VAPT testing (Vulnerability Assessment and Penetration Testing) is a cybersecurity practice that identifies and exploits security vulnerabilities before attackers do. It can also help organisations be aware of their real risk exposure and upgrade their protection through proactive testing.
India has been reported to have registered more than 1.5 million computer-related security attacks, indicating that cybersecurity threats have been on the rise in recent years (Indian Computer Emergency Response Team). The National Institute of Standards and Technology is another advocacy challenge that also suggests the need to carry out vulnerability testing as a primary control to reduce the risks of breaches.
The conventional security is not sufficient due to the fact that businesses increasingly rely on cloud services, APIs and other digital infrastructure. VAPT test is a structured and feasible way of identifying loopholes that can be exploited and improving the overall security preparedness.
What Is VAPT Testing?
VAPT (Vulnerability Assessment and Penetration Testing) is a cybersecurity procedure applied to detect, examine, and confirm security vulnerabilities in systems, networks, and applications. It is a combination of automated scanning and manual testing, which offers a full assessment of the possible vulnerabilities.
VAPT does not limit itself to issue identification, unlike the basic security checks. It also confirms the possibilities of exploiting those vulnerabilities and the way they can affect the system.
Core Components of VAPT
1. Vulnerability Assessment (VA)
Vulnerability Assessment involves the discovery of vulnerabilities in systems.
Key characteristics:
- Automated tools are used to scan systems.
- Identifies established vulnerabilities and misconfigurations.
- Extensive attack surface
Output: A table of vulnerabilities of severity levels.
2. Penetration Testing (PT)
Penetration Testing goes an extra mile by replicating real-life attacks.
Key characteristics:
- Carried out by security professionals.
- Efforts to seek the advantages of known weaknesses.
- Shows how an attacker can achieve access.
Output: Evidence of exploitation and actual effect.
How VA and PT Work Together
Component | Role | Outcome |
Vulnerability Assessment | Finds weaknesses | Risk identification |
Penetration Testing | Exploits weaknesses | Impact validation |
Combined, they offer visibility and validation, which makes VAPT a full security testing method.
Types of VAPT Testing
VAPT testing is realized on various levels of the technology environment in the organization. Both types target a particular area, which makes sure that every possible entry is considered.
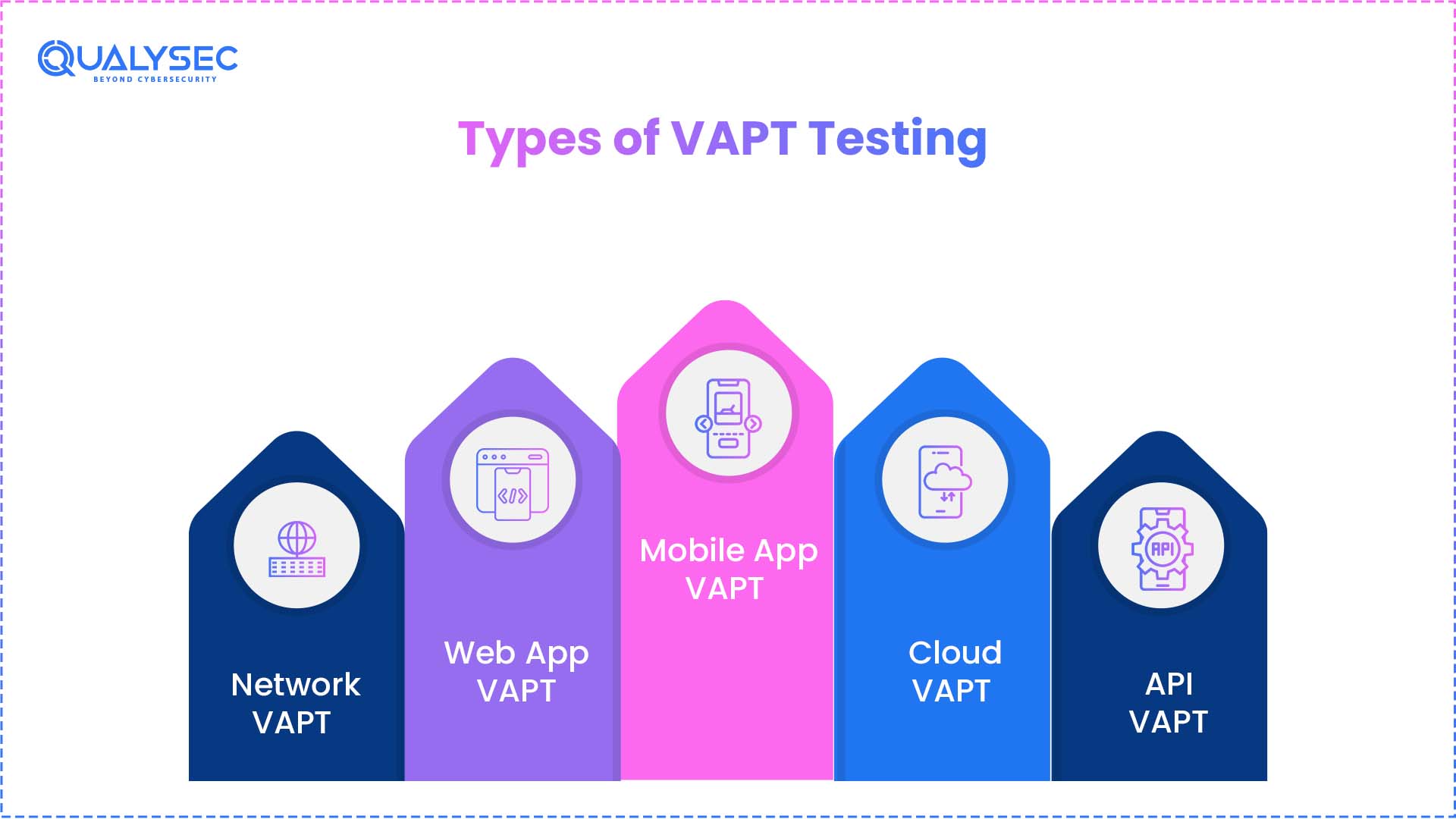
1. Network VAPT
This category is concerned with the safety of network infrastructure.
