Automated Vulnerability Assessment and Penetration Testing (hereinafter referred to as the Automated VAPT) is a specialised cybersecurity approach to identify, assess, and mitigate vulnerabilities in web applications through automated vulnerability scanning solutions, tools and techniques.
In the last year, the world lost 4.4 million USD due to a data breach. In the USA alone, the law enforcement authorities reported $16 billion in 2024. Some reports also estimate that companies in the U.S. lose between $500 billion and $1 trillion annually due to downtime caused by cyberattacks.
Currently, traditional vulnerability assessments and penetration tests are no longer sufficient to address modern cyberattack surfaces that change daily due to cloud adoption, DevOps practices, and third-party integrations. Automated VAPT in such cases enables organisations to continuously identify, assess, and remediate security vulnerabilities across networks, applications, APIs, and cloud environments with minimal intervention by manual testing.
In this article, you will understand what automated VAPT is, its benefits, why there is a shift from manual to automated VAPT, its limitations, and what is the right way.
What is Automated VAPT?
Automated VAPT is a systematic approach that uses automated penetration testing tools and methodologies. It identifies, analyses, and exploits security weaknesses in systems, networks, and applications. The process combines Vulnerability Assessment (VA) and Penetration Testing (PT). It performs security evaluations while reducing manual intervention. It provides detailed insights into an organisation’s cybersecurity posture through vulnerability scanning automation.
How does Automated VAPT Work?
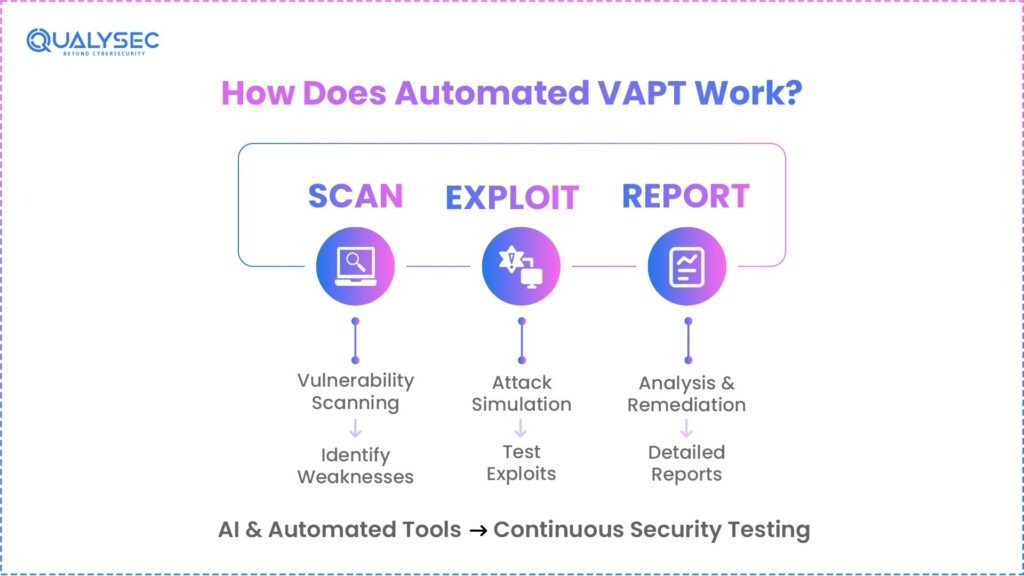
Automated VAPT functions through a systematic, multi-stage process that is designed specifically to identify, assess, and mitigate security vulnerabilities. In simple terms, automated security testing tools and AI work on patterns faster and cover more than traditional manual methods. The process is:
- Vulnerability Scanning Automation: Automated VAPT solutions are used to scan networks, systems, and applications to find known security issues, mistakes in the organisation cybersecurity setup, and itsweaknesses. These tools can run different scans, such as network, malware, mobile device, and compliance scans. In this step, important details about the environment are collected, including IP addresses, DNS names, MAC addresses, operating systems, and open ports with the services running on them. The identified vulnerabilities are then classified and prioritised on the basis of their severity.
- Exploitation and Attack Simulation: Once vulnerabilities are identified, Exploitation and Attack Simulation are carried out. During this phase, automated penetration testing tools simulate real-world attack scenarios, check whether these weaknesses can be exploited and understand the possible impact if an attack is successful using continuous VAPT.
- Reporting and Remediation: After the scanning and exploitation attempts are completed, automated security testing tools generate detailed reports. These reports are a summary of the findings and the results of the attack attempts, to help organisations understand the current position in providing cybersecurity for the data. The report also helps in prioritising remediation efforts and allocating resources effectively.
