The penetration testing execution standard is becoming very important as cyber threats are growing at an unprecedented rate, with the introduction of artificial intelligence playing a greater part in the attacks. The 2025 Cost of a Data Breach report by IBM identifies that half of the breaches involved AI instances handled by an employee without company permission, with 20 per cent representing shadow AI. This contributed an additional average of USD 670,000 to the total cost of a breach. Meanwhile, a majority (70 per cent) of organizations conduct penetration testing in the context of their vulnerability management efforts, and 67 per cent of organizations conduct tests to validate compliance with security standards.
The approach of firms to address these emerging risks is by using structured frameworks. The Penetration Testing Execution Standard (PTES) is a well-formulated standard that is used to demonstrate every stage of a penetration test, from planning to final reporting. This makes tests reliable, repeatable, and compliant with global regulations/standards like ISO 27001, PCI DSS, HIPAA, and GDPR.
In all subsequent sections, we are going to describe the PTES methodology, introduce its seven phases, compare it to other penetration testing approaches and standards to identify the similarities and distinguishing features, and explain the way in which embracing the PTES approach can help organizations bolster their security level and achieve compliance with due diligence.
What is the Penetration Testing Execution Standard (PTES)?
Penetration Testing Execution Standard (PTES) is an internationally accepted framework detailing how penetration tests are supposed to be planned, executed, and reported. In 2009, a group of security professionals wrote the pentest standard to deal with inconsistencies, supervision, and quality assurance in the early procedure of penetration testing. It is common before PTES that business owners received partially complete, inconsistent or excessively technical pentest results, which did not enable them to make meaningful decisions.
PTES has become one of the most popular metrics and frameworks to conduct a penetration test, as today it balances technical focus and business understanding. It provides organizations with the idea as to what exactly they should expect from a pentest, how the vulnerabilities can be discovered and affected, and how the findings need to be reported to enable them to be compliant and remedied.
Why PTES Matters
- Consistency: PTES removes the element of guessing by providing a methodology that becomes repeatable across industries.
- ISO 27001, PCI DSS, HIPAA, and GDPR: The PTES methodology is compatible with these compliance standards, and so an appropriate methodology is achievable.
- Business Impact: It makes the technical findings of merit to the business in terms of risk that can be addressed by the executives and compliance officers.
- Credibility: PTES pentest reports help to show customers, partners, and regulators due diligence.
Such transparency is what renders PTES prominent compared to other penetration testing methodologies and standards, such as the OWASP, NIST, or OSSTMM, which can be more limited in their scope.
What is Penetration Testing and Why Does it Matter?
Also known as pentesting, it is a methodical form of security testing that employs the use of ethical hackers who carry out computerized simulations of attacks to an organization’s system, networks and applications. Penetration tests dig deeper than automated vulnerability scans by actually trying to exploit issues and demonstrating the consequences of such an attack had a malicious party decided to exploit them.
Benefits of Penetration Testing:
- Proactive Risk Identification: Pentesting helps detect the weaknesses that may not easily be detected through the normal security audits or automated scans. It supports businesses to identify latent misconfigurations, insecure integration, and logical failures before cybercriminals can identify them.
- Meeting Regulatory and Client Demands: Many regulatory standards, including the PCI DSS, HIPAA and ISO 27001, have requirements that evidence of penetration testing has been well. Companies beyond adherence drive are increasingly requiring recent pentest execution standard based reports before involving business contracts.
- Reducing Business Disruption: A well-timed penetration test can prevent costly downtime caused by breaches or ransomware incidents. By identifying high-risk vulnerabilities in advance, organizations can strengthen resilience and avoid operational halts.
- Building Trust: Hiring an outside party to complete regular penetration testing execution standards (PTES) based assessments demonstrate to partners, investors, and customers that security is well regarded as a business need. This ensures that brand reputation is not just damaged but also that in competitive markets, a company stands out.
Are you looking to strengthen your security measures for potential attacks? Do you want compliance with the required industry standards? Book a consultation with us for the best penetration testing service now!
Talk to our Cybersecurity Expert to discuss your specific needs and how we can help your business.
Different Types of Penetration Testing
This penetration testing execution standard (PTES) accommodates varying methods of testing, depending on the amount of information about the target system available to the security team. That defines the angle of the test and the type of risks that can be revealed.
1. White Box Penetration Testing
During a white box pentest, the ethical hackers are provided with all internal information including, but not limited to, source code, diagrams of their networks and systems credentials. This permits extensive testing of application logic, holes in configuration and architectural weaknesses. White box tests suit business areas that are strict with compliance, such as banks or healthcare, where regulators insist on the exhaustive demonstration of risk coverage.
