American companies are confronted with a bleak truth: IT security assessments are the alternative to disaster recovery, i.e., act in advance, and act in response. Recently updated information indicates that cyber attacks target U.S. organizations, on average, every 14 seconds, and a systematic security assessment is, therefore, not a checkbox compliance but a business requirement. Financial incentives are gaining momentum, and the cost of data breaches has gone as high as an average of 4.45 million dollars worldwide and much more among American companies.
IT security assessments offer organizations a formalized way of determining vulnerability, assessing the effectiveness of controls, and ranking security capital investment in relation to the real risk exposure. As compared to a simple security scan or a one-time audit, an extensive information security assessment program establishes a sustained visibility of your security position, as well as the ability to make data-driven decisions. This process of systematic approach assists organizations to get out of reactive patching to strategic risk management that is aligned with business goals and regulatory demands.
What Are the Essential Steps for Conducting IT Security Assessments?
Effective IT security assessments have a well-organized methodology that will cover everything and provide a course of action. The knowledge of these basic steps assists the organization in dealing with assessments in a systematic way and not in a random manner.
1. Define Assessment Scope and Objectives
The initial phase in any information security assessment would be to define what you would like to accomplish and what systems require testing. This preparation period establishes the background of all that comes after it. Organizations must identify specific business units, applications, networks, and data types to assess.
The cybersecurity assessment checklist should consist of whether you are performing a compliance audit, risk assessment, or vulnerability assessment. Each type serves a different purpose and requires a different approach. As an example, a HIPAA compliance assessment is one that pays much attention to the protection of healthcare data, whereas a financial services assessment is one that pays much attention to PCI DSS requirements.
2. Inventory and Classify IT Assets
The basis of successful IT security assessments resides in asset discovery. There is nothing that you can protect without knowing its existence. This step includes the provision of a detailed inventory of all hardware, software, databases, networks, and cloud services in your organization.
During this stage, classification is equally important. Not every asset carries the same level of risk or requires the same protection. Environment Critical systems dealing with sensitive customer information require stronger security controls than the internal development environment. It is functional classification that contributes to the prioritization of the assessment activities and efficient allocation of resources.
3. Identify Threats and Vulnerabilities
Current enterprise IT risk assessment should take into consideration external and internal threats. Cybercriminals, nation-state actors, and even hacktivist groups are external threats to American businesses. Internal risks include employee grievances, human factors, and poor access controls.
Vulnerability identification requires multiple approaches:
- Automated vulnerability scanning tools
- Manual penetration testing
- Configuration reviews
- Policy and procedure evaluations
- Social engineering assessments
- Physical security inspections
4. Evaluate Existing Security Controls
Your information security assessment must evaluate how well current security measures perform against identified threats. This evaluation goes beyond simply checking whether controls exist. It examines their effectiveness, implementation quality, and operational consistency.
Security control assessment is supposed to be in terms of technical, administrative, and physical security. Firewalls, encryption, and access management systems are considered technical controls. Administrative controls include training programs, policies, and procedures. Physical controls entail the creation of building security, protection of equipment, and environmental surveillance.
Read more: Security Testing Methodologies | Process & Checklist.
5. Document Findings and Risk Levels
The right documentation will turn assessment activities into valuable business intelligence. The team must provide comprehensive descriptions, possible impact analyses, and suggested correction measures for the identified vulnerabilities. Risk scoring also aids in prioritizing remediation activity according to probability and business potential impact.
| Risk Level | Likelihood | Impact | Action Required |
| Critical | High | High | Immediate remediation required |
| High | High | Medium | Remediation within 30 days |
| Medium | Medium | Medium | Remediation within 90 days |
| Low | Low | Low | Monitor and address during the next cycle |
Which Critical Areas Should Your Information Security Assessment Cover?
Various areas should be encompassed by comprehensive IT security assessments, which are all related to each other and will determine the security posture of your organization. There are dangerous blind spots when key areas of attention are given to technical controls, but governance and compliance are left out.
