Key Takeaways
- CTEM represents the evolution of traditional vulnerability management, designed for how modern threats actually move.
- In the current cybersecurity environment, constant visibility and validation are becoming a necessity, rather than an option.
- According to Gartner (Strategic Planning Assumptions, 2023), organisations deploying CTEM initiatives may be three times less prone to a breach in 2026.
- The framework links security decisions not only to the technical severity but also to business risk.
- Exposure management firms are trying to provide a quantifiable result as opposed to a non-quantitative report.
- The names of Pentera, Qualysec, XM Cyber, Cymulate, and Tenable One appear most frequently in 2026.
- The potential return on investment is better compliance, increased resilience, and speedier remediation.
Introduction
Cybersecurity used to be simpler. You’d scan for vulnerabilities, patch what you could, and move on. That approach worked, until it didn’t.
Today’s attack surfaces don’t sit still. Cloud environments, SaaS sprawl, and hybrid infrastructure; threats are constantly shifting, and traditional vulnerability management vendors were simply not built for this kind of complexity. They identify, sure. But identifying isn’t the same as understanding risk. And that gap? It’s exactly where breaches happen.
Industry estimates suggest the CTEM market is expected to grow significantly through 2030. This development is part of a wider move towards ongoing, risk-based security measures driven by modern CTEM vendors.
The potential impact of CTEM has also been mentioned by Gartner. Organisations with a mature CTEM program, based on its strategic planning assumptions, might be as much as three times less likely to suffer a breach by 2026. Although this is a projection into the future, it highlights the increasing strategic relevance of the framework.
The focus on CTEM is gaining momentum in industries, and numerous organisations are examining or testing exposure management programs as components of their overall cybersecurity measures. Such a rate of adoption does not occur without reason.
CTEM vendors and exposure management companies are stepping in where legacy tools have fallen short. Offering continuous visibility, real validation, and actual remediation pathways.
This blog breaks down why that shift is happening, and which solutions are driving it.
What Is CTEM? Understanding the Framework
Gartner introduced Continuous Threat Exposure Management in 2022, and it’s fair to say the framework arrived at exactly the right time.
CTEM isn’t a product. It’s not a CTEM certification or a single-vendor solution. It’s a structured program, one that organizations run continuously to identify, prioritize, validate, and remediate security exposures before attackers can act on them. The distinction matters because a lot of teams still confuse “buying a tool” with “having a strategy.” CTEM is the strategy.
What makes it different from older approaches is the word continuous. Unlike traditional approaches that rely on periodic assessments, CTEM emphasizes continuous monitoring and ongoing risk evaluation across cloud, on-premises, SaaS, and hybrid environments.
Cybersecurity platform providers and CTEM vendors operationalize this through five defined stages:
| CTEM Stage | Description | Business Value |
| Scoping | Defines critical assets, systems, and attack surfaces | Aligns security with actual business priorities |
| Discovery | Surfaces vulnerabilities, misconfigurations, and shadow IT | Improves environment-wide visibility |
| Prioritization | Ranks risks by exploitability and potential impact | Cuts down unnecessary remediation effort |
| Validation | BAS validates security controls, AEV validates attack paths, & Penetration testing validates deep exploitation and business logic flaws | Reduces false positives significantly |
| Mobilization | Pushes remediation workflows and drives response | Speeds up risk reduction across teams |
Each stage feeds into the next. Skip one, and the whole program weakens.
As enterprises move deeper into hybrid and cloud-native infrastructure, this kind of structured, ongoing exposure management isn’t optional anymore. It’s foundational.
Key Exposure Categories in CTEM
CTEM programs rely on multiple exposure management layers to provide full visibility:
- EASM (External Attack Surface Management)
Focuses on internet-facing assets, shadow IT, and unknown external exposures - CAASM (Cyber Asset Attack Surface Management)
Provides visibility into internal assets, configurations, and ownership across environments - DSPM (Data Security Posture Management)
Identifies where sensitive data resides and how it is exposed or misconfigured
Together, these categories help organizations move beyond vulnerability scanning toward full exposure visibility.
Limitations of Traditional Vulnerability Management
Legacy vulnerability management had its place. But that place was a different era of cybersecurity, one where attack surfaces were smaller, slower, and far more predictable.
Today, that model is struggling to keep up. A few reasons why:
1. Periodic scanning, not continuous monitoring:
Most traditional tools run on scheduled cycles. Quarterly or monthly scans mean weeks of blind spots between assessments.
2. CVE overload is real:
More than 40,000 vulnerabilities were disclosed in 2024, according to data from the National Vulnerability Database (NVD). Security teams using old prioritization methods simply cannot triage that volume effectively.
3. CVSS scores only tell part of the story:
A high severity score doesn’t mean a vulnerability is actively exploitable in your environment. Without context, teams end up chasing the wrong risks.
4. No validation layer:
Traditional vulnerability management vendors flag weaknesses but rarely confirm whether those weaknesses can actually be exploited. That’s a significant operational blind spot.