Benefits of Automated VAPT
Automated VAPT solutions are crucial in the United States of America. Cyber threats are rapidly escalating across industries. Security breaches cause significant financial and reputational damage. Manual security testing methods have inherent limitations.
1. Efficient and cost-effective:
Automated VAPT makes automated security testing faster. It scans systems, networks, and applications to find known vulnerabilities, configuration errors, and weaknesses. This process takes less time and costs less than manual penetration testing.
2. Proactive in Vulnerability Identification:
Automated VAPT helps businesses find and fix security weaknesses before attacks and gain a potential advantage over the attackers. Even a small vulnerability can cause serious problems if it is not fixed. Automated penetrating testing tools run different types of scans to give a clear view of possible weak points across the system.
3. Able to provide continuous security assessment:
Cyber threats are everywhere now, and they demand an ongoing process for cybersecurity. Automated VAPT provides continuous VAPT and monitoring, making it an essential part of maintaining a cyber-threat-proof system.
4. Automated Red Teaming:
Automated VAPT supports automated red teaming by reducing the time and manpower needed for manual testing. It allows U.S. businesses to simulate complex, real-world cyberattacks to identify vulnerabilities. This approach also helps organizations test their incident response capabilities in a more efficient way using vulnerability scanning automation.
5. Large companies and complex IT Infrastructures:
Organizations with large networks, many applications, and cloud-based systems can benefit greatly from automated VAPT solutions. Manual testing in such cases is often difficult because it takes a lot of time, costs more, and is hard to manage at such a large scale. Automated penetration testing tools can quickly scan systems to find known vulnerabilities, configuration issues, and security weaknesses.
6. Compliance Requirement:
In the United States, 66% of companies report that compliance mandates directly influence their cybersecurity budgets (e.g., PCI DSS, HIPAA, SOC-2), and about 80% of organisations cited regulatory requirements as a key reason for using advanced testing tools such as AI-assisted penetration testing to satisfy audit criteria. HIPAA require regular vulnerability assessments and documented technical safeguards, PCI DSS mandates quarterly network scans and penetration tests to validate security controls around cardholder data. By implementing automated VAPT solutions, organisations can generate evidence of vulnerability discovery, severity ratings, and remediation tracking.
7. Defence against advanced and AI-Driven threats:
According to industry reports, 59% of security teams find that the pace of AI adoption outstrips their ability to secure and test these systems effectively. Modern automated penetration testing tools, with the help of AI, find security risks more effectively. They continuously scan systems and combine results from different environments. Automated penetration testing tools now use machine learning to simulate possible attacks. They also help decide which risks are most important. This allows organizations in the U.S. to move from occasional testing to ongoing and proactive security checks.
Limitations of Automated VAPT Tools
Automated VAPT solutions offer significant advantages in efficiency and coverage. Despite these benefits, they have certain limitations. These limitations impact their overall effectiveness and generalizability.
1. Defined Test Scope:
This is a primary limitation that can significantly affect the length and breadth of vulnerability detection. A restricted scope of vulnerability detection may overlook important vulnerabilities, especially those that exist in less obvious attack vectors or in newly deployed system components. Similarly, an overly broad scope can complicate procedures, deplete resources, and lead to an abundance of false positive results.
2. Generalizability of Deep Reinforcement Learning (DRL) algorithms:
Many current DRL-based tools used in automated penetration testing tools that are tested only on a small number of systems that were also used for training. This raises concerns about how well they will work in new or unfamiliar environments. Because these tools are not tested on a wide range of different systems, they may struggle to adapt to changes in network structure, operating systems, or applications.
3. Adversarial nature of cybersecurity:
The performance of a continuous VAPT tool depends on the strength and sophistication of the defence system during testing. Similarly, the performance of a defensive tool depends on the type of attacker it is tested against. Because of this, test results can vary widely based on the characteristics of the attacker or defender used in the evaluation. This challenge is especially important for AI-based cybersecurity tools, which must be tested against realistic and dynamic opponents to accurately measure their effectiveness.
4. The “black-box” nature of deep learning models:
The “black-box” nature of some deep learning models used in advanced VAPT tools presents a limitation. This is especially true for tasks like Advanced Persistent Threat detection. The decision-making process is opaque in nature. This makes it difficult for security analysts to understand why a vulnerability was flagged. It also complicates understanding why a specific attack path was chosen.
Learn: AI-Based Application Penetration Testing and Its Importance
Why did Organisations shift from Manual to Automated VAPT?
In the United States of America, organisations are increasingly shifting from purely manual vulnerability assessment and penetration testing to automated VAPT due to an increase in the complexity of cyber attacks and digitalisation.
