Key Takeaways
- An IT security audit is a planned review of your systems, networks and policies in order to discover loopholes and ensure compliance- before your attackers discover them first.
- In 2024, the average data breach cost in the world was 4.88 million and proactive auditing is one of the most lucrative security investments a company can have.
- IT security audits are of 8 different types, not one type fits the majority of organizations.
- An effective IT security audit adheres to a 7-steps procedure where scoping is the initial step emphasizing the need to monitor and document the results obtained and confirmed remediation at each stage.
- IT security audits cannot be equated with penetration testing or vulnerability testing – a knowledge of the difference is what will help you know which of the two is the one that your business really requires.
Introduction
A set it and forget it security stance is a disaster in an environment whereby cyber threats are rapidly advancing faster than the software they are designed to prevent. According to the IBM Cost of a Data Breach Report 2024, the average cost of a data breach was at its highest point with many intrusions in 2024 at a staggering 4.88 million, worldwide. In the case of Indian businesses, it was 19.5 crore on average (= 23 million) per incident. However, most of these attacks took advantage of the gaps that could have been detected and reported by a daily IT security audit check months before.
To a more contemporary business, an audit is not merely a matter of uncovering vulnerabilities, but reaffirming resilience to social engineering by AI and more advanced attacks on the supply chain. This roadmap disaggregates a high-performance approach to defend your assets and at the same time have your business agile, compliant, and ahead of the imminent digital risks.
What is an IT Security Audit?
An IT security audit is a thorough and methodical analysis of computer systems, networks, applications, and security policies of an organization – which aim to determine their vulnerabilities, determine the level of control they currently have, and also detect whether they are meeting the industry regulations and their own standards.
In contrast to a one-time fix, a security audit provides an assessment of the entire picture of your security stance in five domains, including physical infrastructure, software and applications, network architecture, human and process controls, and regulatory compliance. This is not only to discover what is broken but to ensure that what was intended to be working is actually working and record the fact.
An IT security audit should be conducted properly to provide responses to the following three questions that any organization must receive answers to:
- How are we weak? – spotting vulnerabilities before they can be exploited by attackers.
- Are Our Defenses Working? -Checking that the defenses on paper are working as intended, rather than on paper.
- Do we comply? — ensure that we are in compliance with GDPR, PCI-DSS, HIPAA, ISO 27001, SOC 2 and other relevant frameworks.
The result is a comprehensive audit report containing findings, risk levels and a prioritized remediation roadmap that security teams, management and auditors can immediately take action on.
Why IT Security Audit is Important?
IT security audits play an important role in ensuring the security and stability of digital systems. Here are some key benefits:
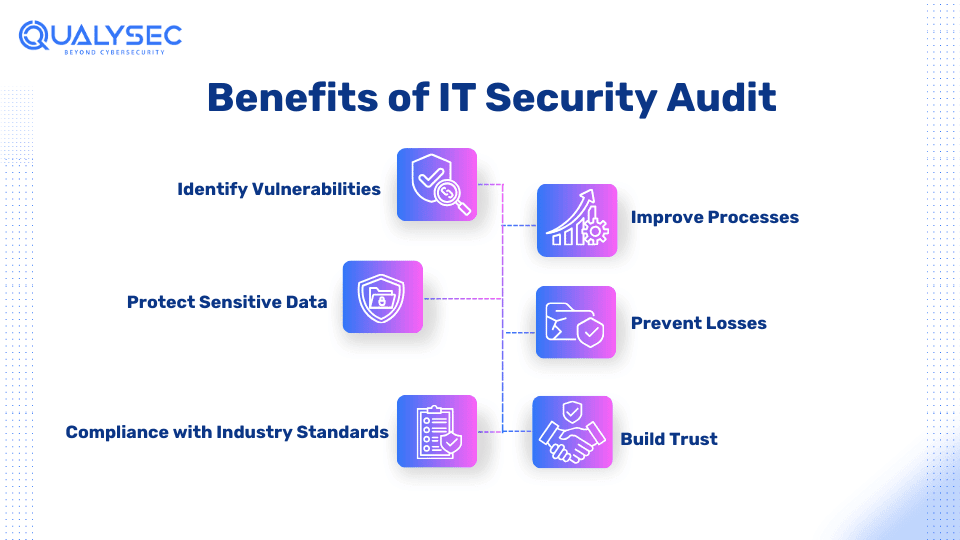
Companies with an active practice of IT security audits always outscore those with no such audits in terms of breach rate, compliance level, and response time. The reason why audits are not negotiable in 2026 is as follows:
1. Detecting Vulnerabilities Before Attackers Find
Audits are performed in a systematic way to reveal Misfits, old software, undue privileges, and unpatched systems, the very points of weakness that attackers seek. The report by Verizon 2024 Data Breach Investigations reports that the use of vulnerabilities as an opening attacker has grown by 180 percent over the last year.