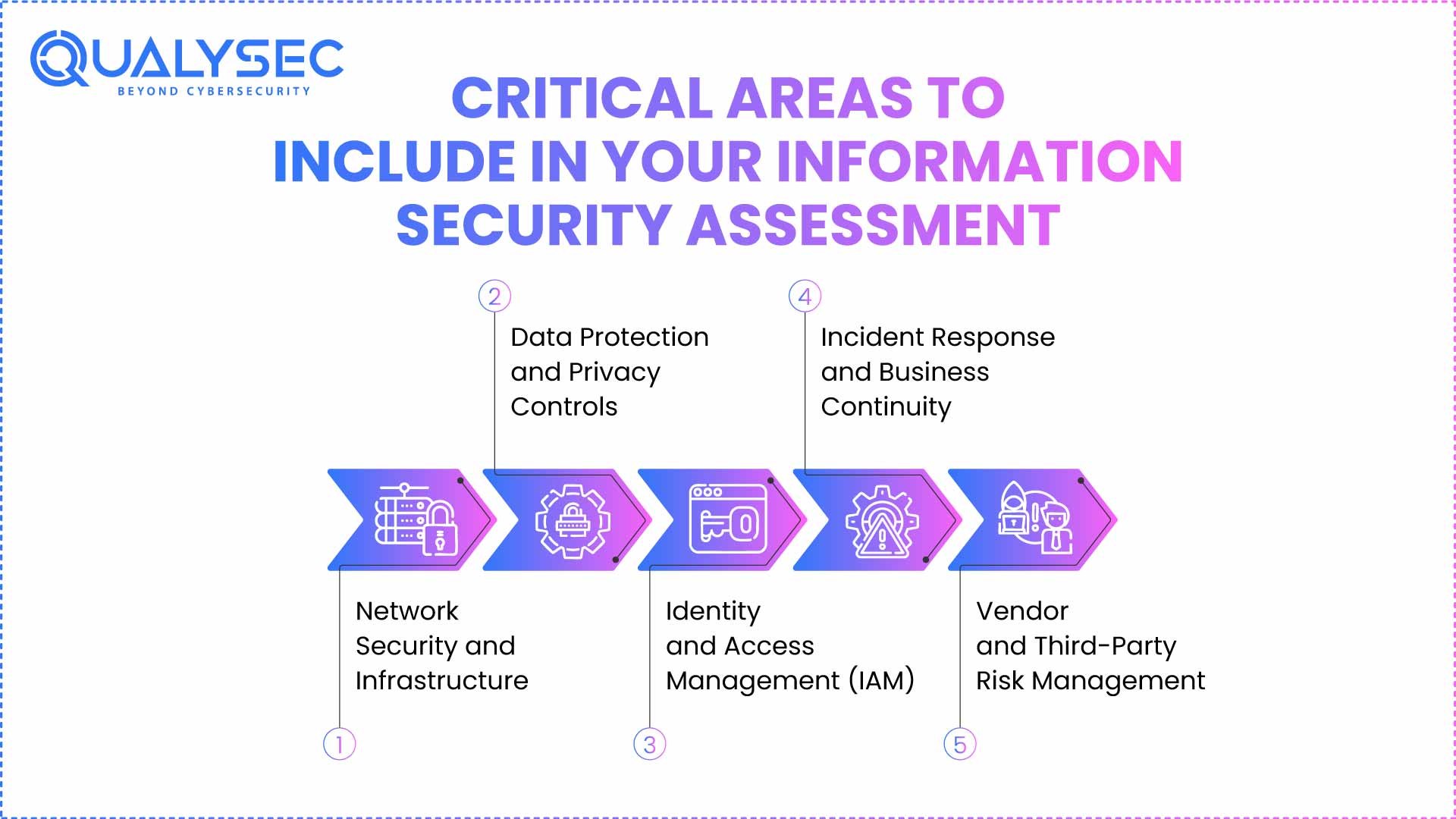
1. Network Security and Infrastructure
Network security assessment forms the core of most cybersecurity assessment checklists. This evaluation examines perimeter defenses, internal network segmentation, wireless security, and remote access controls. Modern businesses rely heavily on cloud services, making cloud security configuration equally critical.
Key network security areas include:
- Firewall rules and configurations
- Intrusion detection and prevention systems
- Virtual private network (VPN) implementations
- Network access control (NAC) systems
- Wireless network security protocols
- Cloud service configurations and access controls
2. Data Protection and Privacy Controls
Data is the crown jewel of most organizations, and it is the main target of cybercriminals. Your information security assessment should be done comprehensively to ensure that the manner in which sensitive information is collected, stored, processed, and transmitted within your environment is properly addressed.
The data protection analysis should examine the encryption policies, data classification plans, retention, and disposal policies. Privacy controls become even more important as American companies are going through stringent regulatory frameworks, including CCPA, GDPR, and industry-specific requirements.
3. Identity and Access Management (IAM)
Identity-based attacks have been on the increase in American organisations, and IAM assessment is essential to high-quality enterprise IT risk assessment. This assessment includes user provisioning, password policy, multi-factor authentication, privileged access control, and periodic access control.
The assessment of IAM needs to deal with human and non-human identities. Things like service accounts, API keys, system to system authentication tend to get less attention even though they present a major attack path. Correct IAM evaluation makes sure that only authorised organizations are able to see sensitive resources.
4. Incident Response and Business Continuity
Your IT security assessments would be to measure the preparedness of the organization to security breaches and business interruptions. This evaluation will cover incident response processes, communication, forensic, and recovery processes.
Business continuity assessment encompasses backup systems, recovery plans, alternate processing location, and resiliency in the supply chain. The COVID-19 pandemic showed that the disruption of business mechanisms can be rapid, and therefore, these capabilities are critical to the survival of the organization.