Scope includes:
- These are internal and external networks.
- Switches, routers and firewalls.
- Unprotected ports and services.
Objective: Find vulnerabilities in network setups and ports.
2. Web Application VAPT
This is centered on web-based applications and web-based platforms.
Scope includes:
- Authentication and login procedures.
- User input handling
- Session management systems
Objective: Find weaknesses in application logic and user interfaces.
3. Mobile Application VAPT
This determines the safety of Android and iOS mobile applications.
Scope includes:
- Data storage on devices
- Access control and settings.
- Connection to the back-end services.
Objective: Be sure that mobile applications are data-secure and resistant to unauthorized access.
4. Cloud VAPT
This is aimed at cloud-based infrastructure and services.
Scope includes:
- Cloud storage and databases
- There is identity and access management (IAM).
- Cloud resource configuration.
Objective: To detect cloud misconfiguration and exposure vulnerability.
5. API VAPT
This is on APIs that facilitate communication between systems.
Scope includes:
- Authentication and authorization policies.
- Data exchange processes
- Endpoint security
Objective: It is necessary to make sure that APIs do not leak sensitive information or provide unauthorized access.
Type | Focus Area | Primary Surface |
Infrastructure | Network layer | |
Applications | Browser-based systems | |
Mobile apps | Devices and APIs | |
Cloud systems | Hosted environments | |
Integrations | Data exchange layers |
All VAPT types target another aspect of an attack surface. The full security audit involves the choice of the relevant types of selection depending on the systems used.
VAPT Methodology (Step-by-Step Process)
The testing of VAPT is performed in a systematic manner in order to make the security assessment systematic and comprehensive. The phases are based on the other to lead to discovery and validated findings.
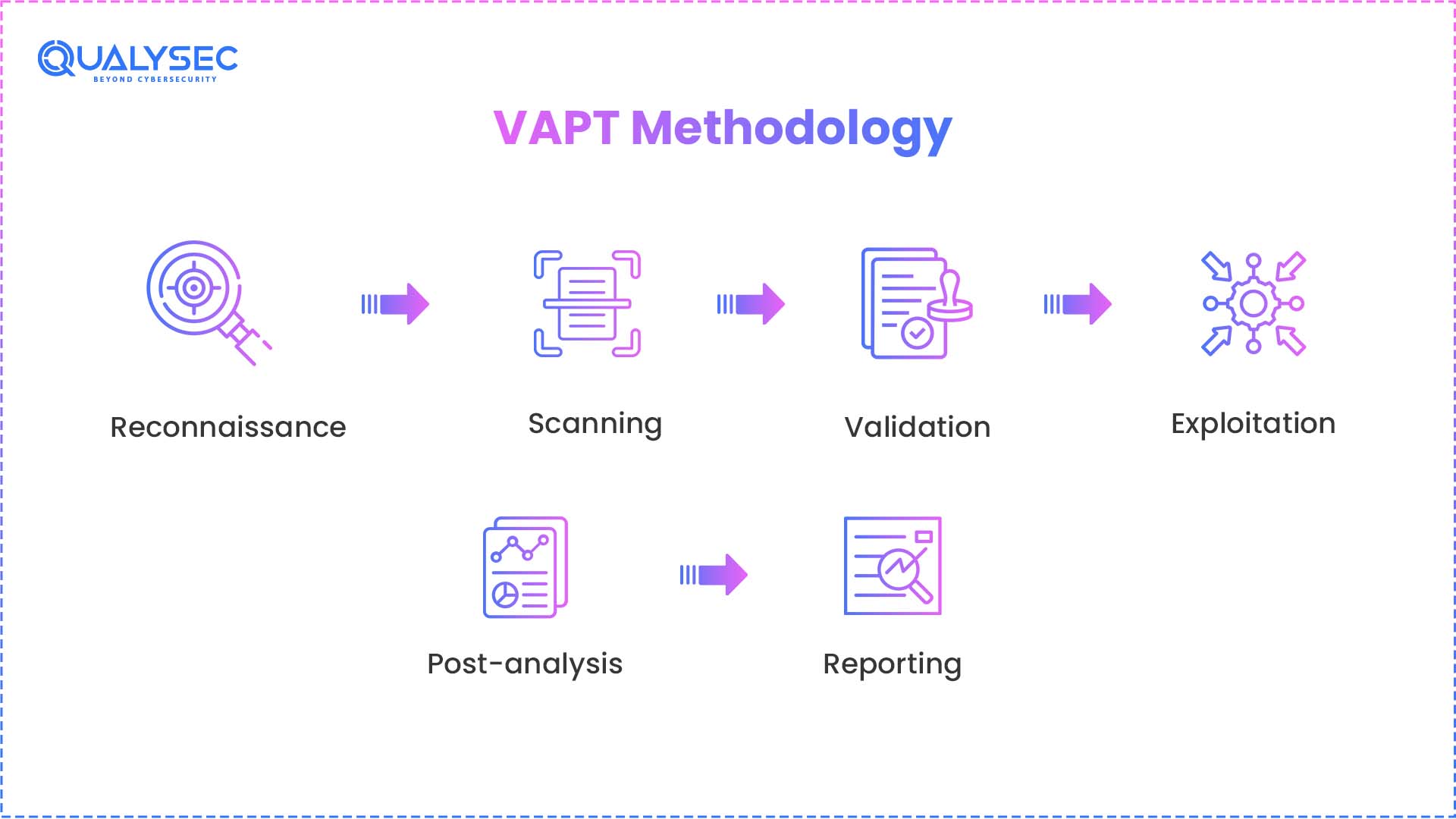
1. Reconnaissance
This stage entails gathering facts concerning the target environment.
