Do you use automated compliance tools vs penetration testing to safeguard your business? Provided that, you may be exposing possible security gaps to a wide open. A lot of enterprises in the USA nowadays think that the usage of such a platform as Vanta or Drata will render them safe automatically. But compliance does not always bring about security. This is a full-fledged guide to understand how the use of automated compliance tools and real-world security testing are in tandem with each other, and more so, why you should have both in order to be able to really secure your organization against a cyber attack.
What Are Automated Compliance Tools and How Do They Differ from Real-World Security Testing?
It is important to know the basic disparities between the two methods to develop a strong security strategy. Let us deconstruct what each of them performs and how they are used to the service of various purposes.
Understanding Automated Compliance Tools
Automated compliance tools are computer-based platforms designed to assist business organisations in achieving and maintaining compliance with multiple regulatory frameworks. Therefore, the tools simplify the task of achieving standards such as SOC 2, ISO 27001, HIPAA, and PCI DSS. Instead, popular platforms like Vanta, Drata, and Secureframe are working around the clock to check on your systems to make sure you are checking the right boxes.
These tools typically perform the following functions:
- Policy Management: They assist in developing and sustaining security policies that are necessary as a requirement.
- Evidence Collection: Gather evidence automatically that controls are in place.
- Integration Monitoring: Interlink with the tools that you are using to monitor compliance.
- Audit Preparation: Create compliance audit reports and documents.
- Continuous Monitoring: Measure compliance status across your infrastructure.
- Workflow Automation: Automate CRM compliance.
However, one thing is that compliance automation limitations are clear, though, when you think about what is not done by these tools. They mostly worry about the presence of controls and not the effectiveness of the controls in relation to the reality-based threats.
What Is Real-World Security Testing?
Real-world testing of security, especially penetration testing, is very different. Rather than examining the presence of policies, penetration testing recreates real-life cyberattacks to determine weaknesses that evil hackers can take advantage of. Moreover, this offensive security method identifies vulnerabilities that can not be detected by automated scanners.
Penetration testing involves several key components:
- Black Box Testing: Testers simulate external attacks without prior system knowledge
- White Box Testing: Comprehensive testing with full access to system architecture
- Gray Box Testing: Combines external and internal perspectives
- Business Logic Testing: Identifies flaws in application workflows and processes
- Social Engineering: Tests human vulnerabilities alongside technical ones
- Exploitation Verification: Confirms that vulnerabilities are actually exploitable
The objective is very easy but important. So, it is needed to locate vulnerabilities and rectify them before cybercriminals. Reported USA cybersecurity studies indicate that a combination of compliance automation and frequent penetration testing decreases the probability of breach to more than 60 per cent for businesses.
The Critical Differences Explained
To better understand automated compliance tools vs penetration testing, let’s examine their key differences:
| Feature | Automated Compliance Tools | Real-World Security Testing |
| Primary Purpose | Verify compliance with standards | Identify exploitable vulnerabilities |
| Approach | Checklist-based verification | Offensive simulation of attacks |
| Frequency | Continuous automated monitoring | Periodic manual and automated testing |
| Scope | Policies, procedures, and controls | Technical systems and attack surfaces |
| Detection Method | Configuration checks and rule-based scanning | Active exploitation attempts |
| False Positives | Higher rate of false positives | Minimal false positives with manual testing |
| Outcome | Compliance certification | Actionable security improvements |
| Cost Structure | Subscription-based annual fees | Per-engagement or retainer-based |
This table clearly shows that while both serve important purposes, they address fundamentally different aspects of your security posture.
