What is an IT Compliance Security Audit? IT Compliance Security is a detailed review of an organization’s network security, security measures, and IT systems security. Organizations conduct IT Compliance Security Audit to identify vulnerabilities in the organization’s system. By conducting an IT Compliance security audit, organizations can identify whether the methods they follow fall under the industry regulations or not, it is also done to close security gaps.
It can also be defined as a comprehensive assessment of a firm. A report indicated that in 2024 there were a total of 875,603,102 known data breaches. These breaches can be avoided by just conducting an IT Compliance Security Audit. Overall IT Compliance Security Audit not only helps organizations with compliance but also helps to protect sensitive information like user information and data logs. This blog aims to provide a comprehensive overview of IT compliance security audits.
What is an IT Compliance Security Audit?
An IT compliance security audit is an independently conducted assessment that evaluates an organization’s cybersecurity tools, methods, and policies to comply with industry standards such as GDPR, PCI DSS, HIPAA, SOC 2, etc. Further, certification authorities or organizations that set standards ensure that specific requirements, compliance regulations, and laws are met through examinations.
The primary goal is to ensure that an organization’s IT processes comply with existing regulations. These audits are important because they help to protect industries’ valuable privacy and confidentiality.
How Does an IT Compliance Security Audit Work?
How does an IT Compliance Security Audit work? An IT Compliance Security Audit determines if an organization’s IT and Network Security comply with industrial regulations and standards. The Auditing firm evaluates the company’s policies, processes, and controls to ensure that the organization is following the industrial standards set. They not only ensure whether the organization is following the industrial regulations but also suggest improvements and detect weaknesses if any.
During an IT Compliance Security Audit, the firm audits the firm/ organization on different aspects such as compliance with different regulations, policies, and security measures. This process ensures that the identification of vulnerabilities is done and a report is provided to the organization so that the organization is informed about their compliance with the industrial regulations.
An IT compliance audit discovers security flaws, suggests methods to improve protection, and provides a complete report for informed decision-making. Additionally, it protects the organization’s digital assets by maintaining compliance with regulatory standards and best practices, as well as strengthening security measures for best resilience against cyber threats.
Difference Between IT Compliance Audit and IT Security Audit
| Aspect | IT Compliance Audit | IT Security Audit |
|---|---|---|
| Focus | Ensures adherence to laws and regulations regarding information security. | Identifies and mitigates security risks and vulnerabilities to protect the organization from cyber threats. |
| Purpose | Ensures the company is following laws and regulations to avoid legal trouble and demonstrate a commitment to information security. | Protects the organization’s digital assets and infrastructure by identifying and addressing security weaknesses. |
| Scope | Evaluates compliance with laws, regulations, policies, and standards related to information security. | Focuses on the security posture of the organization, including the assessment of security policies, infrastructure, and protection measures. |
| Areas Assessed | Compliance with laws and regulations, data protection measures, information handling procedures, and adherence to security policies. | Security policies and procedures, network security, access controls, vulnerability management, incident response, and security awareness training. |
| Key Benefits | Helps companies avoid legal penalties, demonstrates commitment to security, and enhances trust with stakeholders. | Strengthens security posture, reduces the risk of data breaches, protects against cyber threats, and improves overall security resilience. |
| Examples of Regulations | GDPR, HIPAA, PCI DSS, SOX | ISO 27001, NIST Cybersecurity Framework, CIS Controls, GDPR, HIPAA |
To have a thorough grasp of the penetration testing report that helps with compliance audit, feel free to download the sample report.
Latest Penetration Testing Report

What is the Main Purpose of an IT Compliance Security Audit?
An IT compliance security audit is designed to determine whether an organization’s IT systems, processes, and controls adhere to applicable regulatory demands, accepted standards, and optimal practices. Moreover, audits will help in achieving the goal of creating a secure and reliable information system that will protect organizations’ data from unauthorized access, misuse, or any breach.
IT compliance security audits aim to: identify vulnerabilities in the systems, ensure regulatory compliance, Assess the effectiveness of current Security Controls, mitigate security risks, and enhance Trust and Confidence.
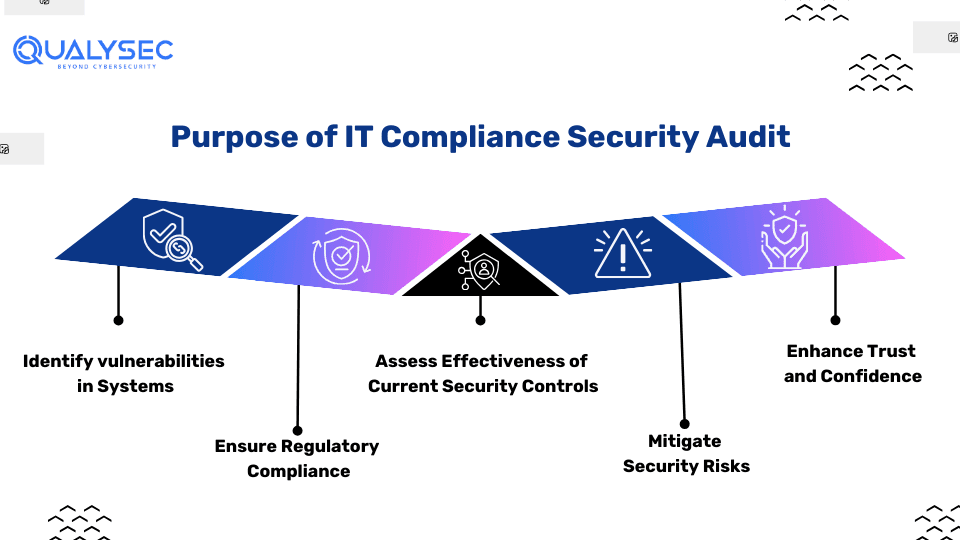
1. Identify Vulnerabilities in the Systems
Audits are means to find any security flaws or possible entry points in IT infrastructures.
