Today, organizations are constantly exposed to changing cyber threats that may pose a threat to sensitive information, affect operations, and harm reputation. Cyber security risk assessment report is, in short, the vital defense roadmap to your organization, and it is proof of the most thorough analysis of vulnerabilities, threats, and possible effects on all your digital infrastructure. It is a crucial document not only because it helps recognize where your organization is most at risk, but it also helps establish priorities in remediation and security strategy spending to protect what is critical.
The need for understanding and taking action on a successful cyber security risk assessment report is even more critical because hackers may take advantage of vulnerabilities in systems, processes, and human behavior. As a small business dealing with customer data or a large enterprise with complex IT environments, this ultimate guide will take you through all you should know about creating, understanding, and utilizing these important security reports.
Understanding What a Cybersecurity Risk Assessment Report Contains
There are various significant components in a good cyber security risk assessment report that function together. The report begins with a list of all digital assets of your company. These are data storage systems, networks, computers, and software. Consider it as compiling a list of all things of value that hackers can want to destroy, or more precisely, steal.
The cyber security risk assessment report then examines various forms of threats your business could be exposed to. There are numerous sources of such threats. Hackers are external, and they attempt to steal money or information. Internal employees can do it unconsciously by sending out passwords or clicking on malicious links. The report describes the threats that are likely to impact your particular type of business.
The report also finds weak spots in your security setup. These weak spots are called vulnerabilities. They might include:
- Old software that needs updates
- Weak passwords that are easy to guess
- Missing security programs like antivirus software
- Workers who need better training about online safety
Next, the IT security risk assessment report explains what could happen if hackers exploit these weak spots. Some issues could cost thousands of dollars. Others could put your business to a halt for several days or weeks. The report assists in knowing the risks that need correction at the earliest.
Lastly, the report provides a definite action plan for you. It gives you the exact step-by-step things to do to solve every problem. There are fast, inexpensive repairs. The others are more costly and time-consuming. The report assists you in the decision-making process of what ones to address first, depending on their risks.
Get Your Risk Assessment Report from Our Experts!
The Critical Importance of Cybersecurity Risk Assessment Reports
Core Components of Risk Assessment Reports
A cyber security risk assessment report contains several key parts that work together to protect your business:
- Complete list of all digital assets and systems
- Identification of potential cyber threats
- Analysis of security weaknesses and gaps
- Risk ratings for different threat scenarios
Types of Assets Covered
The cyber risk assessment report examines various business components:
- Hardware like computers, servers, and mobile devices
- Software programs and online applications
- Network equipment, including routers and firewalls
- Important data and customer information
Threat Analysis Section
Your IT security risk assessment report identifies specific dangers:
- External hackers trying to steal data or money
- Inside workers who might make security mistakes
- Malware and ransomware attacks
- Physical security risks to equipment
Ready to protect your business with a professional risk assessment? Talk with our experts at Qualysec today to get started.
Step-by-Step Process for Obtaining Your Risk Assessment Report
There are strategies and proper planning in order to acquire a good cyber security risk assessment report. The decision-making always begins with choosing what exactly in your business you want to assess. You can concentrate on your company as a whole or only on those departments that deal with sensitive information.
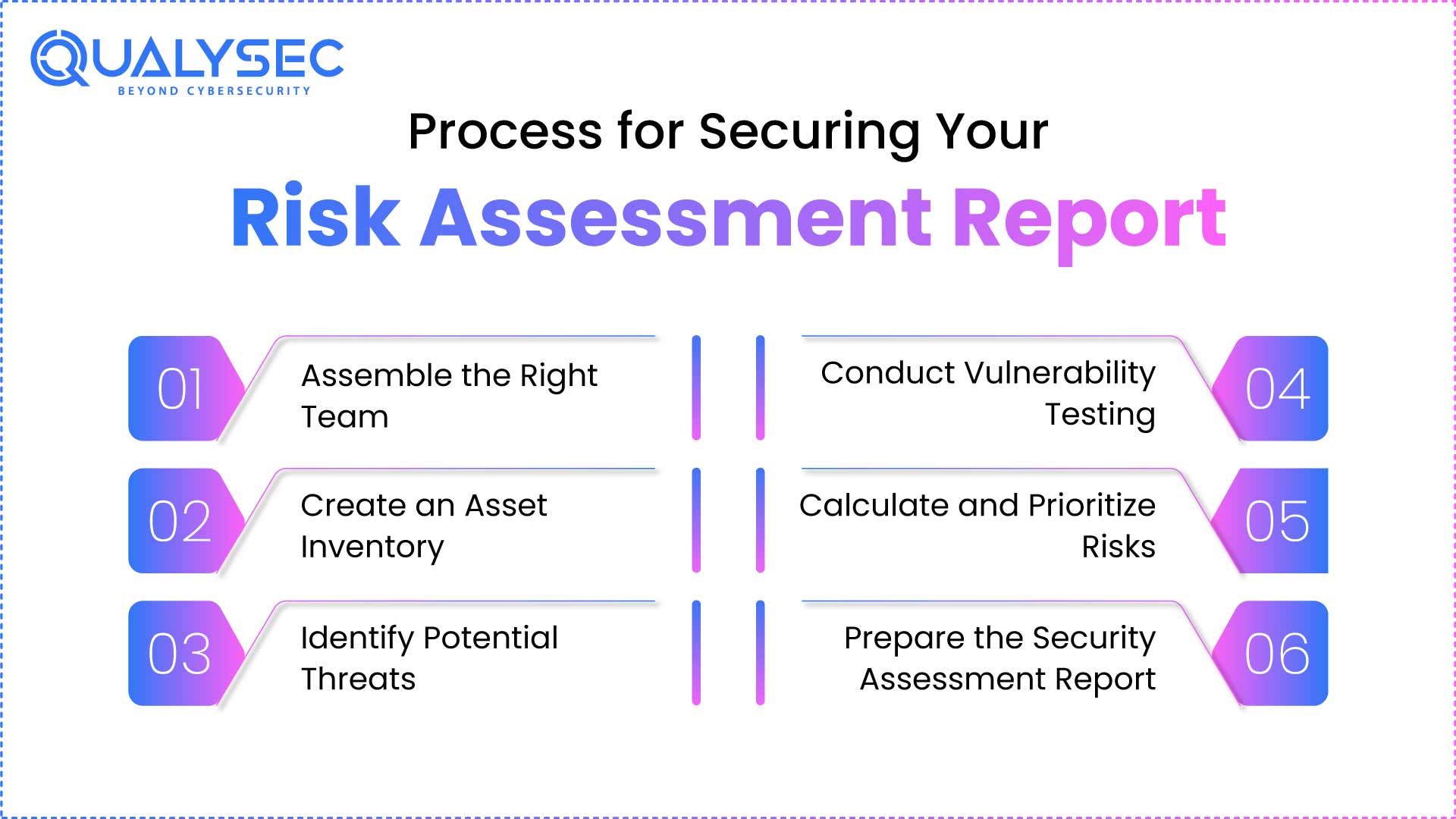
1. Assemble the Right Team:
The initial one entails gathering the appropriate individuals who belong to various sections of your company. You will also require individuals in IT, security, legal, and business departments. Each group will provide different knowledge that will make the assessment better and useful.
2. Create an Asset Inventory:
Next comes making a complete list of everything that needs protection. This inventory process includes:
- All computers, servers, and mobile devices
- Software programs and online services you use
- Network equipment like routers and wireless systems
- Important data and where it is stored
3. Identify Potential Threats:
Once the assets have been listed, the assessment team will consider the kind of attacks against which your business is likely to be attacked. They read reports concerning the cyber criminals and how they operate. They also consider the attacks that have been perpetrated against other companies in the same industry as yours.
4. Conduct Vulnerability Testing:
The vulnerability testing stage involves the use of special computer programs to conduct a sweep of security holes. Your systems are also manually scrutinized by security experts to locate the issues that could not be detected by the automated devices. This hybrid strategy has identified more problems when compared to a single method.
5. Calculate and Prioritize Risks:
It is all summed up by risk calculation. Ascertaining the likelihood and the amount of damage a particular type of attack can cause is what the team considers. They come up with ratings that enable you to understand which issues require attention as priorities. The problems that pose the highest risks are addressed immediately, whereas those of the lesser risks can be dealt with later.
6. Prepare the Security Assessment Report:
The next step builds your complete IT security risk analysis report outlining the recommendations. Every proposed solution will contain what needs to be done by whom, what the duration will be, and the possible expenses. This is real advice that will assist you in getting ready to take action and make your security better.
Read also: Our complete guide to Vapt Report.
Latest Penetration Testing Report

Key Elements Every Risk Assessment Report Should Include
A sample of a professional cyber security risk assessment report has a specific structure that qualifies it as helpful to various individuals in the company. The executive summary provides the leaders of the companies with an overview and not many technical details. Here, the emphasis is on business impact and what decision should be taken.
The description of how the assessment was conducted can be found in the methods section. It enumerates which tools it has used and what areas of the company it has examined. This data will assist you in getting to know the extent to which the assessment was conducted and in preparing to plan others.
The main findings section presents all discovered problems in an organized way. Each problem includes important details:
| What’s Included | Why It Matters | How It Helps |
| Problem Description | Understanding the issue | Know what needs fixing |
| How Hackers Could Use It | See the danger level | Decide how urgent it is |
| Business Impact | Know potential damage | Plan for worst-case scenarios |
| Risk Level | Compare different problems | Prioritize your efforts |
| Fix Recommendations | Know what to do | Take action to improve |
The action plan part converts findings into particular actions. It gives every task to the appropriate individual and proposes achievable deadlines. This roadmap would guide you to structure your efforts in making improvements and see progress over time.
Other parts of good reports are visual, such as Bubble charts and graphs. These simplify the sophisticated information to laymen who are not security experts. Images are sometimes much more effective than pages of text that provide information on levels of risk.
Also Explore cybersecurity penetration testing services.
Why Qualysec Stands Out in Cybersecurity Risk Assessment Reports
Unique Methodology and Expertise
When you need a professional cybersecurity risk assessment report, Qualysec offers distinct advantages. Our team combines advanced scanning technology with deep human expertise to find problems others might miss.
Don’t wait for cyber criminals to find your weaknesses. Schedule a free consultation with Qualysec today.