Activities include:
- Determining domains, IP addresses and endpoints.
- Mapping publicly revealed resources.
- Collecting information about the technology stack.
Output: A predefined testing attack surface.
2. Scanning
There are automated vapt tools used to identify known vulnerabilities on the identified assets.
Activities include:
- Application scanning and system scanning.
- Identification of out-of-date software and settings.
- Preliminary vulnerability analysis.
Output: An unprocessed list of identified vulnerabilities.
We’ve put together a complete guide on vulnerability assessment reports to show you how to interpret these initial findings.
3. Validation
The specified weaknesses are examined and checked.
Activities include:
- False positives removal.
- Actually proving that the vulnerabilities exist.
- Prioritizing problems by their severity.
Output: An approved and tested set of vulnerabilities.
4. Exploitation
An effort is made to have testers deal with tested vulnerabilities in a controlled way.
Activities include:
- Testing access controls
- Working with fragile elements.
- Assessment of system responsiveness.
Output: The behavior of the system when it is simulated in the attack situation.
5. Post-Analysis
The exploitation outcomes are examined in order to see the degree of exposure.
Activities include:
- Reviewing the levels of achieved access.
- Determining the affected components.
- Determining the dispersion of the environment.
Output: The understanding of system exposure.
6. Reporting
Everything is recorded in a tabular form.
Activities include:
- Note-taking on the vulnerabilities and observations.
- Assigning severity levels
- It offers remediation advice.
Output: A detailed report in detail to the technical and management teams.
If you want to see what a professional result looks like, download a sample penetration testing report here.
Stage | Focus | Result |
Reconnaissance | Asset discovery | Attack surface defined |
Scanning | Detection | Initial findings |
Validation | Verification | Confirmed vulnerabilities |
Exploitation | Interaction | System response observed |
Post-Analysis | Review | Exposure understood |
Reporting | Documentation | Actionable report |
A formalized methodology makes the testing process dependable and reproducible as the findings are consistent, validated and documented clearly.
Talk to our Cybersecurity Expert to discuss your specific needs and how we can help your business.
VAPT vs Vulnerability Assessment vs Penetration Testing
Vulnerability Assessment, Penetration Testing and VAPT are very similar but have different scopes of operation, execution and result. These differences are useful in choosing the right approach depending on the need to be secure.
Comparison Overview
Aspect | Vulnerability Assessment (VA) | Penetration Testing (PT) | VAPT |
Objective | Identify vulnerabilities | Interact with vulnerabilities | Combine identification and interaction |
Approach | Tool-driven | Tester-driven | Hybrid |
Coverage | Broad | Focused | Broad with validation |
Output Type | Detected issues | Observed behavior | Consolidated findings |
Execution Style | Automated | Manual | Combined |
Vulnerability Assessment (VA)
- Concentrates on the identification of known problems in systems.
- Falls under the automated scanning tools.
- Gives a list of vulnerabilities identified.
Penetration Testing (PT)
- Concentrates on dealing with particular weaknesses.
- Implemented by human security testers.
- Monitors the behavior of systems under virtual conditions.
VAPT (Combined Approach)
- Combines exploration and interaction.
- Works with tools and with their hands.
- Gives a summarized result of findings.
Selection Guidance
Requirement | Suitable Approach |
Broad visibility of issues | Vulnerability Assessment |
Targeted interaction testing | Penetration Testing |
Combined evaluation | VAPT |
Both strategies have different objectives. The choice of a suitable method will be determined by the nature of the need discovered, requirements for interaction, or both.
What Happens If You Don’t Perform VAPT?
Not performing VAPT testing puts systems unscreened to real-world threats. This leaves loopholes, which are not realized until they are used.
