Web Penetration Testing is a critical process for ensuring the security and resilience of your web applications. In this guide, we will walk you through the essential steps to plan and execute a successful Web Penetration Testing engagement. By following these steps diligently, you can uncover vulnerabilities, assess risks, and fortify your web applications against cyber threats in the realm of cybersecurity.
Planning for the Web Penetration Test
Before diving into the intricacies of Web Penetration Testing, it’s crucial to set a solid foundation for your testing strategy. This begins with meticulous planning, which involves two key components:
Define the Web Penetration Testing Goals
The first step in planning your Web Penetration Testing project is to define clear and specific goals. What do you aim to achieve through this assessment? Your goals should align with your overall security objectives. Common objectives include:
- Identifying and mitigating security vulnerabilities.
- Evaluating the effectiveness of security controls.
- Assessing the security posture of web applications.
- Enhancing the protection of sensitive data.
Identify the Penetration Testing Scope
The scope of your Web Penetration Testing project outlines the boundaries and limitations of the assessment. It outlines what the test will cover, how it will be conducted, and what it will not cover. Consider the following factors when defining the scope:
| Aspect | Description |
|---|---|
| Web Applications | Clearly specify which web applications or domains will be included in the test. It’s essential to provide a comprehensive list to avoid overlooking critical assets. |
| Functionality | Identify specific functionalities within your web applications that require testing. This could include user authentication, payment processing, file uploads, and more. |
| Restrictions | Determine any restrictions that should be imposed during testing. For instance, you might want to avoid testing during peak hours to minimize disruption to users. |
| Exclusions | It’s equally important to specify what won’t be tested. This may include third-party services or components that are out of scope for the assessment. |
By defining a well-scoped Web Penetration Testing project, you ensure that your testing efforts are focused and efficient, allowing you to uncover vulnerabilities and address security issues effectively. In the subsequent sections of this guide, we will delve deeper into each phase of the penetration testing process, providing you with the knowledge and strategies needed to conduct a thorough assessment of your web applications.
What Environment Should Be Tested?
When planning a penetration test, it’s essential to consider which environments should be tested. Typically, you should aim to test the following environments:
- Production Environment: This is the live environment that your users access. It’s crucial to assess the security of your production environment to identify and address vulnerabilities that may be exploited by attackers.
- Staging Environment: Staging environments are meant to mirror your production environment closely. Testing in the staging environment helps ensure that any changes or updates you plan to make to your production environment won’t introduce vulnerabilities.
- Development Environment: While not typically a priority for penetration testing, it can be beneficial to assess the security of your development environment, especially if it closely resembles your production environment. This helps prevent vulnerabilities from making their way into the production code.
- Testing Environment: If you have a separate testing environment where new features or code changes are tested before deployment, consider conducting penetration testing here to catch vulnerabilities early in the development lifecycle.
Remember that each environment may have its unique security requirements and configurations. Ensure your organization’s priorities align with a well-defined scope for the penetration test.
Should You Tell Your Hosting Provider About Penetration Testing?
Yes, it’s generally advisable to inform your hosting provider about your intention to conduct penetration testing. Hosting providers often have policies and security measures in place to detect and respond to unusual network activity. Penetration testing may trigger security alerts, and without prior notification, it could lead to unintended consequences, such as the temporary suspension of services or misinterpretation of the testing as an attack.
By notifying your hosting provider, you can work together to coordinate the testing, establish rules of engagement, and avoid any disruptions to your services. They may also provide guidance or assistance during the testing process.
How to Choose a Good Penetration Testing Team
Selecting a competent and trustworthy penetration testing team is crucial for the success of your assessment. Here are steps to help you choose the right team:
| Criteria | Description |
|---|---|
| Qualifications and Certifications | Check for relevant certifications (e.g., CEH, OSCP, CISSP) and qualifications of team members. |
| Expertise | Evaluate the team’s expertise in technologies and frameworks relevant to your web applications. |
| Communication and Reporting | Assess their ability to communicate findings clearly and provide actionable recommendations. |
| Compliance and Ethics | Ensure adherence to ethical hacking standards, legal compliance, and responsible disclosure. |
| Collaboration | Consider their ability to collaborate effectively with your internal IT and development teams. |
| Cost | Evaluate the cost of services, but prioritize value and quality over the lowest price. |
| NDA and Legal Agreements | Confirm willingness to sign non-disclosure agreements and other legal contracts to protect data. |
Ultimately, choosing the right penetration testing team involves a thorough evaluation of their qualifications, experience, and alignment with your organization’s needs. Don’t rush the selection process, as the quality of the team can significantly impact the security of your web applications.
