In today’s world where the development and introduction of new technologies are happening faster than before, one such rapidly growing technology is a web application. Web applications use APIs (application programming interfaces) for sharing and connecting the data between users. As businesses are dependent on the usage of APIs, they are prone to attacks by hackers and cybercriminals. This is where API security testing comes in.
API security testing is important in making a safe place for users to share and receive data. This blog highlights the significance of the API security testing checklist & its guidelines to be followed by organizations to ensure data privacy.
What Is API Security Testing?
API security testing involves assessing the security measures of Application Programming Interfaces (APIs) to protect them against unauthorized access, data breaches, and other vulnerabilities. It verifies if APIs adhere to necessary security standards and best practices. API security testing includes evaluating authentication methods, such as API keys or tokens, to confirm they prevent unauthorized users from accessing sensitive data or functionalities. It also examines authorization controls to ensure that users only authorized users have access to the resources. Additionally, API security testing checks for encryption protocols to secure data transmitted between clients and servers. It involves conducting penetration tests to identify potential security gaps and vulnerabilities that hackers could exploit. By performing API security testing, organizations can enhance the overall security posture of their applications and systems, mitigating security risks and safeguarding sensitive information.
What Is an API Security Checklist?
APIs are prone to attacks by cyber-criminals, basic security checklist is needed to ensure that the data is protected. These checks will help the organizations cover their weak spots and make sure their data is safe and secured.
API security testing is important because these APIs act as barriers between the third-party resources and the company’s resources. If either of these resources is compromised then the risks associated with it would also be large. This happens because security breaches can access and harm sensitive information. A Complete API security testing checklist needs to include all the steps such as :
- All the assets associated with the digital supply chain and APIs are covered and assessed.
- The focus shall be on runtime protection.
- Ensure a Strong API security plan after the security testing.
Why API security is important
A firm must prioritize API security testing to keep digital assets safe. We need to secure the sensitive data exchanged between the user and the company’s resources. We must prevent data leaks and protect it from theft by cybercriminals. Apart from these reasons, the other reasons are as follows:
1. Integration Demands
Most businesses have undergone digital transformation and have made their presence online. APIs are a great set of tools but without API integration, sensitive data is left unsecured and hence needs to be protected.
2. Dependency on APIs
Cloud-based web applications depend on APIs. APIs are essential for exchanging data. If there is any vulnerability unchecked, this can affect the whole cloud-based web application. Hence API security testing is essential for avoiding the risk.
3. Unique API Vulnerabilities
APIs have their own set of vulnerabilities. API access cannot be just protected by the current policies provided. Cybersecurity companies like Qualysec can expose those API vulnerabilities that are not properly covered by standard security methods and they can also tailor custom solutions.
APIs introduce unique security challenges, and traditional security solutions designed for web applications may fall short. Attackers can exploit API vulnerabilities not adequately addressed by generic security measures, making specialized API security solutions necessary.
4. Complex Ecosystems
The rise of microservices architectures further complicates API security. Numerous interconnected microservices communicate through APIs, creating an intricate web of potential vulnerabilities.
5. Exposure to Threats
The increased number of application programming interfaces (APIs) has exposed them to cybercriminals. If we don’t minimize threats, their exposure and attacks increase. Every single API endpoint can become a potential ransomware call, so we should pay additional attention to firewalls and other protective algorithms.
Types of API Security Testing
1. REST APIs Security Testing
Just think about REST APIs as a postman. They use a system called JSON system which uses the internet to perform various tasks like sending, getting, and deleting messages. Storing these messages in a specific order to make them safe, is much like securing an object behind a closed door, which is why we call it the API gateway. In this security testing, the testing firm installs the REST APIs behind the API gateway to protect it.
2. SOAP APIs Security Testing
Consider SOAP APIs as special mail trucks that carry structured data, thus providing benefits over the Internet. Cybersecurity firms usually protect data with a system known as HTTPS, and then the cybersecurity firms encrypt the data with digital signatures and codes. A code of conduct known as Web Services (WS) protocols is followed during SOAP API security testing, which secures the communication
3. GraphQL Security Testing
GraphQL is like an interpreter which tells clients how to interact with information. This solution also enables the existing data to meet these tasks. Developers communicate with GraphQL to retrieve specific data from single or multiple sources. However, the security of GraphQL is hard due to the flexible nature of the tasks. During GraphQL API security testing, risks are minimized by limiting the throttling defining a maximum query depth, and using a query timeout.
API Security Best Practices
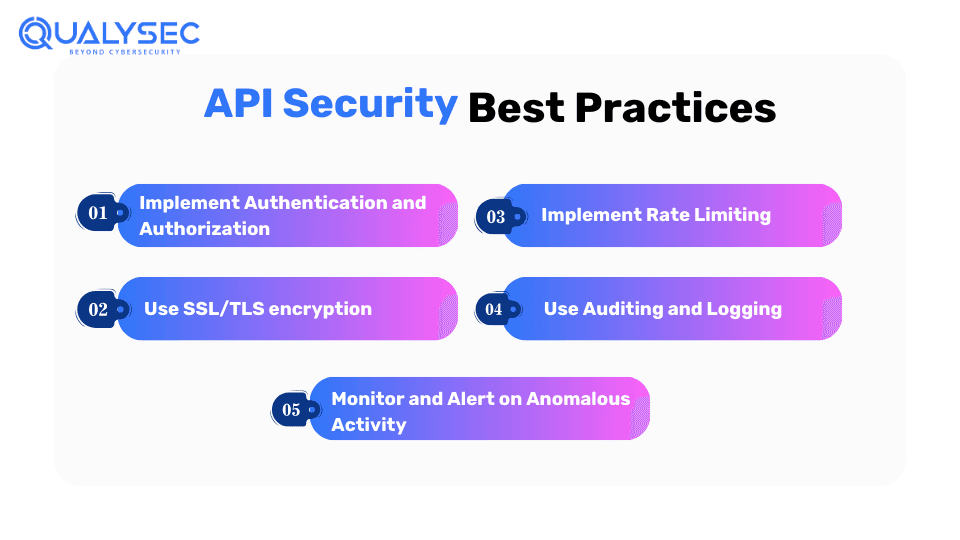
APIs are needed despite these dangers mentioned above, APIs. Nearly every online application that needs to connect to others requires APIs.