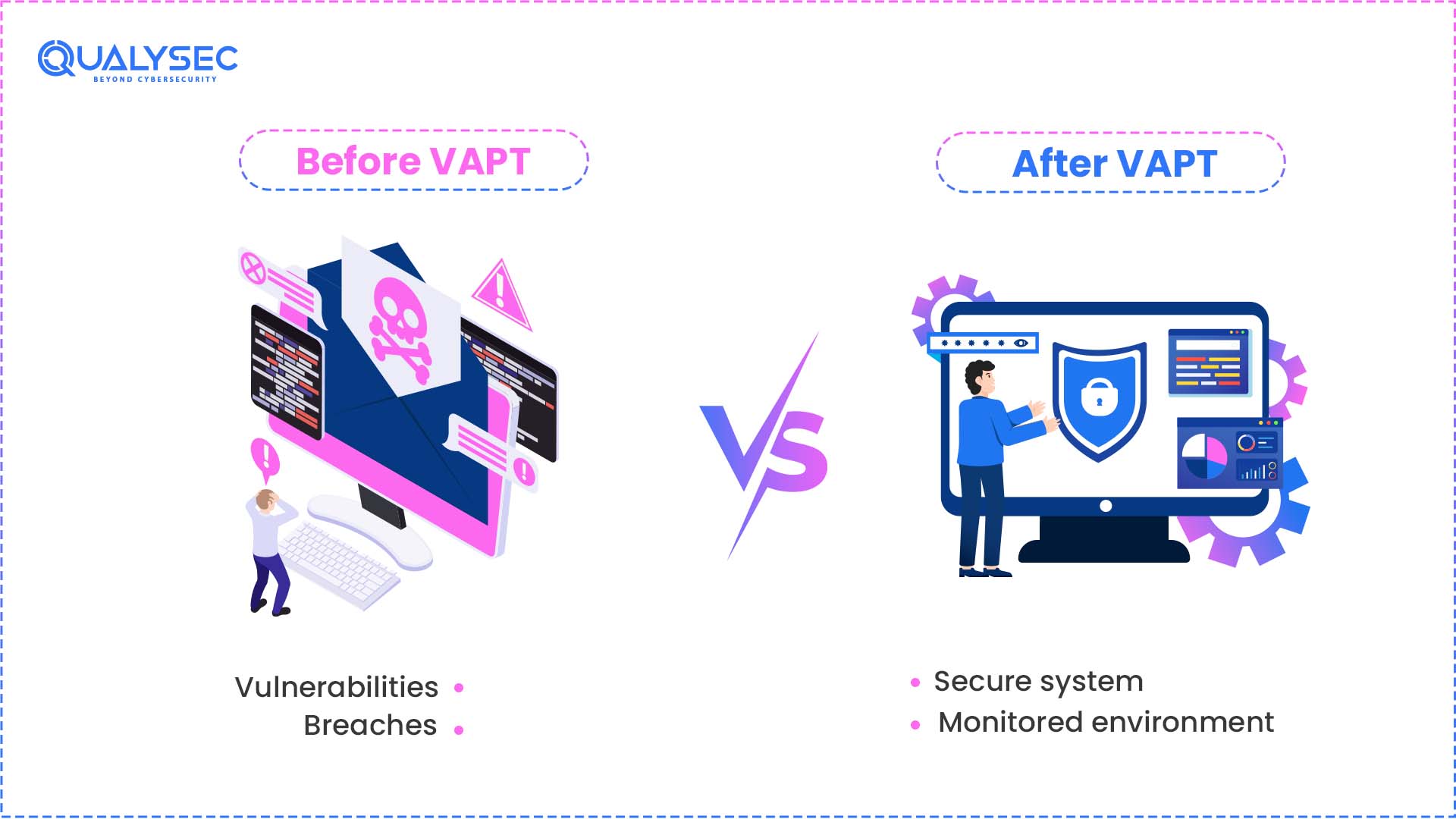
1. Undetected Exposure Points
Security gaps are not visible to systems and applications without testing.
Outcome:
- Unmonitored entry points
- The undetected vulnerabilities of setups.
- More visibility-free attack surface.
2. Higher Likelihood of Security Incidents
Unauthorized access to systems that are not frequently checked is more likely to occur.
Outcome:
- Additional likelihood of intrusion.
- Intruder interactions with the system.
- Breaking the normal functions.
3. Data Exposure Risks
Systems which are not validated can also open sensitive information to unwanted access.
Outcome:
- Leakage of classified information.
- Inability to control information stored.
- Potential misuse of data
4. Compliance Gaps
There may be a failure of organizations to comply with the necessary standards of security validations.
Outcome:
- Audit failures
- Regulatory issues
- Delays in certifications
5. Operational Disruptions
Weaknesses that are unknown may have an impact on the reliability and availability of the system.
Outcome:
- Service interruptions
- System instability
- Unexpected downtime
6. Increased Recovery Effort
It takes more time and resources to fix the problems that have emerged.
Outcome:
- Extended resolution cycles
- Higher operational effort
- Slow recovery of normal operation.
Scenario Overview
Situation | Without VAPT |
System exposure | Not identified |
Security gaps | Remain unverified |
Data protection | Not validated |
Compliance readiness | Incomplete |
System stability | Uncertain |
Suspect systems have unknown exposure. In the absence of structured testing, there are only unmeasured but present risks.
Why VAPT Testing Is Important for Businesses
The VAPT test is important in assisting organizations to retain control over their online environment. It is used to make informed decisions as it helps in establishing clarity on the reliability and security preparedness of systems.
