Did you know that the average cost of a data breach in India soared to ₹19.5 crore in 2024? That’s a 9% jump from the previous year and a stunning 39% rise since 2020. The global breach costs share the same trend, reaching a record of USD 4.88 million in 2024. This reiterates the need for an effective and reliable Application Security Assessment.
Whether you’re launching a fintech app, scaling a SaaS platform, or building a telehealth product, security failures pose a real risk. From breaking trust to getting regulatory scrutiny, reputation damage is just a step away.
Application security assessments are more than a buzzword. It is a structured process to uncover critical weaknesses in your application before malicious attackers do. Learn more about application security testing services.
In this guide, we explain everything – what a security assessment actually involves, its importance, the checklist, and more.
Application Security Assessment: What Does This Mean?
In technical terms, an application security assessment is a comprehensive, methodical evaluation of your app’s architecture, code, and behavior. Experts generally do it to identify vulnerabilities in the application. This includes:
- Authentication and session handling flaws
- Access control weaknesses
- API exposure risks
- Injection vulnerabilities (SQL, XSS, etc.)
- Insecure third-party libraries or plugins
- Misconfigurations in cloud services
- Business logic flaws that scanners simply don’t catch
A proper application security analysis combines automation with manual expertise to expose meaningful risks. It is not only about scanning, but instead more about understanding how your app behaves in the hands of a malicious attacker.
At Qualysec, we opt for a hybrid approach when performing application security assessments. We blend automated scans with manual discoveries to ensure nothing is missed.
Request a compliance-aligned assessment report for your audit needs.
Importance of Application Security Assessments
Let’s understand the current scenario to have a better understanding of why application security analysis is the need of the hour.
Most breaches don’t happen because attackers are brilliant. They mostly happen because someone assumed the app was secure enough.
In India, over 76% of data breaches in the past 18 months were traced back to insecure applications, misconfigured cloud setups, or unauthenticated APIs. The consequences? Compliance violations, financial loss, and an uphill battle to regain customer trust.
To ensure that doesn’t happen, you need to opt for an application security assessment. Here’s what can happen if you skip the application security vulnerability assessment:
- India’s Data Protection Board under the DPDP Act can now enforce breach reporting and levy penalties. Now, if you add ISO 27001, SOC 2, and RBI compliance, an unassessed app is a liability, not a grand launch anymore.
- Investors have recently started reviewing security checklists during due diligence. A single “pending” assessment can delay funding or trigger conditional terms.
- Keep in mind that the user data you get is equal to the integrity of the brand. Breaches not only contribute to the fall of revenue but also increase churn and damage your reputation across platforms and media.
Recommended: explore our guide on Application security best practices.
Application Security Assessment: Step-By-Step Process
Application security vulnerability assessments aren’t some vague checklists to tick off. If done right, they follow a transparent, collaborative process. Here’s a step-by-step process that typically unfolds in an application security assessment.
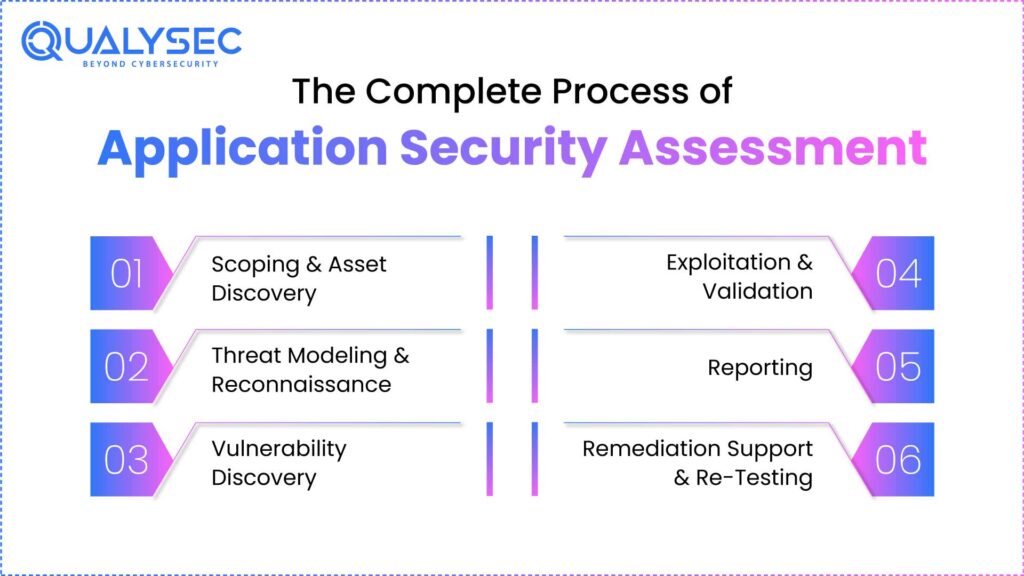
1. Scoping & Asset Discovery
The process begins with clearly defining the scope.
- What platforms are involved (web, mobile, APIs)?
- Is this black-box, grey-box, or white-box testing?
- What environments will be used (staging, pre-prod)?
- Are there compliance requirements tied to the deliverables?
The more accurate the scope, the more focused the assessment.
