Introduction
Imagine you run a small online shop. One morning, you open your laptop and see dozens of messages from angry customers saying money has been stolen from their accounts. You check your systems and discover that hackers have broken in and stolen credit card details stored in your cloud account.This is not just a bad dream. It happens to businesses every day — from small shops to big companies.
The problem? Most businesses assume that storing card data in the cloud is inherently safe. But unless you follow PCI Cloud Compliance rules, you are leaving the door open for trouble.
Understanding PCI DSS in Simple Words
The full name is Payment Card Industry Data Security Standard (PCI DSS). This is a set of rules made by the biggest card brands like Visa and Mastercard.
Think of it as a safety guide for anyone who handles cardholder data — things like card numbers, names, and expiry dates.
It tells you exactly how to store, protect, and use card data so that hackers can’t steal it.
Talk to Our Experts About Securing Your Cloud Data.
What PCI Cloud Compliance Really Means?
When you keep cardholder data in the cloud, you must still follow all PCI DSS rules.
PCI Cloud Compliance means:
- Your cloud setup follows PCI DSS safety rules.
- Both you and your cloud provider share the work of keeping the data safe.
- All risks are checked and fixed regularly.
Example: If your store uses Amazon Web Services (AWS) to save card details, both you and AWS must follow the rules — you by setting up your systems securely, AWS by keeping their own cloud infrastructure safe.
Why It’s Critical for Businesses Today?
In the old days, card data was stored only on office computers. Now, many companies use cloud services because they are cheaper, faster, and easier to manage.
But the cloud is not magic. It’s just someone else’s computer you access online. If you don’t lock it properly, hackers can still break in.
Stat: More than 60% of businesses store card data in the cloud, but only 39% follow all the PCI DSS rules.
That means more than half of businesses are taking huge risks without realizing it.
Explore our recent article on cloud security service.
How the Cloud Changes Compliance Needs?
With cloud storage, you have what’s called a shared responsibility. This means:
- The cloud provider handles the safety of the hardware, network, and basic services.
- You handle the way data is stored, accessed, and protected inside that system.
If either side fails, your data can be exposed.
Risk Without PCI Compliance vs With PCI Compliance
| Without PCI Compliance | With PCI Compliance |
| Hackers can steal card data easily | Data is locked with strong protection |
| Businesses can face heavy fines | Follows legal and industry requirements |
| Customers lose trust and leave | Customers trust you and return to buy |
| Hard to win back your reputation | Builds a reputation for safety |
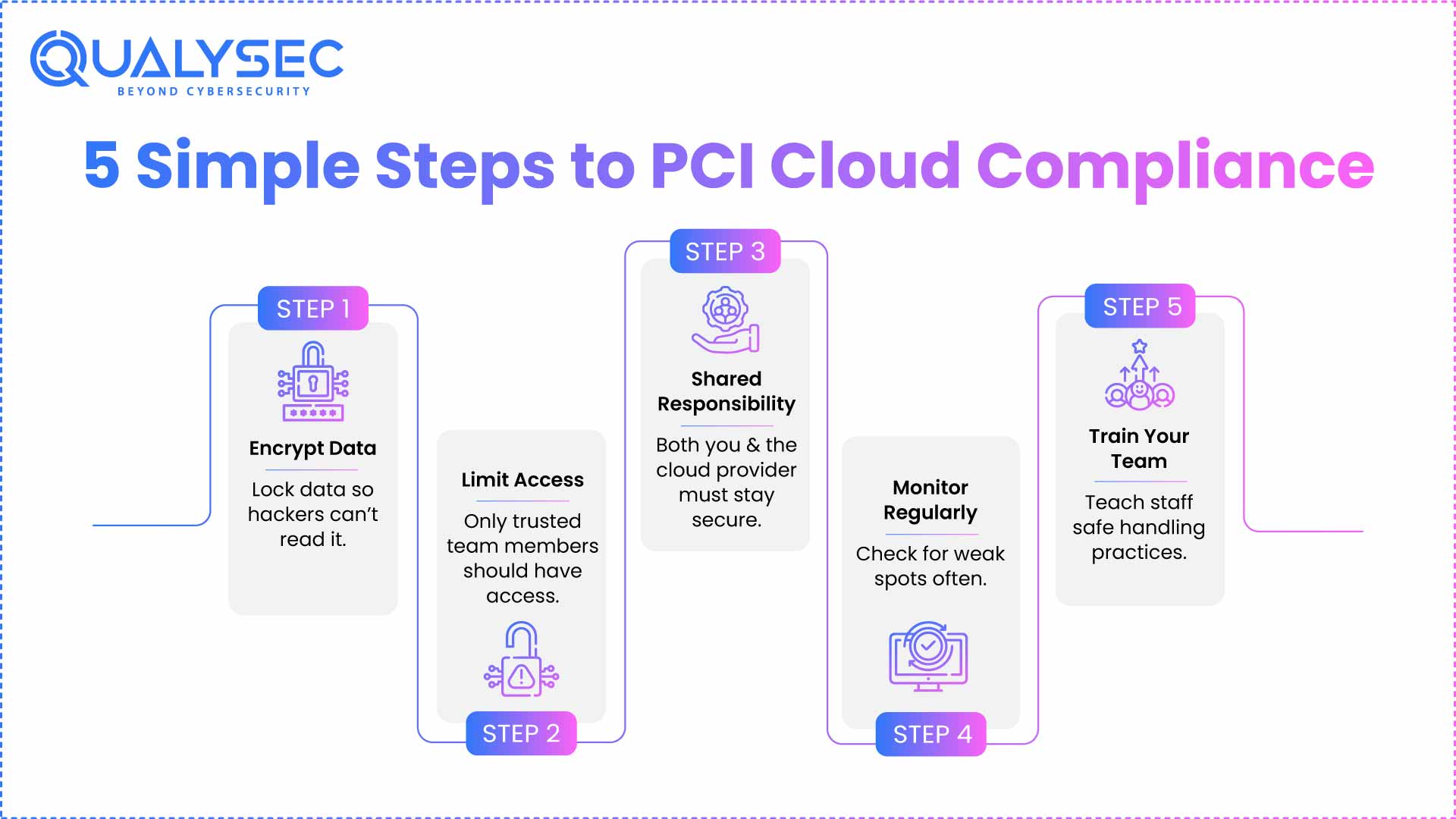
PCI DSS Cloud Guidelines – Made for Busy Business Owners
If the official rules look scary, here’s the short version:
- Know who does what – Make a clear agreement with your cloud provider about who protects which parts.
- Limit access – Only the right people in your team should see or use card data.
- Encrypt data – This means turning data into secret code so hackers can’t read it.
