The principle of Drata compliance has transformed the way organizations treat at-on-going compliance monitoring, but a fundamental query is “Does automation override the necessity of penetration testing”? The short answer is no. Although Drata compliance simplifies the numerous compliance operations, it does not exclude thorough security testing. In addition, those organizations that use only automated tools might experience serious security vulnerabilities that can result in expensive breaches. Thus, the reasons why Drata compliance needs penetration testing are necessary to ensure a sound cybersecurity posture. Indeed, as per the latest industry data, 68 percent of breaches are those that are known but have not been patched. This article will therefore explain reasons why penetration testing is essential in addition to Drata compliance automation and the best way to implement penetration testing in the USA.
Is Automated Compliance Monitoring a Substitute of Security Testing?
Does Automated Compliance Monitoring Replace Security Testing?
Understanding the Limitations of Automation –
- Automated compliance vs security testing are two different yet complementary strategies to cybersecurity. Although Drata compliance is very effective at continuous monitoring and evidence collection, it is more of a compliance and not an active threat detection tool. Moreover, automated tools verify that controls are present and operating, however, they do not recreate actual attack situations.
- Drata limitations cybersecurity are evident, taking into consideration the sophistication of recent cyber threats. As an example, automated systems can check that a firewall is in place, but cannot say whether an attacker is capable of beating the firewall. Also, compliance automation does not check against logic errors, abuse of business logic or new zero-day threats that cannot be detected by humans.
- The American Institute of CPAs (AICPA), the regulators of SOC 2 compliance, stipulate that organisations should evaluate risks and take the required controls to minimise the risks to the level that is acceptable. One of the potential evaluations that organisations may be willing to conduct is penetration tests, which is specifically stated.
The Gap Between Compliance and Security
Regulatory compliance with Drata compliance helps to ensure that your organisation remains in compliance with regulatory requirements. But, compliance does not necessarily mean security. This is a serious gap that can be seen with the following differences:
- Control presence undergoes compliance tests, whereas control effectiveness is confirmed by the penetration test.
- Automated scanning detects known vulnerabilities, whereas penetration testing discovers unknown weaknesses
- Compliance monitoring tracks configuration, while security testing exploits misconfigurations
- Automation provides point-in-time snapshots, but penetration testing reveals real-world attack paths
- Compliance tools verify documentation, while penetration testing validates the actual security posture
- Automated systems follow predefined rules, whereas skilled testers adapt to unique organisational contexts
Talk with Our Experts at Qualysec to understand how penetration testing complements your Drata compliance program effectively.
| Aspect | Drata Compliance Automation | Penetration Testing |
| Primary Focus | Compliance validation & evidence collection | Active security vulnerability discovery |
| Testing Approach | Automated, continuous monitoring | Manual + automated, periodic deep-dive |
| Scope | Configuration checks, policy compliance | Real-world attack simulation |
| Detection Capability | Known vulnerabilities, policy violations | Unknown vulnerabilities, logic flaws, attack chains |
| Frequency | Continuous, real-time | Periodic (quarterly/annually recommended) |
| Human Expertise | Limited, primarily in configuration | Extensive, simulates attacker’s mindset |
Why Do Organizations Using Drata Still Need Penetration Testing?
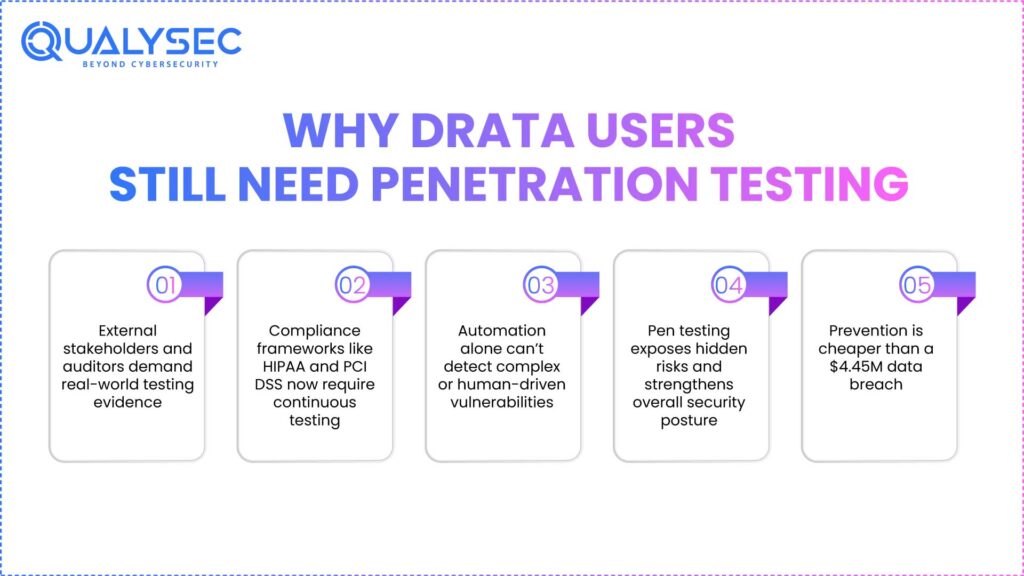
External Stakeholder Expectations and Industry Standards
It is a common practice in the industry to have many organisations request or require their vendors to perform a penetration test occasionally to locate vulnerabilities in the perimeter as well as to estimate the risks of an external cyber threat. Thus, despite the Drata compliance which you may have established, your customers, prospects, and auditors will almost certainly demand evidence of penetration testing.
