Introduction: The Incident at a Glance
On 19th April 2026, Vercel, the world’s most widely used cloud deployment platform and the company behind Next.js, disclosed a serious security incident. On X, Guillermo Rauch, Vercel’s CEO, tweeted to the community about the breach and outlined the next actions that needed to be considered.
The incident did not start directly on Vercel’s infrastructure. Instead, it got through a third-party app OAuth app integration with Context.ai, which was being internally used by some of the employees at Vercel. Screenshots of the stolen data began appearing on Reddit and hacker forums simultaneously. One user said they were selling access to Vercel’s internal systems for $ 2 million.
Attackers compromised Context.ai, abused the OAuth access and used the path to intrude into Vercel’s internal systems through a Google Workspace account. Later, the attackers stole the data and listed the same for sale on underground forums. Vercel took immediate action by revoking the tokens, notifying the customers and then advising everyone to rotate their secrets.
Through this blog, we will walk you through the entire incident in plain language. We will cover how it started, what was stolen, who was impacted, and what the best practices one can apprehend if you or your team is a user of Vercel. This incident is a stringent warning that in 2026, the security of a major platform like Vercel was undermined by the vulnerability of a single, connected third-party app.
Check the 2026 Cloud Security Assessment Checklist to identify hidden OAuth risks today.
Background: Who Are Vercel and Context.ai?
Before diving deeper, let’s understand the players involved in this event.
- Vercel is a cloud platform that lets developers host and deploy websites and web applications securely. It is the company that owns Next.js, one of the most popular React frameworks in the world. Nowadays, Vercel has become a platform whereby millions of websites and projects, ranging from small projects to large enterprises, are being deployed and hosted. This is what it peaks up as a target source for attackers.
- Context.ai is a tool which helps companies build AI agents that get smarter every week. This is being used to analyze user conversations, monitor AI product performance, and gain insights from large volumes of data, which would help the companies. Like many SaaS products, Context.ai integrates with other tools using OAuth, a standard protocol that allows one application to access data from another without needing the user’s password.
- OAuth, in its simplest form, means giving a spare key to your house to your trusted friend. This friend can come, do whatever he feels like in your house, implying he can do that much whatever he has been allowed to. But, once the spare key has been stolen from your friend by any other third person, then there is a high risk that your house is in danger, and a third person has access to your house. This is what the recent scenario is all about.
Timeline: How the Breach Unfolded
The first step to understanding the risk is to understand when and how the incident occurred. Here is a simplified timeline based on Vercel’s official bulletin and Context.ai’s security update.
- June 2024: It starts here. Hackers break into Context.ai’s OAuth app, tied to their Google client ID (Google client ID: 110671459871-30f1spbu0hptbs60cb4vsmv79i7bbvqj.apps.googleusercontent.com). Over the next 22 months, these attackers quietly steal tokens, hiding in regular traffic and staying off the radar.
- March 2026: Context.ai finally spots something odd; unauthorized AWS access. They block it with CrowdStrike, but miss the bigger issue where attackers have already exfiltrated OAuth tokens. Then, Context.ai kills off its consumer Office Suite and alerts one customer.
- Early April 2026: Now with stolen tokens in hand, hackers hijack a Vercel employee’s Google Workspace account. (over-permissioned “Allow All” scopes). This opens the door to Vercel’s internal environment. The attackers checked out about 580 employee records and poked around some non-sensitive API keys and database credentials. The good news: no core customer apps or production data were accessed.
- April 19, 2:02 AM ET: ShinyHunters, a known “pay or leak” group, pops up on BreachForums, claiming to have Vercel’s internal data, asking $2 million for it. Their sample includes employee info, NPM and GitHub tokens, even access to Vercel’s Linear.
- April 19, 11:04 AM PST: Vercel goes public, posting a Knowledge Base Bulletin to confirm “unauthorized access to certain internal systems.”
- April 19-20: Recently, Context.ai was named, Vercel fixes up some UI issues with environment variables, and starts notifying affected customers directly.