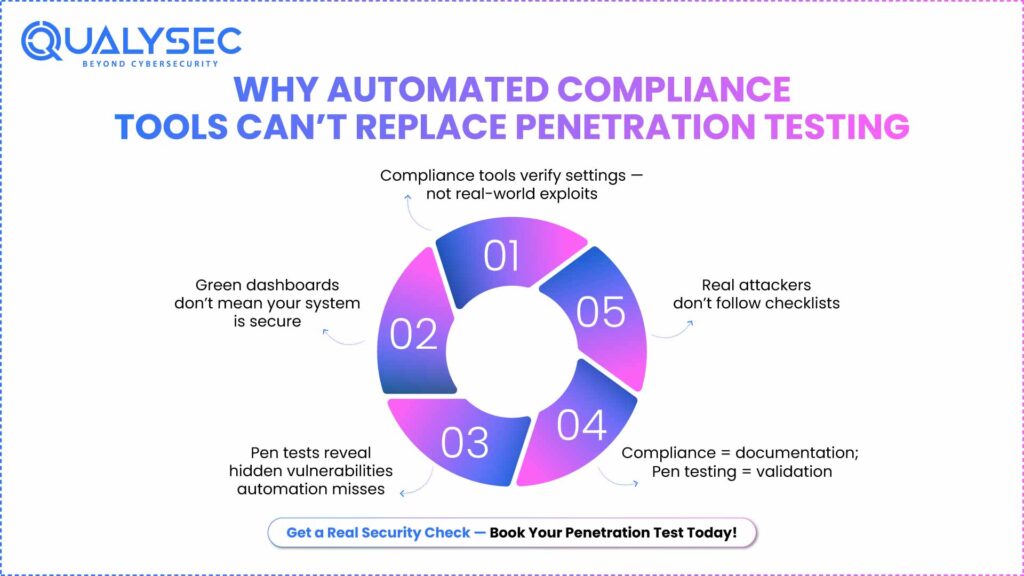
Can Automated Compliance Tools Replace the Need for Penetration Testing?
The answer to this is a resounding no, and the reason why this has been proven more than ever before to be important in USA businesses that have to deal with the ever-growing, sophisticated cyber threats.
Understanding Vanta Compliance Security Gaps
Vanta is a highly used automation of compliance in the USA. However, although Vanta spies on your systems at all times, there are major Vanta compliance security breaches. Vanta is better at documented and configured security controls. Nonetheless, it does not model an attacker with a will to crack into your systems.
For example, Vanta might verify that:
- Your firewall rules are documented
- Multi-factor authentication is enabled
- Access reviews happen quarterly
- Encryption is configured for data at rest
But it won’t tell you if:
- An attacker could bypass your firewall using a misconfigured rule
- Your MFA implementation has a bypass vulnerability
- Privilege escalation is possible due to a configuration error
- Your encryption keys are stored insecurely and could be compromised
These limitations apply to most automated compliance tools. They’re designed for compliance verification, not security validation.
The Reality of Drata vs Real-World Security Testing
Comparing Drata and real-world security testing, one can see similar patterns. Drata offers great compliance automation that assists companies with the achievement of SOC 2, ISO 27001, and others. Nonetheless, adherence does not necessarily mean safety.
Consider this real-world scenario from a USA-based SaaS company: they were able to be certified through Drata to obtain a SOC 2 Type II certification through Drata and they sailed through their audit. Thereafter, they contracted their first penetration test after six months. The results? Penetration testers found out that 12 critical vulnerabilities, such as, were there:
- SQL injection vulnerabilities in their main application
- Hardcoded credentials in source code repositories
- Inadequate session management allows account takeover
- Business logic flaws enabling unauthorized data access
All these vulnerabilities were present, and their compliance dashboard displayed green on all boards. It is an example of how compliance automation limitations can render penetration testing not just necessary but also important.
What Compliance Tools Miss
Automated compliance tools typically miss several critical security issues:
- Business Logic Vulnerabilities: These are application-based vulnerabilities. In one instance, a negative amount shopping cart or a password reset system that displays the information of the user. Such are not picked up using automated tools, which are not sensitive enough to the business context.
- Zero-Day Vulnerabilities: The zero-day vulnerabilities are those that have not yet been signified or detection rules and will not be identified by automated scanners. However, expert penetration testers may discover such unknown weaknesses by using manual techniques.
- Complex Attack Chains: This is also a typical characteristic of actual attackers to join different smaller vulnerabilities and complete their goals. Compliance tools check individual controls and do not check how they interact.
- Human Factor Exploits: Social engineering, phishing vulnerability and user behavior problems must not be automated but tested by a human being.
- Configuration Weaknesses: Tools can scan configurations to verify that they are present, but even then will not identify minor misconfigurations that will be exploited by an adept attacker.
Get Expert Compliance Security Audits – Find Out More.
How Do Continuous Compliance and Security Testing Work Together?
Compliance and security testing should not be viewed as mutually exclusive approaches to achieving security, one being good, and the other being bad, but one that completes the other as good components of an effective security policy. This is the way in which they complete each other effectively.
The Integrated Security Approach
Compliance automation should be viewed as your defensive baseline, and penetration testing as your offensive validation. The two of them form a compliance and a truly secure security posture.