Every time we introduce a new API, it opens a new gate for hackers to intercept personal data. Therefore, while managing software integration the firm implementing the integration must understand API security issues as well. Cybersecurity firms measure and defend weak spots against cyber-attacks and prevent unauthorized access to sensitive data.
1. Implement Authentication and Authorization
In simple words, implementing authentication means establishing authentication through valid credentials. A Firm should prevent unauthorized access by developing a system that logs in with valid credentials and authenticates before providing access to the data.
2. Use SSL/TLS encryption
All communications between clients and APIs must be through protocols such as TLS protocol. According to standard security measures, it is required to implement HTTPS protocol. Encryption needs to be done before requesting or sending data out.
3. Implement Rate Limiting
Automated Malicious attacks are common nowadays. Implementation of Rate Limiting on API requests is essential as it helps shield against malicious automated attacks. This ensures that requests are actively handled.
4 Use Auditing and Logging
Auditing and logging are essential to be done, as the data needs to be tracked down. This is done to ensure that the data isn’t in the wrong hands. API request needs to be validated and monitored. This essentially ensures data privacy.
5. Monitor and Alert on Anomalous Activity
If an abnormal activity is noticed, a firm should immediately alert the cybersecurity company and thus avoid intrusion. Cybersecurity companies can fix the problem at the initial stage without letting it escalate further. Monitoring the activities ensures that the activities occurring are safe.
6. Conduct Regular API Penetration Testing
Regular API security penetration testing is necessary because developments and the introduction of new technologies are happening faster than before, and digital space is introducing new APIs now and then. In API penetration testing, cybersecurity professionals use manual techniques to find vulnerabilities present in the APIs. As a result, organizations can secure their APIs by finding and fixing vulnerabilities before they are exploited by hackers.
Feel free to look into the whole structure of a sample report. Click and download the sample right now!
Latest Penetration Testing Report

Conclusion
In conclusion, API technology is the support system for running web applications. APIs need security testing to minimize the threats and risks associated. APIs serve a lot of benefits but also they come with serval vulnerabilities. API security testing minimizes these vulnerabilities before hackers exploit them.
Implementing an API security checklist and best practices can help maximize the advantages of APIs. Thus, reducing disadvantages and improving your digital defense. Consider seeking professional help to transform the lessons from this guide into practical security changes. Begin your security checklist and ensure best practices with Qualysec today!
Qualysec offers top-of-the-line vulnerability assessment and penetration testing for APIs, web applications, mobile apps, cloud, IoT devices, etc. along with source code review and AI/ML penetration testing. Contact Us Now!
Talk to our Cybersecurity Expert to discuss your specific needs and how we can help your business.
FAQ’s
Q: Why Do You Need API Security Testing?
A: To ensure APIs are secure against attacks, protecting data and systems. We consider API Security Testing important because we need to keep digital assets safe. The data that flows between the user and the company’s resources is sensitive and we need to secure it.
Q: What is the REST API?
A: REST API is an architectural style for web services, using HTTP methods (GET, POST, etc.) and JSON or XML for data exchange.
Q: How Does API Security Testing Work?
A: API Security Testing works by ensuring APIs are secure, reliable, and compliant with standards. API Security involves:
- Discovering APIs and endpoints.
- Scanning for vulnerabilities.
- Penetration testing.
- Reporting and remediation.























































































































































































































































































































































































































































































































































































































0 Comments