Qualysec
Qualysec, Founded in 2020, it quickly became one of the most trusted names in the cybersecurity industry. The company provides services such as VAPT, security consulting, and incident response.
Although Qualysec’s Oppressional office is not situated in Norway, Qualysec’s extensive knowledge and expertise in cybersecurity testing services have earned a reputation among the top companies to provide penetration and vulnerability assessment services.
Technicians at Qualysec can detect flaws that fraudsters could abuse. After these flaws have been found, Qualysec collaborates with the organization to establish a plan to address them and boost the company’s overall security posture. Among the several services available are:
- Web App Pentesting
- Mobile App Pentesting
- API Pentesting
- Cloud Security Pentesting
- IoT Device Pentesting
- AI /ML Pen-testing
The Qualysec team, comprising seasoned offensive specialists and security researchers, collaborates to provide clients with access to the latest security procedures and approaches. They provide VAPT services using both human and automated equipment.
In-house tools, adherence to industry standards, clear and simple findings with reproduction and mitigation procedures, and post-assessment consulting are all features of Qualysec’s offerings.
The solution offered by Qualysec is particularly beneficial for businesses that must adhere to industry rules or prove their dedication to security to clients and partners. So, by doing routine penetration testing, businesses may see weaknesses and fix them before thieves attack them.
As a result, Qualysec is rated as the best.
Talk to our Cybersecurity Expert to discuss your specific needs and how we can help your business.
What to Do During Web Penetration Testing
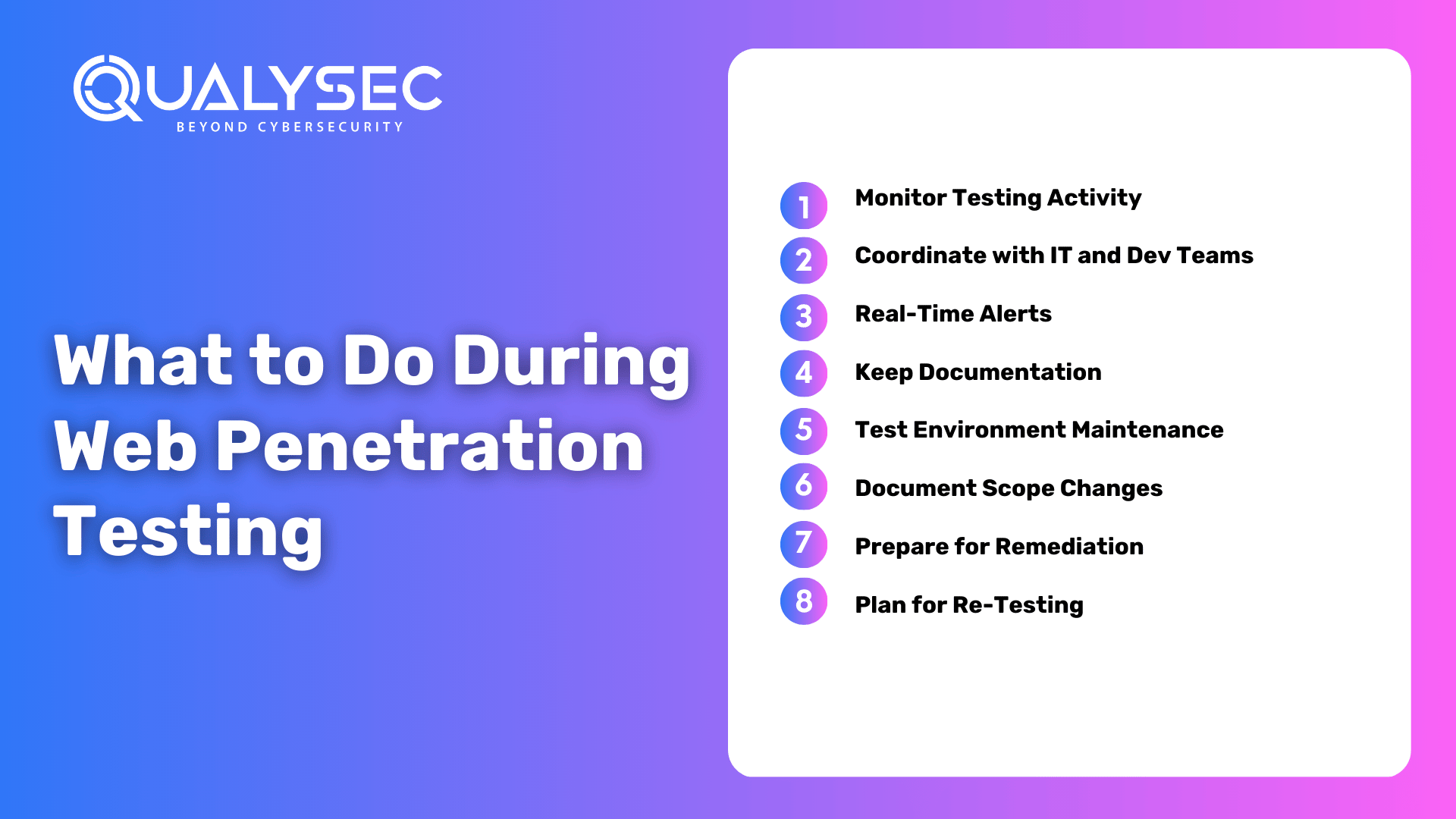
The Web Penetration Testing process involves several crucial steps that must be carefully managed. Here are some key actions to take during the testing phase:
- Monitor Testing Activity: Continuously monitor the testing activity to ensure that it aligns with the predefined scope and objectives. Be prepared to address any questions or requests for additional information from the testing team.
- Coordinate with IT and Dev Teams: Maintain open lines of communication with your internal IT and development teams. Inform them about the testing schedule and potential disruptions. Collaboration between teams can help address vulnerabilities more effectively.
- Real-Time Alerts: Be prepared to receive real-time alerts from your penetration testers if they discover critical vulnerabilities or unexpected issues that require immediate attention. Have an incident response plan in place.