The Root Cause: How the Breach Actually Happened
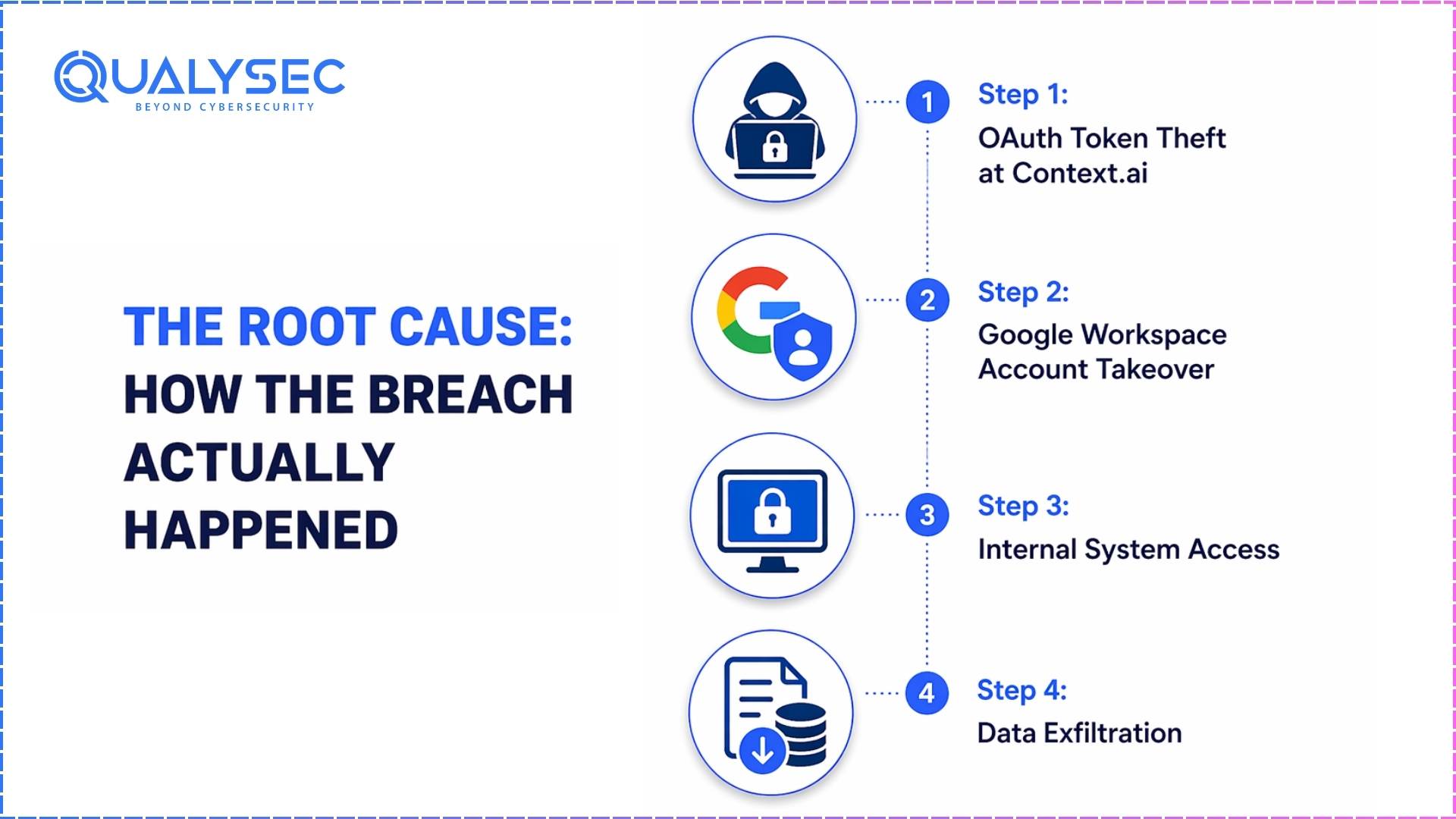
The breach was navigated through a technical path that abused the OAuth implementation gaps:
Step 1: OAuth Token Theft at Context.ai
Attackers got in through Context.ai’s Google OAuth app, which had permission scopes that were far too broad. They exploited this for nearly two years, collecting refresh tokens. Because these tokens don’t need constant re-authentication, the attackers just blended right in.
Step 2: Google Workspace Account Takeover
With those tokens, they accessed a Vercel engineer’s Google Workspace account that had SSO to Vercel and “Allow All” permissions. This basically gave them a skeleton key to internal tools.