5. Cloud, identity, and shadow IT fall through the cracks:
Many legacy tools were not originally designed to address modern cloud, identity, and SaaS-driven environments, creating visibility gaps that newer solutions aim to close. Attack surface management vendors were, in many ways, created specifically to fill that gap. Traditional tools rarely provide visibility into identity-related exposures. This includes:
- IAM misconfigurations that grant excessive permissions
- Privilege escalation paths across users and roles
- Machine identities and service accounts operating with long-lived credentials
In modern environments, attackers often move through identity layers rather than exploiting software flaws directly. Without identity visibility, critical attack paths remain hidden.
6. Alert fatigue slows everything down:
Too many alerts, too little context. Remediation stalls, and real threats get buried.
7. Visibility Issues:
No visibility into identity risks, such as privilege escalation or token misuse.
Identity exposures are largely ignored. Traditional tools focus on CVEs but miss identity risks such as over-permissioned accounts, stale credentials, and service-to-service trust relationships. In modern breaches, attackers often move laterally through identity paths rather than exploiting a single vulnerability. Therefore, huma-led analysis is important.
Talk with Qualysec experts today

Why CTEM Vendors Are Replacing Traditional Vulnerability Management
Vulnerability management didn’t fail because it was poorly designed. It failed because the threat landscape outgrew it. CTEM vendors aren’t just offering a better product; they’re offering a fundamentally different way of thinking about risk. And organizations are paying attention.
1. From Reactive to Proactive
Traditional tools wait for scheduled scans to surface problems.CTEM runs continuously, so it identifies and assesses exposures in real time, not weeks after they appear. With some vulnerabilities within days, or even hours, of disclosure, periodic scanning no longer meets the needs of modern security environments.
2. Prioritization That Actually Reflects Risk
CVSS scores measure severity in isolation. CTEM vendors factor in exploitability, active threat intelligence, and direct business impact. The result is a shorter, more accurate remediation list that security teams can actually act on.
3. Full Attack Surface Coverage
Cloud misconfigurations, third-party integrations, shadow IT, and identity exposures. Legacy tools weren’t built for any of this. Attack surface management vendors and exposure management companies have stepped in specifically because modern environments require visibility that goes well beyond the traditional perimeter.
4. Attack Path Analysis Changes Prioritization
CTEM does not treat vulnerabilities in isolation. It maps how attackers can move across systems by chaining weaknesses together. This includes:
- Lateral movement across cloud, identity, and endpoints
- Combining multiple low-risk issues into a high-impact attack path
- Graph-based modeling to identify how critical assets can be reached
This approach helps teams focus on exposures that are actually reachable and exploitable, rather than isolated vulnerabilities that may never be used.
5. Validation Before It Matters
Breach-and-attack simulations and continuous penetration testing allow cybersecurity platform providers to confirm whether an exposure is genuinely exploitable before an attacker gets there. Traditional methods flag. CTEM confirms.
6. Faster, Smarter Remediation
Automation and orchestration push remediation tasks directly to the teams responsible for fixing them. Security and IT stop working in silos. Response times drop.
7. Regulatory Pressure Is Accelerating Adoption
The changing rules, including GDPR, NIS2, DORA, and the SEC cybersecurity disclosure rules, are emphasizing more on continuous monitoring, risk visibility, and documented security practices, which are more in line with CTEM principles.
Stop chasing thousands of vulnerabilities. Contact us to fix the ones that actually matter.
| Feature | Traditional VM | CTEM Vendors |
| Approach | Reactive | Proactive |
| Frequency | Periodic | Continuous |
| Scope | Known vulnerabilities | Full attack surface |
| Prioritization | CVSS-based | Risk and threat-based |
| Validation | Limited | Continuous testing |
| Business Alignment | Low | High |
| Outcome | Lists of issues | Measurable risk reduction |
| Identity Security | Limited | Core focus |
| Attack Path Analysis | Not supported | Central capability |
CTEM isn’t a rip-and-replace of vulnerability management. It’s what vulnerability management should have evolved into.