2. Threat Modelling & Reconnaissance
In the next step, the expert team builds an attacker’s mental map of the application. These include –
- Entry points
- Data flows across functions
- Third-party integrations
- Business-critical logic paths
3. Vulnerability Discovery
In this stage, manual and automated testing begin. Experts simulate exploit scenarios across:
- Authentication and session handling
- Role-based access control
- Input validation and output encoding
- API endpoints
- Cloud asset configurations
- Injection points and error handling
It is at this stage that the issues are confirmed instead of simply guessing them.
4. Exploitation & Validation
Vulnerabilities are verified through controlled exploitation to prove impact:
- Can an unauthenticated user access privileged functions?
- Can chained flaws lead to data exfiltration?
- Could improper logic let users bypass workflows?
False positives are filtered out.
5. Reporting
A well-conducted report includes:
- Executive summary
- Technical breakdown of each finding
- Severity rating (based on CVSS or risk models)
- Proof-of-concept evidence
- Steps to reproduce
- Clear, actionable remediation guidance
- Compliance mapping (ISO, SOC2, etc.)
6. Remediation Support & Re-Testing
Here’s where most providers fail to live up to. You will definitely need help interpreting findings, implementing fixes, and confirming closure. And here is where Qualysec steps in. Our experts stay involved until issues are resolved and validated.
Latest Penetration Testing Report

The Qualysec Method: How We Deliver Secure, Audit-Ready Reports
At Qualysec, we approach every application as if it’s already under attack. That is because we understand exactly how real-world breaches happen. Here’s what sets our approach apart:
We Simulate Attacker Behavior
Qualysec don’t just conduct tool-based checks; we simulate real-world attacks. We focus on finding logic flaws, trust boundary violations, and real-world exploit chains that automation misses.
We Align With Your Compliance Goals
Whether you’re aiming for ISO 27001, SOC 2, HIPAA, FDA, PCI DSS,or GDPR testing, our assessments are mapped to those frameworks.
We Are Always Available
Whether you’re a fintech founder under pressure or a product manager looking to launch securely, we help you cover vulnerabilities and secure them seamlessly. And if you have queries, we are always glad to answer.
To know more, talk to our experts today!
Conclusion
Whether you’re preparing for ISO 27001, chasing a funding round, or launching a product that holds user data, application security isn’t a checkbox. It’s a foundation. One missed flaw can undo months of engineering and marketing in a single breach.
A proper assessment gives you more than a report. It shows you how your application holds up under pressure, where it’s exposed, and how to close the gaps.
At Qualysec, we provide compliance-aligned reporting and effective security assessments to ensure your app is secure and ready to launch.
Explore our flexible pricing plans designed to suit startups, enterprises, and everything in between
Talk to our Cybersecurity Expert to discuss your specific needs and how we can help your business.
FAQs:
1. How to test an application for security?
Testing an application for security involves –
- Scoping the environment (web, mobile, API, cloud)
- Running automated scans to catch baseline issues
- Conducting manual testing to identify logic flaws, chained exploits, and access control issues
- Validating findings with real-world impact
- Creating a remediation roadmap
This is done through a well-structured application security assessment. To explore this in more detail, check out our approach.
2. What is a software security assessment?
A software security assessment is a comprehensive review of an application’s code, configurations, and behavior to identify vulnerabilities. The goal is to find security gaps before attackers do.
3. What is the security assessment?
A security assessment is a methodical process where trained experts evaluate the security posture of your software, infrastructure, or environment. It aids in finding technical flaws, architectural issues, and more.
4. How long does a security assessment take?
The time it takes to complete a security assessment depends on the size and complexity of the application. However, it can take anywhere between 2-4 weeks.
5. What are the three main types of security assessments?
The three main types of security assessments are black-box assessment, grey-box assessment, and white-box assessment. You can request the type you want depending on the app’s security needs.





















































































































































































































































































































































































































































































































































































































































































































0 Comments