If your company works with the U.S. government and manages sensitive data, you must follow NIST 800-171. It is a group of rules that helps keep important information safe from falling into the wrong hands and is essential for achieving NIST 800 171 compliance.
One of the significant aspects of meeting these requirements, and one that we promote heavily, is penetration testing. Penetration testing is more than running a basic scan; penetration testing is simulating actual attacks and determining security gaps so that bad actors cannot exploit the weaknesses.
In this blog, we will explain how penetration testing meets NIST 800-171 compliance, what controls it fulfills, and why it is necessary to maintain a solid security posture.
Where Does Penetration Testing Fit In?
Penetration testing applies to NIST 800-171 in the sense that it allows an organization to discover and remediate threats to security in any organization before hackers can exploit them. It is a practice where ethical hackers will assess the security of your systems like a cyberattack.
Penetration testing relates to NIST controls, which focus on risk assessment and assessment of vulnerabilities. The vulnerability scan is automated, whereas penetration testing is much deeper and manual.
In essence, it identifies what the threat could do to your organization for real. For U.S.-based companies requiring CUI, it is a great way to demonstrate that your systems can sustain security and compliance.
Compliance doesn’t wait; why should you? Let Qualysec help you meet NIST 800-171 with confidence. Talk to industry experts—book your free call now.
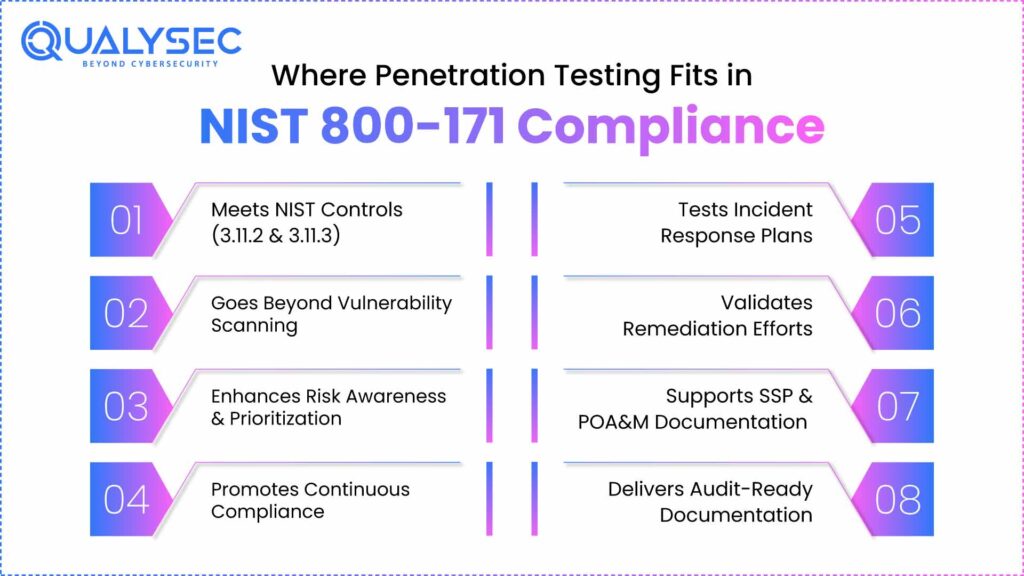
1. Meets Key NIST Controls (Especially 3.11.2 & 3.11.3)
Penetration testing fulfills two important controls in NIST 800-171, mainly 3.11.2, which requires scanning for vulnerabilities, and 3.11.3, which focuses on remediation based on risk. Vulnerability scans perform a great job covering the common problems, though they leave one huge hole in that scanning will never give you certainty that a weakness can be hijacked.
Pen testers will bring the validation of testing into your risk assessment. As well as help prove to auditors or federal agencies that you were not just scanning but actively trying to exploit and remediate your systems.
2. More than Vulnerability Scanning
Vulnerability scans are a good start, but are often all automated and, as such, simply at the surface level. Penetration tests are more than a step in the right direction because a pen tester will simulate an actual threat actor with a biased evaluation instead of rule sets to identify how deep a threat may be able to traverse, should they gain entry, and what data would be assumed as exposed.
Where a scan will list many potential flaws, a pen test will show how a flaw could be used in an actual breach. Used together, you can see where you fall, not only in risk but also from an actual breach standpoint, validating the theory of an organization’s security position alongside the reality of the risks identified. Book a live penetration test demo.
3. Enhances Risk Awareness & Prioritisation
Not all vulnerabilities carry the same threat level, and penetration testing helps your team figure out the most urgent ones while understanding you might need to wait longer to address other issues, within reason. It enables you to facilitate an assessment of what the real-world impacts of those issues were and sits right into the idea of risk-based decision-making, like the NIST framework.
Basing priorities on real-world impact for remediation instead of treating all issues equally means the team is working smarter, expending valuable time and resources where they’ll make the biggest difference.
4. Test Your Incident Response Plan
A crucial aspect of NIST compliance is how well you and your team can respond to an actual attack. Penetration testing will provide you with the ability to test that in a safe and controlled manner.
During a test, an ethical hacker may attempt to break in, escalate privileges, proffer lateral movement, hijack working sessions, and/or strike senselessly at their target data. You will observe how your team reacts, what alerts they generate, and where their response actions fail. Knowing these insights is important for fine-tuning and improving your incident response plan before something tangible happens.
Struggling to prioritize vulnerabilities? Let our team assess your risk and give you actionable insights.
5. Validates Your Remediation Efforts
Remediating a vulnerability is only half the challenge; you also have to validate that your remediation actually worked. Penetration testing will assist in remediation validation for you by retesting systems after a patch or update.
The hill you chose to die on regarding your policies easily includes NIST controls like 3.11.3, 3.12.3, and 3.14.1, which strive towards incessant vigilance and verification. Pen tests lend hard evidence that security controls are implemented, working, and ready to defend you against an actual threat.
