Third Party Risk Management is critical as the United States is very dependent on vendors, SaaS, cloud providers, payment processors, AI solutions, and outsourced services. This reliance provides a broader attack target where one vulnerable vendor can introduce an organization to operational disruption, data breaches or risk compliance fines.
Supply chain attacks have grown at a steady pace during the last few years, and now threat actors target smaller vendors as a convenient way to enter larger companies. Third party cyber risk management is now an essential part of operational stability with an increasing number of applications, integrations, and artificial intelligence (AI) based workflows.
Organizations cannot use internal controls only in 2026. They have to assess, oversee, and govern the security of all external partners who access data, connect to internal systems or full business operations. An effective third party risk management framework limits exposure, enhances readiness to comply, and cushions the firm against failures on the side of its vendors.
What is Third Party Risk Management in Cybersecurity?
TPRM, also known as third party risk management, is the procedure of identifying, evaluating, and tracking security risks that come about from external vendors, service providers and partners. In contemporary settings, vendors inevitably maintain data, access inner systems or become directly connected to the cloud application, and therefore, they are included in the extended attack surface of the organization.
The third party cyber risk management also aims at making sure that all external partners fulfill the standard of security and compliance prior to and after they start collaborating with the business. This consists of assessing vendor data handling, data infrastructure maintenance, network security, and incident response of the vendor. It is a straightforward objective that involves minimizing the vulnerability of the organization by making sure that vendors are not a source of cyberattacks or data breaches.
Must read: Third Party Security Audit: A Comprehensive Overview
Types of Third Party Risks Businesses Face in 2026
There are several classes of risk in modern vendor ecosystems which are not merely related to cybersecurity. The USA organizations should consider all types to realize how a third party is likely to affect the operations, data integrity, and compliance.
- Cybersecurity Risks: Vendors can possess ineffective authentication, unpatched systems, or cloud assets, and insecure API. These loopholes can give hackers indirect access to your network or confidential information.
- Risks of Data Privacy and Compliance: Third parties frequently process customer, financial, or healthcare data. In the event their practices are a breach of rules, including HIPAA, PCI DSS, or the privacy laws of a state, your organization is potentially liable and subject to punishment.
- Operational Risks: A vendor laboratory’s outage, service interruption, or hacked system can disrupt your business operations. Even brief downtimes can have an impact on revenue and customer confidence in critical industries.
- Cloud and SaaS Risks: Poor configuration of cloud storage, lax integrations, and poor identity controls on vendor systems pose a great exposure, with more businesses depending on SaaS applications.
- Reputational Risks: Even when you do not have your internal systems compromised, a breach at a third party will hurt your brand. The customers tend to fault the main business rather than the vendor.
- New AI and Model Integration Risks (New for 2026): Vendors based on AI or LLMs can accidentally disclose data, misuse training sets or use third party AI APIs that are insecure. This puts in place new avenues to leakage and unauthorized access.
Suggested read: How to Conduct a Cybersecurity Risk Assessment.
The 2026 TPRM Framework (USA-Focused)
The current third party risk management program should encompass the entire lifecycle of mechanism involvement, including the initial onboarding and monitoring of the process, as well as eventual offboarding. The framework shown below, from 2026, indicates how organisations in the USA analyse and select vendors in a dynamic threat environment.
1. Identify All Third Parties:
Concentrate on an inventory of all vendors, SaaS tools, suppliers, contractors and software integrations that connect to your systems or data. This involves fourth parties that subcontract.
2. One of the procedures is to classify Vendors by Risk Level:
Group the vendors into risk categories (low, medium, high, critical) depending on the data they are able to access, access to the system, and the result of the attack on the business.
3. Conduct Due Diligence:
Gather records and reports that reveal how the vendor safeguarded the data, controlled access, secured infrastructure and met the compliance criteria. This is what provides a foundation for decisions.
4. Justify Controls and Security Practices:
Audit cybersecurity policies, cloud configurations, encryption criteria, identity administration, incident reaction practices, and technology clusters. Technical verification on higher-risk vendors might be necessary.
5. Determine Contractual Requirements:
Ensure the contract clearly defines data handling rules, breach notification timelines, access controls, audit rights, and security responsibilities. Unambiguous provisions help prevent disputes.
6. Introduce Constant Surveillance:
Monitor changes in vendors, new vulnerabilities, breach reports and threat intelligence. Continuous monitoring allows you to detect increased risks early, before the annual review.
7. Incorporate Vendors into the Incident Response Processes:
Vendors must understand their role during an incident, know whom to report to, and gather the necessary evidence. This prevents delays in addressing actual threats.
8. Carry out Periodic Re-Assessment:
Review the vendors using new risks, technology, performance concerns, or compliance. The frequency is based on the level of risk and criticality of the business.