Compliance automation provides:
- Consistent baseline security controls
- Continuous monitoring of configurations
- Evidence for regulatory requirements
- Quick identification of policy violations
- Scalable security management
Penetration testing adds:
- Validation that controls actually work
- Discovery of unknown vulnerabilities
- Real-world attack simulation
- Prioritized remediation guidance
- Security posture verification
Building a Hybrid Strategy
An effective hybrid strategy has several important elements:
- Monthly Compliance Monitoring: Continuous compliance should be tracked with the help of such tools as Vanta or Drata. This will keep you in your base security posture and allow configuration drift to be detected fast.
- Quarterly Vulnerability Assessments: Automatically scan for vulnerabilities to detect the known security risks in your infrastructure. Moreover, this assists you in being at the forefront of patch management.
- Annual Penetration Testing: Manual penetration testing should be done comprehensively at least once per year. This is literally required by many compliance frameworks. You can also consider testing after major changes in the system have occurred or when launching of products.
- Continuous Improvement Cycle: Penetration tests provide you with results that you can utilize in improving your compliance controls. Also, comply with monitoring of use to identify areas where greater security testing should be done.
The Risk Management Benefit
Combining automated compliance tools with penetration testing will result in an effective risk management system. Compliance automation deals with the controls you require. Penetration testing assures how well those controls actually protect you.
Based on the latest USA cybersecurity data, organizations that adopt this interdisciplinary methodology have:
- 67% faster incident response times
- 54% reduction in successful breach attempts
- 43% lower cyber insurance premiums
- 89% higher customer trust ratings
These are not numbers, but actual business value. Furthermore, they also indicate the reason why top organizations do not have a choice of compliance versus security testing – they accept both.
Learn More About Our Advanced Pen Testing Services.
Industry-Specific Integration Examples
Different industries implement this integration differently:
- Healthcare (HIPAA Compliance): Compliance tools are used to ensure HIPAA documentation and controls by healthcare providers. They then have to perform penetration testing to make sure that patient data is not susceptible to new attack patterns. This is an essential combination since the cost of healthcare data breaches in the USA is an average of 10.93 million dollars.
- Financial Services (PCI DSS): Banks and payment processors ensure PCI DSS compliance by automating them and performing quarterly penetration tests as needed. Further, they undertake testing in case of a major change in infrastructure.
- Technology/SaaS Companies: Tech businesses are providers of SOC 2, often achieved through automated means. In the meantime, they also do penetration testing when they are about to launch major releases and have bug bounty programs to ensure ongoing security verification.
Discover more on data security compliance.
Why Is Qualysec the Best Choice for Real-World Security Testing in the USA?
Although compliance automation tools are apt in managing your base needs, the decision on the appropriate penetration testing partner is the difference between achieving your systems and not. This is where Qualysec will be the best option for businesses in the USA.
Why Qualysec Leads the Market?
Qualysec has positioned itself as the leading penetration testing firm in the USA through the use of technical skill and business knowledge. In contrast to pure automated solutions, Qualysec provides full security testing, which prevents attackers by detecting real-world vulnerabilities before they do.
- Comprehensive Testing Methodology: Qualysec does not use automated scanners only. They instead have their certified security personnel perform an extensive manual testing to identify business logic vulnerabilities, intricate attack chains and zero-day vulnerabilities that have eluded automated tools. Moreover, they optimize every interaction to your business setting and threat environment.
- Industry-Leading Expertise: The Qualysec team is made up of certified ethical hackers with such qualifications as OSCP, CEH, and GPEN. They therefore introduce practical attack expertise in each engagement. They know the way real-life cybercriminals think and work, and as a result, they can create realistic attack scenarios.
- Zero False Positives Guarantee: Although automated compliance tools tend to produce many false positives, Qualysec has a human checkpoint on each vulnerability and verifies the vulnerability first before it is reported. This implies that you get findings that can be acted upon and actually require it, and save your group hours of investigation.
- USA-Focused Security Intelligence: As a company mostly operating in the USA market, Qualysec is aware of the local threat environment of American companies. They also keep up with threats against USA organizations and incorporate this intelligence into their testing methodology. Moreover, they have a familiarity with the USA regulatory requirements and compliance models.
Qualysec’s Comprehensive Service Offering
Qualysec is offering a complete range of security testing solutions that are intended to augment your compliance automation systems:
- Web Application Penetration Testing: Find vulnerabilities in your web applications, APIs, and web services. This encompasses the OWASP Top 10 vulnerabilities, business logic vulnerabilities and authentication bypass vulnerability.
- Mobile Application Security Testing: End-to-end testing of iOS and Android apps, client-side security vulnerabilities, insecure data storage, and API security vulnerabilities.