5. Vendor and Third-Party Risk Management
Enterprises today are heavily dependent on vendors, suppliers, and business partners, making risk relationships complex, which have to be considered by an information security assessment. Third-party risk assessment involves looking at the security requirements in the contract, vendor security questionnaires, continuous monitoring processes, and incident reporting requirements.
The issue of supply chain security has become noticeable due to major attacks on software vendors and managed service providers. Your evaluation should look at how third-party relations may make your organization vulnerable to other risks.
Recommended Read: Vendor Risk Assessment: A Complete Guide in 2025.
How Can You Transform Assessment Results into Actionable Risk Reduction?
Doing a comprehensive IT security assessment is just half the battle. The actual value will be realized as the organizations focus systematically on any vulnerabilities identified and improve the general security posture. Most tests end up failing since reports end up being locked up in reports and do not lead to any meaningful change.
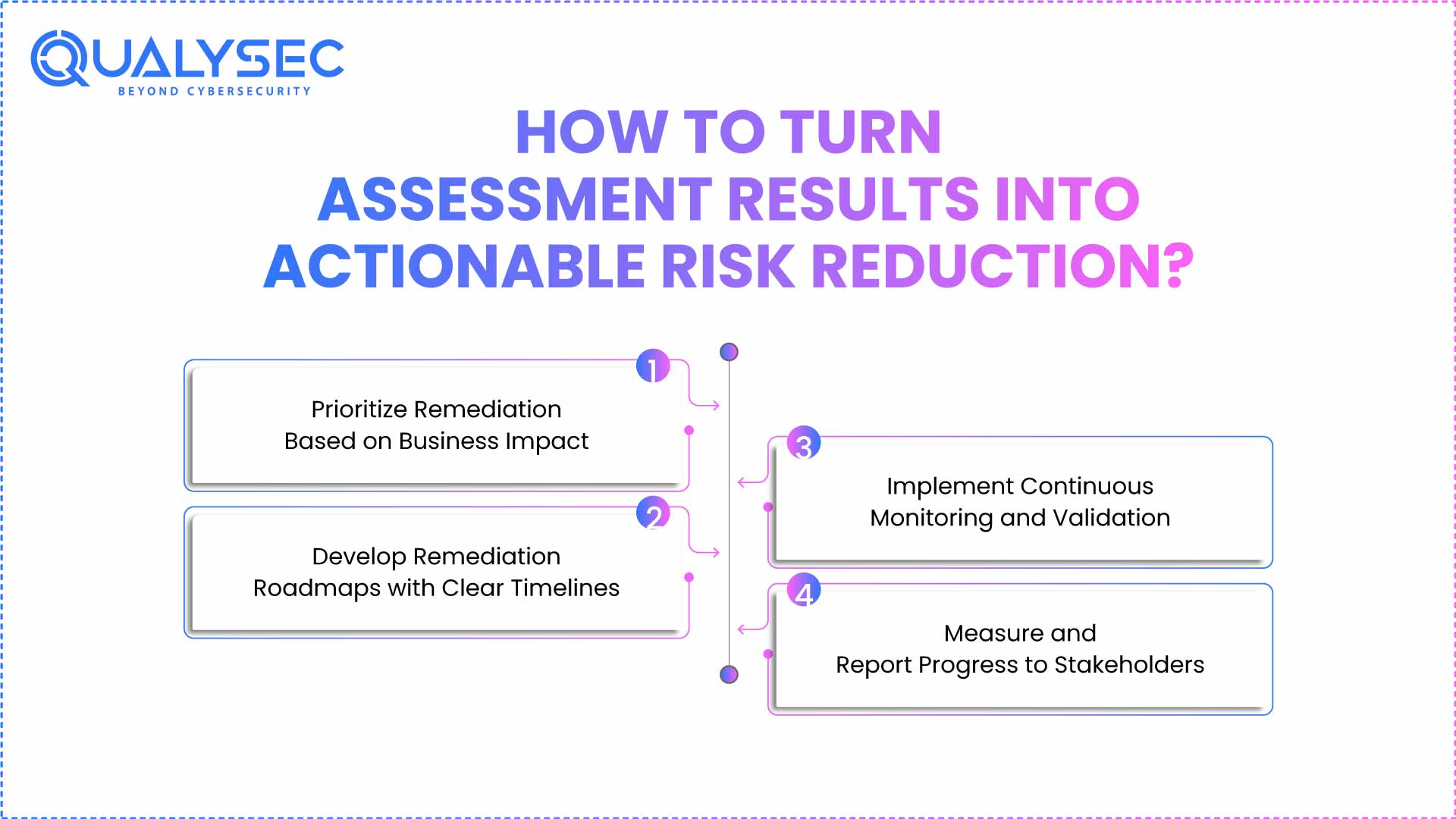
1. Prioritize Remediation Based on Business Impact
Remediation needs to be approached strategically and not by trying to solve everything at the same time. In your cybersecurity assessment checklist, risk scoring methodologies that both look at the severity of risks and their context to business must be included. High-risk vulnerabilities that impact revenue-generating systems have to be addressed as a priority, whereas the lower-risk ones can be subjected to standard change management procedures.