- Keep Documentation: Maintain detailed records of the testing process, including the methodologies and tools used. These records can be valuable for future reference, compliance, and reporting.
- Test Environment Maintenance: If necessary, ensure that the test environment (e.g., staging or testing environment) is properly maintained to mirror the production environment accurately.
- Document Scope Changes: If there are any changes or adjustments to the testing scope or objectives, document them carefully and communicate them to all relevant parties, including the testing team.
- Prepare for Remediation: Anticipate that vulnerabilities will be identified during testing. Begin preparing for remediation efforts by allocating resources, setting priorities, and assembling a response team.
- Plan for Re-Testing: Discuss and plan for re-testing of identified vulnerabilities after they are remediated. Ensure that both the testing team and your organization are aligned on expectations for the re-testing phase.
Communication with Your Penetration Testers
Effective communication between your organization and the penetration testing team is essential for a successful assessment. Here are some tips for establishing clear and productive communication:
| Communication Aspect | Description |
|---|---|
| Regular Meetings | Schedule regular meetings or status updates with the testing team to discuss progress and findings. |
| Providing Context | Offer context about your web application, architecture, and known vulnerabilities to guide testing. |
| Clear Objectives | Ensure the testing team understands your objectives and priorities for the penetration test. |
| Access Information | Provide necessary access to systems, data, and resources required for the testing process. |
| Escalation Procedures | Establish clear procedures for addressing critical findings or unexpected issues promptly. |
| Question Clarification | Encourage testers to seek clarification if they encounter uncertainties or ambiguities. |
| Feedback Loop | Maintain an open feedback loop for both parties to provide feedback and improve future engagements. |
| Reporting Expectations | Discuss reporting expectations, including format, content, and timelines for the final report. |
| Secure Communication | Ensure that communication channels for sharing sensitive information are secure and encrypted. |
| Designated Point of Contact | Designate a single point of contact within your organization to liaise with the testing team. |
Clear and effective communication fosters collaboration and ensures that the Web Penetration Testing process runs smoothly, allowing you to address security vulnerabilities and enhance your web application’s security posture efficiently.