2. Protecting Sensitive Data
Customer records, financial data, intellectual property, and healthcare information are all highly valuable targets. Audits confirm that access controls, encryption standards, and data handling policies are, in fact, safeguarding what they are meant to safeguard, not what is mentioned in the policy document.
3. Ensuring Regulatory Compliance
GDPR, PCI-DSS, HIPAA, SOC 2, and ISO 27001, and India’s DPDP Act 2023 have large fines in the event of non-compliance. The documented evidence that regulators need to identify loopholes in compliance before they lead to fines is enabled by regular audits.
4. Minimizing Financial Risk
The Security audit cost is only a small fraction of the breach average cost. With companies in the banking, health, and e-business sectors where the fines and legal expenses imposed by the regulators and the loss of customers increase the bottom line, the ROI of proactive audit is always provable.
5. Establishing Customer and Partner
It is becoming an obligation in procurement to perform IT security audits regularly, and with certification. Major corporate and financial institutions and customers of the healthcare sector typically demand written audit evidence before commencing or renewing vendor relationships. An audit is not a mere security device, but it is a business indicator.
Case Study: SolarWinds Supply Chain Attack (2020).
The SolarWinds breach revealed how hackers can access thousands of organizations and do it by using one trusted supplier. Having introduced malicious code into the SolarWinds Orion software updates, attackers provided access to approximately 18,000 organizations, including the US governmental agencies. It had an estimated cost of over 100 million dollars in SolarWinds, and the total economic damage to all the victims was in the billions.
Lesson Learned: An audit nowadays should go beyond your perimeter and encompass third-party software supply chains, vendor security testing, and software bill of materials (SBOM) auditing.
IT Security Audit vs Penetration Testing vs Vulnerability Assessment
This is one of the most commonly confused distinctions in cybersecurity and one of the top Google “People Also Ask” questions for this topic. Here is a clear breakdown:
|
Aspect |
IT Security Audit |
Penetration Testing |
Vulnerability Assessment |
|
Purpose |
Evaluate overall security posture and compliance |
Simulate real-world attacks to test defenses |
Identify and catalog known vulnerabilities |
|
Approach |
Systematic review of controls, policies, and systems |
Active exploitation by certified ethical hackers |
Automated scanning against known CVE databases |
|
Output |
Audit report with findings, risk ratings, compliance status |
Report with exploited vulnerabilities and attack paths |
Scan report with severity scores |
|
Who Performs It |
Internal/external auditors, IT audit firms |
Certified ethical hackers (OSCP, CEH, CREST) |
Security teams, automated scanning tools |
|
Frequency |
Annually minimum; quarterly for regulated sectors |
After major releases or at least annually |
Monthly or continuous |
|
Includes Exploitation? |
No — review and testing only |
Yes — controlled exploitation is the core activity |
No — identification only |
|
Compliance Value |
High — directly satisfies audit requirements |
Medium — supports audit evidence |
Medium — supports risk assessment |
Which do you need?
- Board-level risk review or compliance audit, IT Security Audit.
- Understand the distance that an attacker may gain access to your systems – Penetration Testing.
- Quick general scan of obvious vulnerabilities – Vulnerability Assessment.
- Having a comprehensive coverage – the trio of it on a coordinated timetable.
