Key Takeaways
- CTEM security operates 24/7 to identify exposures as they happen, rather than on a regular quarterly basis.
- The CTEM framework cybersecurity model encompasses five recurring phases, which relate findings to business risk.
- Exposure management security covers more than CVEs. It includes misconfigurations, identity risks, and leaked credentials.
- Continuous security monitoring paired with validation proves whether your controls actually stop real threats.
- Cyber risk management strategies built on CTEM help prioritise what matters most to your business.
- A proactive cybersecurity approach using CTEM can reduce breach likelihood by up to two-thirds, according to Gartner.
Introduction
CTEM security assists in minimising cyber risk in real-time, through the continuous process of identifying and ranking security exposures, validating and correcting them to ensure that these exposures are not exploited. CTEM security is a continuous cycle, whereas periodic scans have serious gaps. This proactive cybersecurity approach relates technical discoveries to real business impact and is now vital to organisations around the globe.
The numbers tell a clear story. Verizon 2025 DBIR reviewed 22,052 cases and 12,195 verified breaches in 139 countries. Exploitation of vulnerabilities increased by 34 and is currently 20% of all breaches (Verizon DBIR 2025). By 2025, CISA has added 245 new vulnerabilities to its Known Exploited Vulnerabilities (KEV) catalogue, a 30% increase over the previous year (CISA KEV Catalogue). It had a median time to patch edge device flaws of 32 days and an average of five days time-to-exploitation (Cybermindr).
Gartner estimates that in 2026, organisations with a continuous threat exposure management program will be three times less likely to experience a breach. It is this prediction that has seen CTEM security rise to be a leading priority among security leaders around the world.
What Is CTEM in Cybersecurity and How Does It Work?
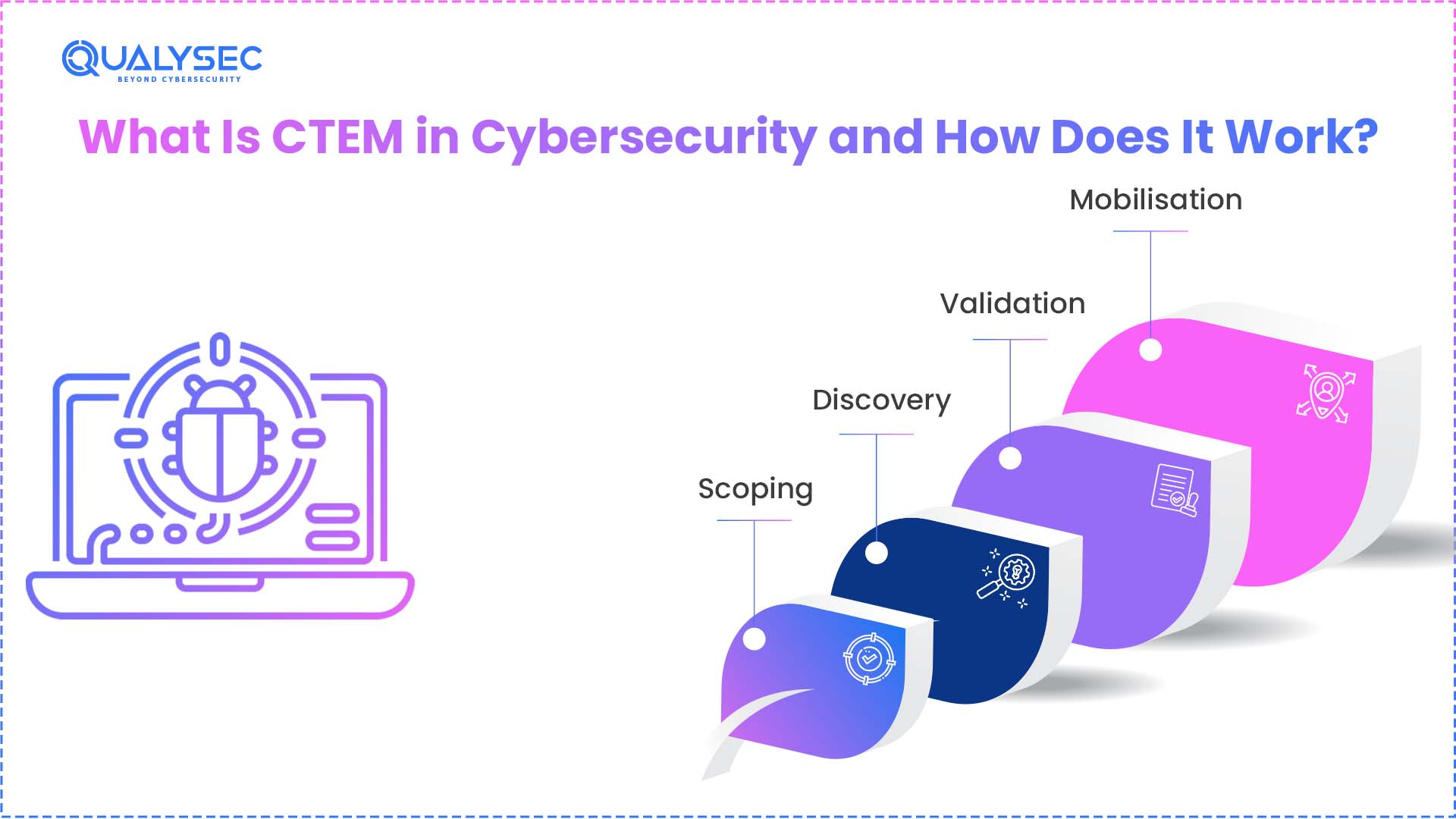
CTEM security is an abbreviation of Continuous Threat Exposure Management. This framework was introduced by Gartner in 2022. The CTEM framework cybersecurity model is based on five stages that are implemented in a cyclic manner (CTEM.org).
