As medical devices become more sophisticated and the Software as a Medical Device (SaMD) business grows in popularity, it is critical to ensure that your medical equipment is cyber-secure. Because of the huge volumes of health information and data, such as patient health, product performance, or data from other devices linked to the same network, the healthcare business has long been a target of cyber assaults.
Due to the increase in cyber assaults on medical devices, the FDA (U.S. Food and Drug Administrator) released a Guideline for cybersecurity in medical devices manufacturers on how to secure their devices from assaults. In this blog, we will discuss the importance of cybersecurity, the guidelines of the FDA, and how to protect IoMT (Internet of Medical Things).
Understanding the Cyber Threats of Medical Devices
Many healthcare assaults utilize phishing and the establishment of persistent threats within networks and devices in order to attack when the potential benefits are greatest. 327 data breaches have been reported since the beginning of 2023.
According to research, that statistic has grown more than 104% from 160 breaches as of mid-2022 and shows “no signs of abating.” In 2023, cyberattacks targeted more than 40 million individual patients, representing a 60% rise year on year for the first six months.
According to the report, there were five breaches of at least 3 million data each in the first half of 2023, compared to a single breach of 2 million records last year. Healthcare business associates are also in danger, accounting for 14% of all reported breaches and increasing from 22 in mid-2020 to 82 this year. According to the study, this is a 273% increase.
Talk to our Cybersecurity Expert to discuss your specific needs and how we can help your business.
FDA Cybersecurity Guidelines for Securing Medical Network Devices
While the new guidance is similar in structure and content to the previous version, it adds two new substantive sub-sections to the original security risk management section:
- A new appendix identifying which specific documentation elements recommended for inclusion in premarket submissions will also apply to IDE submissions,
- Several cybersecurity term definitions.
September 26, 2023: The FDA supports the establishment and use of a “Secure Product Development Framework,” or “SPDF.” This defines as a collection of activities that limit the number and severity of vulnerabilities in products across the device lifecycle.
The SPDF is meant to be the core structure which manages cybersecurity risk, and focuses on three main elements:
- security risk management
- security architecture
- cybersecurity testing
The guideline also mentions IEC 81001-5-1, a health software reference standard, as a viable framework to explore developing the SPDF. To assist in showing device safety and efficacy, the FDA Cybersecurity Guidance continues to suggest including a security risk management report in a premarket submission.
The revised guidance’s modified security risk management section includes two new sub-sections, the first of which is on “Cybersecurity Risk Assessments.” The guideline acknowledges that cybersecurity risks are difficult to foresee and that previous data or modeling cannot estimate and quantify the possibility of an incident occurring.
As a result, a cybersecurity risk assessment should concentrate on the exploitability of vulnerabilities existent within a device or system, as well as those that anticipates to exist in the context of use. The FDA recommends that the cybersecurity risk assessment include not only the risks and controls identified in the threat model but also the methods used for scoring such risks before and after mitigation, as well as the associated acceptance criteria, as well as the method for transferring security risks into the safety risk assessment.
The risk management section also includes a new section on “Interoperability Considerations,” which addresses cybersecurity concerns that may arise from interoperable functionality. This includes interfaces with other medical devices and accessories and other functions.
The guidance states that properly implemented cybersecurity controls will help ensure the safe and effective exchange and use of information. It also advises device manufacturers to assess whether additional security controls beneath common technology and communication protocols such as Bluetooth and network protocols are required to ensure safety and effectiveness. The guidance advises device manufacturers to consider the appropriate cybersecurity risks and controls that associates with interoperability capabilities and ensure they are in the document.
According to FDA requirements, all cybersecurity efforts must be well documented and traceable, including records of risk assessments, security controls, testing findings, and mitigation plans. This paperwork must provide useful information for post-market monitoring and risk management.
The FDA emphasizes the need to regularly monitor and analyze cybersecurity threats throughout the lifespan of a device. Manufacturers are expected to have mechanisms in place to identify, respond to, and mitigate cybersecurity events in a timely manner, assuring the device’s continuous safety and efficacy.
These recommendations define the material necessary for premarket filings, ensuring manufacturers present enough documentation of their cybersecurity risk management strategies. This comprises documentation of risk assessments, security controls, testing findings, and a cybersecurity risk management plan for the device.
The FDA is asking for an SBOM (Software Bill of Materials), which is a complete inventory of all software components that utilizes in a medical device, including those generated by the maker and those developed by third parties. An SBOM helps device makers and users discover possible security threats in a timely way, hence facilitating risk management processes.
The Mandates of Cybersecurity in Medical Devices FDA
Testing, like other aspects of product development, uses to show the efficacy of design controls. While software development and cybersecurity are closely related disciplines, cybersecurity controls necessitate testing that extends beyond standard software verification and validation activities.
This is a need in order to demonstrate the effectiveness of the controls in a proper security context. This demonstrates that the device has a reasonable assurance of safety and effectiveness.
