Insurance cybersecurity has emerged as a major concern for organisations worldwide due to the increasing number of cyber threats. Additionally, insurance companies store a significant amount of sensitive information on policyholders, making them attractive targets for cybercriminals.
Moreover, the trend of the digital transformation in the insurance industry has opened new areas that are prone to exploitation and, therefore, need well-developed protection strategies. Moreover, the area of insurance cybersecurity does not only refer to technological solutions but also regards holistic compliance frameworks and risk management approaches.
In the modern digital environment, the security of customer information and the ability to keep up with regulatory standards are key factors in establishing trust and ensuring the survival of a business. Consequently, learning about cybersecurity as an insurance firm has become a business necessity.
What Are the Major Cybersecurity Threats Facing Insurance Companies Today?
The insurance industry is now exposed to advanced cybercrimes that have the potential to interrupt business processes as well as disrupt policyholders. Therefore, these threats should be studied, and awareness will be the initial move towards the creation of effective defensive strategies.
1. Ransomware Attacks
Ransomware has become one of the most destructive threats to insurance companies. In particular, such attacks are used to encrypt important information, and the information is released only upon payment. In addition, recent statistics reveal that insurance companies are more vulnerable to ransomware attacks than other sectors. Moreover, ransomware attack on the insurance industry has an average cost of over 5 million dollars in terms of downtime and the cost of recovery.
Protect your organization from rising cyber threats with our Ransomware Penetration Testing guide.
2. Data Breaches and Information Theft
Data protection in the insurance sector involves being vigilant about breach attempts at all times. Moreover, cybercriminals use insurance databases to rob people of their personal information, medical records, and money. After that, stolen information is usually sold in dark web markets or used for identity theft. Hence, the insurers need to install several layers of protection to avoid illegal access.
Discover the Top Data Security Solutions in 2026.
3. Phishing and Social Engineering
Insurance employees are still seriously vulnerable to phishing attacks. On the same note, social engineering tricks deceive employees into credential disclosure or malware download. Consequently, a single hacked account can give hackers entry into whole systems. Therefore, employee training is an important element of threats to insurance cybersecurity.
Key Threat Statistics
| Threat Type | Impact on Insurance Sector | Average Recovery Cost |
| Ransomware | 65% increase in attacks (2024) | $5.2 million |
| Data Breaches | 40% of incidents involve customer data | $4.5 million |
| Phishing | 85% of organizations experience attempts | $1.8 million |
| Insider Threats | 30% of security incidents | $2.3 million |
Read our latest article on Data Breach Prevention: How to Protect Your Business from Costly Cyber Incidents.
How Can Insurance Companies Implement Effective Data Protection Strategies?
The reduction of large-scale data protection in the insurance sector means multi-layered actions involving technology, policies, and people.
1. Encryption and Data Security Measures
Encryption is a basic defence mechanism for safeguarding sensitive information. In particular, the insurance companies have to encrypt their data at rest and in transit. Furthermore, higher levels of encryption standards will ensure that, in case of any data interception, the data will be unreadable without the necessary decryption keys. Moreover, end-to-end encryption helps to ensure that the communications and policy documents of the customers are not accessed by unauthorised users.
Cybersecurity for insurance companies involves the following necessary encryption measures:
- Data-at-rest encryption for databases containing policyholder information
- Transport layer security (TLS) for all web communications and API transactions
- Field-level encryption for particularly sensitive data like social security numbers
- Encryption key management systems to control access and rotation schedules
- Database encryption with role-based access controls
- Email encryption for sensitive correspondence with clients and partners
2. Multi-Factor Authentication (MFA)
In addition to passwords, MFA introduces important security controls, which lessen the risk of breaches to a great extent. Moreover, the presence of several verification factors contributes to the unauthorised access being exponentially harder. Therefore, despite compromised passwords, accounts are secured by means of extra authentication.
3. Network Security and Firewalls
Insurance cybersecurity defence systems are based on robust network architecture. On the same note, next-generation firewalls ensure threat detection and intelligent traffic filtering. Moreover, intrusion detection systems will watch the activities of the network to observe suspicious behaviour and take automatic action related to the possible dangers.
