UL 2900 penetration testing is becoming increasingly important, as over 51% of hospitals and clinics report being victims of malware on their medical devices. The FDA has experienced a 457% increase in reconnaissance activities, denial-of-service attacks, attempted exploitation, and other cyber incidents targeting its IT infrastructure, compared to pre-pandemic years. The recent cyberattacks, such as the Ascension cyberattack and Change Healthcare ransomware breach in 2024, demonstrate the extent to which cyber threats alter the face of patient care, supply chains, payment systems, and health services.
This risk is quickly increasing in number since numerous medical devices are currently interconnected. It is estimated that military IoMT will be worth from USD 13.12 billion in 2025 to USD 23.92 billion by 2031, which is an increase in the number of devices in hospitals, defense, and emergency services will be online. The faster the spread, the greater the need to have effective cyber protection. The UL 2900 penetration test is one of the major investments by device manufacturers.
Wish to secure your medical appliances? Register for UL 2900 penetration testing of Qualysec Technologies!
What Defines the UL 2900 Standard?
The UL 2900 standard is an instrument for testing and shielding devices that are linked to a network. This is applied to products primarily in hospitals, factories, and healthcare. UL Cybersecurity Assurance Program (UL CAP) made it. The standard guides manufacturers in the process of checking, testing, and demonstrating the capability of their equipment with regard to fending off cyber attacks. The FDA announced in 2018 that UL 2900-2-1 is a reasonable solution to demonstrating that a device is safe, and the makers can comply with regulatory requirements with the help of the solution.
Structure of the UL 2900 Standard
UL 2900 consists of several components that encompass various types of devices –
UL 2900-1 – General Requirements
It has fundamental regulations that apply to any product that can be connected to a network.
UL 2900-2-1 – Healthcare and Wellness Systems
This governs the medical equipment and wellness products. It is the most significant aspect for Internet of Medical Things (IoMT) makers.
UL 2900-2-2 – Industrial Control and Operational Technology System
This section explains control systems used in factories, medical manufacturing, and hospital automation.
Makers should also look into the device’s weaknesses, software flaws, firmware integrity, and malware in all sections. Claims like secure boot, encrypted data, or verified messages have to be demonstrated by repeatable tests. Compliance demonstration will reduce the risks and make the equipment less dangerous to patients and regulators.
Recommended Read: Penetration Testing – A Comprehensive Overview
Basic Requirements of UL 2900 Compliance
The UL 2900 compliance will entail a comprehensive inspection of the device at each point, including design, as well as during its use and post-use.
Threat Modeling
The engineers begin by determining how an attacker can exploit the device. They look at –
- How attackers could enter
- Paths for data
- Levels of privilege
- Worst possible scenarios
Core Security Assessments
1. Static Binary Analysis: Checks the code that has been generated against security loopholes, insecure libraries, or bad elements.
2. Fuzz Testing: Inserts invalid or random data into interfaces to detect crashes, memory leaks, or strange behavior.
3. Malware Inspection: Antifraud software packages of concealed or malevolent software.
4. Network Testing: Checks on open ports, communication services, encryption, and wireless protocols.
5. Post-Market Security: UL 2900 expects continued monitoring after the device has been sold.
This includes –
- Reviewing logs
- Installing patches
- Handling rollbacks
- Cryptographic life cycle management
- Securing supply chain components
Also, explore our latest article on What is Security Threat Assessment (STA) and Why It Matters.
UL 2900-2-2 Penetration Testing Phases
The UL 2900-2-2 provides specific regulations of industrial control systems (ICS), which may include medical manufacturing and hospital automation.
- Planning Phase: Professionals determine the scope of the tests, communication channels, protocols, and the level of exposure of the device.
- Execution of Tests: Lots of protocol fuzzing, memory testing, attempted elevation of privileges, and network simulated attacks.
- Wireless Evaluation: Checks Bluetooth, Wi-Fi, Zigbee, and proprietary RF technology for the possibility of unauthorized access.
- Risk Scoring: Security teams use CVSS scores to determine the most critical fixes depending on the actual threat.
UL 2900-2-2 also mandates the verification of bytecode and libraries in an attempt to detect any concealed issues. Testers should demonstrate that they can actually leverage the issues and hence the outcomes result in actual improvement.