- Network Penetration Testing: Tests your network infrastructure security, such as its firewalls, routers, switches, and the effectiveness of network segmentation.
- Cloud Security Assessment: This is a specialized testing of AWS, Azure, and Google Clouds, and locates misconfigurations and cloud-related vulnerabilities.
- API Security Testing: Specific testing of REST, SOAP, and GraphQL APIs to make sure your application interfaces do not leak sensitive information or functionality.
- Compliance-Focused Testing: Penetration testing, which targets the needs of the SOC 2, ISO 27001, PCI DSS, HIPAA, and other compliance standards.
The Qualysec Advantage
The real differentiator of Qualysec is that they recognize the fact that security testing does not merely involve identifying vulnerabilities, but rather it involves enhancing your overall security posture:
- Detailed Reporting: You get detailed reports that are not written in technical language but are presented in business language, describing the vulnerability of that business. In addition, there is step-by-step remediation advice that is reported with priorities in terms of risk level.
- Remediation Support: Because most testing providers simply vanish after presentation of the report, Qualysec offers remediation support. Their squad responds to inquiries and approves mends.
- Competitive Pricing: Qualysec will provide clear competitive prices with no veiled prices. They deal with small and large-scale businesses.
- Fast Turnaround: Knowing that time to market is a thing, Qualysec provides rapid results of testing without affecting quality. The majority of engagements take up to 2-3 weeks.
- Compliance Integration: Qualysec integrates with your compliance automation systems to give you the manual security validation that your audit team needs.
Real Results for USA Businesses
Companies working with Qualysec consistently achieve:
- Successful compliance audit outcomes
- Significant reduction in exploitable vulnerabilities
- Improved security awareness across their organizations
- Enhanced customer trust and confidence
- Better cyber insurance terms
Don’t leave your security to chance. As your compliance tools do the bare minimum, Qualysec makes sure that you are, in fact, safe against real-life threats.
Schedule a Free Consultation with Qualysec Today and discover what vulnerabilities your compliance tools might be missing. Their security experts will assess your needs and provide a customized testing proposal at no cost.
Talk to our Cybersecurity Expert to discuss your specific needs and how we can help your business.
Understanding When You Need Both Compliance Automation and Security Testing
With the idea of how these approaches work differently and complement one another, it is time to take a closer look at particular scenarios where the existence of both is of paramount importance to U.S. businesses.
Regulatory Requirements Demand Both
The vast majority of compliance frameworks specifically mandate penetration testing and ongoing compliance testing. An example is that the PCI DSS requires quarterly scans of vulnerabilities and penetration tests annually. Correspondingly, the SOC 2 auditors also require evidence of periodic security reviews, not merely policy compliance.
Thus, in case your business is working with credit card payments, with healthcare information, or targeting enterprise clients who need SOC 2 certification, penetration testing is not only necessary but is also mandatory. Nevertheless, compliance automation is still required to keep your baseline controls up amongst the testing engagements.
Customer Trust and Competitive Advantage
Customers in the security-conscious modern market are more demanding in terms of real security testing as opposed to compliance certifications. As such, firms that have been able to prove compliance and routine penetration testing are awarded more deals.
Consider this: when reviewing vendors, sophisticated customers ask specific questions:
- When was your last penetration test?
- Can you share the executive summary?
- How do you remediate identified vulnerabilities?
- What’s your vulnerability disclosure policy?
These questions will not be answered by compliance certifications. In the meantime, companies that actively perform penetration testing and are open about their security-related practices should create better relationships with their customers and finalize business deals more quickly.
Cyber Insurance Requirements
The USA cyber insurance providers are also demanding both the documentation of compliance and the evidence of performing regular cybersecurity tests. In addition, the premiums and limits to coverage usually rely on how many times you test your security and what you have done to fix security issues.
Insurance companies are aware that the compliance automation restrictions imply that certified companies continue to be hacked. As such, they provide organizations that confirm their security by means of penetration testing with improved coverage conditions and reduced premiums.
Incident Response Preparation
In the case of a security incident, the response effectiveness requires knowledge of your real security posture. Organizations that conduct compliance monitoring and penetration testing react better since:
- They know their attack surface from testing
- They understand their most critical vulnerabilities
- They have documented incident response procedures from compliance work
- They can quickly assess what assets might be compromised
Furthermore, regular penetration testing essentially provides incident response practice without actual attackers. Your team learns how to respond to security findings in a controlled environment.