Stage 1: Scoping — Identify business-critical assets and processes to protect. This covers workloads in the cloud, SaaS, APIs, and identity.
Stage 2: Discovery — Identify all exposures within the given scope. This includes weaknesses, misconfigurations, credentials leaks, and shadow IT resources.
Stage 3: Prioritisation — Prioritise findings based on business impact and exploitability. Making a mistake in a customer-facing payment system is a lot more important than in an internal test environment.
Stage 4: Validation — Check the possibility of exploiting identified exposures. This involves breach simulations, penetration testing, and red team exercises.
Stage 5: Mobilisation — Organise security, IT, and development team remediation. Monitor improvements and ensure that fixes are effective. There should be clear ownership and schedules.
Once mobilised, the process begins again. This ongoing circle is the source of power in CTEM security over one-time tests. The exposure management security of the entire environment is reinforced with each round. According to Gartner surveys, 71% of organisations have the potential to gain with this approach, although only 16% have implemented it fully by 2026.
Why Does Real-Time Exposure Management Security Matter in 2026?
The threat world is evolving at a faster rate than periodic analysis can cope with. This is why it is important that security is monitored continuously by CTEM security.
- Exploit speed is increasing. In 2024 alone, NIST documented more than 40,000 CVEs, and this trend is expected to continue in 2025 with approximately 131 CVEs being reported daily (NIST NVD). Approximately 28.3% of the exploited vulnerabilities were weaponised within 24 hours of announcement.
- Breach costs keep climbing. In 2025, the average cost of a breach in the world was USD 4.44 million (IBM Cost of a Data Breach Report). This financial exposure is minimised through proactive cyber risk management strategies based on CTEM.
- Compliance demands are tightening. Continuous validation is now anticipated by PCI DSS 4.0, HIPAA, the NIS2 directive of the EU, and even ISO 27001. CTEM security fulfils these requirements directly.
- Patching alone cannot keep up. The Verizon DBIR established that not all edge device vulnerabilities were completely resolved throughout the whole year (54%). The average patch time was 32 days, although exploitation usually occurs in five days.
- Continuous threat exposure management. addresses all of these challenges. It makes sure that security teams work on the actual, exploitable risks and not all the alerts. CISA also encourages all organisations to prioritise vulnerabilities of KEV catalogs as a timely remediation as part of its exposure management security practice.
Get Your Free ISO Readiness Score + Expert Consultation – Talk to Qualysec Experts.
| Challenge | Reactive Approach | CTEM Security Approach |
| Vulnerability speed | Quarterly scans miss fast-moving exploits | Continuous security monitoring catches exposures in real time |
| Prioritization | CVSS score only | Business impact and exploitability-based |
| Validation | Assumed protection | Proven through simulation and testing |
| Remediation | Siloed patching | Coordinated mobilization across teams |
| Business alignment | Minimal | Central to the CTEM framework cybersecurity model |
How Does CTEM Security Differ From SIEM?
Both CTEM security and SIEM address threats, but they have very dissimilar purposes.
CTEM is proactive. It aims at identifying and rectifying exposures before they are exploited. Continuous exposure management is proactive and poses the question, where do we lack at the moment?