2. Black Box Penetration Testing
In a black box Pentest, testers are not preinformed of the environment. They mimic an external attacker, trying randomly to find ways of entry. This form of testing can be used to determine the level of effectiveness that the perimeters and intrusion detection systems have against actual attacks, and the effectiveness of response mechanisms.
3. Grey Box Penetration Testing
A grey box pentest lies in the intermediate between the two extremes. Testers are provided with partial access, say partial credentials or architectural overviews and have to identify other vulnerabilities themselves. This is a trade-off between cost and coverage, and it is therefore a good option among organizations that desire to have both realism in the simulation of attacks as well as the spotting of critical systems.
PTES pentest methodologies can be white box, black box, or grey box, depending on the level of information shared, allowing tests to simulate insider threats, external attacks, or hybrid scenarios.
When to Use PTES vs Other Standards
Although PTES is perhaps the best-known penetration testing methodology available, it is not the only methodology. Standardised methods of penetration testing also exist, notably the OWASP, the NIST SP 800-115, the OSSTMM, and the ISSAF. Its key distinctive feature is that PTES is not as specialized as some alternatives; it aims to find the balance between the technical details and high-level clarity.
Here’s a side-by-side comparison:
| Framework | Scope & Methodology | Compliance Alignment | Deliverables |
|---|---|---|---|
| PTES | Seven phases: Pre-engagement, Intelligence Gathering, Threat Modeling, Vulnerability Analysis, Exploitation, Post-Exploitation, Reporting | Strong mapping to ISO 27001, PCI DSS, HIPAA, GDPR | Business-focused report with proof-of-exploit, CVSS scoring, remediation roadmap |
| OWASP | Application-specific security tests (OWASP Top 10, input validation, session management, etc.) | Used to meet PCI DSS and app-related security benchmarks | Detailed web app vulnerabilities with remediation for developers |
| NIST SP 800-115 | Structured testing methodologies with focus on assessment and documentation | US Government, FedRAMP, FISMA, HIPAA | Assessment procedures, compliance-focused test results |
| OSSTMM | Deep technical security testing, including physical and wireless networks | Less compliance-focused, more operational rigor | Detailed technical vulnerabilities and operational risk scores |
| ISSAF | Covers governance, risk management, and security operations in addition to technical pentesting | Strong focus on enterprise risk and governance frameworks | Audit-style findings with strategic recommendations |
Why PTES Stands Out
- Non-Partisan Coverage: PTES is not specific like OWASP or NIST in that it covers all aspects of a penetration test lifecycle.
- Compliance Ready: PTES reports can be designed in a way that makes them audit-ready, a requirement of ISO 27001, PCI DSS, GDPR.
- Business Value: PTES provides a linkage between vulnerabilities and business impact and may therefore be more of value to business executives in comparison with purely technical applications such as OSSTMM.
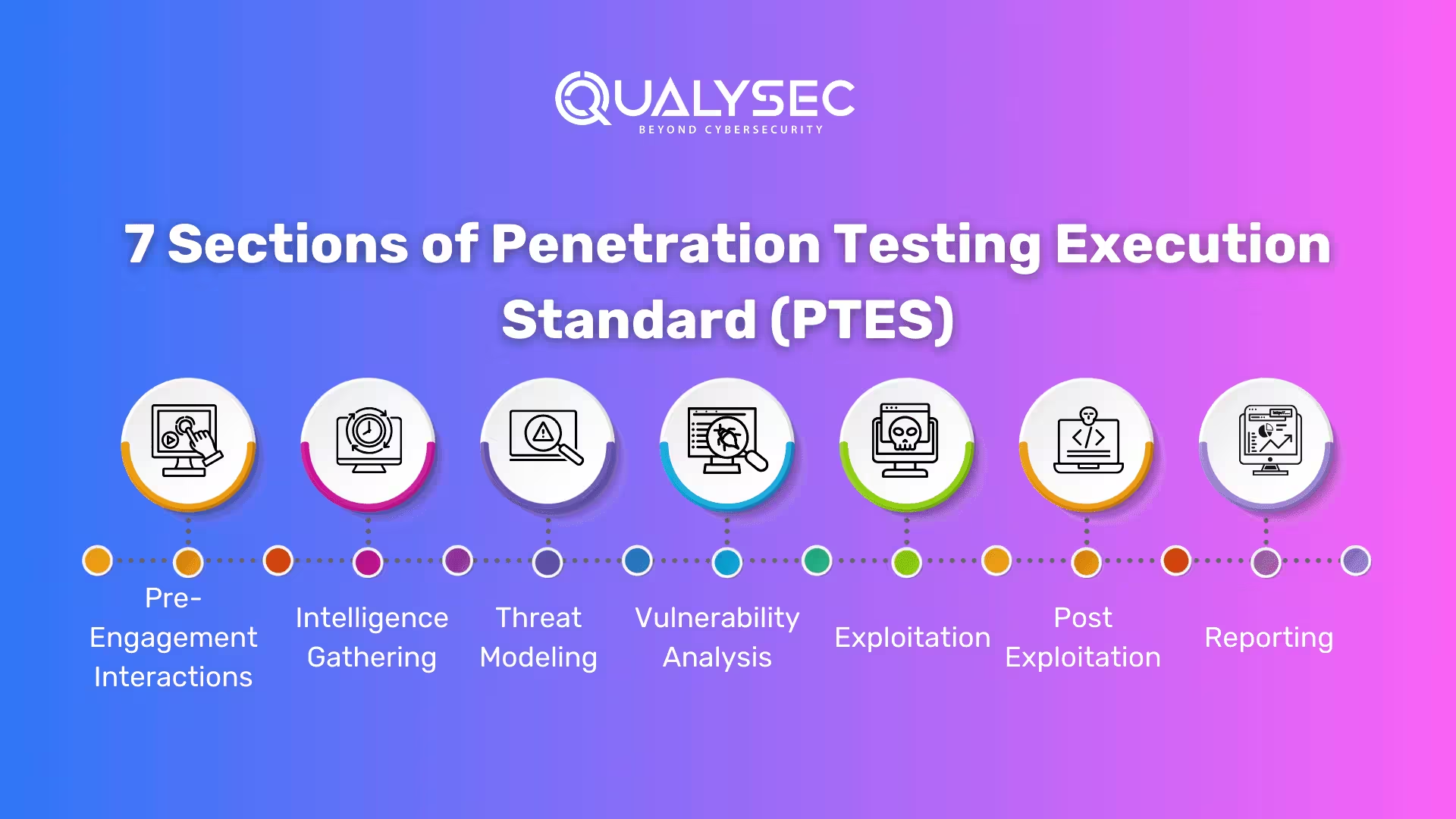
7 Sections of Penetration Testing Execution Standard (PTES)
PTES has seven major parts that elaborate on all the facets of the penetration testing process. PTES aims to provide a technical baseline to give organizations a clear understanding of what to expect from a penetration test and take them through the process. The standard does not encompass all the aspects or conditions which may happen on a pen test. Rather, it details only a few regulations describing the essential standard of any pen test.
