Cybersecurity is the most important worry for every technology executive or business. Hackers are constantly looking for new ways to break into company systems. They scan all known vulnerabilities in business systems. If your company has a weakness, they can quickly access your network. As a result, protecting your company from cyber threats has become critical. Nowadays, almost every business has a website. Websites, on the other hand, are more vulnerable to hacking. It is now vital to have a solid cybersecurity plan with expert “VAPT assessment” and a Leading VAPT Security Audit Company.
What is VAPT?
VAPT, also known as Vulnerability Assessment and Penetration Testing, is a comprehensive security testing method for finding and correcting cyber security flaws. VAPT delivers a detailed study to increase your organization’s cyber security by integrating vulnerability assessment and penetration testing.
In different places, VAPT can refer to a variety of distinct services or a single, unified offering. However, VAPT might include everything from automated vulnerability assessments to human-led penetration testing and red team activities.
Method & Goal of VAPT:
VAPT seeks to proactively detect security flaws, allowing enterprises to rectify them before bad actors exploit them. Penetration testing, in particular, simulates malicious attacks in order to assess a company’s capacity to fight against and sustain cyber-attacks. Vulnerability Assessment entails identifying vulnerabilities using scanning tools and procedures, whereas Penetration Testing aims to exploit these flaws.
Vulnerability Assessment Vs. Penetration Testing: The Key Difference
| Vulnerability Assessment | Penetration Testing |
| It has a greater reach and keeps track of assets and resources in a specific system. | It concentrates on a specific vulnerability and determines the breadth or depth of an attack. |
| It identifies probable flaws in each resource. The purpose is to identify as many dangers as possible. | The aim here is to use the found threat to go to the base of the problem while also testing the sensitive data collected. |
| It is automated, less expensive, and faster. | It is rather expensive and entirely manual. It also needs highly specialized expertise and a longer time frame to accomplish. |
| It provides only a summary of the vulnerabilities and no recommendations for mitigating them. | It displays the complete scope of the exploited threat and ways to reduce the risk. |
| It is more appropriate for non-critical systems or lab conditions. | It is suited for real-time critical systems and physical network design. |
Importance of Conducting VAPT?
Vulnerability Assessment and Penetration Testing (VAPT) is an indispensable practice for organizations across diverse sectors and sizes. In an era where cyber threats are growing increasingly sophisticated, businesses must adopt a proactive approach to cybersecurity to thwart potential data breaches and other malicious cyber incidents.
VAPT serves as a vital cybersecurity process, empowering organizations to proactively identify and rectify potential security vulnerabilities present in their systems, networks, and applications. By leveraging a combination of vulnerability assessment and penetration testing methodologies, VAPT offers a holistic perspective of an organization’s security landscape, enabling a comprehensive and proactive defense against cyber threats. This proactive stance is crucial for organizations seeking to safeguard their digital assets and fortify their resilience against cyberattacks.
In essence, VAPT plays a pivotal role in an organization’s overall security strategy. By conducting VAPT exercises, businesses can effectively identify and mitigate security vulnerabilities, thereby minimizing the likelihood of successful cyber-attacks. Additionally, VAPT aids in reducing security risks by providing actionable insights into potential weaknesses that could be exploited by threat actors. Furthermore, adherence to industry regulations and standards is facilitated through VAPT, ensuring that organizations maintain compliance with the evolving cybersecurity landscape.
Characteristics of the Best VAPT Testing Service Provider
A reliable VAPT Security Audit Company exhibits several key characteristics that set them apart from others in the industry. These characteristics are essential for ensuring that businesses receive comprehensive and effective VAPT assessments that meet their cybersecurity needs. Here are some key traits to look for when evaluating the best VAPT Security Audit Company.

Expertise
The best VAPT Security Audit Company has a team of skilled cybersecurity professionals with in-depth knowledge of the latest threats and vulnerabilities. These professionals have the expertise to identify and assess vulnerabilities across diverse IT environments, from network infrastructure to web applications.
Customized Approach
They tailor their testing methodologies to each client’s specific needs, ensuring thorough coverage and accurate results. This customized approach allows them to address each business’s unique challenges and requirements, providing relevant and actionable targeted insights.
Comprehensive Reporting
They provide detailed reports with actionable insights, helping businesses understand their security posture and prioritize remediation efforts. These reports are not just about listing vulnerabilities but also about providing context and recommendations for addressing them effectively.
Continuous Support
They offer ongoing support and guidance to help businesses address vulnerabilities and improve their security over time. This includes assistance with implementing remediation measures, monitoring for new threats, and staying updated on best cybersecurity practices.
Industry Reputation
The best VAPT Testing Service Providers have a strong reputation in the cybersecurity industry, backed by positive reviews and client testimonials. Their track record of delivering high-quality assessments and valuable insights is a testament to their expertise and reliability.
What are the Perks of Conducting VAPT Testing?