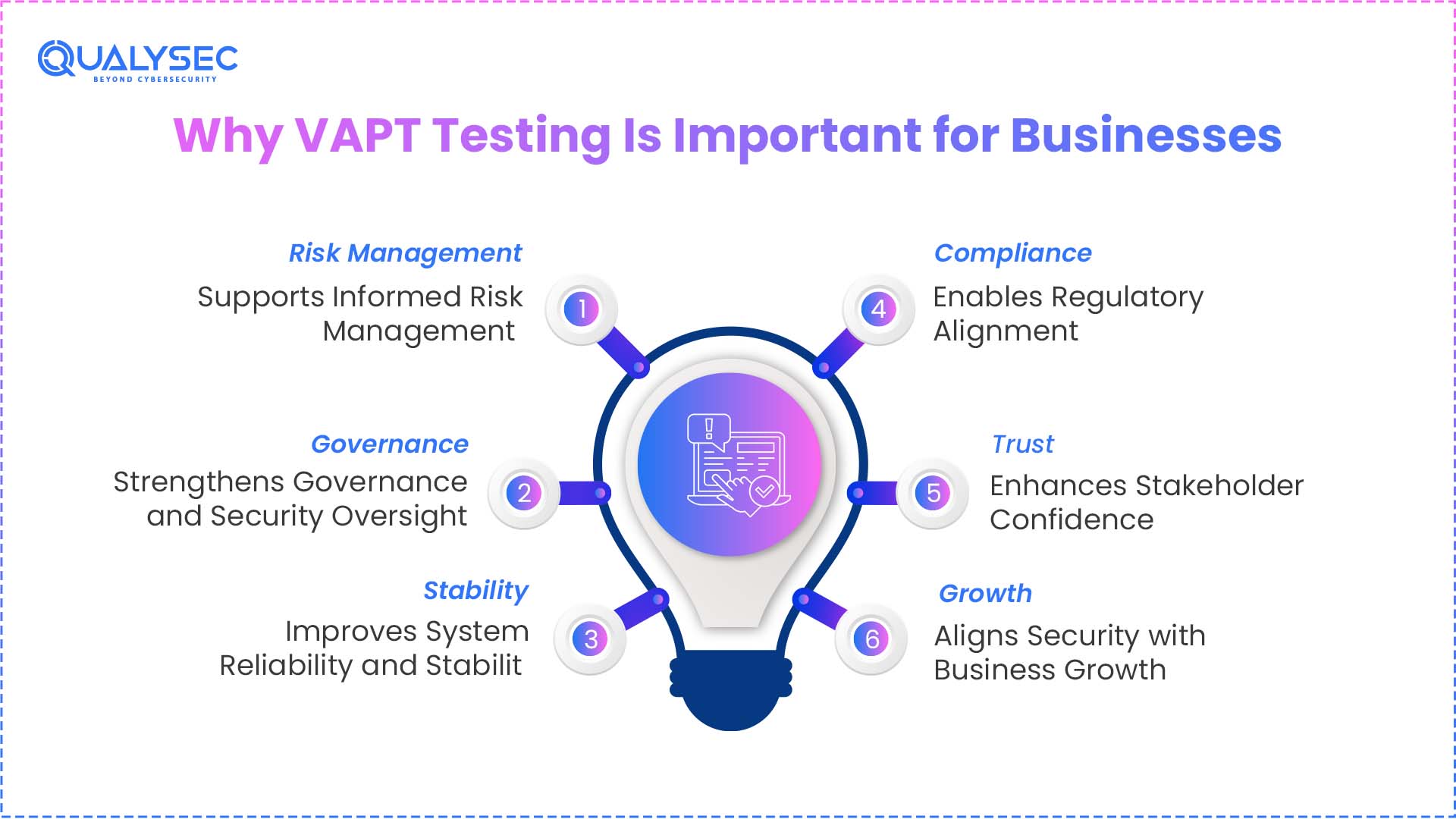
1. Supports Informed Risk Management
Insecurity risks are managed through sound insights in organizations.
Business relevance:
- Facilitates systematic analysis of risks.
- Helps emphasizes security.
- Reconciling technical discoveries with business goals.
2. Strengthens Governance and Security Oversight
Security testing is a part of enhanced internal control and accountability.
Business relevance:
- Enhances transparency among leaders.
- Endorses security policies and structures.
- Improves surveillance and control systems.
3. Enables Regulatory Alignment
Organizations have to show that security controls have been reviewed on a regular basis.
Business relevance:
- Helps to satisfy audit expectations.
- Meets the regulatory requirements.
- Favors documentation and compliance procedures.
For a deeper dive into meeting industry standards, check out our comprehensive guide on compliance audits.
4. Improves System Reliability and Stability
Security testing helps in the stable performance of the system.
Business relevance:
- Minimizes unaccounted system behavior.
- Enhances business continuity.
- Favors consistent online operations.
5. Enhances Stakeholder Confidence
Security assurance has some implications for the perception of an organization by the stakeholders.
Business relevance:
- Develops trust with other clients and partners.
- Shows their adherence to security practices.
- Develops organizational credibility.
6. Aligns Security with Business Growth
Security should grow as the size of organizations increases.
Business relevance:
- Favorable to new technology adoption.
- Facilitates the secure growth of online services.
- Keeps a check on expanding infrastructure.
Business Value Overview
Area | Contribution |
Risk Management | Structured decision-making |
Governance | Improved oversight |
Compliance | Regulatory alignment |
Operations | Stable systems |
Trust | Strong stakeholder confidence |
Growth | Secure scalability |
Security testing is not a technical issue only. It is a business activity that promotes stability, administration and long-term development.
When Should You Perform VAPT Testing
VAPT testing is supposed to be performed with regard to certain stages in the system and application cycle so that security controls are always verified.
1. Before Production Deployment
Before systems or applications are made live, testing must be done.
Trigger:
- A new application or system is ready to be rolled out.
Timing focus: Pre-deployment testing phase.
2. After System or Application Changes
Any change is capable of introducing new variables in the environment.
Trigger:
- Code updates
- Feature additions
- Infrastructure modifications
Timing focus: Post-change check.
3. During Scheduled Security Reviews
Companies tend to have a fixed security review cycle.
Trigger:
- Scheduling of the review every quarter or annually.
- Internal security audits.
Timing focus: Periodic validation
4. Before External Audits
Audit preparation schedules are frequently compressed to security testing schedules.