A manufacturer requires to create and maintain processes for validating the device design. This verification must ensure that the design output satisfies the criteria of the design input. A manufacturer requires to create and maintain processes for certifying its device design. Where applicable, design validation must incorporate software validation and risk assessments.
The FDA advises that verification and validation include adequate testing done by the manufacturer on the cybersecurity of the medical device system, as well as the manufacturer’s inputs and outputs, if applicable. Documentation for security testing, as well as any accompanying reports or evaluations, should be included in the premarket submission.
The FDA cybersecurity guidance 2023 suggests, among other things, that the following types of testing considers for inclusion in the submission:
Security Requirements:
- Manufacturers should give evidence that each design input requirement was effectively applied.
- Manufacturers should offer proof of their boundary analysis as well as the reasoning behind their border assumptions.
Threat mitigation:
- Manufacturers should give information and proof of testing that indicates effective risk management methods based on the threat models presented in the global system, multi-patient harm, updatability and patchability, and security use case perspectives.
- Manufacturers should verify that each cybersecurity risk control is adequate
For example, security efficacy in implementing the stated security policy, performance under maximum traffic circumstances, stability, and dependability, as necessary.
Vulnerability Testing:
Manufacturers should give details and evidence of the following tests and analyses:
- Cases of abuse or misuse,
- Faulty and unexpected inputs;
- Robustness,
- Testing for fuzziness,
- Vulnerability chaining;
- Closed box testing of known vulnerability scanning;
- Software composition analysis of binary executable files;
- Static and dynamic code analysis, including testing for “hardcoded,” default, easily guessed, and easily compromised credentials.
Penetration Testing:
Penetration testing detects and define security-related issues in the product through tests that focus on identifying and exploiting security flaws. Include the following items in penetration test reports:
- Testers’ independence and technical expertise;
- Testing scope;
- Testing duration;
- used testing procedures; and
- Test results, discoveries, and observations
The FDA suggests to conduct cybersecurity testing across the SPDF. Early security testing helps guarantee that security vulnerabilities address before they affect release dates and can avoid the need to redesign or re-engineer the device. Following release, cybersecurity testing undertake on a regular basis commensurate with the risk to ensure that possible to find vulnerabilities and remedy them before exploiting.
Security Majors to be Taken for Healthcare Devices
The FDA guideline for cybersecurity for networked medical devices is published to assist cybersecurity teams in managing medical device security. Key security needs meet while managing medical devices, which include:
- Integrate security into the device: The IoMT devices themselves are the first line of protection against cyberattacks. Devices should be set to give as little access as feasible. Any access-control tools that are available on the devices should be activate, and the default usernames and passwords should alter to be unique.
- Customize security for each device: Every medical device is unique, and no one-size-fits-all IoMT security approach exists. Instead, adapt security procedures for each device for which a company is accountable. These processes should reflect the device’s security posture as well as the type of data produced by the device.
- Protection of Firmware: Firmware is software that incorporates and protects physical devices. Because firmware security problems might allow unwanted access, device administrators must be aware of which firmware is installed on all devices in their network and upgrade it if a security fault in the firmware is announced by the device maker.
- Secure data held in device: Data that remains on medical devices encrypts and controls access.
- Secure device communication: Data should encrypt whenever it leaves a device to prevent network eavesdroppers from accessing it. Furthermore, IoMT devices’ networking protocols must be secure in order to prevent attackers from exploiting protocol weaknesses to obtain unwanted access.
Cyberattacks against medical devices can take numerous forms, from data theft attacks meant to go unnoticed to ransomware assaults in which adversaries proclaim that they have hacked IoMT equipment and demand a fee in order to recover access. Continuous monitoring for all sorts of cybersecurity assaults is crucial for detecting breaches early before attackers inflict major harm.
Given the numerous factors involved in IoMT security, there is no straightforward approach to protect all medical devices from all sorts of attacks. However, a fundamental first step is to verify that you are aware of which medical devices are present on your network, as well as the sorts of attacks that may harm them.
Benefits of Following FDA’s Guidelines for Manufacturers
The advice addresses the key obligations of medical device makers that use OTS software. These duties outlines in the FDA’s Quality System rule. Manufacturers have previously been informed of their duties by the FDA.
This information intends to assist producers in better understanding their duties of cybersecurity in medical devices- FDA. Manufacturers must act to keep their networked devices safe and effective if they choose to utilize OTS software. Furthermore, vulnerabilities in OTS software impair the safety and effectiveness of their devices.
The FDA’s Quality System rule mandates medical device producers to investigate quality data sources and remedy or avoid quality issues. Normally, the FDA will not require to examine software fixes before a device maker installs them.
The FDA considers most software patches to be design modifications that manufacturers can make without consulting the FDA beforehand. The FDA has previously informed producers on when they should consult with the agency.
Under the Quality System rule, manufacturers must validate their software updates. This means they must examine what the modification accomplishes and provide proof that the modified program fulfills user demands and consistently performs as expected.