Top 5 CTEM Vendors in 2026: Global Leaders
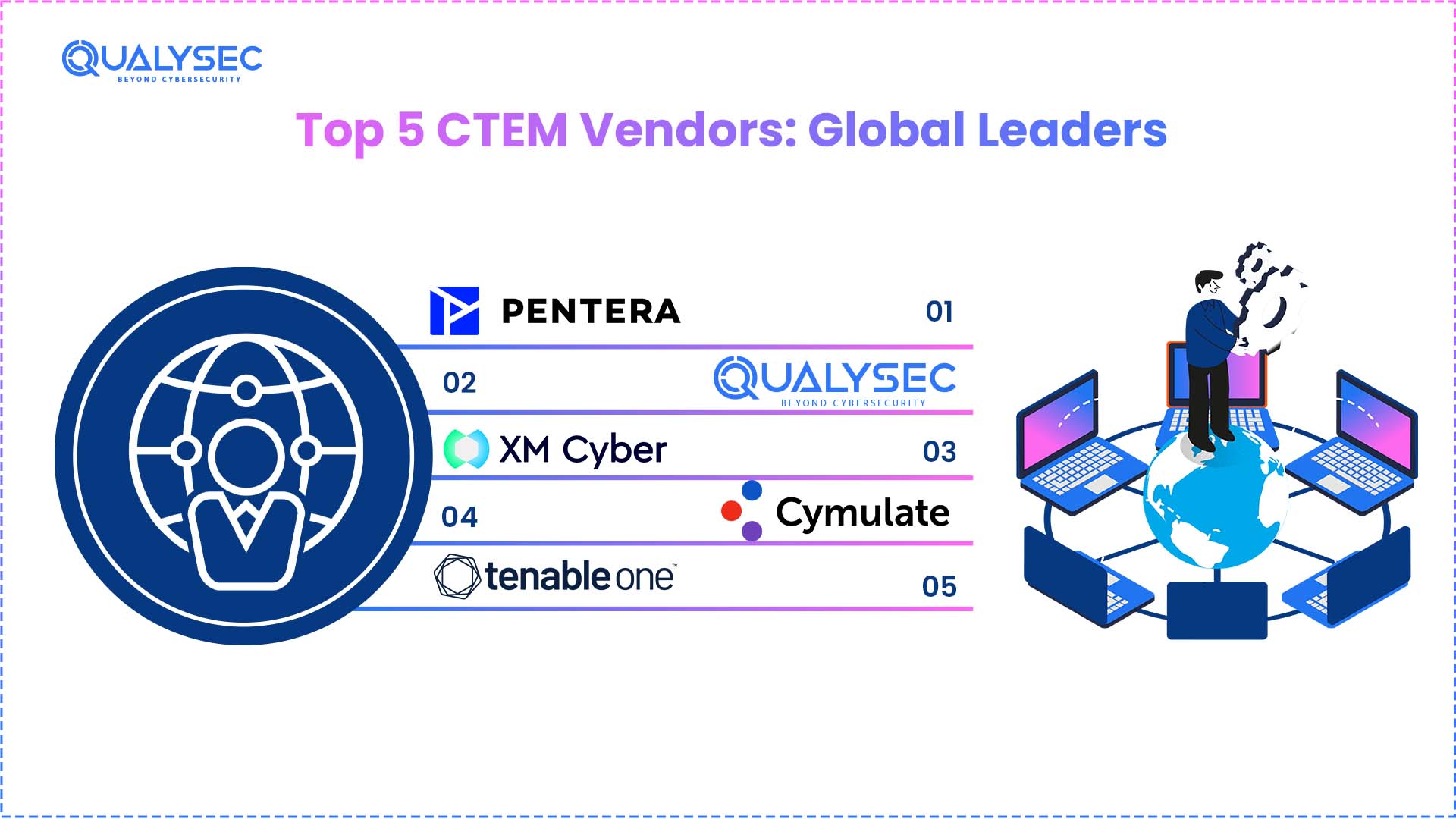
Note: The following vendors are highlighted based on their market visibility, platform capabilities, and industry recognition.This list is not exhaustive and does not constitute a formal ranking.
| Rank | Vendor | Core Strength | Best For |
| 1 | Pentera | Automated security validation | Enterprises seeking real-world attack simulations |
| 2 | Qualysec | AI-driven and human-led penetration testing | Organizations requiring full-lifecycle CTEM |
| 3 | XM Cyber | Attack path management | Hybrid and cloud environments |
| 4 | Cymulate | Breach and attack simulation | Continuous security validation |
| 5 | Tenable One | Exposure management platform | Large enterprises need comprehensive visibility |
1. Pentera
Pentera built its reputation on automated penetration testing that mimics real attacker behaviour. Enterprises that need continuous, evidence-based validation without scheduling quarterly manual assessments rely on it as become a go-to solution among top cybersecurity companies globally.
2. Qualysec
Qualysec combines AI-assisted attack simulation with human-led testing across web, mobile, cloud, API, and IoT environments. Its approach focuses on validating exposures across different stages of CTEM, helping organizations bridge the gap between automated findings and deeper, expert-led analysis.
3. XM Cyber
Most tools tell you what’s exposed. XM Cyber tells you the path an attacker would actually take to get somewhere critical. That attack path context changes, which fixes the matter, and which ones can wait.
4. Cymulate
Cymulate runs continuous breach-and-attack simulations to test whether existing security controls actually hold up. It’s a practical, ongoing validation rather than point-in-time testing.
5. Tenable One
Tenable One pulls IT, cloud, OT, and IoT into a single platform. For security teams managing sprawling infrastructure across regions, that unified visibility alone justifies the conversation.
How to Choose the Right CTEM Vendor
Picking from the available CTEM vendors isn’t just a technical decision; it’s a business one. The wrong fit costs time, budget, and security posture.
A few things worth checking before committing:
- All five CTEM stages covered. Scoping through mobilization. If a vendor skips validation or mobilization, it’s not a full program.
- Plays well with existing tools. SIEM, SOAR, ticketing systems. Integration gaps slow remediation down.
- Risk-based prioritization, not just severity scores. Context matters more than raw CVSS numbers.
- Continuous validation is built in. Pentesting or BAS should not be an optional add-on.
- Compliance support. NIS2, DORA, GDPR, and SEC rules. Your cybersecurity platform providers should understand these requirements, not just acknowledge them.
- Scales with your environment. Cloud, hybrid, global operations included.
- Reporting that shows actual risk reduction. Not just activity metrics.
The right vendor fits where you are and grows with where you’re going.