Trigger:
- Upcoming compliance audits
- Certification processes
Timing focus: Pre-auditing preparation.
5. After Integration of New Systems
Including new elements alters the general atmosphere.
Trigger:
- Third-party integrations
- API connections
- Platform expansions
Timing focus: Post-integration validation
6. During Infrastructure Scaling
Scaling may have an impact on system exposure and configuration.
Trigger:
- Migration to the clouds.
- Digital expansion of digital services.
Timing focus: Phase validation scaling
Lifecycle Overview
Stage | Trigger Point | Timing Purpose |
Pre-deployment | Before launch | Initial validation |
Post-change | After updates | Change verification |
Periodic review | Scheduled cycles | Ongoing validation |
Pre-audit | Before audits | Compliance readiness |
Post-integration | New systems added | Environment validation |
Scaling phase | Infrastructure growth | Configuration validation |
The test of VAPT works best when it is done according to system lifecycle events, so that the validation is done every time the environment has changed.
Common Challenges in VAPT Testing
VAPT testing is a test with several steps and requirements. Organizations are usually confronted with issues that make the results less accurate, complete, and available.
1. Incomplete Asset Visibility
The scope of testing does not always cover all the systems, endpoints and environments.
Issue:
- Lack of applications/APIs.
- Untracked out-of-scope assets.
- Biased coverage of the environment.
2. High Volume of Scan Results
Robotic devices produce data in large volumes.
Issue:
- Wildly excessive observed vulnerabilities.
- Inability to specify useful findings.
- Unnecessarily heavy analysis process.
3. False Positives
Not all the issues identified can be the real vulnerabilities.
Issue:
- Wrong identification of risks.
- Misunderstanding in validation.
- Less confidence in outcomes.
4. Dynamic and Changing Environments
Contemporary systems develop in a dynamic way.
Issue:
- Regular changes in the behavior of systems.
- Components introduced through testing.
- Inability to take a consistent assessment.
5. Limited Context of Findings
Technical deliverables may be out of the business or operational context.
Issue:
- Inability to interpret actual impact.
- Difficulties in prioritisation.
- Incongruency between business and technical teams.
6. Resource Constraints
The process of testing consumes time, resources and expertise.
Issue:
- No or a limited number of professionals.
- Time-bound testing windows
- Limitations to operating in large environments.
7. Complexity of Modern Architectures
Systems may comprise several interrelated units.
Issue:
- Interdependent applications and services.
- Connectivity of cloud and APIs with on-prem systems.
- Difficulty in global assessment.
Challenge Overview
Challenge | Impact Area |
Incomplete visibility | Coverage gaps |
High scan volume | Analysis complexity |
False positives | Accuracy issues |
Dynamic environments | Consistency challenges |
Limited context | Decision difficulty |
Resource constraints | Execution limits |
System complexity | Assessment difficulty |
The problem with VAPT testing is that scale, complexity, and data volume frequently result in challenges in testing and interpretation of the findings, as well as the use of the results.
Best Practices for Effective VAPT Testing
A well-organized strategy, proper testing techniques, and follow-ups are the key to VAPT’s successful implementation. These practices are useful in ensuring that there are reliable and usable outcomes.
1. Define a Complete and Accurate Scope
A well-defined scope should be used to start testing and cover all the assets.
Best practice:
- Including applications, networks, APIs, and cloud parts.
- Have an updated inventory of assets.
- Do not omit interrelated systems.
2. Use a Hybrid Testing Approach
The balanced coverage is guaranteed with a combination of automated tools and manual techniques.
Best practice:
- Employ automated scans to detect generally.
- Use manual tests to further test.
- Compare the results of the methods.
3. Standardize Testing Procedures
Regular procedures enhance the consistency of testing cycles.
Best practice:
- Adhere to systematic approaches.
- Apply standardized tests.
- Repeatability of document testing.
4. Maintain Clear Documentation
Correct documentation will make sure that results are correctly documented and interpreted.
Best practice:
- Test scope, procedures and observations on records.
- Have reports under version control.
- Have traceability of findings.
5. Prioritize Findings Systematically
The systematization of findings assists in handling huge amounts of data.
Best practice:
- Rank the vulnerabilities based on severity.
- Cluster-related problems.
- Have well-organized reporting formats.
6. Perform Retesting After Changes
The process of validation should not be stopped after the fixing.
Best practice:
- Review the issues that were identified before.
- Confirm resolution status
- Update reports accordingly
7. Ensure Secure Testing Environment
The production systems should be controlled and safe when it comes to testing.
Best practice:
- Establish safe testing limits.
- prevent unwanted system interruptions.
- Liaise with concerned groups when carrying out tests.
Practice Overview
Practice | Focus Area |
Scope definition | Coverage accuracy |
Hybrid testing | Method balance |
Standardization | Process consistency |
Documentation | Record keeping |
Prioritization | Data organization |
Retesting | Validation continuity |
Safe execution | Controlled testing |
Regular practices make the VAPT outcomes structured, traceable and consistent in the various environments and testing cycles.
How to Choose a VAPT Service Provider
The choice of a service provider of VAPT must be keen on the capabilities, approach and deliverables. The assessment quality is based on the way the provider fits into the technical and organizational needs.
1. Technical Expertise and Certifications
Evaluate the experience and the qualification of the testing team.
What to evaluate:
- Industry-recognized certifications
- Diversified experience.
- Technical profundity of security testing.
2. Testing Methodology and Approach
Know the way the provider does assessments.
