PCI DSS 4.0 – A New Era of Continuous Security
In 2025, PCI DSS 6.4.3 and 11.6.1 compliance will become a pressing issue that all businesses processing payment card information must address. Furthermore, version 4.0 of the Payment Card Industry Data Security Standard unveiled new requirements that target the vulnerabilities on the client-side. These are new controls designed to secure payment pages against advanced attacks. Organisations now have to adopt complete script management and real-time monitoring systems. In order to prove these security measures, PCI DSS penetration testing is very crucial. Also, companies should know that these requirements are integrated to establish strong payment security compliance. As such, this paper discusses how penetration testing will prove that you are compliance-ready with these key controls.
Client-side scripts can be adopted through the browser, by users are increasingly targeted by hackers. In addition, conventional security systems are not usually able to identify these advanced attacks. DataDome’s analysis of PCI requirements states that client-side attacks may compromise traditional security measures without any further efforts. Consequently, the PCI Security Standards Council added some requirements of PCI DSS v4.0 6.4.3 and 11.6.1. These measures are directly dealing with the increase in the threat environment. To ensure the safety of cardholder data, the organisations should be aware of these requirements.
What is PCI DSS Requirement 6.4.3?
The PCI DSS Requirement 6.4.3 is dedicated to dealing with payment page scripts, which are implemented in the consumer browsers. In addition to this, this need is classified under a larger group of developing and maintaining secure systems. It also focuses on the client-side security PCI DSS issues that are not managed by traditional server-side protection. According to the all-encompassing guide provided by DataDome, rather than addressing the issue of server-side vulnerabilities, hackers have begun to actively use client-side JavaScript to steal sensitive data right out of the browsers of users.
Explore: What is PCI DSS Compliance?
Core Components of Requirement 6.4.3
The need requires three fundamental controls of organisations. To start with, companies have to use script authorisation. Second, they require script integrity check systems. Third, they should have appropriate script inventory management.
1. Script Authorisation and Verification
There is a need to develop definite ways through which organisations can verify script authorisation. Also, they require internal and third-party script development processes. Moreover, authorisation procedures are also important. The integrity check system is used to check that the scripts have not been modified. As a result, they need to be subjected to a regular monitoring system that will ensure the integrity of the scripts.
2. Script Inventory Management Requirements
The entire inventory of all the scripts is a requirement of compliance with PCI DSS 6.4.3 and 11.6.1. In addition, the necessity of every script should be written. Companies should periodically undertake an audit and reorganise their stocks. This is documented to assist in the process of audit and compliance assessment. Hence, companies need to monitor all scripts that are running on their payment sites.
Key Elements Organisations Must Implement
- Authorisation Methods: Organisations should come up with a transparent procedure of verification before implementing scripts on payment pages, and only those scripts that are verified should be implemented on customer browsers.
- Integrity Monitoring: There should be constant verification systems that ensure that the scripts are not changed and that they are actually operating as they were certified by the security departments.
- Complete Documentation: Companies should have full documentation of how and why each script is required, who approved it and the last time it was reviewed.
- Third-Party Management: The companies should evaluate the security practices of vendors and must create stringent approval procedures for the external scripts deployed on payment pages.
- Regular Reviews: Periodic audit of all scripts is necessary to detect unauthorised modifications and make sure that the PCI DSS v4.0 requirements are always upheld.
- Content Security Policies: This is implemented to enforce CSP controls that a script can perform and restrict its functionality on payment pages.
Also, read: What are the 12 PCI DSS Compliance Requirements?
What is PCI DSS Requirement 11.6.1?
Requirement 11.6.1 of PCI DSS presents mandatory change and tamper observation systems of payment pages. In addition, this demand is also aimed at the real-time detection of unauthorised changes. It is more precise regarding what is monitored; it monitors HTTP headers and webpage content. The study by the security centre of DataDome shows that 65% of websites can be targeted by even the simplest type of bot, and more significant client-side security should be implemented. It, therefore, requires companies to install advanced surveillance mechanisms. The effectiveness of this requirement is achieved by the client-side security PCI DSS measures.
The requirement states that organisations should install an elaborate system of change detection. Also, such systems should be able to trace the content of payment pages. Besides, companies need to notify staff about illegal alterations as soon as possible. The frequency of monitoring should not be less than once every seven days. Nevertheless, different periods can be defined by organisations in accordance with a risk analysis.
Understanding Change Detection Requirements
The requirement specifies that organisations must deploy comprehensive change detection systems. Additionally, these systems need to monitor payment page content continuously. Furthermore, businesses must alert personnel to unauthorised changes immediately. The monitoring frequency must be at least every seven days. However, organisations can establish different intervals based on risk analysis.