Drata compliance penetration testing has come to be a differentiator in the competitive USA market. Companies that provide an overall picture of security measures, such as frequent penetration testing, are also at a huge advantage when they are making deals with a security-conscious customer. In the meantime, the ones who can only use automation can either have to go through long security forms or lose competitiveness.
When organisations choose not to perform penetration tests regardless of tradition, the auditors will tend to examine the decision making process and compare other evaluations with the risk evaluations so as to prove that the risks are managed accordingly.
Regulatory Pressure and Evolving Compliance Requirements
Continuous penetration testing is increasingly being required by more compliance frameworks to represent the current always-on threat environment, and compliance is becoming more pressure to shift to quarterly rather than annual testing. Moreover, growing SEC decisions provide enforcement muscle to these demands, and Drata compliance penetration testing is not only good practice, but it is becoming increasingly mandatory.
Regulations that affect the USA specifically, such as HIPAA, PCI DSS, and state laws regarding data security, are starting to focus more on proactive security. Therefore, companies in regulated areas need to show that they are not merely ticking the boxes; however, they are proactively protecting themselves. Also, the average cost of an incident of data breach in the world is currently at 4.45 million dollars, and this figure continues to rise by 15 per cent in three years, therefore, prevention in the form of penetration testing is a cost-effective investment.
Discovering What Automation Misses
In a study of the industry, only 8 per cent of organisations claimed to be very certain that they can find exploitable vulnerabilities with their existing testing method, which indicates that the status quo is not working any more. This is a vivid statistic displaying Drata’s limitations when used alone in cybersecurity.
Penetration testing helps to expose vulnerabilities that are always missed by automated tools. As an illustration, experienced penetration testers can spot attack chains of many minor threats that can form significant security threats. In addition, they also test against business logic defects that demand a proficiency of your application workflows. Likewise, social engineering vulnerabilities and insider threat vectors should be properly tested by humans.
Schedule a Free Consultation with Qualysec to discover hidden vulnerabilities in your environment.
How Often Should Penetration Testing Complement Drata Compliance?
Establishing an Effective Testing Cadence
The frequency of Drata compliance penetration testing will be based on a number of factors, but in your organisation, some of them will be specific to your organisation. Nonetheless, industry best practices offer clear directions to the USA-based organisations that have determined the best security posture.
Recommended testing frequencies include:
- Quarterly penetration testing for high-risk applications processing sensitive customer data
- Bi-annual assessments for moderate-risk environments with stable infrastructure
- Annual comprehensive penetration testing as an absolute minimum baseline
- Ad-hoc testing immediately following major infrastructure changes or deployments
- Continuous vulnerability scanning integrated with periodic manual penetration testing
- Post-incident testing after any security breach or near-miss event
Penetration testing as a service should be used when organisations wish to test more frequently, especially around a major release, and after security incidents, to retest shortly after a fix has been made, and to ensure that remediation has been achieved. Thus, strategic penetration testing at periodic intervals should be added to constant compliance monitoring using Drata compliance.
Aligning Testing with Business Changes
Your penetration testing timetable ought not to be absolutely time-based. Rather, when major changes take place in your environment, they cause other evaluations. An example of these would include a new cloud migration, a rollout of an API or a significant update to software that would introduce a new attack surface and demand urgent security validation.
Timing is important in the modern threat context, since there is just too much that can occur between point-in-time testing. This means that organisations that apply Drata compliance need to conduct event-based penetration testing in addition to their routine. This strategy guarantees that automated compliance vs security testing do not work in opposition but work in harmony instead of creating a false sense of security.
What Type of Penetration Testing Works Best with Drata Compliance?
Comprehensive Testing Approaches for Maximum Coverage
Companies that use Drata compliance penetration testing are advised to bear in mind several testing methodologies in an effort to have full security testing validation. The various types of testing expose the various categories of vulnerabilities, and thus it is important to approach them in a layered fashion.
External penetration testing mimics an external network attacker to your network boundary, and is used to test internet-facing applications, API, or infrastructure. This type of testing fits the Drata compliance perfectly, as it is used to verify that security controls that are visible to the outside world are operational as intended. Meanwhile, internal penetration testing is based on the assumption that an attacker has already been able to access it and is used to gauge whether you can block subsequent lateral movement and privilege escalation.
Application penetration testing concentrates on web applications, mobile applications, and APIs and reveals the vulnerabilities of programs and input validation. Likewise, cloud security testing is now an urgent concern for USA organisations that use AWS, Azure, or Google infrastructure. Moreover, social engineering testing checks your human security controls, which Drata compliance automation cannot sufficiently test.
Specialised Testing for Compliance Frameworks
Various compliance models focus on various elements of security, and different penetration testing methods are needed. SOC 2 gives leeway in terms of the penetration testing, such as the frequency, type (black-box external or white-box internal), and scope (specialised web applications, network, or client-side testing).
