Serverless security has been a serious concern for organisations worldwide. The use of cloud-based functions to develop scalable applications is becoming increasingly popular among modern business companies. Nevertheless, this change raises specific security issues. Older security devices are not always effective at safeguarding temporary or event-based environments.
In the serverless computing model, the developers are no longer involved in the management of infrastructure. This enables the teams to work in terms of code instead of servers. However, there is a danger in this convenience. Functions are temporary functions that are activated based on various occurrences. This generates gaps in visibility. Companies are finding it difficult to track security as it happens.
These are the issues that are tackled in this guide. We examine the Lambda functions’ security, serverless threat detection, and Functions as a service security practices. Also, we discuss serverless IAM best practices and serverless vulnerability management strategies. We will be dealing with AWS Lambda, Azure Functions and Google Cloud Functions. The mission is straightforward: the aim is to ensure that you secure your deployments in your serverless applications.
Recent studies have suggested that serverless computing has radically changed the application architecture in that it removes the infrastructure management burden, but creates unique security risks that cannot be sufficiently mitigated by traditional security tools. Thus, organisations require unique strategies. This paper offers practical methods and approaches to ensuring serverless environments throughout the development cycle.
What Are the Unique Security Challenges in Serverless Architectures?
Serverless environments are not similar to traditional infrastructure. As such, they pose different security threats. To be effectively guarded, one should know these differences.
The Ephemeral Nature Problem
There are no functions during compilation. This impermanence makes security surveillance very difficult. The conventional security agents are not capable of being deployed in temporary containers. In addition, operations can be fully operationalised before security services can effectively check them.
There are three primary cybersecurity issues with organisations that operate serverless functions: low visibility into transient assets, event-driven architecture with larger attack surfaces, and vulnerability noise inundation of developers. It is these challenges that need specially designed solutions as opposed to customised conventional tools.
Expanded Attack Surface
Architectures of events present numerous points of entry. Every potential vulnerability is represented by a function trigger. Moreover, serverless applications are distributed, making them more complex. Applications contain hundreds of interrelated functions. The existence of each connection is a potential attack point.
Since serverless functions are event-driven and react to external inputs, an incoming opportunity is a potential attack surface, which is a significant enlargement of the attack surface. Thus, the development of complex security measures should cover any possible triggering cases.
IAM Complexity
Identity and access control are more complicated. Certain permissions are needed in each of the functions. This generates a plethora of Identity and Access Management (IAM) Services roles and policies. It is not practical to manage them manually. Privilege escalation may happen as a result of misconfigurations. Illegal access to confidential resources becomes a threat.
Key Security Challenges Table
| Challenge Area | Traditional Systems | Serverless Systems | Security Impact |
| Infrastructure Control | Direct server management | Cloud provider abstracted | Limited visibility into the underlying infrastructure |
| Runtime Environment | Persistent processes | Ephemeral execution | Cannot deploy traditional security agents |
| Attack Surface | Fixed endpoints | Dynamic function endpoints | Continuously changing attack vectors |
| Monitoring Approach | Agent-based | API and log-based | Requires new observability strategies |
How Do You Implement Shift-Left Security for Serverless Functions?
Shift-left security embeds protection early in development. This proactive approach prevents vulnerabilities before deployment. Moreover, it maintains developer agility while ensuring robust security.
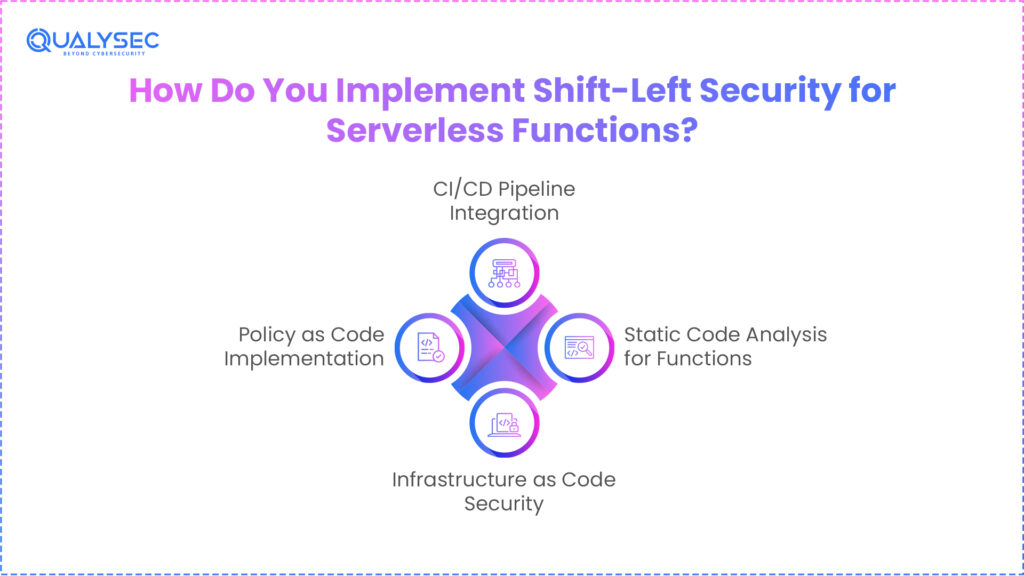
1. Static Code Analysis for Functions
Serverless security begins with code-level protection. Static Application Security Testing (SAST) tools scan function code for vulnerabilities. However, traditional SAST tools struggle with serverless architectures. Therefore, specialised solutions are necessary.