Comprehensive Reporting Approach
Qualysec’s cyber risk assessment reports stand out because we:
- Focus on your specific business needs and industry risks
- Provide clear explanations that non-technical leaders understand
- Include detailed technical guidance for IT teams
- Offer ongoing support for implementing recommendations
Business-Focused Solutions
Our approach ensures your risk assessment report for compliance delivers real value:
- Align security recommendations with business priorities
- Consider budget constraints and operational requirements
- Provide realistic timelines for security improvements
- Support long-term security planning and strategy development
Best Practices for Using Assessment Reports
Implementation Strategy
After receiving your cyber security risk assessment report:
- Start with the highest-risk items identified
- Assign clear ownership for each recommended action
- Set realistic deadlines based on complexity and resources
- Track progress regularly and adjust plans as needed
Ongoing Management
Risk assessment is not a one-time activity:
- Set follow-up evaluations on a regular basis
- Keep an eye out for new threats/vulnerabilities
- Adjust security features with changing technology
- Educate the employees on emerging security measures
Transform your cybersecurity with Qualysec’s expert assessment services. Contact us now for comprehensive protection.
Talk to our Cybersecurity Expert to discuss your specific needs and how we can help your business.
Conclusion
An effective cyber security risk assessment report can be the best way to improve security in your business. Based on these reports, you can know how to defend yourself, plan it, and secure the things that matter. They transform the perplexing security issues into working steps.
Periodically carrying out risk evaluation ensures you keep one step ahead of cyber criminals who are continuously seeking innovative methods of launching an assault on businesses. Firms that conduct such tests regularly experience security incidents of a lesser magnitude and a faster recovery period when challenges exist. Losses incurred due to the professional assessment are worth the money spent in averting the costly cyber attacks.
The digital world will remain in a changing mode, and new threats will constantly emerge. Companies that ensure they have regular cyber security risk assessment reports will be in a better position to face what is ahead. They will also keep the confidence of their customers and partners and secure their precious information and systems.
You built through work and reputation and took care of your customers. Never allow cyber criminals to obliterate that development in one attack. It is time to learn and fix your security risk before you get into trouble.
Transform your cybersecurity posture with Qualysec’s expert-led risk assessment services. Contact us now for a personalized consultation and discover how we can help protect your organization’s most valuable assets.
Frequently Asked Questions
Q: What is the purpose of a cyber risk assessment report?
Ans: A cyber risk assessment report aims to determine, investigate, and indicate priorities of cybersecurity risks that an organization has to its digital infrastructure. It gives practical information to the stakeholders to make effective decisions on whether the investment is worthwhile to use on security, the requirements for the security investment, and the risk mitigation strategies.
Q: Who needs to prepare a cyber security risk assessment report?
Ans: Every organization that either deals with digital data, has online systems, or has a regulatory requirement should develop a regular cyber security risk assessment report. These are all businesses of small and large scales, government, medical entities, banks, and schools.
Q: What compliance frameworks require a cyber risk assessment report?
Ans: Several frameworks also require risk assessment reports to be compliant, such as GDPR, HIPAA, SOX, PCI DSS, NIST Cybersecurity Framework, ISO 27001, and numerous regulations in this or that industry. Such evaluations are proof of due diligence and facilitate audit needs.
Q: How often should a cyber risk assessment be conducted?
Ans: Extensive cyber security risk assessment reports ought to be carried out by the majority of organizations every year, whereas high-risk environments necessitate quarterly updates. Nevertheless, important changes to the system, security incidents, or big changes in businesses that might change the risk terrain should also prompt the assessments.
Q: Can I prepare a cyber risk assessment report without hiring a third-party provider?
Ans: Although basic testing is fairly accessible through internal staff members, including an experienced provider, such as Qualysec, it makes a difference due to the coverage, objective observation, and industry best practices. An independent perspective is usually able to give insights into the blind spots and help apply credibility that is sometimes lacking in internal evaluation, especially in compliance evaluation efforts.












































































































































































































































































































































































































































































































































































































































































































0 Comments