Do you care about securing the financial information of your customers and, at the same time, ensuring that you remain within the federal regulations? GLBA risk assessment is a very important exercise that financial institutions should conduct to ensure that they protect sensitive information and that they comply with the regulations. Additionally, a thorough GLBA assessment has never been so important to comprehend and put in practice as cyber threats are rapidly changing in 2025. The guide will take you through all that you should know about the effective GLBA risk assessment requirements, the implementations of the GLBA Safeguards Rule and the practices of effective GLBA information security risk assessment.
What is GLBA Risk Assessment and Why Does It Matter in 2025?
Imagine a GLBA risk assessment as a type of security exam of the data practices of your financial institution. You are essentially scouting the entire corners of your organization to identify weak areas through which customer information may be compromised. The process examines whether your systems hold data in confidence, whether data remains accurate and unchanged and whether people can access data in a position to access the required data when they need to.
The Gramm-Leach-Bliley Act was enacted way back in 1999 under the Financial Services Modernisation Act. This federal law lays down the principles within which the US financial institutions should treat personal customer information.
Explore more on security compliance for financial institutions to ensure alignment with GLBA and related federal requirements.
Understanding the Legal Framework
The structure of the GLBA assessment has three important elements:
The Financial Privacy Rule regulates the gathering and sharing of the private banking data of customers. Financial institutions should therefore notify the customers of their information-sharing policies and practices. This regulation gives the customers the chance to decide not to participate in some data-sharing agreements.
The Safeguards Rule requires financial institutions to develop elaborate security programmes. That is why it is necessary to have administrative, technical and physical measures in place to prevent infiltration or a loss of information.
The Pretexting Provisions directly deal with the act of falsely presenting oneself in order to gain access to the personal information of the individual. GLBA, therefore, outlaws such a misleading act in an effort to eliminate inaccessible sensitive data.
Current Threat Landscape in the USA
The American financial institutions are struggling against more advanced cyber threats in 2025. Namely, ransomware attacks, phishing attacks, and data breaches have been on the rise. Most current cybersecurity news articles indicate that the financial services continue to be one of the most targeted industries. Thus, the routine performance of GLBA information security risk assessment procedures will enable organizations to be ahead of the new threats.
Talk with Our Experts at Qualysec to understand how current cyber threats impact your organization’s compliance posture.
Who should be in compliance with GLBA Risk Assessment Requirements?
To check the compliance with the GLBA risk assessment requirement, the information of organization with which organizations are going for assessment. This is also limited to the traditional banks.
Covered Financial Institutions
The following entities must comply:
- Banks and credit unions: The banks and credit unions deal with customer deposits and financial transactions daily.
- Insurance companies: The insurance companies that provide the life, health, or property insurance products should comply.
- Investment companies and securities firms:Investment companies and securities firms that deal with investment portfolios and securities trading are also covered under GLBA.
- Mortgage lenders and brokers: Borrowers would like mortgage product providers to safeguard the data of their borrowers.
- Tax preparation services: Taxes are a business that deals with tax submissions and financial statements that need compliance.
- Credit counselling services: They offer counselling services related to debt management, and therefore, the organisations are required to protect the data of clients.
Non-Financial Businesses Affected
Interestingly, non-financial businesses are not exempt because there are also GLBA assessment obligations. In particular, some of this customer financial information provided to the covered institutions by the companies may require the companies to take the right precautions. Therefore, the use of technology service providers, data processors and third-party vendors may be under the jurisdiction of GLBA.
Explore penetration testing services for the fintech industry to address industry-specific vulnerabilities.
How Do You Conduct a Comprehensive GLBA Risk Assessment?
A comprehensive GLBA information security risk assessment needs to be planned and carried out systematically. Additionally, it is a methodical process, and nothing can go astray.
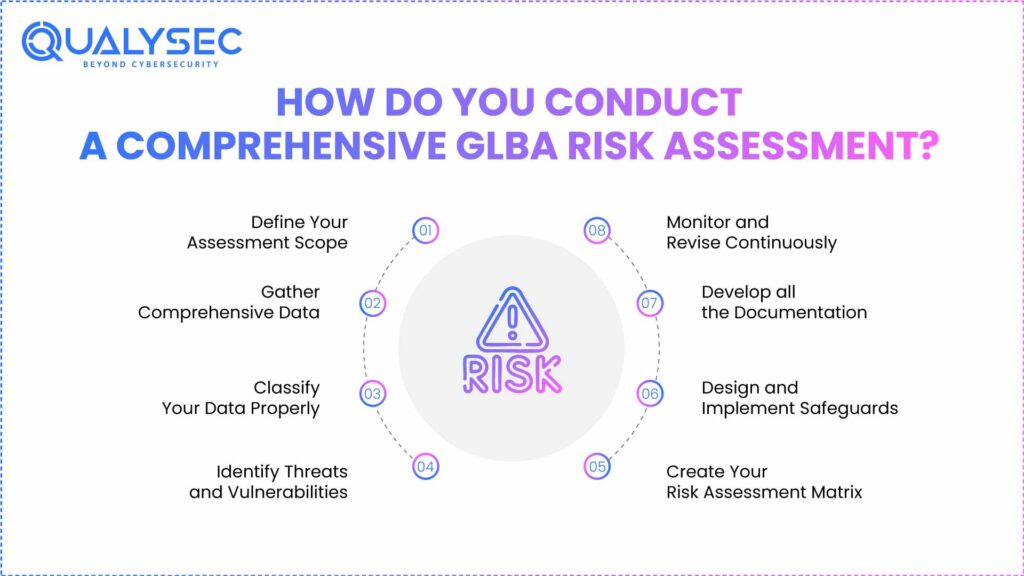
Step 1: Define Your Assessment Scope
The initial thing to do is to identify what you are judging. Thus, you need to locate every individual, business unit, asset and vendor dealing with customer financial information.