Modern tools understand cloud service integrations. They analyse the function code deeply. Additionally, they identify injection flaws, authentication bypasses, and cryptographic weaknesses. Tools like AWS CodeGuru and Fortify provide comprehensive coverage across multiple languages.
Modern SAST solutions provide deep analysis of function code while understanding cloud service integrations, scanning for vulnerability categories including injection flaws, authentication bypasses, cryptographic weaknesses, and business logic errors. This specialised approach ensures effective protection for serverless applications.
2. Infrastructure as Code Security
Serverless deployments are defined by infrastructure as Code (IaC). Misconfigurations are prevented by security scanning of IaC templates. Tools like Prisma Cloud and Checkov are used to analyse templates before deployment.
These tools detect various security risks:
- Overly permissive IAM roles
- Publicly accessible functions
- Unencrypted environment variables
- Missing security controls
Serverless vulnerability management demands automated IaC scanning. This pre-empts security problems in production. This means that the cost of remediation reduces.
3. Policy as Code Implementation
Policy as code brings security standards to implementation. This allows automated validation in the development. Moreover, it allows uniformity in any deployment.
Implementation strategies include:
- Security policies which are version-controlled.
- CI/CD pipeline policy validation.
- Immediate developer feedback on violations
- Connection with cloud-native services.
4.CI/CD Pipeline Integration
Vulnerability detection in CI/CD pipelines is a necessity that is automated. This incorporates several scanning levels. Dependency analysis, container scanning and configuration validation are automatically done. Besides, checks are activated at different stages of the pipeline.
The feedback process should be fast. This promotes agile development practices. At the same time, it has extensive security coverage. The findings should be prioritised according to severity to enable the developers to concentrate.
Talk with our experts at Qualysecto to learn how we implement comprehensive shift-left security for serverless applications.
Why Is Advanced Runtime Protection Critical for Serverless Security?
The runtime protection is a solution to threats when functions are being executed. The old agent-based solutions are unable to work within ephemeral environments. As such, new solutions are required to protect it successfully.
The use of strategies of agentless monitoring.
1. Agentless Monitoring Strategies
The use of agentless monitoring takes advantage of cloud-native logging services. It applies API integrations and platform-specific telemetry. The Falcon Cloud Security platform by CrowdStrike offers vulnerability assessment during pre-runtime on AWS Lambda, Google Cloud Functions, and Azure functions, which is done by integrating it with exposure management tools. This is a non-agent-based and full visibility approach.
In the case of AWS Lambda, CloudTrail and X-Ray are employed for monitoring. Application Insights is integrated with Azure Functions. Such services help the security teams collect the necessary data. In addition, they do not compromise the performance features that render serverless appealing.
2. Real-Time Threat Detection
Cloud Watch and Azure Monitor allow real-time threat detection. These platforms are natively integrated with the execution metric of functions. Security teams define custom alerts and metrics. These detect suspicious behaviours successfully.
Serverless workload characteristics have to be considered in detection strategies:
- Unusual invocation rates
- Abnormal error frequencies
- Unexpected resource access patterns
- Execution duration anomalies
Falcon Cloud Security relies on cloud account registrations to map out serverless functions and all package dependencies and consolidate serverless security data into one tool across cloud providers, languages and runtimes. This central method makes operations of security operations simple.
3. Behavioural Anomaly Detection
Behavioural analysis is important in serverless threat detection. Execution data is analysed through machine learning algorithms of historical data. They construct models detecting deviant behaviours in real-time. The functions that access abnormal resources raise alerts. Handling unusual amounts of data is suspicious.
The detection system should be continuously adjusting. However, updating codes often results in legitimate behaviour change. There is a need to balance between sensitivity and false positive minimisation. This makes security teams to respond appropriately to actual threats.
4. AI-Powered Vulnerability Prioritisation
ExPRT.AI rating system is a dynamically predictive AI model of priority of vulnerabilities according to the level of risk they introduce to environments, including exploit status and advanced threat intelligence. This smart prioritisation assists the teams in working on the key vulnerabilities initially.
Teams do not use generic CVSS scores, but they rank them on a business context basis. This enhances quicker remediation. In addition, it minimises the chances of exploitation.
Download our comprehensive Serverless Security Assessment Report to understand your current security posture.
How Can Organisations Automate Compliance for Serverless Security Deployments?