Although manufacturers seldom need to seek FDA permission for their patches. But, as part of quality control, they should develop and implement a plan for making these modifications. Manufacturers can seek professional help from penetration testing companies to secure the devices and meet the medical device cybersecurity standards as per the FDA.
How can Healthcare Device Makers Improve their Security?
Medical device makers may strengthen their cybersecurity by applying the following measures:
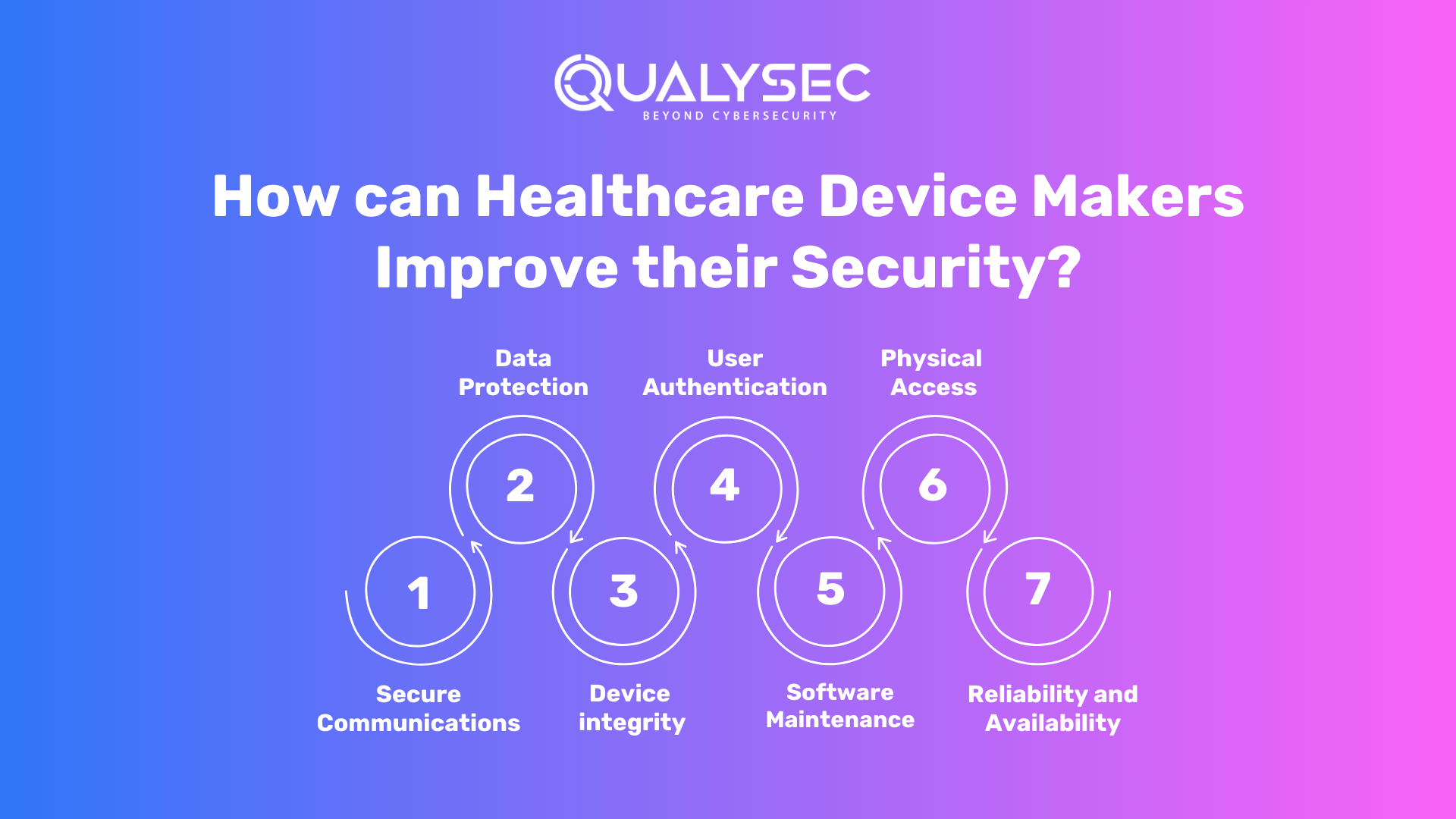
- Secure Communications: When it comes to data transfer to and from the device, the maker should examine how the device may interact with other devices/networks, communication with devices that offer less secure communication, and protection against unwanted access/modification.
- Data Protection: The maker should examine if data stored or exchanged on the device requires a degree of encryption. This also includes whether the device requires confidentiality risk control methods.
- Device integrity: The maker should assess threats to the device’s integrity, analyze the system-level architecture for design characteristics that are required, and consider anti-malware safeguards.
- User Authentication: The maker should think about user access controls that decide who may use the device or offer permission to user rolls.