IT Security Audit Methodology
Improving the organization’s security posture is the goal of an effective IT security audit, which is a crucial security procedure. The following is a detailed guide to IT security audit methodology for an organization:
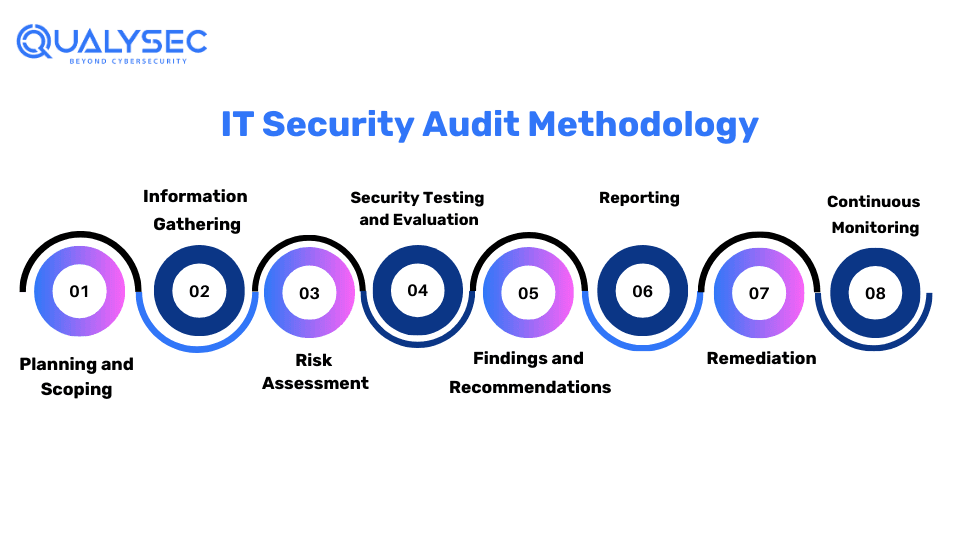
1. Planning and Scoping
The initial stage of the security audit is to make a plan and scope the audit. This part is to find out the range of the audit.
2. Information Gathering
Then, the information gathering will commence. The audit personnel will collect the system information, policies, procedures, and relevant system information. Additionally, the team will be able to find out more about the organization and how it functions thus reducing the time it takes to determine the vulnerabilities.
3. Risk Assessment
The third phase of the security audit carried out is risk assessment. Once the required data has been gathered, the risk assessment is performed. It is done to determine the likelihood and impact of each risk to prioritize mitigation activities.
4. Security Testing and Evaluation
In this stage, the auditor will perform security tests and evaluations according to the comprehensive approach. In which both the automated tools and the manual testing are applied to measure the effectiveness of the vulnerabilities in the different applications, networks, and systems of the company. The test may comprise penetration tests, vulnerability assessments, and other security audit test procedures.
5. Reporting
The report is vital for the organization because it contains information about the security audit. Additionally, the report includes planning and scoping, vulnerabilities discovered, methods used, conclusions, and suggestions. It further assists the technical team in understanding the areas of security that are lacking, the potential consequences, and which practices or recommendations to enhance the organization’s security.
Ever seen a real penetration test report? Well, just click the link below and download one within seconds!
Latest Penetration Testing Report

6. Remediation
If the development team requires assistance mitigating identified vulnerabilities, the service provider assists them online or over consultation calls.
7. Continuous Monitoring
Carry out periodical checks to ensure that all identified vulnerabilities have been tackled and security controls have been implemented accordingly. Include constant monitoring procedures that highlight and address the new threats that emerge.
Types of IT Security Audits
IT security audits are not the same. There is a combination that is required in most organisations that depends on the industry, infrastructure and compliance requirements.