Automation of compliance provides a uniform security posture. The process of compliance management manually is not viable at scale. Thus, serverless environments require automated solutions.
Adapted Security Benchmarks
CIS benchmarks need to be changed to a serverless architecture. Control measures used in the traditional designs targeting servers do not suit the functions. The organisations will need to redefine security controls.
Serverless-specific benchmarks focus on:
- Function-level security control.
- Suitable authentication systems.
- secured environment variables.
- Limited functionality permissions
Deployments are also continuously tested by automated validation mechanisms. This guarantees the uniform security posture of all functions. Furthermore, it makes the compliance reporting much easier.
Configuration Drift Detection
Configuration drift occurs rapidly in serverless environments. Functions deploy easily and frequently. Automated drift detection systems monitor configurations continuously. They identify deviations from approved baselines quickly.
Detection mechanisms track changes across multiple layers:
- Function code and runtime settings
- Environment variables and permissions
- Associated cloud resources
- IAM roles and policies
Real-time alerting enables rapid response. Automated remediation maintains configuration integrity. This prevents security breaches and compliance violations effectively.
Secrets Management Automation
Serverless IAM best practices require robust secrets management. Functions need access to various credentials securely. Hardcoded credentials create significant vulnerabilities. Therefore, automated secrets management is essential.
Implementation strategies include:
- Integration with cloud provider secret stores
- Just-in-time secret retrieval
- Automated secret rotation
- Detection of potential secret exposure
Prisma Cloud generates scans on serverless functions to present visibility of vulnerabilities and compliance problems, and the scanning is performed through the validation of permissions, locating functions, retrieving code, scanning with the help of proprietary sensors, and reporting the findings to the console. This is a holistic solution that will provide extensive security coverage.
Cross-Function Policy Consistency
Automation is needed to ensure that the policies used in several functions remain consistent. Function-as-a-Service security requires standardised controls. Template deployments have security controls as a default feature. CI/CD pipelines have policy validation gates that discourage deviations.
The security updates are propagated effectively by centralised policy management systems. They keep a record of changes to policies. This makes accountability and compliance in the whole serverless ecosystem possible.
Compliance Monitoring Dashboard
| Compliance Area | Automation Method | Validation Frequency | Remediation Approach |
| IAM Permissions | Policy as Code validation | Every deployment | Automated role adjustment |
| Encryption | IaC template scanning | Continuous | Template correction |
| Logging | Runtime monitoring | Real-time | Function redeployment |
| Access Controls | API Gateway analysis | Daily | Configuration updates |
Schedule a free consultation with Qualysec to implement automated compliance for your serverless infrastructure.
Why Qualysec Leads in Serverless Security Solutions for Global Organisations
Qualysec is a globally trusted organisation with regard to a full package of serverless security solutions. We are experienced with AWS Lambda, Azure Functions and Google Cloud Functions. We offer end-to-end protection throughout the lifecycle of development.
Comprehensive Serverless Security Coverage
Qualysec provides niche vulnerability management solutions. Our group knows the peculiarities of ephemeral architectures. We apply protection systems that accommodate a serverless nature. In addition, our solutions are developer agile and strongly secure.
Our services include:
- Advanced Code Analysis: Function-level vulnerabilities deep scanning.
- IaC Security Validation: Automated template analysis avoiding misconfigurations.
- Runtime Protection: Agentless real-time threat detection.
- Compliance Automation: Ongoing checking with the industry standards.
Global Expertise and Presence
Qualysec provides services to organisations in the USA and the rest of the world. We have a wide range of experience in cloud-native security aware of the compliance requirements of the region. We also have localised support and therefore effective communication.
Our global reach enables us to:
- Quickly respond to security-related instances across time zones.
- Give continuous supervision and assistance.
- Regionalised security policies.
- Provide uniform security levels across the nations.
Proven Track Record Serverless Security
Qualysec is preferred by organisations due to its results. We are a mix of innovative technology and experience. We have good practices of serverless IAM. Moreover, our server less threat detection system detects vulnerabilities prior to exploitation.
Client benefits include:
- Minimised security attacks due to proactive security.
- Quicker and more automated security.
- Reduced costs of compliance by automation.
- Better security posture in all deployments.
- Laid-back Solutions to Each Organisation.
Tailored Solutions for Every Organisation
We realise that a set of issues is specific to every organisation. As such, we have highly customizable solutions. We liaise with your teams. This makes sure that security controls are in line with business intentions. Besides, we offer thorough training and continuous guidance.
Industry-Leading Tools and Partnerships
Qualysec uses security platforms that are leading in the industry. We integrate with tools like CrowdStrike Falcon Cloud Security and Prisma Cloud. This provides clients with best-in-class protection. Additionally, our partnerships ensure access to the latest security innovations.
- Serverless Penetration Tests.
- Cloud Functions Penetration Testing.
- Membership Automation Implementation.