For a long time, organisations opted for manual wap for identifying Complex and high-impact security flaws, which is inherently limited by time, cost, and scalability. As we know, in modern times, cloud and DevOps environments change frequently, and periodic manual testing leaves long gaps during which newly introduced vulnerabilities sometimes remain undetected.
Furthermore, as organisations expand across multi-cloud environments, microservices, and distributed teams, it becomes impractical to manually test every application, API, and infrastructure component at the same frequency, often forcing security teams to prioritise only high-risk systems.
The result is lower-visibility assets insufficiently tested. These limitations have increased the adoption of automated VAPT across many organisations in the USA. Automated security testing enables organisations to adopt automated security testing for continuous vulnerability detection. When issues are detected early, automated VAPT helps reduce exposure windows and supports regulatory expectations.
As for the limitations of automated penetration testing tools, it is pertinent to note that iis not a complete replacement for manual penetration testing. While vulnerability scanning automation excels at speed and scale, manual testing helps to identify complex business logic flaws, chained attack paths, and context-specific exploitation scenarios.
Is Automated VAPT Alone Enough to Ensure Complete Cybersecurity?
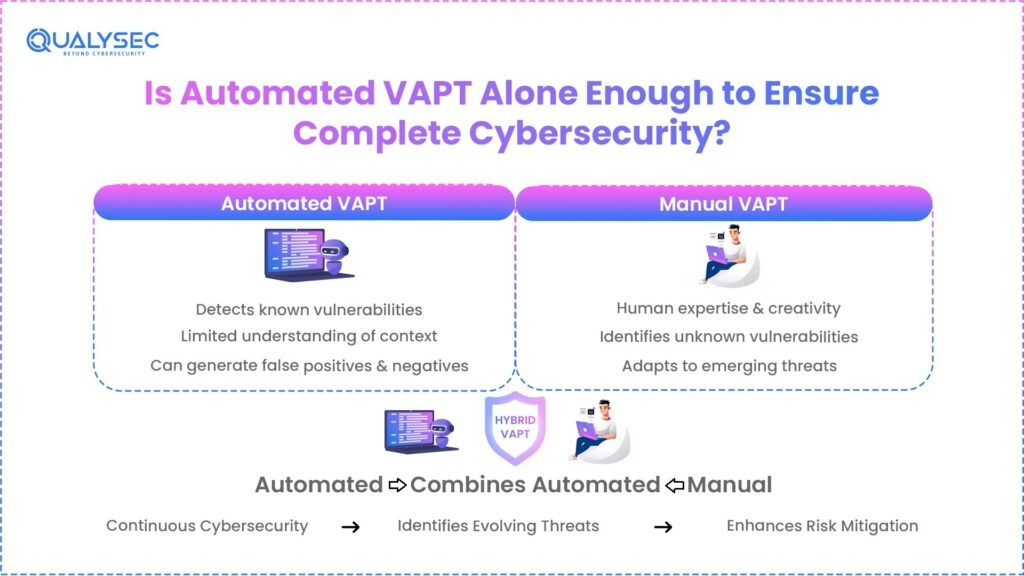
No, automated VAPT alone is not enough for complete cybersecurity. Businesses need to follow hybrid solutions in vulnerability assessment and penetration testing. By hybrid VAPT, we mean applying both manual and automated VAPT solutions to enhance cybersecurity and mitigate risks.
Cybersecurity is no longer a one-time task. It’s a continuous process. Automated VAPT solutions enable organisations to conduct regular automated security testing, but combining automated efforts with human expertise and skill to detect and understand the findings will further help them identify new vulnerabilities and respond to evolving attack methods. It is important to note that:
- Automated security testing tools are designed to detect known issues using predefined patterns, and they often fail to interpret the unique logic or context of an application or workflow.
- Automated scanners sometimes generate false positives, which can waste security team time, and false negatives, where actual vulnerabilities are not reported.
- Tools used in automated VAPT follow fixed rules or signatures and cannot adapt to emerging attack techniques or unexpected system behaviours. Automated penetration tools cannot replicate the human brain and creativity to understand the kind of attacks that have no discernible pattern.
- Many compliance frameworks, including PCI DSS, explicitly mandate manual penetration tests conducted by qualified testers only, and in this case, automation does not satisfy all regulatory audit expectations if it is used in isolation.
Thus, this clearly shows that merely depending on automated tools for your organization’s security isn’t enough. You must take human help to verify each vulnerability and search for more that software/tools have missed.