Step 3: Internal System Access
Once inside, attackers could access the dashboard and peek at environment variables not marked as sensitive. They found some API keys, database credentials (for specific customer projects), and about 580 employee records from internal tools.
Step 4: Data Exfiltration
The attackers downloaded what they wanted, leaving everything else untouched. No NPM packages were touched, and production deployments kept running as normal.
The key technical weaknesses were:
- OAuth apps handed out too many permissions.
- No token binding or PKCE (Proof Key for Code Exchange) to tie tokens to a device or session.
- Some environment variables weren’t marked as sensitive.
- Nobody was really watching what third-party OAuth apps were doing.
What Data Was Compromised?
Vercel confirmed the following data was accessed:
Likely accessed:
- Internal employee chats and project documentation
- Deployment logs (which could have customer project metadata)
- Some environment variables and secrets were exposed by OAuth
- References to internal tooling in source code
- Customer email addresses tied to deployments
Possibly accessed but unconfirmed:
- Actual customer project source code hosted on Vercel
- Customers’ API tokens
- Billing info and account metadata
| Data Category | Specific Items Accessed | Risk Level | Action Required |
| Employee Records | 580 records (names, emails, employment status, timestamps) | Low | Monitor for phishing |
| Environment Variables | Non-sensitive API keys and database credentials from limited projects | Medium | Rotate immediately |
| Internal Tokens | NPM and GitHub tokens (claimed by attackers) | High | Check and rotate |
| Internal Tools | Linear project management data | Medium | Review access logs |
| Customer Applications | None | None | No action needed |
| Production Systems | None | None | No action needed |
The Vercel breach proves that no platform is 100% safe. Secure your cloud infrastructure before the next breach happens—get a free security assessment consultation from the experts at Qualysec.
ShinyHunters claimed they got a lot more, but so far, Vercel says only those initial samples are confirmed. The company insists there’s no evidence of stolen production data or customer source code. Everyone who might’ve been affected got a direct notice.
Not affected based on current information:
- Customer passwords (they only store hashed versions anyway)
- Production deployments (no changes)
- Payment card data (all handled by outside processors)
One more thing: Vercel admits the investigation isn’t over. They’re still figuring out the full reach of the breach, so customers are being told to rotate secrets just to be safe, even if their specific accounts haven’t yet been compromised.
Vercel’s Response
Vercel’s response on this part is commendably fast and significant. After the incident, they took the following steps:
Immediate technical actions:
- Revoked every Context.ai OAuth token across their whole platform
- Segregated any internal systems affected by the breach
- Brought in outside incident response teams and law enforcement
- Double-checked that NPM registry packages and production systems weren’t tampered with
Public communication:
- Published a detailed Knowledge Base bulletin on April 19
- CEO Guillermo Rauch posted a direct technical thread on X explaining the attack chain
- Shared the exact OAuth Client ID used in the attack
- Updated the bulletin on April 20 with Context.ai attribution
Customer actions recommended:
- Rotate all environment variables and secrets in your Vercel projects.
- Check your Google Workspace for third-party OAuth apps—and revoke anything you don’t trust. Turn on two-factor authentication everywhere you can.
- Mark every environment variable as “sensitive” by default.
Product improvements shipped during the incident:
- The Dashboard now includes a proper environment variable overview.
- New variables are automatically marked as sensitive.
- Improved OAuth app monitoring is rolling out.
Honestly, Rauch’s directness stands out. In an industry where CEOs usually let the PR people spin a message, he faced it all head-on, and the developer crowd clearly noticed. This actually enhanced the impression of Vercel taking quick actions to bypass the situations.
Context.ai’s Response
Context.ai’s response has also been public but slightly more measured. Their security update page acknowledges the breach, apologizes to affected users, and outlines the steps they are taking.
Their actions:
- Revoked every OAuth token tied to their applications.
- Called in external experts for a complete forensic review.
- Notified every affected customer, Vercel included.
- Shared Indicators of Compromise (IOCs) with the public.
- Permanently discontinued the affected consumer product.
- Forced new passwords and rotated internal credentials.