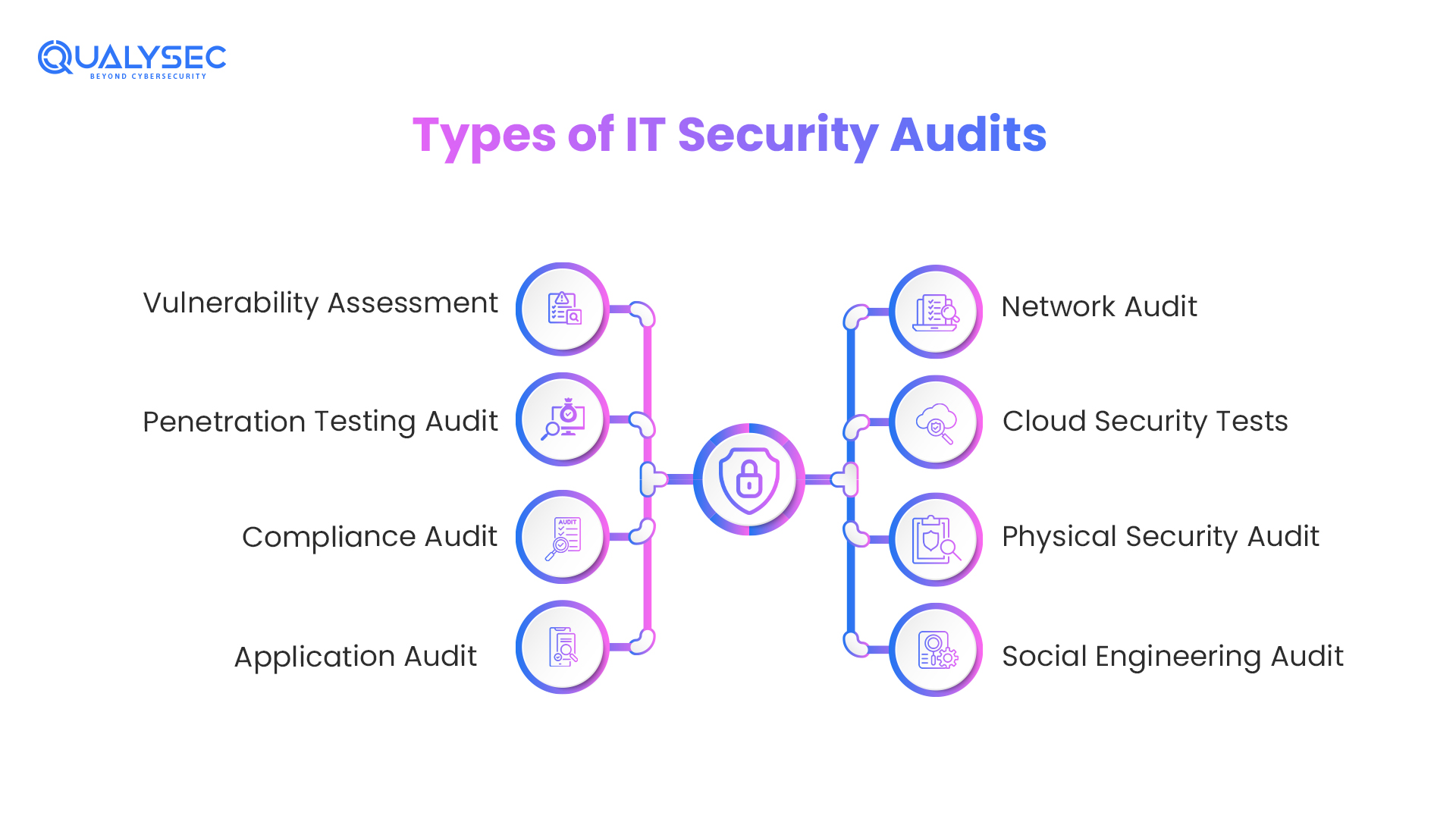
1. Vulnerability Assessment
This involves automated tools to scan systems, networks, and applications for vulnerabilities and misconfigurations. It recognises and gives precedence to the weaknesses, but does not try to take advantage of them. Its application as a continuous baseline monitoring practice is best.
2. Penetration Testing Audit
Ethical hackers who are certified and therefore verified will go the extra mile to gain access to the main system through the application of the weaknesses detected to simulate an actual attack. The output not only displays the vulnerabilities that may be present, but it also shows to what extent an attacker can go in case they discover them.
3. Compliance Audit
Ensures that your company adheres to certain legal requirements, such as GDPR, PCI-DSS, HIPAA, SOC 2, ISO 27001, SEBI/RBI regulations, or India DPDP regulations. Generates effective documentation of controls to regulators, customers, and partners that you have controls in place and functioning.
4. Application Audit
A complete security audit of web apps, mobile applications, and APIs. Includes authentication weaknesses, data injection vulnerability, failed access control, weak data storage, and compliance with the OWASP Top 10.
5. Network Audit
Professional examination of your network infrastructure in its entirety (firewalls, routers, switches, VPNs, wireless access points, and network segmentation). Scans open ports, devices that are misconfigured, too many access controls, and unencrypted traffic paths.