Conclusion
It is not an issue of Automated compliance tools vs penetration testing, but rather seeing the synergies between the two in a way that will provide holistic security. Vanta and Drata are compliance automation tools that offer the necessary baseline security and non-stop monitoring. Nonetheless, they are incapable of substituting the actual world validation that is provided by penetration testing.
The compliance automation limitations and the compliance security gaps at Vanta do not make these tools less useful; it is more to emphasize the necessity of penetration testing. On the same note, when comparing Drata and real-world security testing, it can be seen that they are complementary and not competing at all. Continuous compliance and security testing are the secure components of the security strategy that are adopted by organizations.
It is important to remember that compliance can show that you have controls, but security testing is what can show that controls do work. On the one hand, USA businesses under complex cyber threats must not only effectively protect their resources but also assure the trust of their customers and not go unregulated.
Get in touch with Qualysec Experts Now to develop an integrated security strategy that combines the efficiency of compliance automation with the validation of real-world penetration testing. Don’t wait for a breach to discover the vulnerabilities your compliance tools missed.
Download Our Latest Pentest Report to see exactly what manual security testing can uncover beyond automated compliance scans.
Latest Penetration Testing Report

FAQ
1. What’s the difference between automated compliance tools and real-world security testing?
Automated compliance tools are used to ensure that security controls and policies are in place as per the standards of regulations, and real-world security testing is performed actively to identify vulnerabilities in order to determine whether systems are actually secure. Configuration checking tools are utilized to comply with the configuration; penetration testing is used to ensure that it works against actual attacks.
2. Can automated compliance tools replace penetration testing?
Incidentally, automated compliance tools cannot substitute penetration testing since they are not aimed at security validation, but policy compliance. Penetration testing reveals exploitable weaknesses, business logic defects, and intricate attack vectors which can not be identified and conceived by automated compliance scanners.
3. Why do businesses still need security testing if they already use compliance automation?
Security testing is necessary for businesses since compliance does not ensure they are safe – most compliance organizations are breached. Compliance automation is a mechanism in place that checks the existence of controls, and security testing can be used to ensure that controls in place can withstand real-world attacks and advanced threat agents.
4. How do compliance tools and security testing work together?
Compliance tools also offer sustained control monitoring and enforcement of policies, whereas security tests are used to confirm control efficiency by means of simulated attacks. Combined, they form an integrated security posture: compliance serves as the answer to what you need to control, and testing is the answer to how well it is controlled.
5. Which industries benefit most from combining compliance automation with penetration testing?
The most advantageous combination is in healthcare, financial services, SaaS companies, e-commerce platforms, and government contractors. These sectors are highly regulated, deal with sensitive information, suffer frequent advanced attacks and have customers who require demonstrated safety exceeding compliance certifications.





















































































































































































































































































































































































































































































































































































































































































































0 Comments