9. Offboard Securely:
Stop access, read data, authenticate certifications of destruction, as well as, be certain that connections between systems are eliminated. Inadequate offboarding creates security gaps in the long term.
Book a Free TPRM Consultation.
How to Assess Third Party Security Risks (Step-by-Step)
When evaluating third party security risks, it is necessary to provide a formal audit of the way a vendor handles data and the way systems and threats are addressed. The following steps can assist organizations in risk evaluation in order to give access or integrate systems.
- Collect Security Paperwork: Demand underlying material like security policies, compliance certificates, audit reports and information about infrastructure and data management. This is the basis of vendor assessment.
- Assess Risk According to Access and Impact: Identify what data the vendor will work with, the connection between systems, and the impact such a failure or breach can have. An increased level of access implies increased inherent risk.
- Carry out Technical and Policy Review: Examine identity management, encryption, cloud, network controls, and vulnerability management. This assists in confirming that controls are operational and are not merely written.
- Confirm Thoroughness of Evidence of Security Controls: Seek evidence like penetration testing reports, SOC 2 reports, incident logs or secure SDLC practices. Evidence-based testing minimizes the use of questionnaires.
- Score the Vendor’s Risk Level: Give ratings according to cybersecurity maturity, degree of exposure, sensitivity of the data and impact of the operation. The interval of monitoring and contractual needs is decided through this scoring.
- Approve, Mitigate, or Reject: Based on the evaluation, either approve, approve with controls or deny the vendor. Before integrating, the high-risk vendors might need to be remediated.
Trending read: Vendor Risk Assessment: A Complete Guide.
Third Party Cyber Risk Assessment Checklist (2026)
An organized checklist is a tool that enables organizations to determine the security stance of a particular vendor to meet the appropriate standards. The items below can be used to estimate cyber, operational, and compliance preparedness prior to contracting any third party.
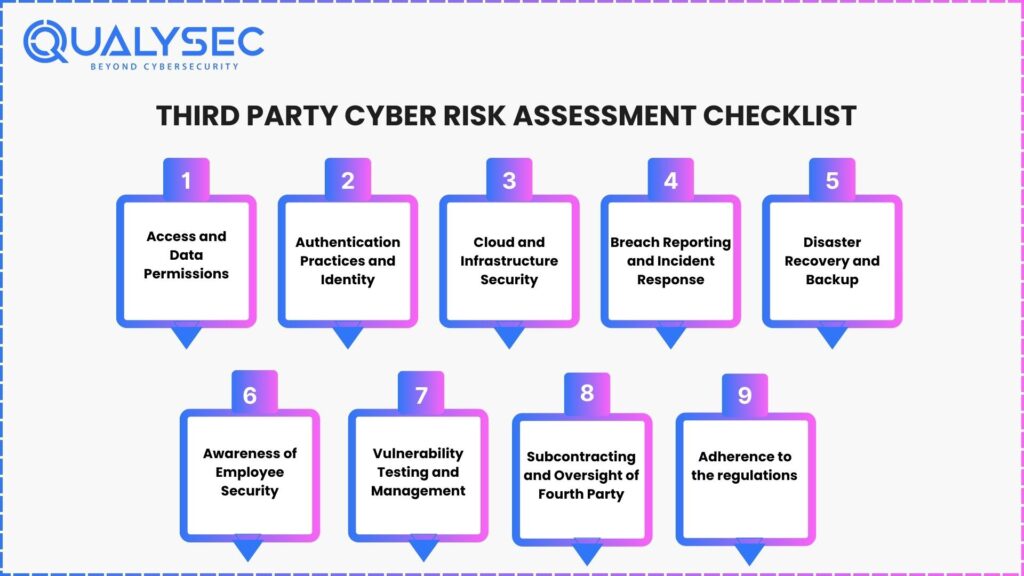
1. Access and Data Permissions:
Ensure the vendor receives only the data necessary to perform the services and that access controls match the sensitivity of the information.
2. Authentication Practices and Identity:
Ensure the presence of solid passwords, multifactor authentication, privileged access control and monitor sessions to minimize risks of unauthorized access.
3. Cloud and Infrastructure Security:
Assess cloud configurations, network segmentation, encryption, patching timeline, and logging. Lack of properly configured cloud assets is a primary third party risk.
4. Breach Reporting and Incident Response:
Ensure the response plan documents the vendor’s role in an incident, including breach notification timelines and collaboration with your internal team during investigations.
5. Disaster Recovery and Backup:
Check to ensure that the vendor has good backups, secure storage and continuity planning. This will ensure that your business does not go out of business in case the vendor is offline.