- Watch your system – Check for weak spots regularly.
- Be ready for trouble – Have a plan to fix things fast if there’s a problem.
Who Is Responsible – You or the Cloud Provider?
Many business owners believe the cloud provider will handle everything. That’s wrong.
The truth:
- The provider keeps their infrastructure safe.
- You must keep your part of the system safe.
Shared Responsibility in PCI Cloud Compliance
| Area | Cloud Provider’s Job | Your Job |
| Physical servers | Protect data centres | Not your job |
| Network protection | Stop outside attacks on their network | Use safe settings in your account |
| Data encryption tools | Provide tools for encryption | Make sure they’re turned on and used right |
| User accounts | Provide account management features | Control who has access and remove unused |
| Compliance paperwork | Share their certifications | Keep your own compliance records |
Read also: PCI Compliance Test: What It Is and How to Prepare Your Business
Challenges Businesses Face
Some problems you might face:
- Thinking the provider does it all – This is the biggest mistake.
- Complex setup – Cloud systems have many settings. One wrong setting can make data unsafe.
- Frequent changes – Every time you update your system, you must re-check your security.
Practical Steps to Secure Card Data in the Cloud
To stay safe:
- Use strong passwords and change them often.
- Allow only trusted team members to access card data.
- Encrypt everything before storing it in the cloud.
- Test your system regularly.
- Track and record all changes.
Explore now: Achieving PCI DSS Compliance in Cloud Environments
Training Your Team
Even the best tools won’t help if your team doesn’t know how to use them.
Train staff to:
- Avoid suspicious links.
- Keep passwords secret.
- Report problems fast.
Repeat training every 3–6 months, so they stay updated.
What Happens When You Neglect PCI Cloud Compliance?
There is a popular misconception among several entrepreneurs that cybersecurity can be resolved at a later stage. But the cost of waiting on this one can be far more terrifying than simply getting started properly. If you fail to play by PCI rules in the cloud, you could be fined heavily, either by a payment firm or government regulators. They can be from one to millions, depending on the gravity of the issue.
There are also repair costs. If hackers introduce themselves to your cardholder data, you may be obligated to bring in a team of experts and repair just to understand what happened, let alone fix it and harden your systems. You may also have to pay for credit monitoring services for customers affected by the breach.
It doesn’t end with money. This can severely damage your business reputation! People put their payment details into your trust. Be assured, you will never see them returned if that trust is lost. Even worse, they will share their experiences with other property interests, which means that you will have just scared prospective customers away.
At the most critical levels, a data breach can shut down your business forever. Many of these small companies will not financially or even conspiracy-wise be able to weather this loss. This is why turning a blind eye to PCI Cloud Compliance is never worth the risk.