Prioritization should account for:
- Potential financial impact of exploitation
- Regulatory compliance requirements
- Operational dependencies and system criticality
- Available resources and technical complexity
- Threat landscape and attack likelihood
Gain Valuable Insights from Our Comprehensive Guide to Compliance Security Audit.
2. Develop Remediation Roadmaps with Clear Timelines
Successful enterprise IT risk assessment initiatives deliver end-to-end remediation road maps that are urgent and realistic to implement. These roadmaps should clearly define who handles each task, what resources they need, their dependencies, and the expected completion times.
Short-term (0-30 days) activities are primarily focused on reducing the immediate vulnerabilities that are threatened. The medium-term projects (30-180 days) are aimed at significant changes in the sphere of security that require planning and coordination. Big infrastructure improvements and long-term strategic security investments are included in the long-term projects (6 or above).
3. Implement Continuous Monitoring and Validation
Teams must continuously validate security enhancements to keep them effective and sustainable. The information security assessment program that you have developed must also have continuous monitoring features to identify new vulnerabilities, configuration drift, and new threats. Periodic certification ensures that the controls in place perform as desired and offer the desired levels of protection.
Monitoring should encompass:
- Automated vulnerability scanning schedules
- Configuration management and compliance monitoring
- Security control effectiveness testing
- Threat intelligence integration and analysis
- Key risk indicator (KRI) tracking and reporting
Learn Why Continuous Security Testing Matters for Your Business.
4. Measure and Report Progress to Stakeholders
Business stakeholders and executive leadership should be provided with frequent reports on the progress of security improvements and their general risk posture. Reporting effectively converts technical findings into business language and points out improvements in protection, achievements of risk reduction, and areas of exposure.
Progress reporting is to contain quantitative indicators, e.g., the number of vulnerabilities, the rate of remediation completion, average time to resolution. Qualitative evaluations give information regarding the maturity of security programs, the evolution of threats, and the enhancement of strategic risk management.
Why Choose Qualysec for Your Enterprise IT Risk Assessment in the USA?
Companies throughout the United States rely on Qualysec to provide a full range of IT security assessments that offer practical information and quantifiable risk mitigation. Qualysec, being one of the most expert cybersecurity assessment providers, ensures a combination of strong technical expertise and business knowledge in assisting American companies to improve their security posture.
The information security assessment methodology of Qualysec is based on industry-standard structures and adjusts to the unique business needs, regulatory compliance, and risk tolerance of every client. Their staff of trained security experts knows the threat environment of American businesses is a complex one and offers viable advice that balances both operational and security efficiency.
Comprehensive Assessment Services –
Qualysec offers a full range of security assessment services tailored to different business requirements. Their cybersecurity assessment checklist includes all of the essential security domains, such as network security, application security, cloud security, and compliance assessment. This holistic manner is what makes sure that any crucial vulnerabilities or compliance lapses do not get out of hand..
Their assessment services include:
- Vulnerability Assessment and Penetration Testing (VAPT) – Determine the technical vulnerabilities by using automated scanning and manual testing.
- Web Application Security Assessment – Thorough assessment of web-based applications and APIs.
- Mobile Application Security Testing – iOS and Android applications security testing.
- Cloud Security Assessment -AWS, Azure, and Google Cloud setup.
- Network Security Assessment – Network security testing and configuration testing.
- Compliance Assessment – The verification of compliance with such regulations as SOC 2, PCI DSS, HIPAA, and NIST.
Industry-Leading Expertise and Certifications –
Qualysec is certified with security professionals who have industry-recognized certifications like CISSP, CISM, CEH, OSCP, and CISSP. Such proficiency means that your enterprise IT risk assessment will take advantage of the latest techniques and adhere to the best practices in the security industry. They constantly educate and monitor threat intelligence to keep their team abreast of the latest threats and attack strategies, as well as defensive technologies.
The company has a history of successful audits of Fortune 500 corporations, government agencies, health care departments, financial institutions, and technology firms throughout the United States. Such a broad experience will allow Qualysec to know sector-specific risks and compliance needs, which generic assessment providers are not always aware of.
Advanced Tools and Methodologies –
Qualysec is an automated scanning system that uses manual testing to offer complete vulnerability identification and validation. Their testing methodology uses both authenticated and unauthenticated testing to simulate the different attack scenarios real threats might use.
Their testing approach incorporates:
- Static Application Security Testing (SAST) for source code analysis
- Dynamic Application Security Testing (DAST) for runtime vulnerability identification
- Interactive Application Security Testing (IAST) for comprehensive application assessment
- Software Composition Analysis (SCA) for open-source component evaluation
- Infrastructure as Code (IaC) security scanning for cloud deployments
Actionable Reporting and Remediation Guidance –
It is not just the case that, in its assessment reports, Qualysec merely identifies vulnerabilities. They offer comprehensive remediation instructions, risk prioritisation according to the business environment, and step-by-step instructions on how to go about the identified problems. They consist of executive summaries of the reports to the stakeholders of the business and technical summaries to the implementation teams.