4. Regular Security Audits and Assessments
The regular security assessments assist in the detection of vulnerabilities before they can be exploited by attackers. As such, quarterly security evaluations and an annual overall audit should be performed by the insurance companies. Besides, third-party security analysis offers independent information on the security state and compliance condition.
As it was reported by the research conducted on the topic of cybersecurity solutions to be used by the insurance company, such protective measures can greatly decrease the risk of data breach and preserve the trust of the customers.
5. Cloud Security Best Practices
Storing of data and processing in the cloud is currently being used by many insurers. Nevertheless, cloud settings entail particular security settings and surveillance tools. Then, insurers are required to make sure that cloud providers comply with industry security standards and requirements. Also, the use of cloud access security brokers (CASB) is useful to track and manage the usage of cloud applications. Check our Cloud Security Services →
Why Is Penetration Testing Essential for Insurance Cybersecurity?
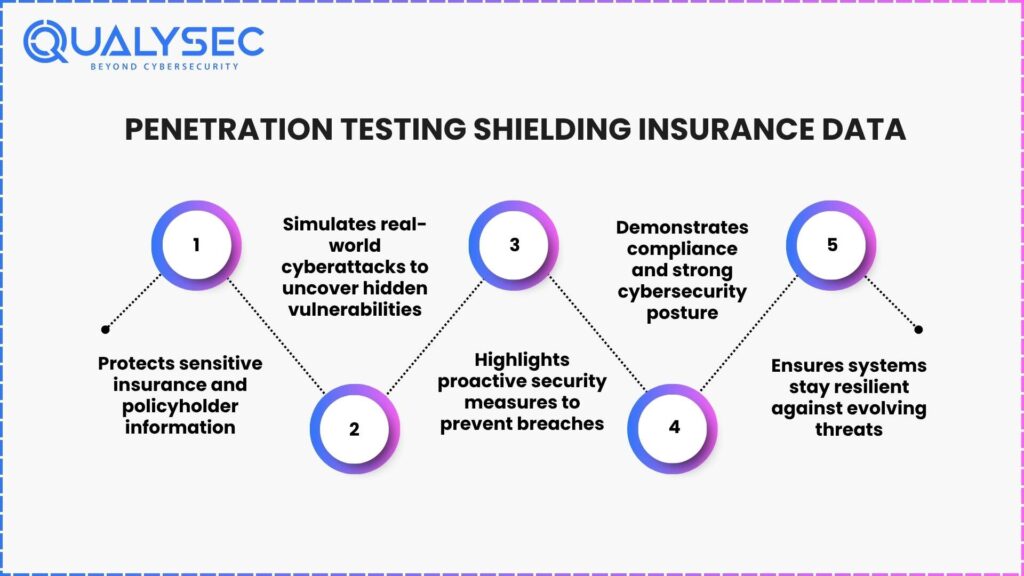
Insurance penetration testing also gives important clues about the security vulnerability through real-world scenarios of the attack. Moreover, such a proactive method can detect the weak points before they can be abused by bad actors.
1. Understanding Penetration Testing
Penetration testing is an activity in which authorised security personnel work to compromise insurance systems in the same manner that cybercriminals do. As a result, the process unveils security lapses, which may not be very visible during conventional tests. In addition, frequent penetration tests enable the insurers to keep up with the changing threat environments.
2. Types of Penetration Testing for Insurance Companies
Insurance penetration testing encompasses several specialized approaches:
- External network testing evaluates internet-facing systems and applications
- Internal network testing assesses security from within the organization’s perimeter
- Web application testing examines customer portals and online policy management systems
- Social engineering testing evaluates employee awareness and response to manipulation attempts
- Physical security testing assesses access controls and facility security measures
- Wireless network testing identifies vulnerabilities in Wi-Fi and mobile networks
3. Benefits of Regular Penetration Testing
Regular penetration testing delivers multiple advantages for insurance organizations. Specifically, it validates existing security controls and identifies configuration errors. Additionally, testing results provide actionable insights for security improvement initiatives. Furthermore, documented penetration tests demonstrate due diligence to regulators and stakeholders.
Penetration Testing Frequency Recommendations
| Organization Size | Testing Frequency | Scope Focus |
| Small Insurers (< 500 employees) | Annually | Critical systems and customer portals |
| Medium Insurers (500-5000 employees) | Bi-annually | Comprehensive infrastructure testing |
| Large Insurers (5000+ employees) | Quarterly | All systems with continuous monitoring |
| After Major Changes | Immediately | Affected systems and integrations |
Get a Free Sample Pentest Report

What Compliance Standards Must Insurance Companies Follow?