- Software Maintenance: The manufacturer should consider the communication process. This includes how the software will be updated or controlled. In addition, how the device will be updated to secure it against other vulnerabilities, the required connections to conduct updates, and the use of code signing for connection authenticity.
- Physical Access: The manufacturer should consider adding restrictions to prevent unwanted access to the device.
- Reliability and Availability: The maker should think about designing features that will allow the device to detect, resist, respond to, and recover from cybersecurity assaults.
Practices in Cybersecurity for the Internet of Medical Things
Following the rules below can assist in preserving the safety, integrity, and dependability of IoMT devices and networks.
- Risk-Based Approach
Manufacturers are strongly pushed to identify their advantages as well as possible threats and weak points. They must examine how vulnerabilities and threats can jeopardize the device’s functionality and endanger the safety of users or patients. It is also critical to assess the possibility of these hazards occurring and to devise appropriate risk-mitigation solutions.
- Extensive Security Testing
All devices and systems should be thoroughly inspected to identify any potential weak connections. Manufacturers should conduct activities such as penetration testing and vulnerability scanning to ensure their security procedures are up to date.
- Clear Labeling
The device’s labeling should be clear about its security features and any safety precautions that users should be aware of.
- Incident Response Plan
Manufacturers must be prepared to address any cybersecurity risks once the gadget is on the market. This should include a well-thought-out approach to exposing vulnerabilities and successfully dealing with them.
Latest Penetration Testing Report

Conclusion
The healthcare industry is evolving with an increasing number of businesses relying on smart gadgets i.e., Internet of Medical Things. While IoMT provides cutting-edge methods for updating medical procedures and improving patient care, it is not without danger.
Because these devices lack sufficient security measures, they are easy targets for possible cyberattacks. To ensure that we cover all of our bases, we must detect any and all potential security flaws and threats. We can put effective safeguards in place once we know what we’re up against.
Managing the attack surface, which is the total of all potential security concerns, may make the network operate safer. Not to mention that keeping patient data and electronic medical records safe is critical as this technology evolves.
When we talk about safeguarding medical devices, we should seek professional help. QualySec Technologies of a professional company that provides services for healthcare vulnerability and penetration testing.
We at QualySec Technologies realize the crucial need to secure healthcare systems and patient data. Our specialist healthcare penetration testing services are intended to uncover vulnerabilities in your medical equipment, software, and networks in advance.
Don’t wait for a security breach to put patient safety and confidence at risk. Contact QualySec Technologies now to set up a complete healthcare penetration test targeted to your organization’s specific requirements. Let’s work together to strengthen our defenses and provide a robust and secure healthcare environment for everybody.
FAQ:
What is cyber security in medical devices?
Medical device cybersecurity refers to the procedures and technology used by HDOs to safeguard their Internet of Medical Things (IoMT). It also connects medical devices and software against illegal access, data theft, patient safety harm, and/or interruption of key services.
What is a networked medical device?
Infusion pumps, pacemakers, and diagnostic imaging equipment are examples of networked medical devices. These gadgets can be used to provide care, transfer patient data, and/or monitor patients remotely.
Why is cybersecurity important in medical devices?
Cybersecurity helps to protect medical equipment from malicious hackers who may get access to the device and change data. Furthermore, this can lead to care disruptions, privacy infractions, or monetary losses.
What are the network devices used in hospitals?
Physiological monitors, mobile applications, wearables, and scanners such as MRI, CT, or ultrasound devices are examples of these. They are all required for hospital personnel to give vital medical care and services to patients. Some gadgets are also crucial to maintaining and monitoring a patient’s health.
What is the cyber security standard for medical devices?
IEC 81001-5-1 acquired its structure from IEC 62304, therefore MedTech firms are already familiar with the procedure and language. IEC 81001-5-1 supplements IEC 62304 by defining a job that is only relevant to the cyber security of a connected Medical Device. IEC/TR 60601-4-5 specifies a set of security standards that must be met by the linked medical device’s hardware and software.