2. Ensure Regulatory Compliance
Auditors aim to confirm that the organization’s IT practices are aligned with the applicable laws and regulations, such as GDPR, HIPAA, PCI DSS, or ISO 27001.
3. Assess Effectiveness of Current Security Controls
Audits determine whether the security controls and procedures implemented by the organization to protect its data are effective.
4. Mitigate Security Risks
A key benefit that audits offer is the ability to identify vulnerabilities and areas of non-compliance, which in turn enables organizations to implement measures that will reduce risks and strengthen their security posture.
5. Enhance Trust and Confidence
The ability to successfully pass audits assures partners, customers, and regulators about the organization’s reliability and security measures for protecting data.
IT Compliance Security Audit Checklist
An IT compliance security audit checklist includes all the areas that are needed to be reviewed. It ensures that the areas specified are within the industrial regulations and norms. Organizations must ensure that the data is protected. Here’s a simplified version of what might be on such a checklist:
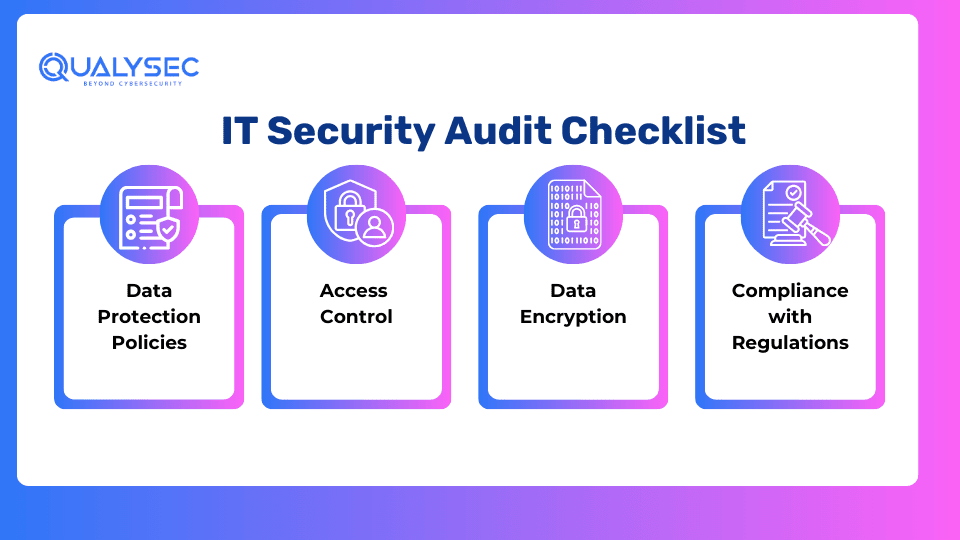
1. Data Protection Policies
-
- Provide thorough data protection guidelines that address all aspects of managing, storing, and processing data at every stage.
- The Policy needs to be monitored and updated frequently to meet the changing threats and legal requirements.
- Procedures for data backup, retention, and data secure deletion.
2. Access Control
-
- User access management: Periodic assessment and adjustment of users’ permission based on their assigned roles and responsibilities.
- Strong authentication mechanisms: Implementation of multi-factor authentication (2FA) for accessing sensitive systems as well as data.
- Access monitoring and logging: Continuous monitoring of access logs to facilitate detection and elimination of attempts of unauthorized access.
- Principle of least privilege: Installing the minimum level of access for the users to successfully perform the duties.
3. Data Encryption
-
- Encryption protocols: Implementing encryption for data at rest, data in transit, and data processing.
- Encryption key management: Securing the storage and management of encryption keys to avoid unauthorized access.
- Regular encryption audits: Regular reviews to make sure that all confidential data is properly encrypted.
4. Compliance with Regulations
- Regulatory alignment: Comply with regulations like GDPR, CCPA, and HIPAA for data protection·
- Regular compliance audits: Undertake internal and external audits to evaluate compliance with regulatory norms.
- Data breach response plan: Create a formal data breach response and reporting policy, consistent with regulatory obligations.
5 Major IT Compliance Regulatory Frameworks
The following 5 major frameworks have been developed to provide data privacy, security, and integrity assurance in many sectors and industries. However, compliance with these rules is not only required from a legal point of view but also it is essential to build trust with customers and partners.
1. HIPAA (Health Insurance Portability and Accountability Act)
HIPAA sets the standard for the confidentiality of patient information. Hence, all PHI (public health information) holders must have all required physical, network, and application security measures in place.
2. PCI-DSS (Payment Card Industry Data Security Standard)
PCI-DSS is a set of security norms stating that companies that accept, process, store, or transmit credit card information must maintain a secure environment. Hence, compliance with the PCI-DSS is a must for organizations that process payment card transactions of any kind.