Key actions include:
- Map customer financial data: Find the location of information storage, processing, and transmission between systems, cloud platforms, and third-party vendors.
- List all authorized users: Name all the individuals who have access to sensitive information such as employees, partners and service providers.
- Focus on GLBA-relevant systems: The evaluation should be limited to departments, IT systems, and vendors that process consumer financial data.
Absence of guidelines would lead to teams wasting time on evaluating systems that do not touch on sensitive data. Moreover, it is essential to keep an updated IT asset inventory to do scoping.
Step 2: Gather Comprehensive Data
True to its name, your GLBA risk assessment is based on data collection. Also, this step involves cooperation between several departments.
Start by listing all the systems that store, process or channel information about customers. Later, examine available records, policies and procedures pertaining to data privacy and security. Collect and organise this information in standardised templates.
Step 3: Classify Your Data Properly
Classification of data assists in setting priorities for protection. As a result, classify the customer data according to their sensitivity and possible effect.
Classification categories include:
- Non-public personal information (NPPI): Social security number, account number and personal identifiers.
- Financial data: Credit reports, history of transactions and income.
- Authentication credentials: Passwords, security questions, and access tokens.
Under each category assign risk levels according to the harm that could be caused by unauthorized access or disclosure. Thus, the data that is of the high sensitivity is provided with the best protection measures.
Step 4: Identify Threats and Vulnerabilities
One aspect of your GLBA information security risk assessment is determining the potential threats. There should also be internal and external threats which should be considered.
Internal threats include:
- Employee negligence or human error
- Inadequate access controls
- Poor password management practices
- Insider threats from disgruntled employees
External threats include:
- Cyberattacks and malware infections
- Phishing and social engineering schemes
- Distributed Denial of Service (DDoS) attacks
- Third-party vendor vulnerabilities
Conduct quality scanning to detect vulnerabilities in the information systems by carrying out vulnerability assessments. Moreover, penetration testing requires simulation attacks in real-world scenarios in order to discover such weaknesses that may go undetected in passive tests.
Step 5: Create Your Risk Assessment Matrix
A risk assessment matrix needs to visualise the identified risks and prioritise them. Also, this tool examines the likelihood and the possible impact.
| Risk Category | Likelihood | Impact | Risk Score | Priority |
| Phishing Attacks | High | High | Critical | 1 |
| Insider Threats | Medium | High | High | 2 |
| System Vulnerabilities | High | Medium | High | 3 |
| Physical Security Gaps | Low | Medium | Medium | 4 |
| Third-Party Vendor Risks | Medium | Medium | Medium | 5 |
This matrix can be used to identify suitable safeguards depending on the level of risk. Consequently, critical risks receive immediate attention and resources.
Schedule a Free Consultation with Qualysec to develop a customized risk assessment matrix for your organization.
Step 6: Design and Implement Safeguards
Prepare detailed protection based on the risks that have been identified in accordance with the GLBA Safeguards Rule. Thus, use controls in three categories:
- Administrative controls: It contains security policies, training programs and incident response procedures.
- Technical controls: Have encryption, multi-factor authentication and intrusion detection systems.
- Physical controls: Have facility security measures, access card systems and surveillance cameras.
Conduct quality scanning and penetration testing for GLBA compliance to identify vulnerabilities before attackers do.
Step 7: Develop all the Documentation
The GLBA risk assessment requirements depend on record keeping to a great extent. Moreover, close documentation has demonstrated compliance during audit.
Document all the risk assessment process, results and risk rating, safety precautions implemented and policy changes. Subsequently, prepare a report on findings and suggestions in detail. Present the existing findings in front of the board of directors, which will be reviewed and approved and supervised.
Step 8: Monitor and Revise Continuously
GLBA assessment process is not completed once it is initially implemented. Also, constant observation means its perpetual effectiveness.