Learn how penetration testing helps achieve PCI DSS Compliance. Download a sample report now.
Latest Penetration Testing Report

Selecting the Right Cloud Provider
When you want to define PCI Cloud Compliance, one of the essential factors is choosing the right cloud provider. These are all good things, but not all cloud providers are created equal. Some are seasoned and secure; others may not.
If you answered “yes” to any of those questions, then before you choose a voice service provider, ask if they are PCI DSS compliant and for proof. Inquire whether they provide security solutions such as encryption, firewalls, and access control. Learn more about their threat monitoring capabilities and how fast they can respond to incidents.
You also need to inquire how frequently they get their systems updated. Security updates are also crucial since they patch problems that hackers can exploit. If your provider avoids or cannot answer your simple questions, then that is the sign then and there that your search was not correct.
Keep in mind that you are giving over control of your customer’s vulnerable card data to this provider. Well, then you’d better make sure they do.
Encryption in Cloud-Based Systems
One of the most reliable and useful data protection Prime Spectacle, which can be used to mask your cardholder data. It converts the details into a secret code. The only ones who can read this are the people who have the correct key.
This means that if hackers get access to your cloud account and find encrypted data, they will only see the jumbled letters and numbers, which tell them absolutely nothing. PCI Cloud Compliance requires that cardholder data be encrypted at rest, that is, when stored in the cloud, and in transit, as it moves around.
Most cloud providers do provide encryption as part of their service, but you must ensure that it is enabled and properly configured. It is like locking your front door but having all windows wide open, because without encryption, everybody will see your data in transit.
The Importance of Access Control
But it is also very simply addressed by having minimal access to those who not only need to see the data (typically only administration) but have an associated processing requirement. This is not information that should be available to everyone in your company.
So, first things first, you have to list those who are allowed to breach Cardholder Data. So delete access for everyone who is not supposed to have that. This shrinks the attack surface by limiting the number of people who might inadvertently or deliberately create a security issue.
Ensure that anyone who has access is using strong passwords as well, and multi-factor authentication for a second code or approval before letting someone in. Immediately deactivate the accounts if any employee quits in order to avoid unauthorized use.
The fewer the number of users who have access to this, the safer the business will be.
How to Include PCI Cloud Compliance in Your To-Do List?
A lot of companies view it as a one-time thing they have to do with PCI Cloud Compliance. However, data security is not one project — it is an ongoing endeavor.Make it a point to review your cloud security settings on at least a monthly basis to ensure no one has accidentally altered this fundamental aspect of your virtual machine. Always make sure your software is updated since updates often plug security problems. Go through your cardholder data access control list and delete everyone who does not need this information.
Which is why you need to test backup restores, to ensure that in the event of a disaster, data can be restored quickly. It’s an old argument, but the fact is that backups are like a safety net: you never want to need it, but when you do, you must let it perform as designed.
Finally, train your team regularly. The best systems in the world are useless if people screw up. Organize special training every couple of months to remind employees how to use cardholder data safely, not click on Phishing emails, and report suspicious activity.
After some time, this becomes less about being required to do something for PCI Cloud Compliance and more like locking your door when you leave the house.
You might like to learn: PCI Risk Assessment: What It Is, Key Steps, Benefits, and Compliance Tips
How QualySec Can Help?
You cannot simply purchase the flowery cloud security tool and expect that cardholder data will magically be safe. The sad fact is that zero days will probably always be around; some smart person can always find a crack in our armor. It’s about knowing how to effectively use them and ensuring that they do not get abused before the last line of defense hits. Here is where QualySec gets into the picture as your confidante.
PCI DSS cloud compliance guidelines need to be analyzed and implemented throughout the lifecycle of business processes, secure pipeline assemblies and for that, there are companies like QualySec — a team of cybersecurity experts who can help businesses of all sizes keep their clouds audited. They recognize that not every business has a large IT team or strong technical acumen, so they break everything down into basic, straightforward steps.
What QualySec Do for You?
- Complete cloud security scan – this includes a scan of your cloud environment to look for vulnerabilities that might expose cardholder data.
- Fixing the issues – When risks are identified, they tell you what to do with them or can take care of the fixes for you.
- Team Training — Your contingent will be trained to handle card data safely, avoid mistakes and observe compliance rules on a day-to-day basis.
- Ensuring your compliance – They help keep you in line with PCI DSS regulations and ensure that even as systems and rules evolve, they can continue to support these requirements.
- No matter what, the coolest thing is that you are not alone. QualySec is with you from that initial check to continuous monitoring. This allows you to focus on your business whilst reducing the risk of stolen customer card data and maintaining your clean reputation.
Book a Free Consultation if you have any queries.
Talk to our Cybersecurity Expert to discuss your specific needs and how we can help your business.