6. Aids in Developing SSPs & POA&Ms
NIST 800-171 requires each business to have two primary documents: a System Security Plan (SSP) and a Plan of Action and Milestones (POA&M). You’ll need the results from your penetration tests to develop your SSP and POA&M.
The details of the penetration test will provide you with a detailed and factual report of security issues present, levels of risk according to the test-identified issues, and subsequent remediation efforts or fixes. Demonstrating you are aware of the risk and building a return to closure is a win-win for compliance and contract eligibility.
7. Delivers Audit-Ready Documentation
When it comes time for an audit and preparing for CMMC certification, you will need documentation that supports your information security compliance efforts. The penetration test documentation will come in handy in providing solid proof of your practices.
Penetration test results provide a clear summary of what was tested and what was discovered, as well as a summary of your plans and actions taken. Auditors like to see this, particularly when it clearly articulates that what you said you had in place for security controls exists and works.
Good documentation provides a level of transparency, which is always a benefit when working with contracting officers and their government partners.
See our sample penetration test report to understand how we identify real threats.
Latest Penetration Testing Report

How Qualysec Can Help
Qualysec provides expert-led penetration testing services focused on helping U.S.-based organisations meet NIST 800-171 compliance. Our certified ethical hackers perform simulated real-world attacks to identify and validate security vulnerabilities – far beyond simply performing a vulnerability scan.
We detail our findings in an audit-ready report, which addresses specific NIST controls like 3.11.2 and 3.11.3 and assists your organization in remaining compliant and secure.
We also provide retesting and re-verification after remediation efforts, verifying that any vulnerabilities have been corrected. Our continuous testing model ensures that your organization remains compliant over time.
Our services, from cybersecurity risk assessments to documentation/planning support with System Security Plans (SSPs) and Plans of Actions and Milestones (POA&Ms), include much more. Qualysec provides comprehensive compliance support to assist your organization.
Stay ahead of hackers—get a real-world security test today. Schedule your penetration test with Qualysec now.
Talk to our Cybersecurity Expert to discuss your specific needs and how we can help your business.
Conclusion
NIST 800-171 compliance is important for any organisation that handles Controlled Unclassified Information (CUI) for the U.S. government. Regular penetration testing can help achieve this goal. It reveals actual vulnerabilities, allows for necessary fixes, and ensures ongoing risk management.
A penetration test verifies several key NIST controls and strengthens your overall cybersecurity efforts. You should conduct continuous penetration testing as a regular part of your security measures. It’s not just a task to tick off; it’s essential for protecting sensitive data and proving you are prepared to collaborate with federal agencies.
Not sure if you’re truly NIST compliant? Qualysec’s testing gives you proof, not assumptions.
See what real clients say about our results: View Qualysec’s Clutch profile.
FAQs
1. What is NIST 800-171 Compliance, and Why Is It Important?
NIST 800-171 is a set of cybersecurity rules for organizations that handle Controlled Unclassified Information (CUI) under U.S. government contracts. It is important because it establishes best practices for managing sensitive data and is required for federal work.
2. How Does Penetration Testing Help with NIST 800-171 Compliance?
Penetration testing helps find real security gaps that hackers could exploit. It supports key NIST controls related to vulnerability scanning, risk assessment, and fixing issues.
3. What Vulnerabilities Does Penetration Testing Identify for NIST 800-171?
Penetration tests can uncover weak passwords, open ports, misconfigured systems, outdated software, and other problems that automated scans may miss. These are all risks that NIST wants organizations to address.
4. How Often Should Penetration Testing Be Done to Maintain NIST 800-171 Compliance?
Most organizations perform penetration tests at least once a year. However, it is generally a good idea to test when there are significant system changes or when new threats arise. Some organizations may choose to conduct ongoing penetration testing as an extra layer of security.
5. Can Penetration Testing Evidence NIST 800-171 Compliance?
No, penetration testing is just one part of the whole process. You will also need access controls, incident response plans, security training for your staff, and the necessary documentation to meet NIST 800-171 compliance successfully.



















































































































































































































































































































































































































































































































































































































































































































0 Comments