What to Do After Web Penetration Testing
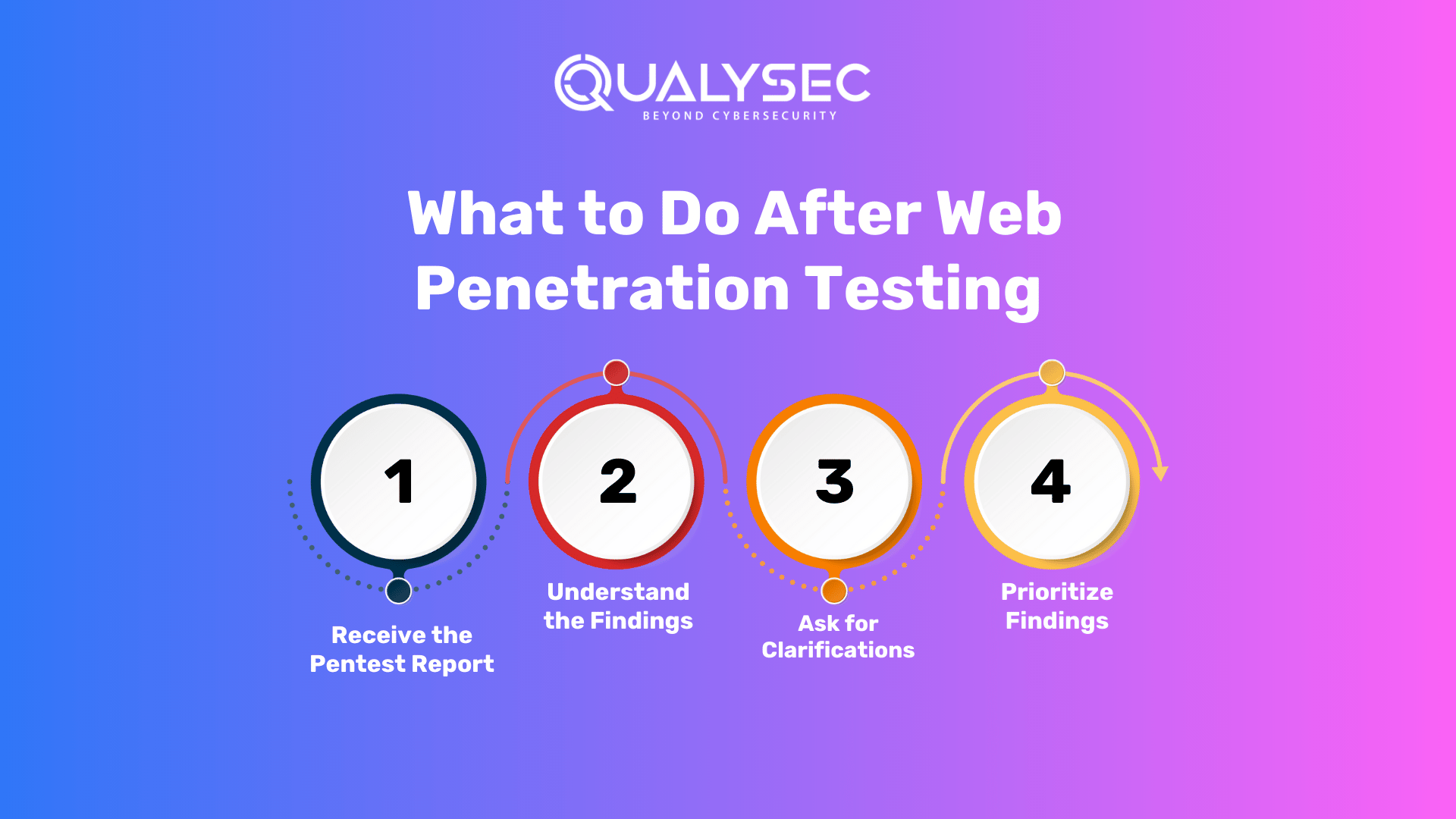
After completing the Web Penetration Testing phase, you need to take several important steps to ensure that the assessment delivers actionable results and contributes to the overall security of your web applications. Here are the key actions to consider:
Reviewing the Penetration Test Report
- Receive the Report: Once the penetration testing team has completed their assessment, you will receive a detailed penetration test report. Ensure that you securely receive the report, such as through encrypted channels.
- Understand the Findings: Carefully review the report to understand the vulnerabilities and security issues identified during the testing. Pay attention to the severity ratings assigned to each finding.
- Ask for Clarifications: If you have any questions or need clarification on any aspect of the report, reach out to the testing team for further explanations.
- Prioritize Findings: Prioritize the identified vulnerabilities based on their severity and potential impact on your web applications. Consider the ease of exploitation and the criticality of the affected assets.
