Key Takeaways
- PTaaS market is surging: The Penetration Testing as a Service market is forecast to grow from $141.83 million in 2025 to $165.46 million in 2026, which would represent a significant change toward outsourced security.
- Internal bias creates blind spots: In-house teams typically use the same reasoning and therefore miss important flaws that outside testers with a hacker approach might find by means of actual attack simulations.
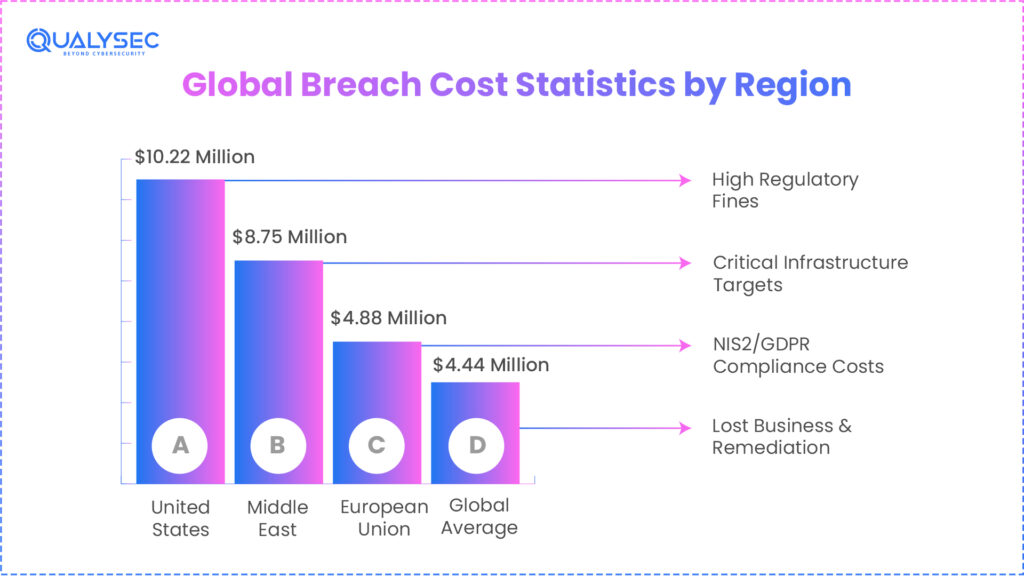
- Breach costs are skyrocketing: U.S. companies incur, on average, a breach cost of $10.22 million; proactive penetration testing can help businesses save up to $2 million per incident.
- AI and cloud are top attack targets: Traditional defenses are insufficient to safeguard contemporary infrastructure, as deepfake-based social engineering soars 87%, and artificial intelligence model exploitation up 45%.
- Hybrid testing provides better results: Automated scanning plus manual expert testing finds difficult flaws like multi-step attack flows and broken business logic that tools alone invariably miss.
Introduction
Outsourcing penetration testing is one of the most reliable approaches to figure out the security gaps and loopholes that hackers can exploit. Giving the cybersecurity responsibility to the experts who know this game can be the best way for modern CISOs and CTOs to reduce the burden.
As per one of the2026 reports, the market of Penetration Testing as a Service (PTaaS) is increasing to around $165.46 million. This number has grown significantly to $141.83 million in 2025.
Nowadays, in the age of AI and digitization, the cybersecurity standards and practices have changed in various ways. Gone are the days when manual checks or scanning were enough to bypass any potential cyber threat or risks. In 2026, AI phishing and other forms of cyber attacks will be more common than you can think of. That’s where you need the experts with the third-party tools to get an honest validation of your security frameworks.
Additionally, the outsourced penetration testing services can keep your organization ahead of hackers while maintaining global compliance regulations. Let’s try to understand more about why relying on the internal security audits is not going to work anymore.
The Rising Necessity of Outsourced Security in 2026
The global cybersecurity market has gone through a major shift over the years. While the previous blockers or concerns were once simple malware. Now, we have very complex and Agentic AI threats that can impact any organization in real-time. That’s why annual or routine cybersecurity audits are no longer enough. For company leadership, the question has changed from whether you will be targeted by hackers to how strong our defenses are against potential exploitation.
One major reason to have a penetration testing service provider by your side is that attacks are a real threat now. Because of internal compliance paperwork or daily operations, the security audit often leaves loopholes for hackers to exploit. Once they’re in, it’s not just your money or customer data at risk of exposure, but your market reputation as well. The experts specializing in cybersecurity services and applications will bring deep, creative strategies for ethical hacking.
If we look at recent reports, one thing is clear: internal teams are failing to keep pace with modern-day cybersecurity trends and requirements. With more and more channels opening up, potential vulnerabilities and hacking attempts are almost impossible to keep an eye on. That’s exactly where organizations are failing if they’re not considering outsourcing penetration testing.
One of the 2026 reports highlights that 2025 had around 30,000 new vulnerabilities for organizations in various sectors. If we go into more in-depth research, the number has seen around a 17% rise from the previous year’s records. This flood of increasing loopholes for organizations makes the need for a reliable cybersecurity partner unavoidable.
Still looking for your company’s ideal outsourced penetration testing provider?
