Introduction
GDPR Article 32 security testing documentation requires organisations to implement technical and organisational measures, such as regular testing and evaluation of security controls. According to reports from the European Commission, more than 280,000 personal data breach notifications have recived to EU data protection authorities since May 2018. Many of these incidents happened because of technical weaknesses.
In several cases, systems were misconfigured, access controls were not strong enough, and some software vulnerabilities were not detected in time. It is commonly seen everywhere that organisations initially focus on building infrastructure, but do not document their security testing activities. They mostly conduct occasional vulnerability scans or fix issues as they arise, but there is no collection of evidence of such steps. Only when the organisations prepare for compliance review, the security team realises that while some testing occurred, there is little documented evidence to show continuous evaluation of security controls as required under Article 32 of the GDPR.
This guide helps you understand GDPR Article 32and its core requirements. How you should document security testing, and how organisations can implement a practical documentation framework for compliance.
What is Article 32 of the GDPR?
Article 32 of the GDPR refers to the provision in the General Data Protection Regulation that mandates “Security of Processing.” It requires organisations to ensure they protect personal data against unauthorised access, accidental loss, destruction, or alteration. It mandates that controllers and processors implement appropriate technical and organisational measures to protect personal data.
The regulation also mandates that organisations implement measures appropriate to the risk level associated with personal data processing.
Applicability of Article 32 GDPR
Article 32 of the GDPR is applicable to:
- Data Controllers and Data Processors.
- any organisation, including its employees and staff, regardless of its size or location, that processes the personal data of individuals located in the European Union (EU) or European Economic Area (EEA).
Requirements under Article 32 GDPR
Article 32 of the GDPR requires:
Implementation of technical measures
Controllers and processors must implement the following security measures that match the level of risk involved. These measures help protect personal data properly:
- Pseudonymisation and encryption of personal data. These methods help reduce the risk of data exposure. Organisations’ mandate to maintain the integrity, availability, and resilience of the systems and services used for processing data.
- Another important requirement is the ability to restore access to personal data quickly if something goes wrong. This could be a technical failure or even a physical incident.
- Finally, the GDPR mandates that organisations regularly test and review their security measures to make sure they are still effective.
Risk assessment consideration
Whenever an organisation has to determine appropriate security measures, Risk assessment considers the risks presented by processing during:
- Accidental or unlawful destruction
- Loss
- Alteration
- Unauthorised disclosure
- Unauthorised access to personal data transmitted, stored, or processed.
Certification
The organisation must adhere to the approved code of conduct as referred to in Article 40 of the GDPR, or to an approved certification mechanism as referred to in Article 42 of the GDPR, because it can use as evidence of compliance with the requirements set forth in Article 32.
Assess control
Controllers and processors must ensure that any person acting under their authority who has access to personal data only processes it on instructions from the controller, unless required by law.
Why is security testing documentation important for GDPR Compliance?
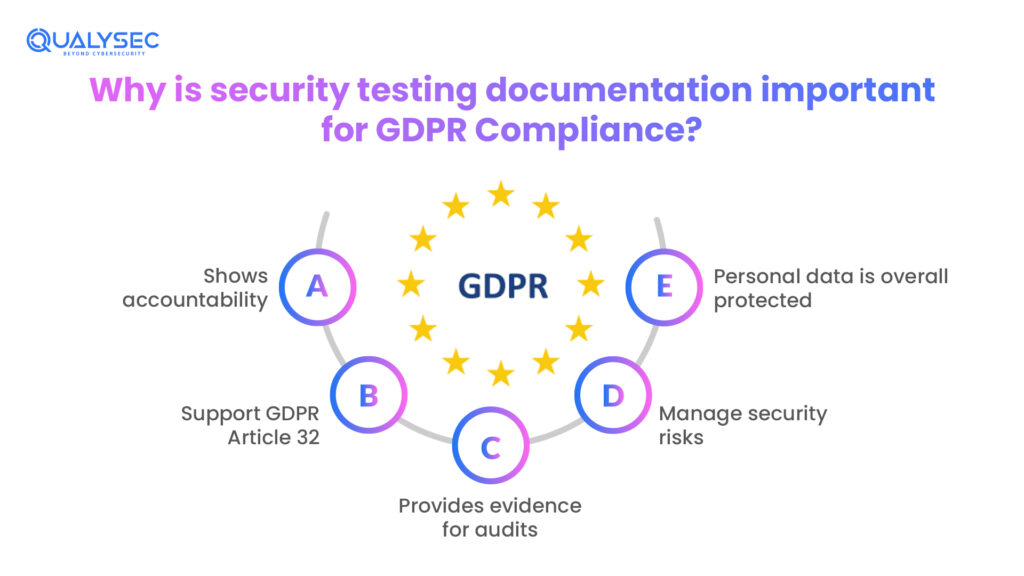
Security testing documentation helps organisations:
- Shows accountability: GDPR requires organisations to show that they protect personal data. Security testing GDPR Article 32 security testing documentation, such as GDPR penetration testing reports and remediation records, proves that security checks are performed regularly and that risks are addressed properly.