Organisations should align their Drata compliance penetration testing strategy with their specific compliance requirements:
| Compliance Framework | Recommended Penetration Testing Focus | Minimum Frequency |
| SOC 2 Type 2 | External web application, infrastructure | Annual |
| PCI DSS | External network, internal segmentation | Annual (external), Six months (internal) |
| HIPAA | External perimeter, internal application | Annual minimum |
| ISO 27001 | Risk-based comprehensive testing | Annual minimum |
| FedRAMP | Multi-layered, extensive documentation | Annual (varies by impact level) |
| GDPR | Data protection-focused, breach simulation | Risk-based, recommended bi-annual |
Download Our Pentest Report to see real-world examples of vulnerabilities discovered through comprehensive testing
Latest Penetration Testing Report

Why Qualysec Is the Best Partner for Drata Compliance Penetration Testing in the USA?
Expertise in Compliance-Driven Security Testing
Qualysec is the best match for USA-based organizations in terms of searching among the best penetration testing partners to supplement your Drata compliance program. Having a profound understanding of both the need to comply and the need to test security, Qualysec works as a fitting bridge between automated compliance testing and automated security testing.
The service offered by Qualysec specifically focuses on the Drata limitations in cybersecurity by offering human-based security validation that cannot be repeated by automated tools. The senior security experts of the company are familiar with the special regulatory environment that influences the business in the USA, such as the state-specific data privacy regulations, federal cybersecurity policies, and the industry-specific regulatory frameworks.
Key differentiators that make Qualysec the best choice include:
- Compliance-aligned methodology that integrates seamlessly with Drata compliance workflows
- USA-based security experts who understand domestic regulatory requirements and business contexts
- Flexible testing cadences supporting both scheduled and event-driven continuous compliance monitoring needs
- Comprehensive reporting that satisfies auditor expectations and customer security questionnaires
- Rapid remediation validation enabling quick turnaround on fix verification
- Strategic security guidance helping organisations mature their security programs beyond basic compliance
Proven Track Record and Comprehensive Service Offering
Qualysec also provides penetration testing services in all the major frameworks that need security verification as well as Drata compliance. Their testing procedures comply with the SOC 2 guidelines of AICPA, requirements of PCI DSS, HIPAA requirements on cybersecurity, and the newly introduced federal cybersecurity requirements for USA organisations.
Location: Serving organizations throughout the United States with specialised expertise in USA regulatory requirements
Services Offered:
- External and internal penetration testing
- Web application security assessments
- Cloud security penetration testing (AWS, Azure, Google Cloud)
- API security testing
- Mobile application penetration testing
- Social engineering assessments
- Red team exercises
- Continuous penetration testing programs
The only difference between Qualysec is that they know that Drata compliance penetration testing is not only about identifying vulnerabilities, but is also about proving to the stakeholders that full security due diligence exists. Their audit reports are detailed and offer the evidence that your auditors, customers, and prospects desire, and the guidance they offer on how to remediate the issue ensures your team can correct issues in the most efficient way possible.
In addition, the pricing schemes at Qualysec can fit any organisation at different levels of development, including start-ups developing their first security program and enterprises with multifaceted compliance needs in multiple frameworks. Their elastic models of engagement mean that, regardless of your requirements, be it annual all-around testing or monthly target testing, you still get the same quality and comprehensive coverage.
Make a free consultation with Qualysec now to discover how their penetration testing services can enhance your Drata compliance program and strengthen your overall security posture. Schedule your consultation with their security experts.
Talk to our Cybersecurity Expert to discuss your specific needs and how we can help your business.
Implementing Penetration Testing Alongside Drata Compliance
Building an Integrated Compliance and Security Program
The combination of Drata compliance and penetration testing has to be strategically planned and properly integrated. The organizations should practice these approaches as complementary to each other, as opposed to conflicting priorities. Moreover, the definition of working processes between compliance monitoring and security testing will lead to a more robust program overall.
Begin by understanding your most vulnerable assets and systems with your Drata compliance system. These are prioritised targets of penetration testing. Also, based on continuous compliance monitoring data provided by Drata, decide penetration testing scope and areas of focus. As an example, when Drata detects configuration drift in cloud environments, the institute planned cloud configuration testing on a regular basis to confirm the security implications.
Best Practices for Effective Integration
The effective implementation of Drata compliance penetration testing involves coordinating the work of several teams, communication channels, and so on. Security teams, compliance officers, development teams, and operations staff are all very important to successful integration.
Having clear goals and scope for every penetration test in accordance with certain compliance requirements and business risks. Select penetration testing partners that are well-versed in compliance frameworks and can provide reports meeting the auditor requirements. As well, make penetration testing a part of your software development life cycle, and run a test at important points in the cycle, such as pre-production releases or post-major infrastructure changes.
Develop moving testing schedules that are responsive to your changes instead of using calendar-based testing only. Findings of the feed penetration testing are used to feed back into your Drata compliance program to tweak controls and overall security posture. In addition, make sure that there is rapid validation of remediation, so that it is tested shortly after the fix is made, thereby bridging the gap between the vulnerability discovery and the fix.
Organisations are also expected to have a record of documentation that illustrates the correlation between automated compliance vs security testing activities. This documentation shows auditors and customers that you are approaching security in a holistic fashion instead of leaning on automation.
Read our recent article on Vanta Compliance Services!