Contact Our Security Professionals
Why Do Internal Teams Often Miss Critical Flaws?
One of the major sources of cybersecurity risks is internal bias. In simple terms, when the same team is aligned on testing, they tend to follow the same logic. It’s like their minds are working in one direction without going towards different possibilities. That’s one of the major differences between in-house Vs outsourced penetration testing.
When you hire the external team for cybersecurity work, they bring in a different perspective towards finding potential loopholes. Think of the outsourced testing team trying out the hacking mindset by simulating in the same way as the exploiters. This will highlight the broken business logic and loopholes that you might be unintentionally ignoring.
Market Shift Toward Outsourced Security Services
| Feature | Internal Testing | Outsourced Penetration Testing |
| Perspective | Internal/Biased | Objective/Third-Party |
| Cost Model | High Fixed (Salaries/Tools) | Variable/Project-Based |
| Skill Diversity | Limited to Hired Staff | Broad Global Expert Pool |
| Compliance Value | Lower (Self-Assessment) | High (Independent Validation) |
Why are CISOs Investing in Proactive Penetration Testing?
Irrespective of the organization, the CISO is always concerned about making the right balance for the budget. In reality, the investment for third-party penetration testing will be just a slight amount in comparison to what you’ll lose in a single data breach. In 2026, the financial stakes are higher, mainly for organizations in the United States. Along with the financial information, cyber risks and threats are more focused on sensitive customer information.
If we take the global view, the expenses behind the data breach keep fluctuating. This becomes a serious concern for organizations, with an impact on each of them. The problem gets more serious for companies that are either unprepared or still relying on the older approaches. As per the IBM Cost of Data Breach Report, U.S. companies are facing a breach expense of around $10.22 million. That’s where you need the reliable support of the outsourced penetration testing services.
Understanding The ROI of Penetration Testing
Your investment in the periodic enterprise penetration testing services typically reduces the “Mean Time to Identify” (MTTI) of a breach. Organizations trusting these third-party companies and testing tools put up a strong defense against potential exploitation. Such companies end up witnessing a massive difference in the financial recovery gains.
In reality, the companies relying on incident response testing and timely security validation can save around $2 million per incident. On the other hand, this can be huge savings in comparison to those that still rely on older processes.
2026 Global Breach Cost Statistics by Region
| Region | Average Breach Cost (USD) | Primary Reasons for Expenses |
| United States | $10.22 Million | High Regulatory Fines |
| Middle East | $8.75 Million | Critical Infrastructure Targets |
| European Union | $4.88 Million | NIS2/GDPR Compliance Costs |
| Global Average | $4.44 Million | Lost Business & Remediat |
Protecting AI and Cloud Assets With Penetration Testing
With Chief Technology Officers prioritizing the integration of Artificial Intelligence and cloud-native technologies, the third-party penetration testing is a definitive need. The reason behind this is that such integration opens various channels for exploiters to find their way in.
In 2026, significant cyber threats are targeting the intelligent parts of the network infrastructure. Gone are the days when traditional firewalls were able to stop the cyber attackers. Now, you need modern cybersecurity mechanisms to save the AI model or hidden API endpoint from exploitation.
If we check a report fromForrester’s 2026 Predictions, the majority of the data breaches happen from the agentic AI frameworks. This makes the outsourced penetration testing a priority requirement for the AI models’ security.
Nowadays, cybersecurity experts are the best choice for identifying weak areas. These loopholes can be prompt injection, model inversion, and data poisoning. Additionally, these approaches will also figure out other possible ways capable of compromising information.
Top 2026 Attack Vectors Requiring Testing
| Attack Vector | Growth in 2026 | Testing Focus |
| AI Model Exploitation | 45% Increase | Data Integrity & Prompt Security |
| Supply Chain/Third-Party | 30% Increase | Vendor Access & API Security |
| Cloud Misconfigurations | 22% Increase | IAM Roles & Storage Permissions |
| Social Engineering (Deepfakes) | 87% Increase | Human Element & Vishing |
How Qualysec Secures Your Organizations With Penetration Testing Strategy

Till now, you must be thinking about the query: how to choose a penetration testing company? In 2026, this question matters a lot as you need the experts who can really help with a strong defense setup. Rather than just making superficial promises, the cybersecurity company needs to have enough experience and exposure to safeguard from cyber risks or threats.
Qualysec, the best penetration testing company, stands out in the market with trusted frameworks, mechanisms, and third-party tools. Rather than just relying on the automated tools, Qualysec empowers cybersecurity with the combination of human input and expertise. The experts implement deep and process-focused third-party penetration testing to upscale the security standards.
The company is a reputed cybersecurity service provider that meets the exact needs of modern CISOs and CTOs. You can say goodbye to just a list of bugs or issues, and hello to a proper roadmap of cybersecurity from potential exploiters.
Ready to outsource your penetration testing to experts who simulate real-world attacks?
Get Your Free Security Assessment.
Hacker-Like Simulations To Find Weak Areas
At Qualysec, we do much more than run scanners for enterprise penetration testing services. You can expect the real-world attack simulation from our experts to be very similar to how actual hackers would do. With experienced and expert hacking teams, we perform hybrid-level penetration testing that combines automation and manual testing.