1. Pre-Engagement Interactions
The first section of the Penetration testing execution standard (PTES) deals with the processes involved before starting the pen test. It includes the interactions between the client or organization and the pen testing team, starting from the final negotiation till the pen testing begins.
The guidelines PTES has set for this section are:
Goals of the Pen Test:
Both the testing team and the client establish specific goals for the pen test. The PTES suggests them to prioritize the following:
- The primary goal of the pen test should be security
- The secondary goal should be compliance and legal accountability
Scope of the Analysis:
After setting clear goals, the pen testing team and the client must agree on the scope and scale of the testing. Here are the elements that need to be considered:
- Identifying the areas to be analyzed
- Deciding on the quality and quantity of the test procedures
- Duration and time of the test
Rules of Engagement:
The testing team and the client should also establish clear expectations and limitations regarding what behaviors are not allowed. This includes:
- Defining particular resources that are “off limits.”
- Setting boundaries for social engineering scams
Once these pre-engagement meetings are done and goals are set, then the pen testers can start the first stage of the penetration test, i.e. reconnaissance.
2. Intelligence Gathering
During this phase, the pen testers gather information through publicly available sources and perform basic searches following the rules of engagement. This process, also known as open-source intelligence (OSINT), collects all the information that could be useful for the later stages of the testing process.
The intelligence-gathering stage includes three levels of reconnaissance:
- Level 1: This is a minimum level of interest in the compliance requirement and could be automatically performed. It contains only the mandatory data on the minimal security requirements of a company.
- Level 2: This level investigates how the organization complies with best practices and priorities other than compliance.
- Level 3: This is an expert level where the pen testers probe deep into the depths of the organization’s business relationships and the complexities to reach more hidden information.
After gathering the necessary information, the pen testing team will then begin planning potential targets for attack.
3. Threat Modeling
After gathering intelligence and understanding the target’s security measures, the next section in the penetration testing execution standard (PTES) is threat modeling. This involves identifying which assets are most likely to be targeted by ethical hackers and what resources might be used to attack them. The pen testers use all the information that has been gathered to plan the attack.
The PTES has outlined a distinct 4-step process for threat modeling:
- Gathering Documentation: The gathering of appropriate documentation and information on the target of its assets and resources.
- Categorizing Assets: Identifying the primary and secondary assets most important or in danger.
- Categorizing Threats: Figuring out the primary and secondary threats which are harmful to the assets.
- Mapping Threat Communities: Associating threats with those assets they attack and who or which organisations may conduct attacks.
- Having defined what can be used, and where possible weak points may lie, this section prepares to move onto phase two, which is to analyse how to exploit the threats.