Adherence is one of the foundations of insurance cybersecurity actions. Furthermore, there are several regulatory frameworks that govern the manner in which insurers should protect and handle their customers’ data.
1. Key Regulatory Requirements
Insurance firms must navigate complex compliance environments regionally and jurisdictionally. As such, it is essential to be aware of relevant laws to avoid fines and continue operating.
GDPR (General Data Protection Regulation)
For insurers operating within the European market or in other markets where they serve, compliance with the GDPR is required. In particular, GDPR concerns any organization that handles personal information of EU citizens and involves safe storage, legal use of data, and entitlement to its transferability, with breaches that could amount to fines of up to EUR20 million or 4% of annual revenues. Also, GDPR requires that notice of breach be presented within 72 hours after its identification.
Learn about: GDPR Penetration Testing
HIPAA (Health Insurance Portability and Accountability Act)
In the United States, health insurers should adhere to high standards of HIPAA. Moreover, HIPAA regulates the management and dissemination of health data in the US and stipulates that organisations should implement role-based access to sensitive medical claims that are sensitive. Violation may, in turn, lead to fines of up to $1.5 million per category of violation every year.
Read more on: HIPAA Penetration Testing
CCPA (California Consumer Privacy Act)
CCPA concerns the businesses that are located in California and forces companies to provide consumers with such rights as access, deletion, and opt-out of data selling. In addition, the insurance companies need to keep comprehensive information on the processes of data collection and processing.
Explore: Penetration Testing for CCPA Compliance
PCI DSS (Payment Card Industry Data Security Standard)
The PCI DSS stipulates that insurers that handle payment transactions should use robust encryption, network management, and access control in order to minimise fraud and breaches. Also, compliance with these security standards is checked every year.
Check out: What is PCI DSS Compliance? Key Requirements & Best Practices
2. SOC 2 Compliance for Insurance
SOC 2 compliance for insurance companies are required to comply with SOC 2 to show commitment to data security by undergoing independent audits. In particular, SOC 2 considers the control over security, its availability, processing integrity, confidentiality, and privacy. Additionally, the SOC 2 certification evaluation presupposes the adoption of extensive security policies and procedures.
SOC 2 Type I vs Type II
Type I of SOC 2 analyses the issue of whether security controls are appropriately designed at a certain time. On the other hand, SOC 2 Type II assesses the effectiveness of controls in the long-term operation, which is usually 6-12 months. Thus, Type II certification is beneficial as it gives more confidence to clients and partners.
Benefits of SOC 2 Compliance
Achieving SOC 2 compliance for insurance organisations brings about strong business benefits:
-
- Enhanced customer trust through demonstrated security commitments
-
- Competitive differentiation in security-conscious markets
-
- Streamlined vendor assessments, reducing partnership friction
-
- Improved security posture through continuous monitoring and improvement
-
- Regulatory alignment satisfying multiple compliance requirements simultaneously
-
- Risk mitigation through systematic security control implementation
3. NAIC Model Law and State Regulations
NAIC offers a model law to govern the data handling process of insurance companies, such as the protection of policyholder data, cybersecurity, and reporting of incidents in the US. Moreover, these model regulations have been embraced by or changed by many states to be enforced locally. As a result, the different state-level requirements can be followed and adhered to by insurers.
International Compliance Considerations
There is further regulatory complexity in global insurance operations. Similarly, various states implement various policies in the insurance sector in terms of data protection requirements. Thus, multinational insurers require multifaceted compliance packages that would cover different jurisdictions at the same time.
The research on data compliance management shows that non-observance may result in severe fines, operational obstacles, and negative reputation, whereas non-observance of compliance delays the claims processing, undermines customer loyalty, and influences business development.
Compliance Management Best Practices
|
Compliance Area |
Implementation Strategy |
Monitoring Frequency |
|
Data Privacy |
Privacy impact assessments and consent management |
Quarterly |
|
Access Controls |
Role-based permissions and regular access reviews |
Monthly |
|
Data Retention |
Automated retention policies and secure deletion |
Continuous |
|
Breach Response |
Incident response plans and notification procedures |
Annual testing |
|
Audit Trails |
Comprehensive logging and monitoring systems |
Real-time |
Explore: Data Security Compliance: A Step-by-Step Guide
Why Choose Qualysec for Insurance Cybersecurity Solutions in the USA and Globally?