Each vulnerability report includes:
- Risk rating based on CVSS scores and business impact
- Proof of concept demonstrations showing exploitation potential
- Remediation steps with specific configuration changes or code fixes
- Timeline recommendations for addressing different risk levels
- Compliance mapping showing how fixes address regulatory requirements
Schedule a Free Consultation with Qualysec Now to discuss your organization’s security assessment needs and discover how their expertise can strengthen your cybersecurity posture.
Talk to our Cybersecurity Expert to discuss your specific needs and how we can help your business.
Conclusion
IT security assessments have become more of a matter of voluntary compliance with mandatory business requirements within American organizations. As cyber threats increase and regulatory demands grow, systematic security assessment can be a source of successful risk management and protection of business.
The evaluation procedure must be well planned, thorough, and long-lasting in terms of correction and enhancement. Organizations that look at security assessment as a one-off process instead of a program fail to take the opportunity to develop a resilient security posture that can be adjusted to changing threats.
The key to success is to choose qualified assessment providers that are familiar with the technical details of security measures and business operational issues. The investment in professional information security assessment services is yielding: minimized risk of breach, better posture of compliance, and increased confidence among stakeholders.
Download our comprehensive pentest report template to learn what thorough security assessments should include and how to document findings for maximum business value.
Latest Penetration Testing Report

One should bear in mind that security assessment is a process and not an aim. Common and continuous improvement and proactive threat management keep organizations on par with the new and increasingly sophisticated digital threat environment.
Talk with Our Security Experts to create a tailored security assessment plan that fits your business needs and risk level.
FAQ
1. What steps should businesses follow to conduct an IT security assessment?
To initiate an IT security assessment, businesses must make certain that they identify a clear scope and objectives, and then they should conduct an extensive asset inventory and classification. This would be followed by the threat and vulnerability identification, security control assessment, and recording of the findings with relevant risk rating. Lastly, organizations should come up with priority-based remediation roadmaps and create ongoing monitoring procedures to ensure the sustained security enhancement.
2. Which areas of IT infrastructure are most critical to assess?
Key points to consider in terms of information security assessment are network security infrastructure, data security safeguards and data security privacy, identity and access control systems, and incident response capabilities. Also, enterprise IT risk assessment needs to consider the relationship with vendors and other third-party providers, the setup of the cloud platforms, handling of the mobile devices, and their alignment with the applicable regulatory frameworks based on your geographical location and industry.
3. How can assessment results be effectively acted upon to reduce risk?
Organizations can also translate the outcomes of cybersecurity assessment checklists into mitigation by prioritizing the remediation regarding the business consequences and probability of the threat occurrence, creating extensive roadmaps with a timeline, and assigning tasks and schedules. The attributes of success include carrying out the process of continuous monitoring and validation, quantifying the progress, regularly reporting the improvements to the stakeholders, and staying on track with technical fixes and process improvements.



















































































































































































































































































































































































































































































































































































































































































































0 Comments