Components of Requirement 11.6.1
There are various essential controls that should be adopted by organisations. To start with, they have to implement change detection mechanisms. Second, they must stick to specific routines of monitoring. Third, they should put in place alert response procedures.
1. Detection and Monitoring Systems
The ability to detect change should be fast and able to detect unauthorised changes. In addition, both the content of payment pages and HTTP headers should be tracked. Also, the evaluations should be done at least once a week or even more. Risk analysis can be carried out in documentation to justify the monitoring intervals taken by the organisation. As such, constant supervision offers the most suitable protection against attacks at the client side.
2. Alert Response Procedures
The PCI DSS penetration testing is useful to confirm alert response procedures. Clear protocols of investigation need to be established in organisations. Besides, they require documented response procedures in the face of detected changes. Moreover, it is necessary to keep the records of all the alerts and responses. As a result, companies can prove to be adherent during auditing.
Learn about PCI Compliance Test: What It Is and How to Prepare Your Business.
Critical Monitoring Elements
| Component | Requirement | Purpose |
| HTTP Headers | Continuous monitoring | Detect unauthorised header modifications |
| Page Content | Real-time scanning | Identify malicious script injections |
| Alert System | Immediate notifications | Enable rapid response to threats |
| Evaluation Frequency | Minimum weekly | Ensure timely threat detection |
| Response Documentation | Complete records | Demonstrate compliance readiness |
| Baseline Configuration | Initial setup | Establish normal behaviour patterns |
Why Do Most Businesses Fail These Two Controls?
The issue of PCI DSS 6.4.3 and 11.6.1 compliance is a challenge to many organizations due to various reasons. Furthermore, the aspects of modern web applications make it rather difficult. Conventional security solutions are also usually inadequate to meet these needs. As a result, companies require specific solutions to comply.
Common Implementation Challenges
The companies have problems with controlling the third-party scripts in their checkout pages. Also, the dynamic character of contemporary websites makes the maintenance of inventories difficult. Moreover, automated monitoring tools are not available in many businesses. Thus, the paper-based operations are time-consuming and subject to error. Compliance in payment security needs to be constantly oriented with advanced technology.
Learn our latest guide on Digital Payment Security.
Why Traditional Security Tools Fall Short
Web Application Firewalls aim mainly at protecting the server side. In addition, they are also not able to effectively identify script changes on the client-side. Also, the traditional tools lack advanced browser-based attacks. Security analysts at DataDome state that the conventional cybersecurity solutions, such as WAFs, cannot support such demands because their main emphasis is on server-side security. Therefore, specific client-side security PCI DSS solutions are required in organizations. In addition, the penetration testing of PCI DSS identifies such gaps in security coverage.
Technical Complexity Barriers
- Third-Party Scripts: There is a lot of complexity that arises when it comes to dealing with a lot of external scripts by a variety of vendors, and it becomes hard to keep track of all dependencies and possible vulnerabilities.
- Dynamic Content: Contemporary websites are being dynamically loaded, so real-time inventory maintenance is difficult without the presence of automated discovery and monitoring tools.
- Resource Constraints: Lots of organisations do not have special security teams that are knowledgeable in client-side security, which creates a gap in implementation and continuous monitoring.
- Integration Issues: The interface of new security controls and the integration with the existing infrastructure must be carefully planned, tested, and coordinated among different teams of technicians and systems.
- Continuous Monitoring: 24/7 surveillance of payment pages requires a high number of resources and advanced automation, which most businesses can hardly implement in the right way.
- Documentation Requirements: Multiple scripts, changes, and justifications involve maintaining detailed documentation, which entails structured procedures that can be effectively implemented in line with what the PCI DSS v4.0 demands.
How Does Penetration Testing Validate Compliance?