6. Cloud Security Tests
Cloud Configurations (AWS, Azure, and GCP), IAM, S3 Bucket Permissions, Container Security, serverless functions, and CSPM alignment. In the future (2025-2026), cloud misconfigurations will continue to be the number one reason for cloud information breaches.
7. Physical Security Audit
Those physical security controls around your IT infrastructure Server room access, badge systems, CCTV coverage, visitor management, and clean desk policies. This is required, and is critical, to ISO 27001 and SOC 2 compliance, and is often ignored.
8. Social Engineering Audit
Tests the human layer: Attacks that are simulated in the form of phishing, vishing, and in-person tailgating. This type of audit is not an option anymore as more than 74 of breaches include a human factor according to Verizon DBIR 2024.
2026 IT Security Audit Framework: Step-by-Step.
In order to keep up with the current security requirements, we apply a five-phase approach that attends to both technical and business imperatives.
Scope and Planning (The Blueprint)
The boundaries must be set up before the first line of code attracts attention. This implies the identification of essential assets (crown jewels), confidential data flows and regulatory needs (e.g., GDPR 2.0, HIPAA, or DORA).
Material Consideration: Discovering Shadow AI applications and rogue cloud environment.
Risk Assessment and Threat Modelling
We examine the threat landscape which is relevant to your industry currently. This will entail measuring your vulnerability to Deepfake phishing and AI-driven exploit kits in 2026.
Fact: 74 per cent of breaches today are now human element-based, and this has made the test of social engineering very crucial in auditing.
Implementation: Policy Test and Technical Test
This is the “stress test” phase. It entails scanning vulnerabilities, penetration, and immersing into your Identity and Access Management (IAM) protocols.
Vulnerability Insight: The latest CVE-2026-X1 brought up the fact that despite the existence of fixed systems, they can still fail when configuration logic is incorrect.
Prioritisation and Analysis
Not all risks are equal. We classify the results with regard to the Blast Radius. We are not interested in the 200 pages of the document about minor issues, and we would rather concentrate on the top 10-percent but 90-percent of the risk.
Reporting and Continuous Remediation
A roadmap appears at the end of the audit. In 2026, however, remediation is not a one-time event anymore. Our solution is a Continuous Audit model, in which automated tools are used to track the regressions each day.
IT Security Audit Checklist
Access Controls
- Minimum permissions are required on all user accounts (principle of least privilege).
- All administrative and remote access is enforced.
- Unused accounts (90 days or more) are deactivated or deleted.
- Standard user accounts are distinctly different from privileged access accounts.
- Anomalous activity is also checked in access logs regularly.
Network Security
- Rules of the firewall are recorded, examined and up-to-date.
- The network is subdivided to restrict lateral mobility in case of a breach.
- All open ports that are not required are shut.
- VPN settings are checked, and encryption measures are disabled.
- WPA3 is implemented to secure wireless networks and isolate them.
Data Protection
- Inventory Data of sensitive data is classified and inventoried.
- The encryption of data at rest works with AES-256 or equal.
- Transit data is encrypted with the help of TLS 1.2 or TLS 1.3.
- Backup processes are recorded and verified on a periodic basis.
- Policies to do away with and hold data are applied.
Application Security
- Applications are also patched and updated to the latest versions.
- There has been testing of Web applications on the OWASP Top 10.
- Authentication controls and rate limiting are in place in APIs.
- CVEs are given an inventory and tracked on third-party libraries.
Compliance & Policies
- Security policies are written, examined annually, and recognised by employees.
- There is an incident response plan that has been tested, is documented and exists.
- Controls are mapped onto compliance requirements (GDPR, PCI-DSS, HIPAA, ISO 27001, DPDP Act).
- All the staff undertake security awareness training at least once a year.
Physical Security
- There is limited, logged-in access to server rooms.
- The visitor management processes are recorded and observed.
- There are policies of a clean desk and screen lock.
- Physical hardware is disposed of in a documented manner.