They’ve been clear: the breach hit their OAuth app, not their main AI research tools. The community’s reaction? All over the map—some respect the transparency, others wish they’d shared more technical details, especially why Context.ai was storing long-lived OAuth tokens in the first place.
How the Developer Community Is Reacting
The social media platforms and developer forums have shown strong reactions to this situation. Security professionals have been dissecting the attack chain as a textbook example of supply chain risk. The community has maintained this warning for years about connecting AI tools to sensitive systems without review, which this incident supports.
Developers who participate in cloud-focused forums are evaluating whether different platforms offer better protection than their competitors. The research shows that all platforms face risks because their system design creates permanent vulnerabilities which exist independently of Vercel’s specific security weaknesses.
People are engaging in passionate arguments about the ShinyHunters listing, which has led to extensive screenshot sharing, while most security-aware users proceed cautiously to authenticate the material. Rauch’s thread on X has attracted thousands of replies that display both supportive and critical opinions. Developers want to know which specific accounts on their systems Vercel’s team has been answering all day.
The technical blogs Juliet.sh and CanTech have created comprehensive analyses, while BleepingComputer, Dark Reading and ITNews report on this incident as a crucial supply chain security breach.
The Bigger Picture: Why OAuth and SaaS-to-SaaS Risk Is the New Frontier
The current breach constitutes a supply chain security breach, which has occurred in multiple instances before this one. The current breach follows a series of supply chain attacks which have become more common in recent years.
GitHub reported an identical event in 2022 when third-party OAuth tokens were stolen and used to gain entry into private repositories. The year 2023 witnessed multiple supply chain attacks which targeted NPM packages and their automated systems. The theme shows a constant connection. Big platforms now face attacks from attackers who focus on their smaller security tools, which provide extensive system access.
Software development today faces its main challenge because modern development processes create complete dependency between different software components. Most development teams operate with about fifty SaaS tools which give them various degrees of access to sensitive company information. Each tool provides hackers with the opportunity to enter the system. The modern attacks use authorized user credentials, which creates challenges for detection because security systems need traditional firewall breaches to identify threats.
OAuth was designed to be secure when used correctly, but in practice, it has weaknesses:
- Scopes are often too broad
- Tokens are often long-lived
- Users rarely audit which apps have access
- There’s no standard way to monitor what a connected app is doing with the access granted
Events like this will keep on happening until enterprises shift their approach from the root level to acknowledge how to approach third-party risk.
According to recent industry data, OAuth-related attacks rose roughly 300% in 2025. The upcoming year will bring stricter rules about OAuth monitoring and third-party application approval processes.
Qualysec’s cloud pentest gives you results—no endless emails, no digging through PDFs, no guesswork.

What Vercel Customers Should Do Right Now
If you or your team uses Vercel in this critical situation, these are the immediate, clear checklist you need to act upon.
Immediate actions (do within the next hour):
- Log in to Vercel’s dashboard.
- Turn every project’s environment variable.
- Check Settings Review Integrations for unknown OAuth applications and revoke them.
- If you have not already done so, turn on two-factor authentication.
- Designate all credential-bearing factors as sensitive.
Within the following 24 hours:
- Check review deployment logs for odd behavior in the last few weeks.
- Search for forbidden deployments or changes in environment variables.
- Check Google Workspace for undiscovered linked apps.
- Make sure your domain and DNS configurations have not been altered.
- See Have I Been Pwned for employee emails.
Within the next week:
- Check your full SaaS inventory linked to cloud providers, GitHub, and Vercel.
- Ask whether the access it provides is really required for every integration.
- Ascertain whether GDPR, CCPA, or HIPAA call for breach notification as a result of this event.
- Plan for forward-looking secret rotation on a schedule.
Long-term OAuth best practices:
- Least Privilege Principle: Ask just for the particular scopes your program calls for.
- Short Token Lifetimes: Set refresh tokens to expire fast.
- PKCE Implementation: Always use Proof Key for Code Exchange
- Token Binding: Link tokens to particular customer instances.
- Regular Audits: Review quarterly third-party integrations with regular audits.
- Automated Monitoring: Put up utilities to automatically check OAuth activity all the time.
- External Secret Managers: Use 1Password, AWS Secrets Manager, or similar for sensitive credentials from outside Secret Managers.