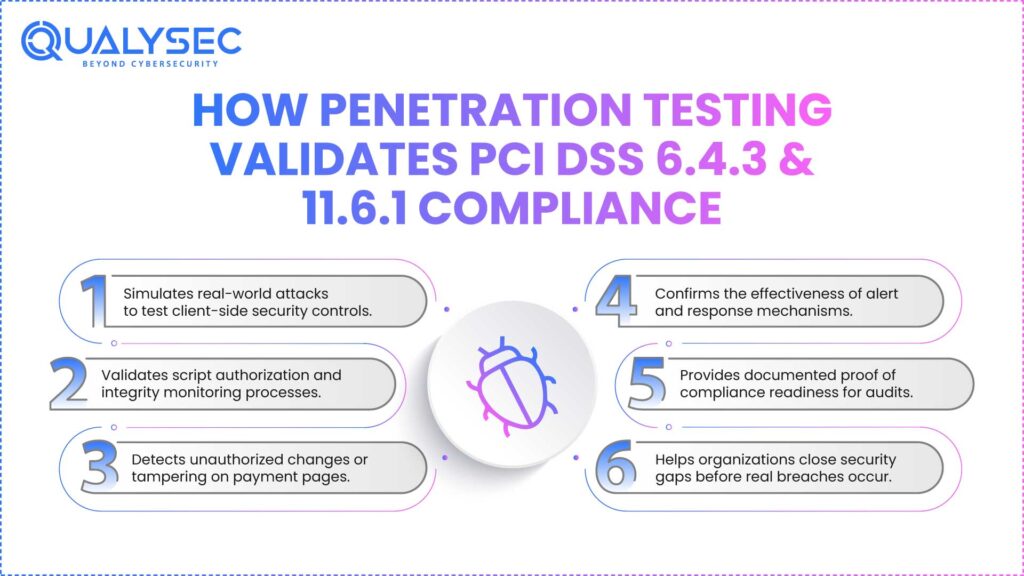
The PCI DSS penetration testing offers essential validation of security controls. In addition, it is able to detect the vulnerabilities that may be overlooked by automated tools. Penetration testing also simulates real-life attack conditions. As a result, organisations are assured of their posture of payment security compliance. Moreover, testing will help justify both requirements 6.4.3 and 11.6.1 at the same time.
Penetration Testing for Requirement 6.4.3
Testing gives the processes of script authorisation a test run. Besides, it checks that integrity monitoring systems are functioning properly. Also, the penetration testers seek to introduce illegal scripts. Thus, organisations can detect the flaws in authorisation processes. Besides, testing brings out loopholes in managing script inventory.
Penetration Testing for Requirement 11.6.1
Testers ensure that mechanisms detecting changes are correct. Also, they are trying to make changes to payment pages without sending any warning. Moreover, the response procedures are effective as tested. As a result, businesses will be able to enhance their response and detection processes. Additionally, compliance audits have evidence in penetration testing.
Key Testing Methodologies
The penetration testing of PCI DSS 6.4.3 and 11.6.1 compliance has a number of approaches. To begin with, testers perform script injection attacks. Second, they make illegal changes. Third, they confirm the system’s effectiveness in monitoring. Also, testers will ensure documentation is complete. In addition, they determine the speed of responding to security alerts.
How Qualysec Ensures You Stay Compliant
Qualysec is also a USA-based company specializing in thorough penetration testing of organisations based on PCI DSS. Also, they have a team of experts who know the intricacies of the PCI DSS requirement 4.0. Qualysec also offers end-to-end security control validation. As a result, the businesses will be able to attain and sustain payment security compliance.
Specialised Testing Approach
Qualysec performs in-depth analyses of client-side security measures. Also, their approach addresses requirements 6.4.3 and 11.6.1 as a whole. Also, they apply sophisticated methods to imitate real attacks. Thus, organisations get practical suggestions on how to improve. Further, testing will involve script management process validation.
Comprehensive Compliance Services
- Script Authorisation Testing: Qualysec tests authorisation procedures by trying to install unauthorised scripts; only authorised scripts should be issued on payment pages.
- Integrity Verification: Testing ensures that the monitoring systems can identify attempts of tampering, and confidence in the effectiveness of client-side security PCI DSS implementation is given.
- Change Detection Validation: This is done by specialists who ensure that the alert systems react appropriately to unauthorised changes so that the detection of a possible security threat can be fast.
- Documentation Review: Thorough examination of compliance documents is used to make sure that organisations have the necessary documentation of PCI DSS 6.4.3 and 11.6.1 compliance audits.
- Remediation Guidance: Detailed reports have specific recommendations as to how to fix the identified vulnerabilities and achieve a much better security posture.
- Continuous Support: Constant support assists organisations to stay compliant with threats constantly changing, as well as updating the requirements of PCI DSS v4.0 periodically.
Schedule a Free Consultation with Qualysec to discuss your specific compliance needs and security concerns today.
Speak directly with Qualysec’s certified professionals to identify vulnerabilities before attackers do.
Why is Qualysec the Leading Provider for PCI DSS Compliance Validation in the USA?
Qualysec is the best option for PCI DSS penetration testing in the United States. In addition, their team is experienced not only in profound technical knowledge but also in profound knowledge of compliance issues. Also, they have a record of successful history in assisting organisations to successfully attain payment security compliance.