- Security Architecture Consulterie.
- Threat Monitoring and Response 24/7.
Make a free consultation with Qualysec now to change your serverless security posture. We will evaluate your present situation. We will find our vulnerabilities and give recommendations which will be implemented. Schedule your consultation today.
Talk to our Cybersecurity Expert to discuss your specific needs and how we can help your business.
Conclusion
Serverless security needs solutions that are specialised in particular architectural issues. Conventional security infrastructures are incapable of securing the event-driven, temporary environments. Thus, organisations should use solutions that are specifically created and stand throughout the development cycle.
This guide discussed holistic protection measures. We discussed the protection of the development of shift-left security embedding. Also, we explored the runtime monitoring, which offers real-time detection of threats. Compliance automation provides the same security posture to deployments.
Effective Lambda function security, including that of Azure functions and Cloud functions, is conditional on a number of factors. CI/CD pipelines need to be automated in scanning by organisations. They require runtime protection agentless monitoring solutions. Moreover, Policy as Code guarantees governance without slowing down the speed of development.
Function-as-a-Service security will be improved through further automation in the future. Increased connection to cloud-native services will improve security. Furthermore, AI-based applications will work as fast and as large-scale as the current serverless applications.
Those organisations that are following these practices can go on with the adoption of serverless computing with great confidence. They also hold firm security stances, but are also taking advantage of the serverless advantage. The point is that serverless security needs change and modification, not adjustment of the traditional methods.
Take action today to secure your serverless deployments. Implement the strategies outlined in this guide. Partner with experts who understand serverless architectures deeply. Contact Qualysec now to begin your serverless security transformation.
Find Your Perfect Security Partner

FAQ
Q1.What is serverless security?
Serverless security is the process of keeping the cloud-based function environments secure against contemporary threats. It covers expert practices that deal with ephemeral architectures. These are practices that are very different from conventional infrastructure security solutions.
Q2.What are the unique security challenges of serverless architectures?
Serverless architectures also confront unique issues, such as the gap in visibility of functions at any point in time and the broadened attacker surfaces. Event-triggered-based triggers provide various points of vulnerability to attacks. Also, having many permissions based on functions makes the IAM even more complex.
Q3.How do you secure AWS Lambda functions?
To achieve AWS Lambda security, it is necessary to use shift-left security and code scanning, as well as IAC validation. Organisations require run-time protection in terms of agentless surveillance and real-time threat identification. To enhance, serverless IAM best practices provide that permission management is taken care of in all functions.
Q4.What’s the difference between securing serverless security vs. container-based applications?
Serverless security will not be able to apply the traditional agent-based techniques because of temporary execution environments. Container security is based on persistent runtime agents and network-based controls. Thus, serverless will need dedicated agentless surveillance and event-driven security measures.
Q5.What tools are available for serverless security?
Several tools offer end-to-end protection of servers, such as Prisma Cloud and CrowdStrike Falcon. Such sites provide vulnerability scanners, compliance automation and runtime protection. Also, AWS CodeGuru and SAST tools with a focus on functions consider the security needs on a functional level.
“Additional Resource Cloud Security Posture Management (CSPM)”





















































































































































































































































































































































































































































































































































































































































































































0 Comments