Perform a regular security analysis and vulnerability scan to continuously monitor implemented safeguards. Furthermore, periodically revise and update your risk assessment to reflect the changes in technology, threats and regulations. In their recommendation to the industry, it is suggested that a full assessment should be done at least once in a year and that quarterly review of critical systems should also be done.
What Are the Key Benefits and Challenges of GLBA Compliance?
Benefits of Implementing GLBA Risk Assessment
- Enhanced Security Posture: Organizations are able to proactively detect vulnerabilities and to provide effective security. Subsequently, this minimizes chances of information security breach and unauthorized access.
- Legal Compliance: Legal liabilities and regulatory penalties can be avoided by fulfilling the GLBA risk assessment requirements. As such, organizations keep federal regulators on good terms.
- Customer Trust: Customers will be confident with the company because it will show their concern with the security of their data. Also, this trust results in higher loyalty and positive referrals.
- Cost Savings: Although in the short term the implementation will incur investments, breaches are prevented and will save money in the long run. Moreover, the chance of not paying regulatory fines and reputational losses has great financial advantages.
- Competitive Advantage: Organizational security practices are used to distinguish organizations within the market. In this way, compliance will be a benefit to the business, not merely a compliance burden.
Use robust controls and security testing to stay ahead of cyber risks.
Common Challenges and Solutions
1. Evolving Threat Landscape: The field of cyber threats is dynamic and it becomes more complex. This is the reason why organisations must be highly vigilant and keep on changing security practices.
Solution: Develop threat intelligence and establish relationships with cybersecurity specialists.
2. Resource Allocation: This will demand a lot of time and funds to perform deliberate assessments. Strategic planning however assists in achieving a balance between security demands and efficiency of operation.
Solution: Critical systems should be a priority and automation should be taken advantage of.
3. Keeping Assessments Current: Regulatory copies ensure that the assessments are up to date with the technology and business processes. But there might be an inconvenience in maintaining records.
Solution: Implement automated-process-based systems of compliance management that make updating programs less challenging.
4. Third-Party Risk Management: There are also risks of vendors and service providers. As a result, third parties assessment and oversight become difficult.
Solution: Have vendor risk management programs with frequent review and contractual security measures.
Download Our Pentest Report to see how Qualysec helps organizations overcome these challenges effectively.
Latest Penetration Testing Report

Why is Qualysec the Leading GLBA Risk Assessment Partner in the USA?
In the processes of choosing your partner in your GLBA information security risk assessment, the consideration of expertise and experience is very important. Furthermore, Qualysec is the leading option of financial companies in the United States.
Comprehensive GLBA Compliance Services
Qualysec offers customized end-to-end GLBA evaluations to suit your corporate requirement. Particularly, our group of accredited security experts offers a strong background of expertise in financial services compliance and cybersecurity.
Our services include:
- Complete GLBA risk assessments: We analyze your full information security program against the requirements of GLBA Safeguards Rule.
- Vulnerability assessments and penetration testing: Our members perform more than 9,300 tests to find out security vulnerabilities in web applications, mobile applications, cloud environments, networks, and APIs.
- Continuous security monitoring: We have 24/7 security checks by ensuring complete vulnerability scanning and threats identification.
- Compliance documentation support: Our specialists will assist in creating detailed reports and documents to be reviewed by regulatory bodies.
- Remediation guidance: We do not identify problems and leave it at that; we offer practical solutions and assist in making security enhancements.
Why Choose Qualysec?
- Proven Track Record: Qualysec has been effective in assisting many financial organizations to design and implement a GLBA compliant program. Also, our customers have documented a consistently better security posture and effective regulatory audit.
- USA-Specific Expertise: Our group is knowledgeable of the specific regulatory environment of American financial institutions. As a result, we offer advice that is in compliance with US federal and regional requirements.
- Advanced Technology Platform: The intelligent vulnerability scanner available at Qualysec mimics the actions of hackers and is developed with each evaluation. In addition, our CXO-friendly dashboard allows easy compliance management and reporting.
- Continuous Support: Qualysec provides continuous support as opposed to one-time assessment to tackle emerging threat. Thus, your organization will remain secured in the interim period between the formal assessment cycles.
- Cost-Effective Solutions: We assist organizations to make the most of security investments, by prioritizing critical risks. The clients are then able to gain compliance without unneeded expenditures.
- Trusted by Leading Organizations: Large companies in any field rely on Qualysec to handle their security. In addition, the quality of our services is addressed by our reputation of excellence.
- Location: Qualysec has clients in all parts of the United States and has a specific focus in major financial centers.
Make a free consultation with Qualysec now to discuss your specific GLBA risk assessment requirements and develop a customized compliance strategy.
Our experts at Qualysec have helped secure fintech, SaaS, and enterprise systems across 25+ countries. Manual + Automated Pentesting. No false positives. Actionable reports.