Conclusion
PCI Cloud Compliance is more than simply describing the technical details; it’s about the assurance of trust in your business to your customers. When a customer gives you their card details, they are giving you the keys to some of their most sensitive data. Once that trust is lost, it’s a Herculean task to regain.
If you do not comply with the rules, you may not only be hacked but also much more than that. If you violate that trust, there are potential financial consequences, legal troubles, and a tarnished rep. Bad news travels quickly in the digital era. A single data breach can turn customers into the waiting arms of competitors who value security.
The good news is that stick PCI Cloud Compliance is completely doable for all-sized businesses when done right. Maximize the security offerings of your cloud provider, because this is a natural choice when they already follow the rules of protection of PCI DSS requirements and also understand clearly how it works in terms of which domains you are responsible for. Keep all data encrypted.
Tokenization: keep cardholder data out of your systems. Train your team frequently.
But you need not face your fears solo. A partner like QualySec has the knowledge, experience and best practices for guiding you through maintaining compliance year by year.
In short, you have to maintain PCI Cloud Compliance.If you care about your customer, revenue, and brand. So why not get going now, as it will be just a matter of time before this is rolled out in law? Go on, get prepared, and maybe in the future you will have a more secure, trustworthy business. Contact Us Now to Secure Your Cloud Environment.
FAQs – PCI Cloud Compliance Explained in Detail
1. What is PCI cloud compliance?
PCI cloud compliance means following special safety rules (called PCI DSS) when you keep or use credit card information in the cloud. These rules tell you how to lock and protect that data so hackers can’t steal it. Even if the card data is stored on someone else’s computer (your cloud provider), you must still make sure it is safe. Think of it like storing gold in a bank locker — the bank keeps the building secure, but you must still lock your locker.
2. Do cloud service providers need to be PCI compliant?
Yes, they do. If a cloud company stores or processes credit card details for you, they must also follow PCI DSS rules. But here’s the important part — even if your cloud provider is PCI compliant, that doesn’t mean your business is automatically safe. You must still set up your account, passwords, and access controls the right way. It’s like living in a secure building but forgetting to lock your apartment door.
3. What are the challenges of PCI compliance in the cloud?
Some challenges include:
- Shared responsibility – The cloud provider secures their systems, but you must secure your part.
- Complicated settings – Cloud accounts have many options. One wrong click can make data unsafe.
- Constant changes – Every time you update your system or add new tools, you must check security again.
4. Which cloud platforms are PCI DSS compliant?
Popular cloud platforms like Amazon Web Services (AWS), Google Cloud, and Microsoft Azure already meet PCI DSS standards. But remember — just choosing them isn’t enough. You must use the security tools they offer, like encryption and access control, correctly.
5. How can I make sure my cloud is compliant?
You can:
- Pick a PCI-compliant cloud provider.
- Encrypt all card data before saving it in the cloud.
- Limit access to trusted team members only.
- Check your system regularly for problems.
- Work with experts like QualySec to guide you step-by-step.



















































































































































































































































































































































































































































































































































































































































































































0 Comments