By identifying valuable assets and potential vulnerabilities, this section lays the foundation for the next phase, which involves analyzing how to exploit these threats.
4. Vulnerability Analysis
In the vulnerability analysis section, the pentester gathers more information related to specific flaws or weaknesses in the client’s cybersecurity systems. This section uses the information gathered earlier to identify and prioritize specific vulnerabilities.
There are two main modes of vulnerability analysis:
- Passive: This involves automated or minimal activity by the ethical hacker, such as Metadata analysis or traffic monitoring analysis.
- Active: This requires more extensive in-depth activity by the attacker. For example, scanning port-based networks, application flaw scanning, and attempting directory listing or “brute force”.
By using these methods, the attacker creates a targeted list of vulnerabilities to focus on during the attack. At this point, ethical hackers often use tools like Vulnerability Scanner Software featured in Spotsaas to automate checks for outdated software, open ports, misconfigurations, and known exploits.
This marks the end of the planning stages, and the ethical hacker is now ready to begin the attack itself.
5. Exploitation
All the preparation done in the previous sections leads to the exploitation phase, which is considered the most important step of penetration testing. This is because it is where the actual attack takes place. The attacker or pen tester will use all the information available to carry out targeted attacks. These attacks may vary depending on the goals outlined in the pre-engagement interactions.
However, there are some general principles set by the penetration testing execution standard (PTES) to guide the attacker:
- Stealth: They aim to avoid detection by security systems.
- Speed: They move quickly to infiltrate the client’s systems.
- Depth: They delve deeply into the systems to find vulnerabilities.
- Breadth: They explore as many paths of attack as possible.
The goal of the attacker is to remain undetected for as long as possible, possibly throughout the entire offensive practice. By following these principles, the pen tester will find maximum weaknesses and get maximum insights into the client’s security system.
6. Post Exploitation
In the post-exploitation phase, the hacker shifts to a different type of attack after penetrating and exploring the full control of any seized systems. This step is vital in some pen tests, especially those focused on internal analysis.
During this phase, the hacker’s goals depend on the agreed scope with the client. However, the main objectives typically involve:
- Identifying the value and functions of compromised resources.
- Creating additional vulnerabilities for potential future exploitation.
- Maintaining ongoing control over the compromised resources.
- Exiting without being detected.
Both parties need to have clear expectations for this stage. If the exploitation reveals deeper weaknesses that the client didn’t see previously, it can lead to changes in scope and potential conflicts.
However, if the initial discussions were thorough, this stage sets the stage for the final step: reporting.
7. Reporting
The final section, reporting, is a straightforward process if the earlier stages have been completed properly.
The client documents all the steps taken during planning and attacking, and this information is compiled into a report. The report includes:
- Assessment of security posture and ranking of risks.
- Breakdown of the risks discovered.
- Detailed plan for fixing any issues.
Once the report is complete, the pen test concludes. This is where the PTES guidelines come to an end.
The penetration testing execution standard (PTES) outlines seven phases: pre-engagement, intelligence gathering, threat modeling, vulnerability analysis, exploitation, post-exploitation, and reporting.
| PTES Phase | Purpose |
|---|---|
| Pre-Engagement Interactions | Defines objectives, scope, and rules of engagement between client and pentest team. |
| Intelligence Gathering | Collects public and internal data through OSINT and reconnaissance to map the attack surface. |
| Threat Modeling | Prioritizes critical assets and maps potential threat actors, techniques, and scenarios. |
| Vulnerability Analysis | Identifies weaknesses using both passive scanning and active probing. |
| Exploitation | Attempts real-world attacks to demonstrate how vulnerabilities can be leveraged. |
| Post-Exploitation | Assesses the value of compromised systems, persistence options, and potential business impact. |
| Reporting | Delivers structured findings with risk rankings, compliance mapping, and actionable remediation. |
Want to see what a sample penetration testing report looks like? Download now!
Get a Free Sample Pentest Report
The significance of PTES is that the process of pen testing is intricate, troublesome and delicate. Having qualified professionals is therefore imperative to a smooth pen testing process in your business.
How QualySec Applies PTES Differently
Our penetration testers are highly experienced and the thoroughness of their work is far ahead of what is prescribed by PTES methodology. Where we really stand above other penetration testing companies, however, is in how we align the results of the penetration tests to business. Unlike just providing a standard checklist of how pentest execution should be performed, QualySec deploys Penetration testing execution standard (PTES), with a manual-first assessment and a compliance-based approach to reporting and revalidation, which makes it one of the best VAPT firms in the USA, India and across the globe.
Manual-First Approach
QualySec does not limit its testing capabilities to automated scanners used by a large number of other vendors; instead, the company focuses on manual penetration exercises performed by certified professionals. Automated tests are utilized to achieve efficiency, yet manual tests are incorporated to capture complex logic bugs, multi-stage exploits and things like business logic vulnerabilities that the automated tools may not detect. This reduces false positives and the quality of the VAPT tests report is more dependable.