What to evaluate:
- Application of systematic approaches.
- Integration of various methods of testing.
- Stability in implementation processes.
3. Reporting Format and Detail Level
Check the way findings are reported.
What to evaluate:
- Clarity of reports
- Level of technical detail
- Finding structure and organization.
4. Scope Handling and Flexibility
Test provider definition and management of scope.
What to evaluate:
- Capability to manage complicated settings.
- Openness to the addition of numerous types of assets.
- Concrete scope definition procedure.
5. Compliance and Industry Alignment
Make sure that the provider is conversant with pertinent standards.
What to evaluate:
- Understanding of regulatory systems.
- Practice in compliance-based testing.
- Conformity to audit requirements.
6. Communication and Coordination
Assess the interaction of the provider.
What to evaluate:
- Clarity in communication
- Frequent updating in the course of testing.
- Defined points of contact
7. Post-Assessment Support
Know what occurs after the assessment is done.
What to evaluate:
- Follow-up discussion availability.
- Clarification of findings
- Re-evaluation should be supported, should it be necessary.
To help you compare your options, we’ve reviewed the top 20 VAPT testing companies in India.
Evaluation Overview
Criteria | Focus |
Expertise | Technical capability |
Methodology | Testing approach |
Reporting | Output clarity |
Scope handling | Coverage flexibility |
Compliance | Regulatory alignment |
Communication | Coordination quality |
Support | Post-assessment interaction |
An organized assessment system will be critical in making sure that the provider of choice matches the technical specifications, organizational expectations and anticipated outputs.
Why Choose Qualysec for VAPT Testing
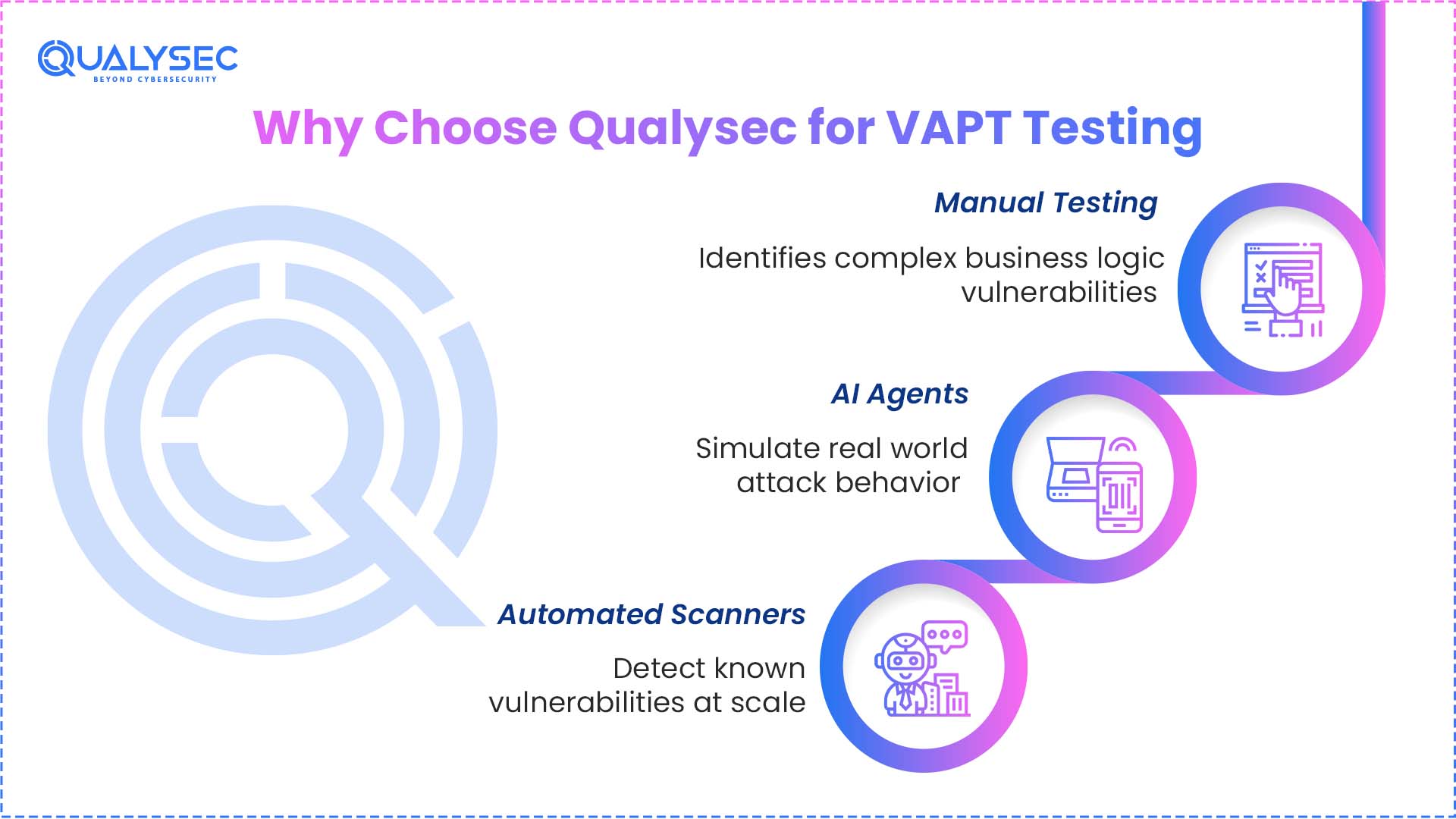
Qualysec offers its VAPT services with a high degree of accuracy, thoroughness, and realistic security results. In addition to conventional penetration testing, Qualysec also focuses on Human-led AI Penetration Testing, a combination of expert analysis, AI-driven testing, and automated scanning to provide wider and more accurate coverage.