Conclusion
Drata compliance is priceless in terms of continuous monitoring and smooth evidence gathering, but it cannot serve as an alternative to the highly important element of penetration testing, which is the validation of security. Combining automated compliance vs security testing methods is mandatory and not optional as the USA organizations are exposed to more sophisticated cyber threats and changing regulatory requirements. The Drata limitations cybersecurity are not shortcomings but are instead natural limitations of what can be accomplished by compliance automation as opposed to security evaluations that are guided by human beings.
Companies that have adopted Drata compliance penetration testing programs can enjoy great benefits such as improved security posture, quicker remediation, met expectations among stakeholders as well as less cost of breaches. Knowing the reasons as to why periodic penetration testing should be used to complement continuous compliance monitoring, businesses can develop entirely robust security programs that can protect against the actual security threats and achieve compliance demands.
Download Our Comprehensive Resources to learn more about integrating penetration testing with compliance automation effectively.
FAQ
1. Does Drata provide penetration testing as part of its compliance automation?
No, Drata compliance is more of continuous compliance monitoring and evidence collection service than penetration testing service. Whereas compliance of drata can be used to verify that security measures are in place and operating in line with compliance standards, it does not imitate real-world attacks or find exploitable vulnerabilities as penetration test does. Compliance Organizations that leverage Drata compliance must collaborate with experienced providers of penetration testing to gain complete security validation.
2. Why is penetration testing needed if I already use Drata?
Automated compliance vs security testing are two different methods that are complementary and not substitutory. Drata compliance is very good at constant monitoring and validation of policy, but Drata drawbacks cybersecurity do not allow it to imitate the actions of an attacker or identify complex vulnerability chains. Penetration testing offers the human-assisted security verification performing an informal verification and detection of logic errors, business logic misuse, and the emergent threats not detected by the automated tools and ensuring that your compliance efforts will be converted into real security.
3. How often should penetration testing be performed alongside Drata compliance?
The frequency of compliance penetration testing is based on your risk profile and regulatory compliance, though in the USA, penetration testing should be a minimum of an annual baseline. The processing of high-risk environments with sensitive data need to introduce quarterly testing whereas moderate-risk organizations can take advantage of bi-annual testing. Moreover, ad-hoc penetration testing should be initiated by compliance monitoring continuously with Drata compliance to ensure that after critical infrastructure changes, new major deployments, or security breaches, the new attack surfaces are protected.
4. What type of penetration testing is most useful for Drata users?
The external penetration testing that is used to verify internet-facing applications and infrastructure as well as the application-specific testing of critical systems is most useful to organizations that have Drata compliance. This is a way of overcoming the Drata limitations cybersecurity that includes real-world attack simulation that supplements automated compliance checks. To select the scope and methodology of testing in particular compliance frameworks such as SOC 2, HIPAA, or PCI DSS, USA businesses ought to think about extensive testing incorporating web application testing, cloud security testing, and API testing.
5. Who performs penetration testing for Drata compliance needs?
Drata compliance penetration testing must be conducted by skilled cybersecurity experts who are knowledgeable about security testing and compliance requirements. Qualysec is the best option to the USA organizations, and it has compliance aligned penetration testing that integrates with Drata compliance testing workflows as well as the gaps in automated compliance vs security testing. Partners chosen to work with organizations should be those that are aware of the expectations imposed by the regulatory bodies, those providing reports that are acceptable by the auditors, and those that deliver quick remediation validation to ensure that continuous compliance monitoring is effective.



















































































































































































































































































































































































































































































































































































































































































































0 Comments