Lessons for Developers and Security Teams
Beyond this specific incident of the Vercel breaches, we have so many lessons to learn.
The first lesson deals with the idea of least privilege. A third-party app should receive the least amount of access required for it to run, not the greatest amount it seeks. Platforms should make their OAuth scopes more granular; developers should push back when OAuth permission screens ask for wide permissions.
The second lesson addresses control of token lifespan. OAuth tokens that last a long time are a liability. Short-lived tokens featuring refresh mechanisms are safer, as even if they are stolen, the window for misuse is limited. More systems should follow this pattern.
The third lesson discusses vendor security assessments. Before any equipment is integrated into your crucial infrastructure, a member of your team ought to assess the vendor’s security measures. This does not have to be a complete audit; simple inquiries about their handling of incidents, who has access to credentials, and how they store them should be addressed.
The fourth lesson covers detection. Before being discovered, the attackers had access for several days. Though it’s quicker than usual, it’s still too sluggish. Organisations require more effective technologies to track unexpected activity from linked integrations, such as spikes in API calls, access from fresh places, or queries for strange data.
The fifth lesson covers incident preparedness. The first few hours following a breach are crucial. Every company should have a playbook with legal notifications, technical response measures, and communication templates. Given their presumably ready playbook, Vercel reacted fairly quickly.
Speak directly with Qualysec’s certified professionals to identify vulnerabilities before attackers do.
Conclusion: The New Reality of Cloud Security
The Vercel breach is more than just another item to pass by on the news. It marks a change that shows how the security scene has drastically evolved. The danger used to be only hackers penetrating firewalls. The threat is the unseen web of trusted relationships among the tools we utilize daily; any one of these can turn into a backdoor should it be compromised.
For developers, the lesson is to stop treating OAuth integrations as harmless conveniences. Every interaction is a choice on who you trust with your information; that trust must be gained and validated rather than freely distributed with a single click.
For companies, the lesson is that security is not a commodity you can just go out and buy and then forget about. It calls for continuous attention, professional review, and a readiness to invest in prevention instead of only hoping you will not be the next headline.
Vercel has responded quite well to this event, and the business will almost certainly come out of it with better security measures than before. But smart companies will not wait until their own fault to make changes. They will use what they learn here to act now.
Let this be the one thing you remove from this article. The issue in 2026 is not the security of your third-party integrations. It is whether you have any way of knowing. And if the response is no, today, rather than after you see your company’s name in the next breach news, is the time to correct that.
Protect Your Business from the Next Big Breach. Request a Free Security Assessment Quote!











































































































































































































































































































































































































































































































































































































































































































0 Comments