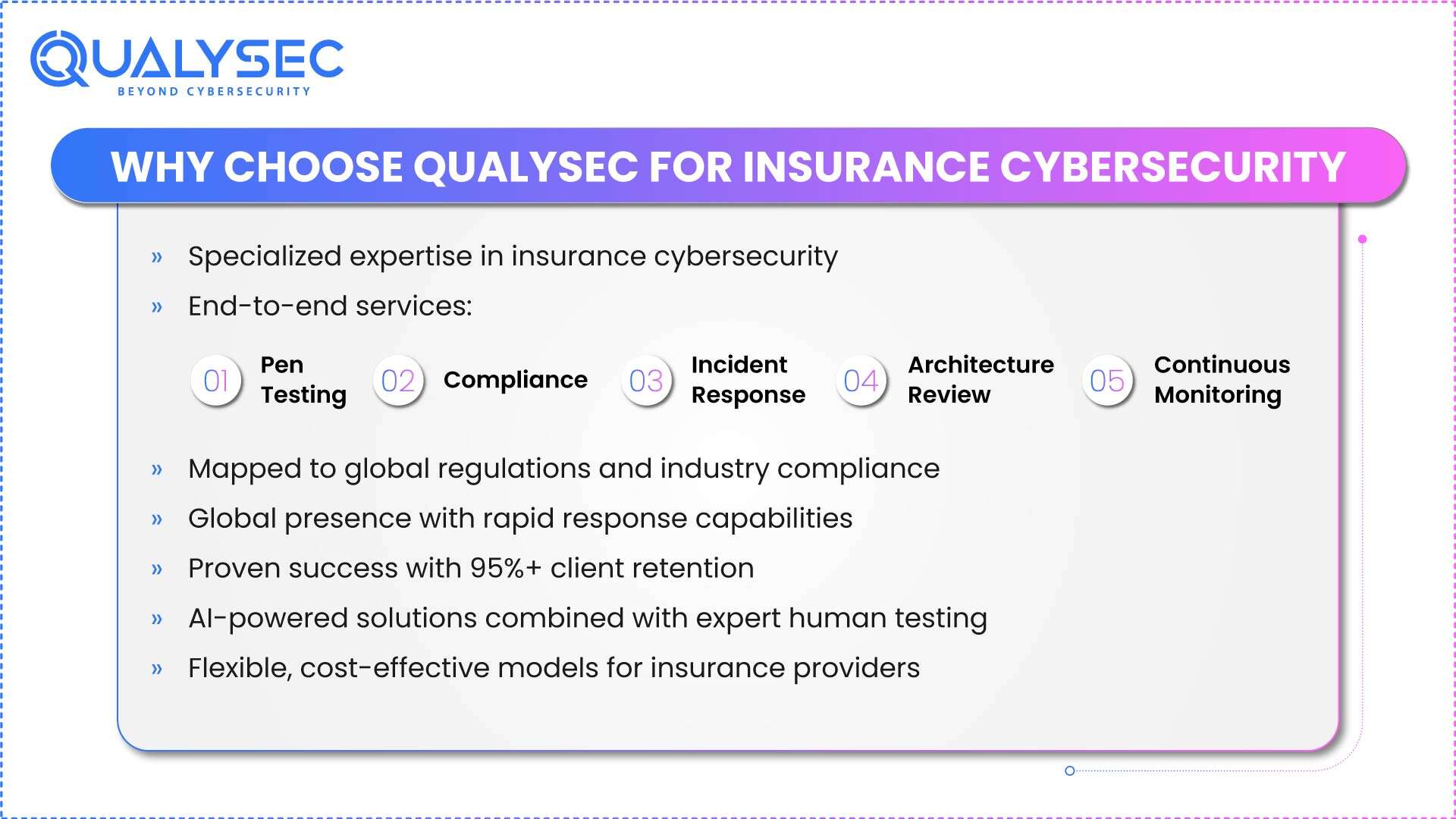
In terms of safeguarding the data of policyholders and adhering to the regulations, the appropriate cybersecurity provider is the key. In addition, Qualysec is the best solution for insurance companies that need complete security solutions.