- Support GDPR Article 32: Article 32 requires organisations to evaluate their security measures. Security testing shows that the organisations conduct regular vulnerability scans, perform penetration testing and monitor risks to personal data.
- Provides evidence for audits: GDPR requires organisations to maintain records and evidence of security processes, including testing activities and remediation actions. GDPR compliance documentation shows the testing methods used, the scope of assessments, and the actions taken to fix identified vulnerabilities.
- Manage security risks: Security testing documentation records vulnerabilities, risk levels, and mitigation steps. This helps organisations monitor security improvements and stay compliant with GDPR security testing requirements.
- Personal data is overall protected: Regular documentation of GDPR penetration testing and EU data protection testing helps organisations identify weaknesses early, improve security controls, which ensure that the personal data is protected
Types of Security Testing Relevant to GDPR Article 32
As per Article 32 of the GDPR, organisations handling personal data must implement appropriate technical and organisational measures. Organisations rely on multiple security testing methods to meet GDPR requirements, such as:
- Vulnerability Assessment (VA): Report from Verizon shows that vulnerability exploitation was responsible for around 14% of all data breaches in 2023. In vulnerability assessment, the cybersecurity experts scan systems and applications to identify security weaknesses. Vulnerability assessment focuses on publicly known vulnerabilities, outdated software, system misconfigurations, and weak encryption mechanisms.
- Penetration Testing: When organisations handle personal information, they use penetration testing to see how a cyberattacker may find their way into their systems. Penetration testing serves as an effective means to demonstrate the correspondence to the requirements of the security testing of GDPR Article 32. Cybersecurity practitioners in penetration testing will recreate real-world cyberattacks to determine the exploitable vulnerabilities of systems that handle personal data. Penetration testing assists in identifying risks of data exposure, API vulnerabilities and vulnerabilities of the network. A detailed format, such as an attack scenario, records the results of testing.
- Application Security Testing: This is used in many organisations in which personal data is handled on the web and mobile applications. Application security testing detects such attacks as injection attacks, broken authentication, insecure data storage and access control vulnerabilities.
- Infrastructure Security Testing: Infrastructure security testing evaluates the security of underlying system components, including servers, networks, cloud services, and operating systems, to ensure that the organisation correctly configures and secures the infrastructure that stores or transmits personal data against unauthorised access or attacks.
- Configuration and Compliance Testing: Configuration and compliance testing verify whether system security settings align with established security standards and best practices. It includes reviewing access control policies, encryption configurations, identity and access management systems, and firewall rules.
If you want to learn about how documentation works, click below to download a sample report that can help your business achieve GDPR compliance.
Latest Penetration Testing Report

Security testing tools commonly used for Article 32 GDPR compliance
- For vulnerability scanning: Nessus, OpenVAS, Qualys VMDR
- For penetration testing: Nmap, Metasploit Framework, Burp Suite, Wireshark, OWASP ZAP, Nessus, SQLmap, and John the Ripper
- Web Application security testing tools (DAST): OWASP ZAP, Burp Suite
- Network security testing tools: Nmap, Wireshark
- System security audit tools: Lynis, Lepide Auditor
Elements of GDPR security testing report.
GDPR Article 32 security testing documentation is important in demonstrating compliance with the GDPR. Article 32 of GDPR states that organisations should have in place suitable technical and organisational controls in order to satisfy certain requirements and that they should also perform and test their security controls regulating personal data regularly, continuously and evaluate their efficiency.
Security testing policy
A security testing policy is a policy that specifies how security testing is done within a given organisation. It gives the description of testing activities and the testing that will be carried out, such as vulnerability scanning and penetration testing. A frequency of testing is also specified by the policy. Besides, it outlines clearly the roles and responsibilities of teams involved in the process of planning, performing and reviewing the security testing activities.
Testing scope documentation
It determines what will be covered under security tests, which includes systems, applications and infrastructure. It also provides a clear list of assets for the team to test in the process of the assessment. Such assets can be web applications, databases, cloud, and network infrastructure. Systems processing or storing personal data, like web applications where user information is processed, databases where personal data is stored, APIs exchanging personal data, and third-party service integrations are also specified in the scope documentation.
Testing methodology
Testing methodology describes frameworks, tools and procedures applicable in the security tests. The policy explains the step-by-step procedure the security team adopts when undertaking testing exercises. This includes how the team identifies vulnerabilities, confirms findings, and duly records the results
Security testing report
The report gives an elaborate overview of the outcome of the security test. These reports have known areas of vulnerability, risk rating, evidence to support working on the vulnerability and suggested remedies. The reports provided formal evidence that the organisation carrie out security testing activities. The organisation uses it as a documented account of the security audits.
Common mistakes organisations should avoid
- Some organisations keep only summary reports and do not include full details of vulnerabilities.