IT Security Audit Tools
|
Tool |
Category |
Primary Use |
Best For |
|
Nessus / Tenable |
Vulnerability Scanning |
CVE detection across networks, systems, and cloud |
Broad automated scanning baseline |
|
Qualys VMDR |
Cloud-based VA |
Continuous vulnerability management and compliance |
Enterprise-scale asset coverage |
|
Nmap |
Network Reconnaissance |
Port scanning, service enumeration, OS detection |
Network topology mapping |
|
Burp Suite Pro |
Web App Testing |
Manual and automated web vulnerability scanning |
Web application and API security audits |
|
Metasploit |
Exploitation Testing |
Controlled vulnerability exploitation |
Penetration testing component of audits |
|
Wireshark |
Network Analysis |
Packet capture and traffic analysis |
Network protocol and traffic audits |
|
OpenVAS |
Open Source VA |
Free, comprehensive vulnerability scanning |
SMB and the internal team use |
|
Microsoft Secure Score |
Cloud / M365 |
Security posture scoring for Microsoft environments |
Organisations using Azure / M365 |
Notable: Tools do not necessarily make up an audit. Professional testing also requires the need to have human-trained reviewers to extract meaning out of results, contextualise findings and find vulnerabilities that are not visible to automated tools, especially business logic flaws, multi-configuration errors, and chained attack conditions, etc.
How Often Should You Conduct an IT Security Audit?
Annually – minimum to any organisation. Meets the minimum compliance provision and gives a complete security posture review.
Quarterly- in case of regulated industries. The banking, fintech, e-commerce, healthcare and government organisations must audit at least quarterly. Physician scans Network scans are mandated quarterly in PCI-DSS. HIPAA requires testing security controls in a regular manner.
Following each significant transformation of infrastructure, i.e. cloud migration, new application implementation, major software upgrade, merger, or network expansion, a targeted audit of the systems concerned.
Following any actual breach or any suspicious activity, a post-security incident audit becomes necessary to know the extent of exposure and ensure that all vectors of attack have been sealed after a security incident.
Continuously (2026 best practice) – It is discovered that the gap between the notification of vulnerability and active exploitation is narrowing. The median dwell time (time between compromise and detection) according to the 2024 report issued by Mandiant dropped to 10 days in the year 2023. Companies must complement with regular audits on a constant basis to ensure visibility between official audit cycles.
IT Security Providers: How to select an IT Security auditor
Certifications and Credentials
Auditors will have CISA, CISSP, OSCP, CEH, or ISO 27001 Lead Auditor Certifications. CERT-In empanelment is the most important organisational certification that is to be considered in the case of India-based engagements.
Requesting Quality
It is always better to seek out a sample report. It must contain the actual descriptions of vulnerabilities, the severity ratings, the business context, the proof-of-concept evidence and the concrete steps of remediation, containing not generic observations only.
Scope of Coverage
Certify your coverage of all the audit types you require: network, application, cloud, compliance, physical and social engineering. Narrow-scope providers are gap creators.
Post-Audit Support
This is not the end of being reported but rather remediation. Select a provider capable of helping your team to fix and confirm remediation using retesting.
IT Security Audit Cost & Pricing
|
Service Tier |
Price Range (USD) |
Price Range (INR) |
What’s Included |
Best For |
|
Basic |
Less than $5,000 |
Less than ₹4.2L |
Network scan, basic compliance review, summary report |
Startups, SMBs, single-site |
|
Standard |
Less than $15,000 |
Less than ₹12.5L |
Full audit (network + app + compliance), detailed report, remediation guidance |
Mid-size, regulated industries |
|
Comprehensive |
Less than $40,000 |
Less than ₹33L |
All audit types, manual testing, cloud review, compliance mapping, and retesting |
Enterprises, complex environments |
|
Custom / Ongoing |
Quoted per scope |
Quoted per scope |
Continuous auditing, quarterly cycles, dedicated auditor, board reporting |
Large enterprises, critical infrastructure |
Factors that affect pricing:
- Using the scope number and the complexity of systems.
- Type of audit needed (full technical or compliance only)
- Regulatory frameworks to be encompassed.
- Manual vs. automated testing.
- Looking after remediation or retesting.
- Residency requirements of data.
Viewpoint: The mean breach of information in India amounts to 19.5 crore. The total IT security audit at 4-12 lakh annually is less than 1 per cent of that amount, one of the best returns on investment in any security investment.