Also Learn: Automated Compliance Tools Vs Penetration Testing
Qualysec: A Hybrid VAPT Partner Combining Automated and Manual Testing
At Qualysec, we believe that effective cybersecurity cannot rely on a single approach, whether automated or manual. Modern cyberattacks are constantly evolving, which makes it essential to secure systems through a combination of automated VAPT solutions and manual testing. We provide:
- Automated Vulnerability Assessment and Penetration Testing (VAPT): We provide continuous VAPT, scalable security testing across web applications, APIs, cloud environments, networks, and infrastructure to identify vulnerabilities early and reduce exposure windows.
- Manual penetration testing: Our expert-led testing simulates real-world attack scenarios to uncover complex business logic flaws, chained exploits, and privilege escalation risks that automated penetration testing tools may miss.
- Risk-Based security assessments: We prioritise vulnerabilities based on their impact on the business, exploitability, and regulatory requirements.
- Compliance support: Our automated security testing aligns with NIST CSF, ISO 27001, SOC 2, PCI DSS, HIPAA, and GDPR to help organisations meet regulatory requirements.
- Report analysis: Our detailed assessment reports provide clear findings, risk prioritisation, and actionable recommendations that help organisations to prepare for any potential security incidents.
- DevSecOps and CI/CD Integration Support: Qualysec provides custom API/webhook support for Jira, Slack, ServiceNow, and generic DevOps pipelines for continuous VAPT integration.
Conclusion
As systems, applications, and cloud environments are changing, organisations need visibility into their security risks. Automated VAPT helps to identify vulnerabilities at an early stage, supports continuous monitoring, and reduces the time attackers have to exploit weaknesses. At the same time, automated penetration tools have limits. They cannot fully understand application logic or simulate complex attack behaviour. Manual penetration testing remains essential for identifying bigger risks and validating real-world security impact. The most effective approach is a combination of both automated security testing and manual VAPT. Together, they provide 100% vulnerability assessment and stronger protection that organisations can use to improve security and meet the compliance requirements.
FAQs
1. Can Automated VAPT replace manual penetration testing?
No, the automated VAPT cannot completely replace manual penetration testing. Automated tools are good at finding known vulnerabilities and common attack patterns. However, manual testing is still needed to detect complex issues, such as business logic flaws and advanced attack techniques that require human judgment.
2. How does Automated VAPT help with regulatory compliance in the United States?
Automated VAPT helps organizations meet U.S. compliance requirements by continuously checking systems for vulnerabilities. It also generates detailed reports that can be used for audits. This supports compliance with standards such as HIPAA, PCI DSS, and SOC 2.
3. How many times should Automated VAPT be performed?
Automated VAPT should be performed regularly or continuously. It is especially important after system updates. Code changes, infrastructure changes, or new deployments can introduce new security risks.
4. What challenges do organizations face when implementing Automated VAPT?
Organizations may face challenges in setting the right testing scope and handling false positives. Accurately identifying assets in cloud environments can be difficult. Integrating automated penetration testing tools with existing security systems and DevSecOps workflows also requires careful planning.





















































































































































































































































































































































































































































































































































































































































































































0 Comments