Unmatched Expertise and Experience
The security professionals of Qualysec have a lot of experience in PCI DSS v4.0 requirements. Moreover, they are aware of the subtleties of client and server security. Also, their group keeps abreast with changing threat environments. As a result, the clients are provided with innovative testing approaches. In addition, Qualysec has aided hundreds of organisations to be compliant.
Comprehensive Service Offerings
The firm offers end-to-end security testing. They also provide elaborate post-testing remediation instructions. In addition, Qualysec provides easy-to-understand, actionable reports. As such, organizations can readily make the required improvements. In addition, their resources assist businesses in understanding difficult concepts of security.
Why Organisations Choose Qualysec
- USA-Based Team: USA-Based Team Local experts familiar with the compliance requirements of the region and the business operations will offer culturally relevant advice on the engagement.
- Advanced Methodologies: State-of-the-art testing methods detect vulnerabilities that others fail to detect, and so carry out complete validation of client-side security PCI DSS controls successfully.
- Rapid Turnaround: Fast processes provide services that are prompt without affecting quality and assist the organization in achieving strict compliance on time.
- Clear Communication: Technical results are made easy to comprehend by the use of business-friendly language, which allows understanding of all levels of the stakeholders on the risks and priorities.
- Competitive Pricing: Professional PCI DSS penetration testing is affordable to small, medium, and large-sized organizations as a result of transparent, value-based pricing structures.
- Ongoing Partnership: Long-term relationships guarantee constant compliance support since the requirements may keep changing as business needs change with time.
Download Qualysec’s Pentest Report to see detailed examples of their comprehensive testing methodology and reporting standards.
Download a Sample Pen Testing Report

Best Practices for Maintaining Ongoing Compliance
The PCI DSS 6.4.3 and 11.6.1 compliance needs constant work and effort to be maintained. Furthermore, organisations should also develop powerful processes that are not limited to the first implementation. Also, repeated checks and observations are used to maintain data security compliance. Therefore, companies require a systematic method of continuous security management.
Establishing Continuous Monitoring
Payment pages should have automated monitoring systems in the organization. Also, such systems should have real-time alerts to unauthorised changes. Moreover, monitoring data reviews indicate the development of threats regularly. Thus, it will be possible to ensure compliance with the payment security through constant monitoring. Besides, automation saves on human labor and error.
Regular Testing and Validation
Penetration testing of PCI DSS is to be conducted at least once a year. In addition, organizations are supposed to test the following major changes in payment systems. Also, periodic vulnerability testing is a complement to penetration testing. In turn, the businesses are assured of having a secure posture. In addition, compliance audits are supported by testing.
Documentation and Record Keeping
Extensive records are available to verify compliance. Also, companies should keep comprehensive script archives. In addition, authorisation decisions and justifications should be recorded. Hence, an audit is made easy through proper record-keeping. Besides, documentation aids in monitoring the compliance status in the long run.
Talk with Qualysec’s Experts to develop a customised compliance maintenance plan for your organisation.
The Role of Automation in Compliance
The automation is a key element in the PCI DSS 6.4.3 and 11.6.1 compliance in an efficient manner. In addition, the automated tools minimize the workload of manual work. They also offer regular checking and tracing facilities. Therefore, institutions are able to stay up to date with compliance. In addition, automation allows immediate reaction to security threats.
Automated Script Discovery
The current solutions have features of automatically finding and indexing payment page scripts. Also, they monitor script modification in real time. In addition, automated systems detect the addition of unauthorised scripts. Thus, the companies can have the right inventories without manual effort. In addition, automation will make sure that nothing goes through the cracks.
Real-Time Change Detection
The automated systems of monitoring identify the unauthorised changes on time. Also, they compare actual states to approved baselines. Moreover, all systems produce notifications in case of any changes. This, in turn, enables security staff to react quickly to any kind of threat. In addition, automation allows the constant validation of compliance.
Integration with Existing Systems
The automation should be built into the current security infrastructure. Moreover, they have to collaborate with Web Application Firewalls. Besides, it can be integrated with SIEM systems, which give complete visibility. Thus, the organisations obtain comprehensive security management. Furthermore, a complex system minimizes complexities and overheads.
Read our complete guide on Automated Compliance Tools Vs Penetration Testing.
See our pricing, then talk with an expert to choose the best solution for your organization.