Compliance Alignment
QualySec customizes all VAPT audit reports to various compliance requirements including ISO 27001, PCI DSS, HIPAA, SOC 2 and GDPR. This renders the reports suitable in both internal remediation terms, and in the context of an audit of the regulatory arm or an RFP process as well. This alignment also speeds up the certification processes in enterprises and SaaS businesses and decreases audit friction.
Remediation and Revalidation
A frequently expressed objection with VAPT vendors is the tendency to drop the report and go. QualySec goes even further and collaborates with development and IT teams to fix the vulnerabilities and then tests the solution again to make sure of the fixes. This means that vulnerabilities cannot only be discovered but they are actually eliminated, and there is a circular relationship between discovery and defensive measures.
Business-Focused Outcomes
QualySec formats reports in such a way the technical results link back to business impact. Rather than a lengthy document of areas they need to consider, clients are presented with prioritized insights, to demonstrate what vulnerabilities present the biggest danger to operations, revenue or compliance. This aids executives in their priority directives when they put resources at key, strategic places and the technicians to work on the most important problems first.
If you want more than just a pentest report, partner with QualySec, a leading VAPT company in USA and India. Our PTES-aligned methodology ensures your systems are secure, compliant, and business-ready. Schedule a free consultation with our security experts.
See our pricing, then talk with an expert to choose the best solution for your organization.

Conclusion
The Penetration Testing Execution Standard (PTES) gives a very crucial guide on how to conduct an effective penetration test. As risks due to cyberattacks are on the rise, it is necessary that businesses examine their security arrangements on a regular basis. PTES offers a structured approach to identifying and prioritizing vulnerabilities so that you get thorough security testing and comprehensive analysis.
In Qualysec Technologies we adhere to PTES Guidelines of penetration testing execution so that to offer the best in the world penetration testing services. A bespoke testing plan is designed by our cybersecurity experts depending on your expected security needs
You can choose anything from the following list of services we provide:
- Web application pentesting
- Mobile app pentesting
- Cloud pentesting
- Network pentesting
- IoT device pentesting
- API pentesting
- Source code review
Chat with our intelligent AI Assistant and get tailored insights in seconds.

FAQs
Q: How does PTES methodology differ from other penetration testing standards?
A: Unlike other penetration testing processes, techniques and standards, PTES covers all the testing phases: pre-engagement, scoping, testing and reporting. It is technical yet at the same time it is understandable at the executive level as well.
Q: Why is PTES penetration testing important for compliance?
A: PTES reports can be organized in a way that maps to ISO 27001, PCI DSS and HIPAA, and GDPR. This not only renders the ptes penetration testing methodology a security requirement, but also as a compliance tool that is audit ready.
Q: How many phases are included in the PTES pentest execution standard?
A: The pentest execution standard involves seven steps which include pre-engagement, intelligence, threat modeling, vulnerability analysis, the use of an exploit, post-exploitation and reporting.
Q: Who should use the penetration test execution standard?
A: The penetration testing execution standard PTES is ideal for organizations that want reliable results. It serves both technical teams fixing vulnerabilities and executives managing risk.























































































































































































































































































































































































































































































































































































































0 Comments