How CTEM Success Is Measured
CTEM is not just about finding exposures. It is measured by how effectively risk is reduced over time. Key metrics include:
- MTTR (Mean Time to Remediate)
How quickly validated exposures are resolved - Exposure Window
The time between when a risk appears and when it is fixed - Risk Reduction Trends
Whether overall exposure is decreasing across the environment - Validation Coverage
The percentage of critical assets and attack paths that are actively tested
These metrics help security teams demonstrate progress and align security efforts with business outcomes.
CTEM Vendors Certification and Training
Currently, no universally recognised CTEM-specific certification exists. As a framework rather than a formal standard, organizations developed CTEM knowledge industry training, cybersecurity certifications, and vendor-led programs.
What’s actually out there worth looking at:
- SANS Institute and GIAC certifications cover threat exposure, penetration testing, and risk validation in depth
- Vendor-led training programs from platforms like Tenable, XM Cyber, and Cymulate teach CTEM through the lens of their own tooling, which is practical if you’re already in their ecosystem
- NobleProg runs dedicated CTEM courses built around implementation and prioritization
- Gartner research and aligned workshops help leadership teams understand the strategic side, not just the technical side
Getting trained matters because the five-stage framework only delivers results when the people running it actually understand it. Buying the platform is the easy part.
Quick Verdict
Cybersecurity teams that are still running quarterly scans and patching by CVSS score are already behind. CTEM isn’t a trend; it’s where serious security programs are landing. Continuous visibility, actual validation, and risk that maps to business impact define how CTEM vendors operate today. That’s the shift happening right now, whether organisations move with it or not. For those wanting expert-led exposure management that actually delivers, Qualysec is worth a serious look.
Conclusion
Threat landscapes continue to evolve, and periodic patching alone can no longer keep pace with modern risks. CTEM shifts the focus from reactive vulnerability management to continuous, risk-driven exposure management. As leading cybersecurity service providers align their strategies around this approach, organisations that adopt CTEM today position themselves to manage tomorrow’s threats with confidence and resilience.
Schedule a call with our Qualysec expert to start fixing real security risks today.
Speak directly with Qualysec’s certified professionals to identify vulnerabilities before attackers do.
FAQs
1. Who are the leaders in the CTEM market?
Pentera, Qualysec, XM Cyber, Cymulate, and Tenable One are the names coming up most consistently in 2026. Each brings something different. Pentera for automated validation, Qualysec for combined AI and human-led testing, XM Cyber for attack path context, Cymulate for continuous BAS, and Tenable One for broad enterprise visibility. Shortlisting depends heavily on your environment and internal capacity.
2. How do I choose the right CTEM vendor?
Start with your gaps, not the feature lists. Does the vendor cover all five CTEM stages? Does it connect with what you already run, SIEM, EDR, ticketing? Can it validate exposures, not just find them? After that, look at managed service options, compliance reporting, and whether their metrics actually tell you something useful about risk reduction over time.
3. Do CTEM vendors offer managed services?
Most do, yes. Penetration Testing as a Service, Breach and Attack Simulation as a Service, and fully managed CTEM programs are fairly standard offerings now. For teams without large in-house security functions, managed services are often the only realistic path to running CTEM properly without stretching existing staff too thin.
4. Are CTEM vendors replacing traditional security vendors?
Do not exactly replace traditional tools; they fill in what traditional tools were never designed Most CTEM solutions sit alongside existing SIEM, EDR, and vulnerability scanners rather than pulling them out. The difference is what happens after detection. CTEM adds validation, prioritisation, and actual remediation workflows that legacy tools don’t handle well.

















































































































































































































































































































































































































































































































































































































































































































0 Comments