SIEM is reactive. It gathers logs, event correlations, and generates alerts following an occurrence. SIEM poses the question: What has just happened within our surroundings?
Consider it in the following manner. Security is achieved in CTEM. SIEM detects the smoke. The two are useful, yet they operate at diverse stages of the security lifecycle.
Organisations that integrate CTEM security and SIEM enjoy layered security. There are fewer incidents because of the proactive cybersecurity approach of the CTEM solution. Anything that leaks through, SIEM picks up. Collectively, they establish a robust cyber risk management strategy (Microsoft Security Blog).
In the case of cloud-native, this combination is even more significant. CTEM security is able to authenticate cloud misconfigurations and identity threats that would never have been detected by SIEM. The teams have full visibility as a result of continuous security monitoring on both levels.
What Are the Best Cyber Risk Management Strategies Using CTEM?

To develop a successful CTEM security program, it takes more than the purchase of tools. The following are the major cybersecurity risk management strategies that ensure CTEM works in practice.
1. Start With Business Context
Make your CTEM framework cybersecurity program scope around what is most important. Define revenue-related systems, customer data repositories and compliance-related assets. This makes exposure management security efforts focused, rather than diffused.
2. Combine Automated and Human-Led Testing
Discovery should be done using automatic scanners to cover a wide area. Then apply human-led AI penetration testing and red team exercises during validation. Continuous security monitoring tools catch known issues. Expert testers detect business logic defects and chained exploits that automated tools do not detect.
3. Validate Before You Remediate
Most organisations are hasty to patch without verifying exploitability. The CTEM security validation phase eliminates wastage of effort. Model real-life to verify what exposures are really dangerous. This preventive cybersecurity solution is time and resource-saving.
4. Coordinate Across Teams
Managing continuous exposure to threats cannot be effective when the findings remain confined to the security team. Active mobilisation needs to have well-defined workflows among security, IT operations, cloud teams, and developers. Assign ownership. Set timelines. Track resolution.
5. Measure and Improve Continuously
Monitor such metrics as the mean time to remediate, rate of exposure reduction and approved risk scores. CTEM security is an ongoing cycle and not a one-off project. At every round, a visible improvement in your exposure management security posture should be observed.
Contact Qualysec today to align your CTEM program with real business impact.
Talk with Qualysec experts today

Is CTEM Suitable for Small Businesses?
Yes. CTEM security applies to both small and large organisations. Smaller companies are usually at a higher risk because they don’t have a dedicated security team. Verizon DBIR discovered that SMBs are almost four times more likely to be targeted compared to large organisations (Verizon DBIR 2025).
The CTEM framework cybersecurity model can be scaled down effectively. A small business does not have to track hundreds of thousands of assets. Nonetheless, one must understand the nature of the exposed systems and the methods to rectify them.
Here is how small businesses can start:
- Focus the scope on customer-facing applications, payment systems, and cloud services.
- Use managed security services that include continuous security monitoring and validation.
- Prioritise based on business impact. A breach of customer financial data matters more than an internal wiki flaw.
- Work with a testing partner that offers exposure management security aligned with compliance needs.
This is the reason why small businesses are usually the target since they do not have good defences. This has seen many ransomware organisations targeting mid-market organisations with high-value data but low-security teams. A proactive cybersecurity strategy with CTEM can enable these organisations to punch above their weight.
Cyber risk management strategies do not have to be complicated to be effective. An intensive CTEM security program, even on a small scale, limits risk tremendously. According to data provided by Gartner, organisations that have a well-organised program of continuous threat exposure have as many as two-thirds fewer breaches.
Schedule a Free Consultation – Contact Qualysec Now
Why Is Qualysec the Best Partner for CTEM Security Implementation?
Qualysec assists organisations to develop and operate successful CTEM security initiatives. The company unites human-led AI penetration testing, structured processes, and compliance-ready reporting to present real results.
What makes Qualysec stand out:
- Human-led AI penetration testing. Qualysec is a combination of human testers and AI-based reconnaissance and scanning tools. Competent testers are in charge of every engagement, and AI enhances the discovery and analysis process.
This method justifies exposures with the real-world precision that pure automation cannot achieve. It helps directly to validate the stage of continuous threat exposure management.
- Full-scope discovery. The team includes web applications, APIs, cloud infrastructure, mobile applications, and network infrastructure. This addresses the discovery stage of the CTEM framework cybersecurity model completely.
- Business-risk prioritisation. Actual business impact is used to rank findings, not severity scores. This identifies with the prioritising phase and assists teams with what is important first.