3. SOC 2 (System and Organization Controls 2)
SOC 2 is a framework established by the American Institute of CPAs (AICPA). It concentrates on the security, availability, processing integrity, confidentiality, and privacy of service organization controls. Additionally, it is frequently employed by cloud computing and technology companies.
4. ISO (International Organization for Standardization)
ISO 27001 is a well-known international standard on information security management. Moreover, it provides guidelines for setting up, operating, safeguarding, and continually enhancing the information security management system (ISMS).
5. GDPR (General Data Protection Regulation)
GDPR is one of the regulations of EU law on data protection and privacy in the European Union and the European Economic Area. It is a transfer mechanism for personal data outside the EU and EEA and primarily aims to give control to individuals over their data and to facilitate business regulations across borders.
How Penetration Testing Helps with IT Compliance Security Audit
Penetration Testing helps IT Compliance Security Audit by complying with industry standards. This compliance requires regular security testing of the IT infrastructure. As a result, many industries mandate conducting penetration tests for compliance. Penetration testing in IT compliance security audits reveals weaknesses inside the networks and systems. By mimicking actual cyber attacks, it shows the possibilities for hackers, so organizations can detect and fix those gaps. This approach provides for the creation of robust security controls that meet the standards of the regulator and the best industry practices.
Penetration testing demonstrates the real image of the company’s readiness to defend the confidential data which is an important factor for passing the compliant audits. Therefore, it assists companies in maintaining trust with stakeholders, preventing financial losses, and meeting legal requirements to have a strong and sustainable information security policy.
Do you want to keep hackers away from your IT devices? Get advice by making an appointment for a free consultation call with Expert Security Consultants.
Talk to our Cybersecurity Expert to discuss your specific needs and how we can help your business.
How Often One Should Conduct an IT Compliance Security Audit?
An IT Security Compliance security audit is paramount for keeping sensitive data safe and finding out that regulations are met. Usually, audits are carried out annually. However, the frequency can be adjusted based on the standards, regulations, and needs of the industry. Routine audits assist in identifying risk areas and ensuring that controls and security policies are effective and up to date. Through continuous auditing, organizations can reduce risks, avoid data leaks, and preserve stakeholders’ trust.
Conclusion
In conclusion, IT Compliance security audits are essential. It is essential as an IT compliance audit to discover security flaws, suggest methods to improve protection, and provide a complete report for informed decision-making. Compliance audits ensure good cybersecurity practices by finding various vulnerabilities and performance evaluations and enhancing the level of trust by providing security for the user’s information. Some of the major regulatory frameworks are HIPAA and GDPR.
Using techniques like penetration testing not only enhances the scope of IT Compliance security audit but also provides a strong foundation for the security measures in place. Hence, for a better security measure of digital assets in the digital era, an organization must consult cybersecurity companies like Qualysec to enhance their security measures.
FAQs
Q. What is security audit and compliance?
A. A security audit together with compliance ensures that the system adheres to the established security standards and regulations. Moreover, this involves the assessment of systems, processes, and controls to discover vulnerabilities and maintain compliance with all legal, industry, or organizational requirements.
Q. What does an IT security audit consist of?
A. IT security audit includes analysis of the effectiveness of security measures, evaluating risks, verifying access controls, checking configurations, reviewing policies and procedures, performing vulnerability scans, and additionally, ensuring compliance with required standards and regulations. It seeks to find out the drawbacks and offer solutions to reduce the chances of cyber attacks.
Q. What is the role of an IT auditor?
A. The responsibilities of an IT auditor are related to reviewing, monitoring, and enhancing the IT governance, risk management, and control processes. Additionally, it entails assessing information systems for reliability and integrity, their compliance with policies and regulations, and providing advice on how to improve security and efficiency.























































































































































































































































































































































































































































































































































































































0 Comments