UL 2900 Penetration Testing Methodology
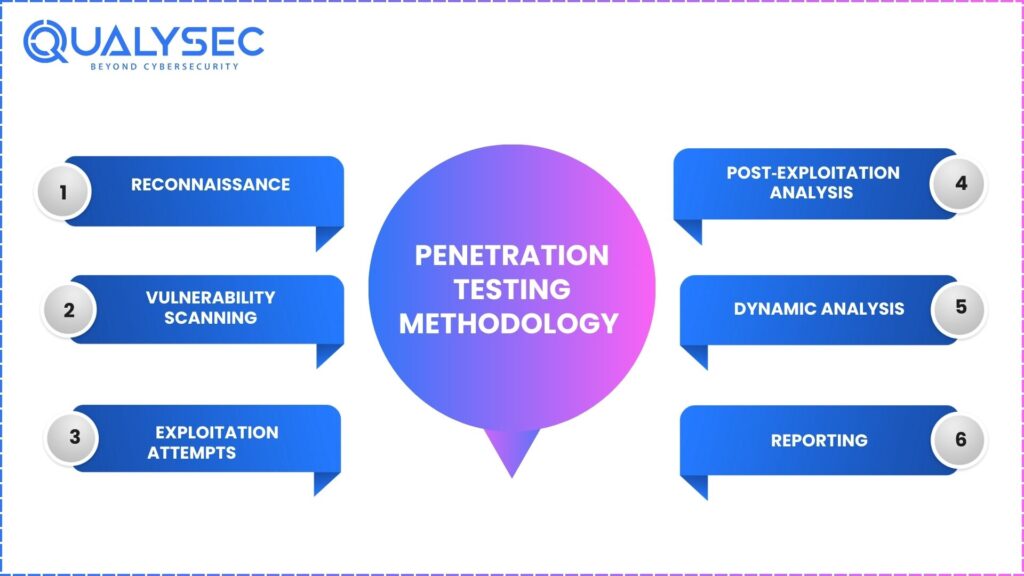
The systematic and repeatable methodology in UL 2900 replicates actual attacks.
1. Reconnaissance: Gather unintrusive intelligence to survey the system and locate areas of weakness.
2. Vulnerability Scanning: Automatic tools locate ancient libraries, feeble setups, and recognized CVEs.
3. Exploitation Attempts: Ethical hackers replicate actual intrusion attempts at the network, firmware, and application levels.
4. Post‑Exploitation Analysis: Examinations on the extent to which an attacker can penetrate, escalate privileges, or remain within the system.
5. Dynamic Analysis:
Examines behavior in real time with –
- Fuzz testing
- Protocol testing
- Resource exhaustion tests
- Crash analysis
6. Reporting: We list each vulnerability in the reports along with the ways of exploitation and the methods of fixing them so that developers can take action.
Download Today – Complete Penetration Testing Checklist for 2026
Agreement and Regulatory Alignment between the FDA and Other Regulatory Bodies
According to the FDA, UL 2900 is an acceptable standard of cybersecurity to be used in submissions of medical devices. The FDA guide of 2025 states that manufacturers have to employ an approach to security that embraces the entire life cycle.
How UL 2900 Supports Regulatory Compliance
- Makes qualified evidence of pre-market filings
- FIPS 140-3 Cryptography NIST standards
- Demonstrates safety in the design, coding, and updating
- Favors 510 (k), PMA, and De Novo pathways
This enhances the confidence of regulators that during cyber threats, the data on patients and clinical functions remain secure.
Major Cyber Threats to Medical Devices
Advanced cyber attacks will overwhelm the healthcare technology landscape due to increased IoMT interconnections, the use of cloud applications, and the continued operation of legacy systems in hospitals.
- Malware & Ransomware: More than 50 per cent of health systems report malware/pursuant to systems, and ransomware has been continuing to generate havoc with imaging systems, EHR-based devices, and medication pumps.
- Remote Access Exploits: Hackers are finding more and more targets in remote diagnostics and maintenance ports and exploiting weak authentication or open ports.
- Supply Chain Compromise: Weaknesses in third-party elements, drivers, and software provide backdoors in medical equipment.
- Data Exfiltration: Hackers steal PHI and other sensitive telemetry and use it to gain financial profits or extort.
- AI/ML Manipulation: With the emergence of AI-based diagnostics, patients can be in danger due to risks such as model poisoning and adversarial inputs.
Such threats underscore the necessity to implement powerful, consistent cybersecurity standards, including UL 2900.
Read the full guide on Medical Device Penetration Testing.
Benefits of UL 2900 Penetration Testing
UL 2900 penetration testing provides robust security and nonconformity benefits to manufacturers.
- Early Discovery: Catch problems before a regulatory review or market release, and minimize recall and breaches.
- Regulatory Confidence: Enforcement of FDA submissions and establishment of defensible evidence on cybersecurity.
- Enhanced Patient Safety: Lowers the risks of manipulating devices, data breaches, or downtimes.
- Operational ROI and Financial ROI: Eliminates loss of time, fines, legal claims, and loss of brand.
- Scalable Security: Prepares organisations to develop IoMT solutions with security in different categories of devices.
Get a Free Sample Pentest Report

How Qualysec Technologies Can Help You
Qualysec Technologies is a reputable cybersecurity and compliance company that focuses on UL 2900 testing of medical and IoMT device penetration. The combination of practical trial with sophisticated automated equipment is used to identify vulnerabilities in firmware, networks, wireless interfaces, and software. We are well informed of the requirements of the FDA and the UL compliance processes and can assist manufacturers to be placed in a better position to adhere to with ease and speed.
The fix guides and support provided by us in the form of detail and documentation make the process of certification more efficient. Both start-up and large organizations, Qualysec provides precise, repeatable, and scalable evaluations to enhance device resilience and ensure that you will be prepared to face the upcoming cyber threats. How are we different? Read to find out –
Proven Methods
The strength of our cybersecurity services is our proven test approach. Re-tests allow us to be better than normal approaches and provide the best UL 2900 penetration testing ever. Clients rely on us.