Industry-Leading Expertise in Insurance Cybersecurity
Qualysec is a specialist in insurance cybersecurity that is well aware of the challenges and needs related to the sector. Besides, they have a team of certified security professionals who have vast years of experience in securing insurance organisations in different parts of the world. Moreover, Qualysec keeps up with the new knowledge of emerging threats and regulations that are relevant to the insurance industry.
Comprehensive Service Offerings
Qualysec delivers end-to-end security solutions tailored specifically for insurance companies:
-
- Advanced Penetration Testing Services: Qualysec insurance penetration testing services make use of highly sophisticated approaches to find vulnerabilities in all systems of insurance. In particular, their testing procedures include web applications, mobile apps, APIs, cloud, and network architecture. Moreover, they offer elaborate remediation advice in ranking of the risk severity.
-
- Compliance Assessment and Management: Proceeding to know that SOC 2 compliance to insurance and other regulatory structures can be demanding, Qualysec provides full compliance services. Their professionals, in turn, make a gap analysis, a remediation roadmap, and continuous monitoring compliance. Furthermore, they help prepare the audits and documentation needed.
-
- Security Architecture Review: Qualysec reviews the current security controls and infrastructure to identify areas of improvement. Also, they develop secure security designs that provide balanced security protection and operational efficiency. Thus, the insurers can put security measures in place that facilitate, not cripple, business processes.
-
- Incident Response and Recovery: Fast response is imperative in case of security incidents. Therefore, Qualysec offers 24/7 incident response services and has teams of qualified personnel who will contain breaches and minimise damages. Moreover, they perform post-incident analysis to make defences against future attacks stronger.
-
- Continuous Security Monitoring: Qualysec provides continuous security checks services, unlike point-in-time assessments. Likewise, they have a security operations centre (SOC) that allows them to detect and respond to threats in real time. Also, frequent security reports are used to update the stakeholders on the security posture.
Why Qualysec Excels for Global Insurance Organizations
-
- Strategic Locations and Global Reach: Qualysec has its headquarters and a good presence in the USA as well as in other parts of the world, among insurance companies. Further, their decentralised team organisation allows quick response irrespective of physical location. Moreover, they are familiar with compliance differences and cultural differences in the region.
-
- Proven Track Record: Qualysec has already managed to ensure a wide range of insurance organisations against cyber attacks. Moreover, their client retention rates are beyond 95 per cent, portraying steady value delivery. Also, case studies are used to present quantifiable security gains and compliance successes.
-
- Cutting-Edge Technology Integration: The security solutions provided by Qualysec become more efficient and timely in their usage since they are based on artificial intelligence and machine learning to extract and identify threats. Besides, they use automated scanning tools coupled with manual analysis by experts to cover all the areas. Thus, the insurers gain access to technological effectiveness and human skills.
-
- Cost-Effective Solutions: The knowledge of financial limitations enables Qualysec’s flexible funding engagement models to provide maximum value. Thereafter, their risk-based strategy identifies the key security investments to make effectively in the allocation of resources. Moreover, the cost of preventing breaches is less than that of recovering from breaches.
-
- Industry Recognition: Qualysec has been certified with CREST, OSCP, CEH, and CISSP, which is an indication that the company is professionally dedicated. Moreover, they are proactive participants in cybersecurity research and forums in the industry. Hence, clients are in the position of having state-of-the-art security expertise and practice.
See Why Companies Worldwide Trust Us

Getting Started with Qualysec
Qualysec makes it easy to start your insurance cybersecurity improvement journey. First, book a complimentary consultation to discuss your unique security issues and compliance needs. Qualysec then carries out initial security assessments so as to have a baseline knowledge. Then, they create tailored security roadmaps to fit your business goals and tolerance of risks.
Take Action Now: Don’t wait for a security incident to prioritise cybersecurity for insurance companies. Instead, contact Qualysec today for your free security consultation. Furthermore, download their comprehensive penetration testing guide from Qualysec’s resources page to understand how testing can strengthen your defences.