Conclusion
Adopting an elaborate GLBA risk assessment program is a necessity to financial institutions within the United States. Additionally, the cyber threats are expected to get more and more advanced in 2025, and thus, the security level and compliance with the regulations may not be more important.
This guide has addressed the key components of the effective GLBA assessments, both the definition of scope and identification of threats up to the establishment of safeguards and continuous compliance. Moreover, knowing the requirements of GLBA risk assessment can assist organizations in ensuring the safety of information of customers without going into the way of hefty fines.
It is important to keep in mind that the assessment of the GLBA information security risk cannot be a one-time project but a continuous process. Thus, continuous compliance and protection can be guaranteed through regular reviews, continuous monitoring, and active security improvements. Through the assistance of such professionals as Qualysec, the financial institutions will be able to go through the intricacies of the GLBA Safeguards Rule confidently.
Now is the time to work together and improve the security position of your organization and safeguard the financial details of your customers.
Qualysec offers complete cybersecurity compliance services to help organizations meet GLBA and other regulatory standards effectively.
FAQ
1. What is a GLBA assessment?
GLBA assessment is an evaluation procedure carried out by financial institutions in a systematic manner to determine and reduce security threats to customer financial data. This is an overall process conducted in review of information systems, data management and control processes with a view of ensuring that the GLBA Safeguards Rule is adhered to. Moreover, the evaluation assists organizations in putting in place the right administrative, technical and physical controls to ensure sensitive data is not accessed and compromised by unauthorized parties.
2. Who must comply with GLBA?
GLBA risk assessment requires the financial institutions of the United States to make sure that they follow the requirements of the risk assessment, which include banks, credit unions, insurance companies, investment firms, mortgage lenders and even tax preparation services. More so, businesses that do not offer financial services, but obtain customer financial data at covered institutions, might also need to take the necessary precautionary measures. The information security risk assessment requirement of GLBA applies to any organization which substantially deals with consumer financial information.
3. How often should GLBA compliance be reviewed?
To ensure that they are in compliance with the GLBA Safeguards Rule, organizations are supposed to carry out complete GLBA risk assessments at least once in a year. Nevertheless, it is advocated that critical systems and control reviews be done quarterly to respond to arising threats. Also, reviews are necessary when there are major developments in the technology infrastructure, business processes or regulatory standards to ensure that the customer financial data remains secure.
4. What are the 5 things a risk assessment should include?
All critical elements of the GLBA information security risk assessment should entail: (1) scope definition: identifying the systems and data to be evaluated, (2) threat identification: internal and external security risks, (3) vulnerability assessment: the weaknesses of information systems, (4) risk analysis: the probability and impact of the threats identified, (5) safeguard development implementation of the relevant administrative, technical, and physical controls. A combination of these factors provides a complete coverage and security of customer financial data.
5. How much is a GLBA violation?
GLBA risk assessment violations carry serious financial implications with fines up to 100,000 dollars being imposed on institutions depending on the violation. Besides, violating officers and directors might be fined not less than 10,000 dollars per occurrence and may face criminal charges such as a jail term of up to 5 years. Besides, failure to comply with the requirements of GLBA Safeguards Rule may also lead to the loss of a license and significant reputational harm that will affect customer confidence and business relationships.



















































































































































































































































































































































































































































































































































































































































































































0 Comments