Here are the top ways VAPT can help shield businesses from data breaches:
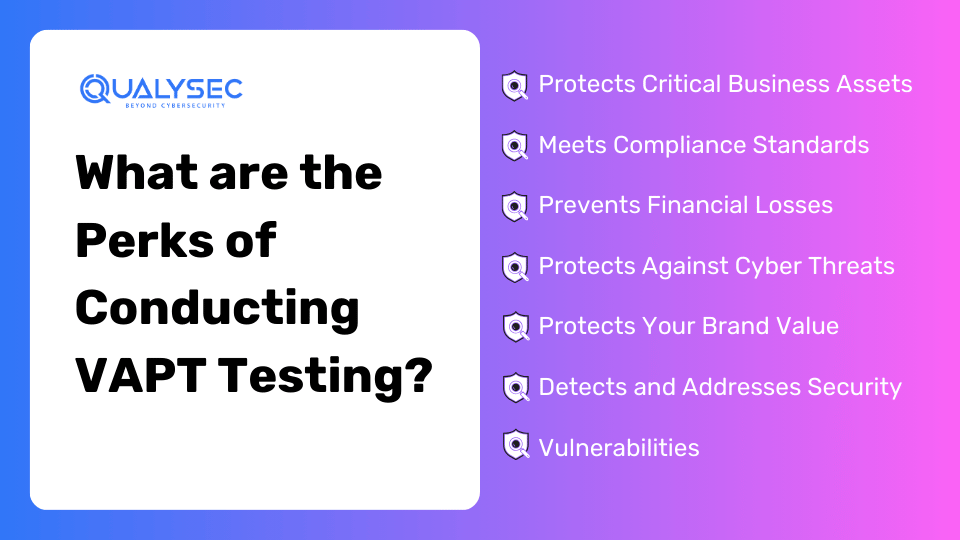
- Protects Critical Business Assets
One of the key reasons organizations need VAPT is to protect vital assets. By conducting frequent “VAPT security testing,” businesses can identify security faults and vulnerabilities that could jeopardize their assets, such as intellectual property, financial data, and customer data.
- Meets Compliance Standards
Businesses must follow unique data security and privacy laws established by various sectors and regulatory organizations. Furthermore, companies may benefit from VAPT’s support in ensuring that their IT infrastructure and security measures meet compliance requirements.
-
- Prevents Financial Losses
Cyberattacks and data breaches may result in massive financial losses for corporations. Furthermore, VAPT can aid firms in averting these losses by identifying vulnerabilities and implementing the appropriate security solutions.
-
- Protects Against Cyber Threats
Businesses are continually worried about cyber threats, and VAPT may assist in giving protection. VAPT examinations can also help identify “vulnerable applications” that hackers may exploit to get unauthorized access to sensitive company data.
-
- Protects Your Brand Value
Gives your industry regulators, consumers, and shareholders due diligence and compliance. Noncompliance can lead to your company losing customers, paying huge penalties, gaining negative press, or finally collapsing.
-
- Detects and Addresses Security Vulnerabilities
VAPT is critical in discovering and addressing security vulnerabilities that bad hackers might exploit. Furthermore, businesses may discover gaps in their apps, networks, and systems by undertaking a thorough vulnerability assessment.
Qualysec

Established in 2020, Qualysec swiftly emerged as a trusted VAPT Security Audit Company We have specialized in cyber security, security consulting, and incident response services. Our expert team is dedicated to identifying vulnerabilities that malicious actors could exploit, collaborating closely with clients to rectify these issues and ultimately bolster overall security.
Qualysec’s expertise in the field of cybersecurity has made it the top preferred VAPT Security Audit Company. At Qualysec, our team comprises seasoned offensive specialists and security researchers. They ensure our clients have access to the latest security techniques.
Our VAPT services incorporate human expertise and automated tools, delivering clear findings, mitigation strategies, and post-assessment consulting—all adhering to industry standards. Our comprehensive service portfolio includes:
- Web App Pentesting
- Mobile App Pentesting
- API Pentesting
- Cloud Security Pentesting
- IoT Device Pentesting
- AI ML Pen testing
This proves invaluable for businesses seeking to comply with industry regulations or demonstrate commitment to security to stakeholders.
Level up your cybersecurity! Download a free sample pen testing report now and fortify your defenses. Don’t wait, secure your systems today!
Latest Penetration Testing Report

The Working Process of VAPT: A Guide
“VAPT testing companies in India” often follow a standardized approach. Here’s a step-by-step guide for understanding the in-depth Vulnerability Assessment and Penetration Testing process.
-
- Pre-Test Interaction
Before a penetration test, the testing team and the company must establish clear communication and collaboration. This also includes establishing the test’s scope, aims, and objectives and gaining the necessary authority to execute the test.
-
- Reconnaissance
In the initial stage of VAPT, an attacker identifies tools to detect live hosts on a network. During this phase, it is critical to map all running devices and find active IP addresses that extend beyond the organization’s boundary.
-
- Threat Modeling
During this step, testers examine the collected data to identify possible risks and rank them based on their likelihood and potential effect. This procedure enables testers to concentrate their attention on the most critical hazards.
-
- Vulnerability Analysis
Testers use various tools and methodologies to scan the target environment for known vulnerabilities and security flaws. Furthermore, this step gives an in-depth look at any vulnerabilities that might be exploited during the test.