Human-led AI Penetration Testing Approach
Qualysec has three layers testing model:
Manual Testing
Hands-on testing is conducted by the security experts to reveal business logic vulnerabilities, authentication problems, and elaborate attack paths which are not always detected by the tools.
AI Agents
The agents that are based on artificial intelligence can mimic the behavior of a real-world attacker, make testing faster, and assist in more effectively identifying latent hazards.
Automated Scanners
The sophisticated scanners identify the known vulnerabilities, misconfigurations, and open services among systems in a short duration.
Comprehensive Coverage
The VAPT services provided by Qualysec include:
Clear Reporting and Ongoing Support
Qualysec gives structured reports that are categorized with findings of level of severity, evidence of validation and remedial advice. Others, such as clarification of findings, remediation discussions or retesting where necessary, are also supported.
Latest Penetration Testing Report
Compliance Alignment
Some of the common frameworks that can do the evaluations include:
- ISO 27001
- PCI-DSS
- GDPR
The Human-led AI Penetration Testing model by Qualysec combines human expertise, AI-led simulation, and automated coverage in one model, and therefore, the assessment becomes more balanced and complete.
If your organization needs a modern VAPT partner with deeper testing coverage, Qualysec’s Human-led AI Penetration Testing approach offers a structured way to assess applications, infrastructure, and digital assets with greater precision.
Ready to see how our Human-led AI approach can secure your specific environment? Schedule a free consultation with our security team.
Conclusion
In the modern threat environment, VAPT testing is not an option anymore. It allows organizations to go beyond speculation and have an explicit, tested view of their security position based on formalized vulnerability assessment and penetration testing.
VAPT is often useful not only to discover the weaknesses in the system but also to certify the behavior of the systems in actual circumstances and ensure that the security controls do not fail to comply with the expectations. Such transparency will aid in making better decisions, improving governance, and having more stable digital systems.
To those organizations that want to go beyond traditional testing, such as the solutions provided by Qualysec, offer a more progressive way of doing so with Human-led AI Penetration Testing, which combines professional knowledge with AI-generated depth to provide a more thorough and modern security test.
While VAPT is critical, choosing the right partner for your overall security is just as important – see our list of the top cyber security companies in India to learn more.
Get a clear idea of what VAPT testing will cost for your system.

FAQs
1. What is VAPT testing?
VAPT testing (Vulnerability Assessment and Penetration Testing) is a test that is used to detect and confirm security vulnerabilities in systems. It integrates the detection and testing to test the interaction of vulnerabilities in a real-life context.
2. What is VAPT in cyber security?
VAPT is a concept of cyber security that involves the evaluation and testing of systems to detect security vulnerabilities and test their response to guided conditions. It aids in making sure that applications, networks and infrastructure are scanned properly against vulnerabilities.
3. What is the full form of VAPT?
Vulnerability Assessment and Penetration Testing is the complete acronym of VAPT. It is a unified method of determining and communicating vulnerabilities systematically.
4. What are the types of VAPT testing?
VAPT tests can be network, web application, mobile application, cloud and API. Both types are concerned with different levels of the system environment.
5. What is the VAPT process?
Some of the stages of the VAPT process are reconnaissance, scanning, validation, exploitation, and reporting. All of the levels help determine and report system behavior in the testing phase.
6. How often should VAPT testing be performed?
The VAPT testing must be conducted on the most important lifecycle events, like pre-deployment, post-updates, and scheduled security reviews. Consistent testing is used to make sure systems are tested regularly.
7. What is the difference between vulnerability assessment and penetration testing?
Vulnerability testing and penetration testing are two aspects that differ in the way they deal with vulnerability and security issues. Up to now, VAPT is a combination of both methods into one.





















































































































































































































































































































































































































































































































































































































0 Comments