AI + Human Approach
We test by mixing automated and hands-on methods until we are sure we have tested everything. Our engineers recheck to locate all the weaknesses. We examine everything – static code, fuzzing, wireless, network ports, and a review of the bill of materials.
Documented Reporting
We also provide comprehensive reports that indicate precisely the locations of the problems and how to fix them, and you can use these reports for compliance documentation.
Remedy Assistance
After completing the test, our professionals will assist in patching the problems and maintaining a healthy level of security. We provide online support for troubleshooting and always deliver clear answers.UL 2900 is a necessity that needs to be undertaken by medical device manufacturers wishing to still be in business in 2025 and beyond in the face of cyber threats.
Compliance Friendly
We design our tests to support the medical equipment, including IoMT and guarding patient information. They are compatible with the FDA regulations.
Comparatively Faster
Our unique approach is time-saving, yet it provides all the information so that the clients can complete certification within a shorter period of time.
Services for Companies of All Sizes
Our services are open to all companies, big and small. We have assisted large corporations and small startups with an array of cybersecurity services. Our solutions also expand with your devices, whether it be wearables or large industrial controls.
Partner with our UL 2900-certified security team to identify vulnerabilities before attackers do. Schedule a consultation with Qualysec Technologies today!
Conclusion
UL 2900 is a necessity that needs to be undertaken by medical device manufacturers wishing to still be in business in 2025 and beyond in the face of cyber threats. As healthcare-related cyberattacks continue to increase, UL 2900 provides a sound and justifiable security foundation required by the industry. Collaboration with experts like Qualysec accelerates the compliance, increases the security of devices, and preserves the trust of the patients.
Get your UL 2900 assessment from our experts and understand exactly what your product needs to meet regulatory and security expectations. Book today!
Speak directly with Qualysec’s certified professionals to identify vulnerabilities before attackers do.
Frequently Asked Questions (FAQs).
1. What is in UL 2900 penetration testing?
UL 2900 testing is a check on the cyber strength of a device. It analyzes the software, performs a review of the bill of materials, tests with random data (fuzz), attempts to break the network and wireless components, scans for malware, and tries to use the vulnerabilities. The goal is to locate soft points to ensure that attackers do not cause damage.
2. How does UL 2900 align with FDA requirements?
UL 2900 complies with FDA regulations of pre-market and post-market cyber safety. It demonstrates evidence of secure design, how risks are managed, and that the software is functioning. The FDA accepts UL 2900‑2‑1. The findings are useful in 510(k), CAP, and audits in order to meet federal standards.
3. Why is UL 2900 important in 2025 and 2026?
Distribution of cyber attacks on the healthcare sector is on the rise: 51 percent of websites are targeted by malware, and ransomware paralyzes care. The more devices of the IoMT, the larger the attack surface. UL 2900 puts the pressure on serious testing of modern attacks, enabling makers to reduce the risk, comply with regulating bodies, and retain trust.
4. What to do after UL2900 testing?
A detailed report of each vulnerability, the way it works, and how to fix it is provided after testing. Our team fixes the bugs, upgrades the software or configurations, reinforces logs and ciphers, as well as verifies the fixes. The updates are recorded in regulatory files, audits, and internal checks to make sure the device is secure.
5. Is it possible to make legacy devices UL-compliant?
Yes. With risk in mind, even old devices can comply with UL 2900. We perform selective penetration tests, patch old parts, harden settings, introduce backup controls, and upgrade weak communication. By updating with attention to detail and safeguarding the layers, you may easily fulfill the current standards in cyber, even when the underlying hardware may not be alterable.





















































































































































































































































































































































































































































































































































































































































































































0 Comments