Conclusion
The PCI DSS 6.4.3 and 11.6.1 compliance is a major change in payment card security. Besides, the requirements deal with the increasing risk of client-side attacks. Also, companies should have full script management and detect changes. As a result, penetration testing of PCI DSS will be necessary to validate it. In addition, companies require expert knowledge to attain payment security compliance.
The conditions require advanced surveillance and observation. Moreover, the conventional security instruments are ineffective in these controls. Thus, the organisations are advised to collaborate with the proven security providers. In addition, sustained compliance is provided by continuous monitoring and frequent testing. Client-side security PCI DSS measures are effective in ensuring the cardholder data.
Qualysec engages in full testing and validation of organisations. Also, they increase efficiency in compliance among businesses. Moreover, their established methodologies see gaps where other people fail. That is why a collaboration with Qualysec guarantees your company that you will achieve success in implementing PCI DSS v4.0.
Make a Free Consultation with Qualysec Now to begin your journey toward complete PCI DSS compliance today.
Frequently Asked Questions (FAQs)
1. What does PCI DSS Requirement 6.4.3 cover, and why is it important for payment security?
The PCI DSS 6.4.3 will have the organisations handling the payment page scripts by authorisation, integrity validation, and inventory maintenance. In addition, this is an essential requirement as hackers are increasingly using client-side scripts to steal payment information directly out of users’ web browsers when transacting.
2. What is the purpose of PCI DSS Requirement 11.6.1, and how does it protect against client-side attacks?
PCI DSS Requirement 11.6.1 is the requirement that mandates the presence of change and tamper detection measures so that the payment pages can be monitored in real-time to detect unauthorized changes. Also, the ongoing monitoring will mitigate against client-side security PCI DSS threats by creating an immediate alert to the personnel in case of malicious scripts being injected into payment pages.
3. Why do many organisations struggle to meet requirements 6.4.3 and 11.6.1?
The issues with PCI DSS 6.4.3 and 11.6.1 compliance are that the management of the third-party scripts and dynamic content is a challenge that involves particular tools that are not offered by traditional security solutions. Moreover, the need to have an idea of constant surveillance and extensive record-keeping requires access to resources and skills that most companies do not have in-house.
4. How can penetration testing help validate compliance with PCI DSS 6.4.3 and 11.6.1?
To ensure compliance, PCI DSS penetration testing is used to test compliance with the code by imitating real-life attacks to ensure that script authorisation processes, integrity monitoring, and change detection systems are effective. In addition, testing determines vulnerabilities and weaknesses that may go undetected by automated scanning tools and offers assurance of the payment security posture.
5. What steps does Qualysec take to ensure businesses remain compliant with these specific PCI DSS controls?
Qualysec performs thorough testing of script authorisation, script integrity and detection of script changes, reviewing of documents and testing, which will ensure full coverage of the PCI DSS v4.0. They also offer specific remediation advice and continuous assistance to enable organisations to stay in consistent compliance as the threats and requirements change.

















































































































































































































































































































































































































































































































































































































































































































0 Comments