- Many organisations do not record how they fixed identified vulnerabilities.
- Security tests are sometimes done irregularly or only after a security incident.
- The methods used for testing are often not explained or recorded.
- Reports may not include proof, such as screenshots or evidence of vulnerabilities.
- Retesting after fixing vulnerabilities is sometimes not tracked.
- Documentation is often outdated or poorly managed.
- Some documentation does not clearly follow GDPR security testing requirements.
How Qualysec can help with GDPR Article 32 security testing
Companies working with personal data use professional cybersecurity companies to conduct expert security inspections and generate documentation compliant with the requirements. Qualysec provides:
- Penetration Testing and Vulnerability Assessment: Qualysec offers vulnerability testing and penetration testing services that replicate the reality of cyberattacks to uncover risks in the apps, networks, and systems that handle personal data.
- Application and Infrastructure Security Testing: Qualysec provides advanced pentesting and secures web applications, mobile applications, APIs, cloud-based systems, and network infrastructure. These services assist in making sure that systems that are dealing with personal data are well set up and are resistant to unauthorised access.
- Compliance-Oriented Security Reporting: Qualysec generates comprehensive penetration testing reports that include vulnerability descriptions, CVSS risk rating, proof-of-concept evidence, and advice on how to fix the vulnerabilities. These reports give official records that organisations may make use of in regulatory inspection or compliance checks.
- Remediation Support: Once vulnerabilities are uncovered, Qualysec provides organisations with remediation advice and testing services to determine that security problems are properly solved.
- Providing Continuous Security Monitoring: Qualysec also provides continuous security testing and monitoring, which will allow organisations to periodically evaluate the performance of their security controls and keep a robust cybersecurity posture.
Conclusion
Article 32 of GDPR is considered a compliance measure; yet in reality, the GDPR Article 32 security testing documentation of security testing the can tell a lot about the work of an organisation. Every identified and remedied vulnerability provides insight into system design, operational functions, and internal human behaviour. By ensuring organisations observe these records closely and keep them up-to-date, rather than merely gathering evidence of compliance, the records can also reveal weaknesses lurking in the organisational background, assist the teams to streamline their work processes and enhance security measures, as well as inform better decision-making processes in the information technology and business processes. It is also able to assist in risk management and security planning in the long-term.
Are you a business looking for a GDPR service provider? Your wait has come to an end. Schedule a FREE call with our expert consultant to learn how to achieve GDPR compliance.
Talk to our Cybersecurity Expert to discuss your specific needs and how we can help your business.
Frequently Asked Questions (FAQs)
Q.Is penetration testing required under GDPR Article 32
The General Data Protection Regulation, specifically GDPR Article 32, does not explicitly require penetration testing. However, it mandates regular testing and evaluation of security measures. Penetration testing identifies vulnerabilities and shows that organisations strengthen data protection controls.
Q.How should security testing be documented for GDPR audits?
Structured records must document security testing, including testing policies, defined scope, methodologies, testing reports, identified vulnerabilities, evidence, and remediation actions.
Q.How often should GDPR security testing be conducted?
GDPR does not specify an exact testing frequency but requires organisations to conduct regular assessments. Many organisations perform security testing annually or after significant system changes.





















































































































































































































































































































































































































































































































































































































































































































0 Comments