This approach has worked wonders in finding the complex vulnerabilities for several organizations from diverse niches. While the traditional automated tools miss potential loopholes, our approach highlights all sorts of broken access, controls, networks, and multi-step logic flows.
Delivering Compliance-Ready Cybersecurity Reports
We understand that a penetration testing report matters a lot for CISOs and CTOs. We create and deliver compliance-ready cybersecurity testing reports that can align with the strictest auditors. No matter if your aim is to get SOC 2, ISO 27001, HIPAA, or DORA compliance, Qualysec provides the steps and summaries that every CISO looks for. Our security reports can be a real game-changer to prove your security standards in front of stakeholders and regulators.
Need an outsourced penetration testing partner that delivers actionable insights with compliance-ready reports?
[Schedule Your Free Consultation]
Speak directly with Qualysec’s certified professionals to identify vulnerabilities before attackers do.
Top-Notch Expertise for Technology Security
- Fintech Security: Our team uses penetration testing to check payment gateways and blockchain implementation with a precision approach.
- AI-Driven Apps: Our cybersecurity testing team comes with the right experience to find potential loopholes in LLMs and complex algorithms.
- Cloud & SaaS: We perform in-depth testing mechanisms on multi-tenancy architectures to separate customer data and protect it.
Final Comments – Outsource Penetration Testing 2026
Hence, in 2026, cybersecurity has bypassed the technical challenge for organizations. It has now become a basic part of the business operations and security approaches. Additionally, the penetration testing also leads to the company’s trust levels and reputation.
Every CISO or CTP who is thinking of outsourcing penetration testing is concerned about safeguarding data and reputation. With Qualysec, the penetration testing RFP checklist and proven approaches ensure that you can target each potential loophole and find a way to resolve it.
Frequently Asked Questions (FAQs)
Q: What can be the frequency of outsourced penetration testing in 2026?
Ans: Usually, the organizations need to conduct penetration testing on an annual basis. However, in 2026, cybersecurity should be an ongoing process rather than a one-time thing. Many cybersecurity experts recommend penetration testing after every major launch or release. Additionally, the penetration testing should be applicable to any significant change to the network architecture. The continuous testing models by penetration testing service providers are new security standards for SAAS and fintech companies.
Q: Can penetration testing assist in reducing the cyber insurance premiums?
Yes, the majority of the insurance providers in 2026 are too strict on the policy. They now ask for proof of independent security validation from companies providing enterprise penetration testing services. Once you’re able to showcase that you’ve already identified and resolved vulnerabilities, it can definitely lower the insurance premiums. These can also help in increasing the policy coverage limits.
Q: Can you explain the key difference between vulnerability assessment and penetration testing?
A vulnerability assessment is like high-level scanning, figuring out the potential loopholes for hackers to find their way in. On the other hand, a penetration test moves to the next phase that simulates the same hacking attempts as an actual exploiter. The approach of third-party penetration testing will give a clear visibility into the weak areas and damage potential. In simple words, vulnerability testing highlights the loopholes, and penetration testing highlights whether hackers can use them to exploit.
Q: How much time does the outsourced penetration testing service take?
Usually, the penetration testing services can take around 2-4 weeks. However, with a new scope, the timeline of the outsourced penetration testing can also be changed. These third-party penetration tests include the initial testing, active exploitation, and reporting with potential solutions.



















































































































































































































































































































































































































































































































































































































































































































0 Comments