner
- Description: Nmap is a network scanning tool that can be used to discover open ports and services on web servers. This information is valuable for identifying potential entry points.
5. Metasploit:
- Category: Exploitation Framework
- Description: Metasploit is an exploitation framework that helps testers identify and exploit vulnerabilities. It includes a wide range of exploits and payloads for various web application vulnerabilities.
6. Sqlmap
- Category: SQL Injection Scanner
- Description: Sqlmap is a specialized tool for detecting and exploiting SQL injection vulnerabilities in web applications. It automates the process of identifying and exploiting SQL injection flaws.
7. DirBuster:
- Category: Directory and File Brute-Forcer
- Description: DirBuster is used for brute-forcing directories and files on web servers. It helps discover hidden or unlinked resources that may contain sensitive information.
How to Choose the Right Tool for the Job:
Choosing the right tool for web application penetration testing depends on several factors:
- Scope: Consider the scope of your testing. Some tools are better suited for specific types of vulnerabilities, so choose accordingly.
- Expertise: Assess your team’s expertise. Some tools are user-friendly, while others require advanced skills to operate effectively.
- Target Application: Understand the technologies and platforms used by the web application. Some tools specialize in certain technologies.
- Budget: Consider the cost of the tool and whether it fits within your budget.
- Reporting: Evaluate the reporting capabilities of the tool. A good tool should generate comprehensive reports that are easy to understand.
Best Practices for Web Application Penetration Testing
Web application penetration testing is a critical process for identifying and mitigating security vulnerabilities. To ensure the effectiveness and ethical conduct of these tests, it’s important to follow best practices. Here are some key best practices for web application penetration testing:
1. Testing in a Safe Environment:
- Use Controlled Test Environments: Always perform penetration testing in a controlled, isolated, and non-production environment. This ensures that the testing activities do not disrupt or harm the live application or its users.
- Data Protection: If real data is used during testing, ensure sensitive information is properly anonymized or obfuscated to protect user privacy and comply with data protection regulations.
2. Following Ethical Guidelines:
- Obtain Proper Authorization: Obtain written authorization from the owner or responsible party of the web application before conducting any testing. Clearly define the scope, rules of engagement, and limitations in the authorization document.
- Adhere to Legal and Regulatory Requirements: Ensure that the testing activities comply with applicable laws, regulations, and industry standards. Consider data protection laws, intellectual property rights, and contractual agreements.
- Do No Harm: Conduct testing with the primary goal of identifying and mitigating vulnerabilities, not causing harm. Avoid destructive actions that can negatively impact the application, data, or users.
3. Communicating Effectively with Stakeholders:
- Engage with Stakeholders: Maintain open and effective communication with all relevant stakeholders, including the application owner, development team, and IT staff. Keep them informed about the testing process and progress.
- Clear Reporting: Provide comprehensive and clear reports that detail the findings, risk assessments, and recommended remediation steps. Reports should be accessible and understandable to both technical and non-technical stakeholders.
- Collaboration: Collaborate with development teams to help them understand and prioritize identified vulnerabilities. Provide guidance on remediation and offer post-testing support.
4. Staying Up-to-Date with Industry Developments:
- Continual Learning: Cybersecurity is an ever-evolving field. Stay up-to-date with the latest security threats, attack techniques, and mitigation strategies. Attend training, conferences, and workshops regularly.
- Tool Familiarity: Keep knowledge of penetration testing tools and methodologies current. Tools are regularly updated to address new vulnerabilities and technologies.
- Industry Standards: Follow industry standards and best practices, such as those provided by OWASP (Open Web Application Security Project) and NIST (National Institute of Standards and Technology).
- Regular Testing: Schedule regular penetration tests to assess the evolving security posture of your web applications. New features, code changes, and updates can introduce new vulnerabilities.
By adhering to these best practices, organizations can conduct web application penetration testing effectively, ethically, and safely. This not only helps identify and mitigate vulnerabilities but also fosters a culture of security consciousness within the organization, ultimately enhancing the overall security of web applications.
Book a free consultation with Qualysec’s Cybersecurity Experts here.
Conclusion
Web application penetration testing is an essential component of modern cybersecurity strategies, allowing organizations to proactively identify and mitigate vulnerabilities in their web applications. In this comprehensive guide, we’ve covered various aspects of web application penetration testing, including preparation, testing types, and tools.
Web application security is an ongoing process, and penetration testing should be integrated into the development lifecycle to ensure continuous improvement. Regular testing, timely remediation of vulnerabilities, and collaboration between security teams and developers are key to maintaining a strong security posture.
By following best practices and staying updated on emerging threats and technologies, organizations can protect their web applications from potential cyber threats and provide a safer online experience for their users.
Qualysec has a successful track record of serving clients and providing cybersecurity services across a range of industries, such as IT. Their expertise has helped clients identify and mitigate vulnerabilities, prevent data breaches, and improve their overall security posture.
When it comes to comprehensive cybersecurity audits, Qualysec is the organization to go with. Their cost of VAPT guide including the web app VAPT helps clients make informed decisions by understanding the various factors that affect the cost.



















































































































































































































































































































































































































































































































































































































































































































0 Comments