- Compliance-mapped reporting. Reports comply with ISO 27001, PCI DSS, HIPAA, SOC 2 and GDPR. This helps in audit preparedness and security of exposure management.
- Remediation and retesting. Qualysec collaborates with development teams in order to seal findings. The team retests after fixes to ensure the issue is resolved. This is the final stage in the CTEM security cycle of mobilisation.
- Global coverage. Qualysec caters to clients in finance, healthcare, SaaS, retail and enterprise industries worldwide.
Whether it is your first CTEM security program or the enhancement of an existing one, Qualysec can offer the knowledge and framework to provide quantifiable risk mitigation. Their vigilant approach to cybersecurity ensures that round-the-clock security checks translate into physical protection.
Get Your Free ISO Readiness Score + Expert Consultation – Make a free consultation with Qualysec now.
Conclusion
CTEM security provides organisations with an organised, ongoing means to mitigate cyber risk on an ongoing basis. It shifts security to regular scans and patching to a continuous process of finding, validating, and coordinating fixing. The CTEM framework cybersecurity model relates all findings to the business impact.
Reactive approaches are not sufficient as the threats become more sophisticated and rapid. An active cybersecurity strategy based on the ongoing management of threats is now requisite. Constant security checks and verification will ensure that what you have in place as security measures is actually functioning.
Today, start developing your cyber risk management strategies based on CTEM. Prioritise what matters. Confirm the real. Propagate what endangers your business. Those organisations that are taking action today will be in the best position to deal with the threats in the future.
Get Your Free ISO Readiness Score + Expert Consultation – Schedule a Free Consultation with Qualysec.
Speak directly with Qualysec’s certified professionals to identify vulnerabilities before attackers do.
FAQs
1. What is CTEM in cybersecurity?
CTEM security is an abbreviation of Continuous Threat Exposure Management. It is a five-step framework by Gartner that assists companies to detect, rank, confirm and rectify exposures on an ongoing basis.
2. What is the difference between CTEM and SIEM?
CTEM security proactively identifies and fixes exposures before attackers exploit them.SIEM is an active tool which identifies and probes security occurrences once they occur.
3. How does CTEM improve security posture?
Continuous threat exposure management enhances security because it performs validation tests to verify actual risk. This exposure management security process makes sure that teams are fixing what matters rather than false positives.
4. Is CTEM suitable for small businesses?
Yes, businesses of any size can adapt the CTEM framework and cybersecurity model. Even small teams can enjoy continuous security monitoring and prioritisation based on business suitability.
5. What frameworks support CTEM?
CTEM security is in line with ISO 27001, PCI DSS, HIPAA, NIST CSF, and the MITRE ATT&CK framework. Organisations can effectively implement these cyber risk management strategies with a combined continuous threat exposure management program.





















































































































































































































































































































































































































































































































































































































































































































0 Comments