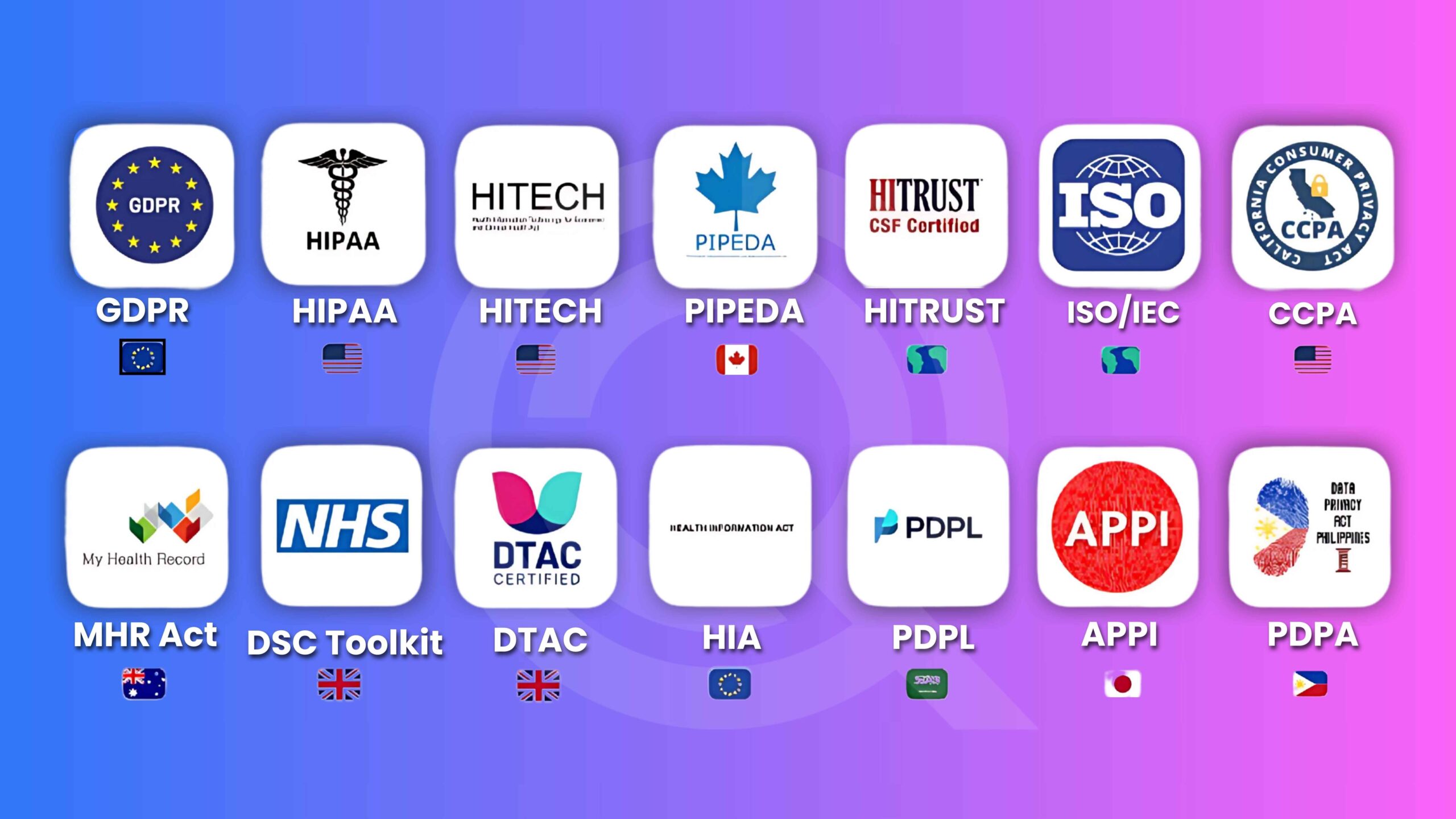
Ensure your healthcare solution is globally compliant.
Qualysec helps you meet HIPAA, FDA, ISO, and more. Contact us today!

















































































































































































































































































































































































































































































































































































































































































































0 Comments