6. Awareness of Employee Security:
Determine whether the vendor educates employees about phishing, data management, and permission-based access. Error by human beings is still one of the major causes of breaches.
7. Vulnerability Testing and Management:
Make the vendor conduct periodic vulnerability scans and independent penetration testing to determine vulnerabilities and remedy them in advance of attackers.
8. Subcontracting and Oversight of Fourth-Party:
Ensure that the vendor checks on the suppliers and service providers. Weaknesses of the fourth party may hit your organization invisibly.
9. Adherence to the U.S. regulations:
Seek compliance with pertinent standards, including SOC 2, HIPAA, PCI DSS, GLBA or state privacy regulations to minimize legal and regulatory risk.
Recommended: Data Security Compliance: A Step-by-Step Guide.
What Should Be Included in a Vendor Security Questionnaire?
A vendor security questionnaire assists organizations in assessing a third party to determine whether the party complies with the minimum conditions of cybersecurity, compliance, and risk management. It is to gather facts, not beliefs. The most crucial groups that any questionnaire must have are included below.
- Background and Ownership of the company Security: Find out who is in charge of security, the structure of the vendor and the fact that they have dedicated personnel on the management of third party cyber risk.
- Data Handling, Authentication, and Access: Ask a question concerning the way the vendor will control access to systems and manage privileged accounts, in addition to securing customer data by encrypting, masking, or tokenizing it.
- Application, Cloud, and Network Security: Make inquiries regarding firewall settings, cloud settings, secure coding standards, API safeguarding and patch administration policies.
- Incident Response and Breach Reporting Process: Know how fast the vendor identifies and reports an incident and how they will cooperate during the process of containment and recovery.
- Business Continuity and Disaster Recovery: Include questions about redundancy, backup testing, recovery schedules, and maintaining operations if their systems fail.
- Vulnerability Scanning and Penetration Testing: Request assistance with frequent scans, free penetration checks and the process of tracing, prioritizing and treating the results.
- Compliance and Certifications: Demand SOC 2, ISO 27001, PCI DSS, HIPAA, GDPR or U.S. state privacy documentation based on industry requirements.
- The use of Subcontractors /Fourth Parties: Explain the dependency of the vendor on other vendors and how they evaluate and manage risk throughout their long supply chain.
Download a Sample Penetration Testing Report!
Download a Sample Pen Testing Report

How Often Should Third Party Risk Assessments Be Performed?
The rate at which one undertakes third party risk assessment will be based on the level of access the vendor has to the data, the sensitivity of the data and how important the data is to the business operations. The industry does not have a single fixed timeline since it has risk-tiered cycles that keep the industry on an ongoing view.
High-Risk Vendors (Critical Access or Sensitive Data)
Assess annually at a minimum. Such providers frequently deal with customer information, the financial system, medical records, or internal infrastructure. Annual monitoring devices will be advisable in the form of round-the-year surveillance.
Intermediate-Risk Vendors (Business Reliance, Non-Sensitive Data)
Assess every 18 to 24 months. These vendors are also assisting significant functions, yet with no direct access to regulated or highly sensitive information.
Low-Risk Vendors (There is no Access to the System or Public Data Only)
Have the assessment done every 2-3 years with lightweight reviews or updating of the questionnaires in between.
Trigger-Based Assessments
Conduct reassessment regardless of tier in case there is:
- A breach by the vendor or his subcontractors.
- A significant change in product/infrastructure.
- New integration with your systems.
- The widening of the access of vendors to sensitive information.
Risk is dynamic, and therefore, the assessment of vendors has to keep up with the behavior of the vendor and the threat environment of the organization. The risk-based schedule, being structured, is proactive instead of reacting to the management of third-party risks.
Why Companies Choose Qualysec for Third Party Risk Management in 2026
The United States has become reliant on a long chain of suppliers, SaaS services, cloud solutions, payment systems, and artificial intelligence-based applications. With this interrelated terrain comes greater exposure, which mandates a third-party verification on a deeper level. Qualysec assists companies to enhance their vendor system with a technical, evidence-based strategy of third party risk management.
TPRM services of Qualysec are not limited to questionnaires. Their team makes independent validation of the security posture of the vendor by hands-on testing, configuration review and analyzing cloud, network, and application level risks. This would make sure that companies do not based on just claims made by vendors that are self-reported, but rather obtain actual knowledge of actual vulnerabilities.
Key Strengths of Qualysec in TPRM
1. Technical Validation Rather Than Documentation Alone
Qualysec conducts real evaluations of vendor resources, such as:
- Identity controls, cloud configurations.
- Application behavior and API.
- Network exposure and misconfigurations.
- Weak, insecure integrations or data processing.
This eradicates blind spots, which the conventional questionnaires do not capture.