Visit Qualysec’s website and find out more about the specialised insurance cybersecurity solutions, and get to know the detailed case studies that will show the experience they have. In addition, their security specialists will be willing to negotiate on how they can assist you in securing your policyholder data and meeting compliance goals.
Speak directly with Qualysec’s certified professionals to identify vulnerabilities before attackers do.
Conclusion
Insurance cybersecurity is a vital business continuity investment and a customer trust investment. Besides, the dynamic nature of the threat environment means that insurance firms must adopt all-around security controls and ensure regulatory compliance. Moreover, a combination of technologies and strategic alliances increases the protection capabilities a great deal.
In this guide, we have discussed key cyber threats to insurers, key data protection measures, the need to test insurance penetration, and key compliance frameworks, such as SOC 2 compliance of insurance organisations. Moreover, the choice of the work of skilled cybersecurity partners such as Qualysec allows achieving maturity in security in a short period and optimising investments in resources.
It is high time that data protection in the insurance sector is enhanced before the occurrence of another cyber attack. In this way, the insurance companies need to emphasise security programs and invest the necessary resources to secure the information of policyholders. Thereafter, a strong cybersecurity system among insurance companies provides competitive benefits in the form of improved customer trust and operational stability.
Ready to Strengthen Your Insurance Cybersecurity? Schedule your free consultation with Qualysec today to assess your current security posture and develop a customised protection strategy. Moreover, explore Qualysec’s comprehensive solutions to get more information on the best practices in cybersecurity in the insurance industry. It is not worth exposing your policyholder data to risks, and it is high time you took active measures to ensure full security.
Frequently Asked Questions (FAQs)
1. Why is cybersecurity important for insurance companies?
Insurance cybersecurity ensures that sensitive policyholder information is not subjected to cyber threats and attacks. Also, high-quality security will help to gain customer confidence and avoid expensive regulatory fines and negative publicity.
2. How can insurers prevent data breaches?
The measures taken by insurers to prevent data breaches are encryption, multi-factor identification, and frequent security audits. In addition, insurance companies have cybersecurity, which involves training of employees and detailed incident response strategies.
3. Which compliance standards apply to the insurance industry?
The most important compliance regulations are GDPR, HIPAA, CCPA, PCI DSS, and NAIC regulations. Moreover, insurance companies have to comply with SOC 2, which proves their dedication to data security by means of an independent audit.
4. How can penetration testing improve cybersecurity for insurers?
Insurance penetration testing refers to the vulnerability identification process in which actual-world attacks are simulated before the criminal can use them. Then, the results of testing can be used to give practical suggestions on how to enhance data safety in the insurance industry.



















































































































































































































































































































































































































































































































































































































































































































0 Comments