What is the Rationale of Selecting QualySec as a Source of IT Security Audits?
QualySec is a cybersecurity firm that is most trusted within the Indian market and offers an overall IT security audit in the banking, healthcare, e-commerce, SaaS, fintech and government sectors.
- CERT-In Empanelled: ‘Empanelled’ by the national cybersecurity agency of India.
- 500+ Successful Tests: Mobile, cloud, network, Equity Audits, API, and more.
- Certified Auditors: CISA, OSCP, CEH, and ISO 27001 Lead Auditor throughout the team.
- Complete Scopes Audit: Network, application, cloud, compliance, physical, and social engineering one engagement.
- Actionable Reporting (Technical Teams and Board Level Leadership): PoC evidence, Compliance mapping, prioritised remediation action, and actionable reporting. Built for technical teams and board-level leadership.
Devoted Remediation Support: This is provided after the report to assist your group through remediations and confirming those with additional retesting.
Conclusion
Organisations must conduct IT security audits to evaluate and improve their security posture. They can find weaknesses, reduce risks, guarantee compliance, and safeguard sensitive data by regularly conducting audits. Additionally, they may increase their overall security defences and execute effective IT security audits by using industry standards, best practices, and a strategic methodology. Companies can proactively safeguard their digital assets and lessen any risks by taking the required corrective action in response to audit results.
Are you ready to secure your application against cyber threats? Contact our specialists for cutting-edge IT security audits. Defend your digital assets right away.
Talk to our Cybersecurity Expert to discuss your specific needs and how we can help your business.
FAQs
Q. What are common IT security audit standards?
A. IT security audit standards such as ISO 27001, NIST SP 800-53, PCI DSS, and SOC 2 are frequently used in the industry. Thus, the frameworks play a role of recommendation on how to measure and mitigate security vulnerabilities of the IT systems.
Q. What does an IT audit consist of?
A. An information technology (IT) audit usually involves the evaluation of internal controls, policies, and procedures. Additionally, it covers access controls, data integrity, and risk management issues.
Q. What is the scope of the IT security audit?
A. IT security audit checks the capability of safety measures in protecting digital possessions via networks, systems, applications, and data. Moreover, its goal is to identify flaws, evaluate risks, and propose solutions.
Q. Who performs an IT security audit?
A. Internal auditors, external auditors, or specialized IT audit companies perform IT security audits. These are the people who have acquired extensive knowledge in cyber security, risk management, and audit methods so they can effectively assess and improve security measures.



















































































































































































































































































































































































































































































































































































































































































































0 Comments