Remediation
| Step | Description |
|---|---|
| Develop a Remediation Plan | Collaborate with internal IT and development teams to create a comprehensive plan outlining the steps required to address each identified vulnerability. |
| Assign Responsibility | Assign specific team members or departments responsible for executing each remediation task. Clearly define roles and set deadlines for addressing vulnerabilities. |
| Implement Security Updates | Apply necessary security patches, updates, and configuration changes to rectify identified vulnerabilities. Thoroughly test these changes to prevent new issues. |
| Monitor Progress | Continuously monitor the progress of remediation efforts. Maintain open communication with teams responsible for implementing fixes to ensure timely resolution. |
| Retest Remediated Vulnerabilities | After remediation, schedule a retest with the penetration testing team to validate that the identified vulnerabilities have been effectively addressed. |
Retesting and Ongoing Security
| Step | Description |
|---|---|
| Retesting | Coordinate with the penetration testing team to retest the remediated vulnerabilities. Ensure that the fixes are effective and that no new vulnerabilities have been introduced. |
| Final Report | Expect to receive a final penetration test report after retesting. This report includes the retest results and confirmation that vulnerabilities have been successfully remediated. |
| Ongoing Security | Maintain a proactive security approach by regularly monitoring and assessing your web applications for new vulnerabilities. Consider periodic penetration tests to stay ahead of threats. |
| Incident Response | Develop and refine your incident response plan based on lessons learned from the penetration test. Ensure readiness to respond effectively to any security incidents. |
| Security Awareness | Promote security awareness among your staff. Educate them on best practices for web application security to reduce the risk of human-related security issues. |
| Documentation | Keep comprehensive records of the penetration testing process, remediation efforts, and retesting results. These records are valuable for audits and compliance purposes. |
| Continuous Improvement | Utilize insights from the penetration test to enhance your organization’s security posture. Implement best practices, conduct training, and stay informed about emerging threats. |
By following these post-penetration testing steps, you can effectively address vulnerabilities, enhance the security of your web applications, and maintain a proactive stance against cyber threats.
Latest Penetration Testing Report

Conclusion
Web Penetration Testing is a critical process for evaluating and enhancing the security of your web applications. This comprehensive guide has walked you through the essential steps involved in planning, conducting, and following up on a successful penetration testing engagement.
By following these steps, you can enhance the security of your web applications, reduce the risk of security breaches, and stay prepared to address emerging threats. Web Penetration Testing is not a one-time effort but an ongoing commitment to safeguarding your digital assets and sensitive data.
Qualysec has a successful track record of serving clients and providing cybersecurity services across a range of industries such as IT. Their expertise has helped clients identify and mitigate vulnerabilities, prevent data breaches, and improve their overall security posture.
When it comes to comprehensive cybersecurity audits, Qualysec is the organization to go with. Their cost of VAPT guide helps clients make informed decisions by understanding the various factors that affect the cost by clicking here.























































































































































































































































































































































































































































































































































































































































































































0 Comments