-
- Exploitation
During this step, active attempts are made to exploit the discovered vulnerabilities in order to obtain unauthorized access, escalate privileges, or disrupt services. The purpose is to imitate real-world cyberattacks and see how the target environment responds.
-
- Post-Exploitation
Following successful exploitation, testers assess the impact of the attack and collect further information to determine the scope of the breach. This might involve retrieving sensitive data or finding new weaknesses that can be exploited in future assaults.
-
- Reporting
At the end of the process, the testing team prepares a complete report summarizing the test findings, including exploited vulnerabilities, potential threats, and recommended repair procedures. This report is a helpful resource for the organization’s security posture improvement.
-
- Retesting
Once the vulnerabilities have been addressed, businesses may decide whether to retest systems to check that the fixes were successful and to determine whether any new vulnerabilities were introduced as a result of the remediation.
What are the Tools Used for VAPT?
There are several VAPT tools open source on the market. However, we have only included the greatest tools. The majority of these tools are solely used to scan your network. For the penetration testing process, you will still want the services of a competent, ethical hacker.
There will still be certain tools used for penetration testing. However, highly skilled experts who can effectively use PT tools are required. The following are some of the most effective VAPT tools:
-
- Nmap
- Metasploit
- BurpSuite
- Netsparker
- Wireshark
Conclusion
In conclusion, cyber security is an essential aspect of any business, and it is crucial to invest in the right cyber security solutions. Among the cybersecurity companies, the above-mentioned company is the top VAPT Security Audit Company.
When choosing a cybersecurity service provider, it’s essential to consider factors such as expertise, experience, and cost. By working with one of the top VAPT Security Audit Company, they can take proactive steps to improve your system with enhanced protection.
Furthermore, Qualysec the best VAPT Security Audit Company, is leading the way in protecting businesses from cyber threats. They offer a range of innovative solutions, cutting-edge technology, and expert teams that can help businesses of all sizes stay ahead. Ahead of the curve when it comes to cybersecurity. Choosing one of these providers can give you the peace of mind you need to focus on growing your business without worrying about cyber attacks.
Choose Qualysec for not just for VAPT Services but also a strategic partnership. A partnership that propels your organization toward a resilient and secure future. Join our community of satisfied clients who have experienced the tangible benefits of our expertise. Let us guide you on the path to cybersecurity excellence just by clicking here.
Frequently Asked Questions
Q. What is the goal of cyber security?
Ans. Cybersecurity is the protection to defend internet-connected devices and services from malicious attacks by hackers, spammers, and cybercriminals.
Q. What are the 4 reasons we need cyber security?
Ans. The Four Reasons are:
-
- Communicate data breaches.
- Appoint a data protection officer.
- Require user consent to process information.
- Anonymize data for privacy.
Q. Which technology is best for cyber security?
Ans. The Various cybersecurity technologies are:
-
- Internet of Things
- Blockchain
- Web security
- Application Security
Q. What are the different cyber security services?
Ans. Advanced and multi-layered network threat prevention technologies include IPS (Intrusion Prevention System), NGAV (Next-Gen Antivirus), Sandboxing, and CDR (Content Disarm and Reconstruction).
Q. What are the three 3 major areas of security?
Ans. There are three primary areas or classifications of security controls. These include management security, operational security, and physical security controls.



















































































































































































































































































































































































































































































































































































































































































































0 Comments