2. Process-Based and Consistent Framework
Qualysec has a set testing procedure that incorporates both automated scan and manual research. This yields standardized outcomes and assists regulated U.S. firms in having audit-ready documentation of HIPAA, PCI DSS, SOC 2, GLBA, and state privacy regulations.
3. Technology Independence and Broad Coverage
Mixed stacks are provided by vendors using legacy systems, multi-clouds, SaaS applications or AI models. Qualysec adjusts and has a comprehensive assessment of the ecosystem of the vendor.
4. Transparent Reporting and Supportive Collaboration
Their reports will describe the risk scores, exploit information, explanation of business impact, and provide clear remediation actions that are easily understandable by both technical and nontechnical staff.
They also provide retesting and vendor-side support to ensure that the problems are completely solved.
5. Cost Effectiveness for SMBs and Enterprises
Firms that employ TPRM have problems related to expensive assessments. Qualysec has a structured process, which allows a thorough assessment at reasonable prices, so the security verification is open to organizations of any maturity stage.
Talk to an Expert About Vendor Security.
Speak directly with Qualysec’s certified professionals to identify vulnerabilities before attackers do.
Conclusion
One of the largest causes of cyber risk within organizations in the United States is now third-party relationships. With the increasing dependence on SaaS platforms, cloud providers, and external vendors, companies are forced to have a well-organized third party risk management program that helps to detect vulnerabilities early and to secure sensitive information throughout the entire ecosystem. An effective TPRM model introduces a high level of visibility, minimizes compliance lapses and increases the resilience to threats to the supply chain.
Organizations which take the time to invest in the management of third-party risks can have a better perspective of their external dependencies and can be sure that all vendors satisfy their security needs. When the onboarding is controlled, the monitoring is implemented, and the evaluation of risks is carried out as a risk, the organizations can take care of the vendors and ensure the safety of their operations. In case your company is interested in bettering third party cyber risk management and testing it professionally, along with the constant verification, Qualysec would help you turn into a secure and trustworthy vendor base.
Request a Vendor Risk Assessment Quote.
FAQs
Q: What is third party risk management in cybersecurity?
A: A third party risk management is the procedure of analyzing and overseeing the security risks that arise due to vendors and other partners. It makes sure the access and data sharing of third parties and integrations do not provide vulnerabilities to your environment.
Q: How do you assess third party security risks?
A: Security questionnaires, compliance review, penetration testing and continuous monitoring are tools by which organizations test the third party risks. An organized vendor risk management procedure assists in exposing the weaknesses prior to access to the internal systems.
Q: What should be included in vendor security questionnaires?
A: Vendor security questionnaires should include questions about data management, access control, incident response, encryption, cloud security practices, compliance frameworks, and prior breach history. They aim to assess how the vendor secures your data.
Q: How often should third party risk assessments be performed?
A: All vendors must be subject to third party risk assessment on an annual basis and more often with high risks. Constant surveillance reinforces TPRM programs, where new threats are manifested depending on the change in the environment of vendors.





















































































































































































































































































































































































































































































































































































































































































































0 Comments