Are you concerned about the security of your business against cyber threats? Software Security Companies have become very crucial in protecting the digital property in the modern networked society. Furthermore, due to the increased complexity of all cyberattacks, the selection of the appropriate partner has never been of utmost importance. Indeed, the US has the highest average data breach of more than 9.4 million, which is expensive. Consequently, Software Security Companies in USA require the services of credible software protection firms that can provide actual protection. This ultimate resource identifies the top 10 providers that are outstanding in ensuring that organizations remain secure. Moreover, we will let you know what makes these cyber security software companies stand out among the rivals.
How Were These Companies Selected? Understanding Our Criteria
The decision on the best software security firms should be carefully made. Therefore, we have employed a number of criteria to determine the leaders in this space. Also, you receive the right information that is useful because of our selection process.
Key Selection Parameters
- Market Presence and Industry Recognition: First, we analyzed the presence of each company in the cybersecurity industry. The firms that are well-established normally have thousands of customers. Likewise, there are awards and certifications in the industry that show dedication to excellence. Thus, sellers who have a record of success were rated higher in our analysis.
- Next, Innovation and Technology Leadership: We evaluated technological capabilities and innovation. There were better scores on internet protection companies that utilize AI, machine learning, and automation. We also examined their response rate to new threats. Additionally, firms that invest in research and development are viable in the long term.
- Trust and Satisfaction among Clients: In addition, client feedback is important. We have checked testimonials, case studies, and independent ratings by more than 3,000 U.S.-based IT decision-makers. Then, the companies that have received top scores in the surveys of satisfaction and positive reviews gained the first places. Moreover, we have taken into consideration client loyalty and retention rates.
- Full Service Provisions: Lastly, we also considered the coverage of security services. There are many solutions available under one roof by the best software security providers. This will, in turn, simplify and enhance general security. Moreover, the possibility of integration with the existing tools was taken into account.
| Evaluation Factor | Weight | Why It Matters |
| Market Presence | 25% | Indicates reliability and scale |
| Innovation | 25% | Shows future readiness |
| Client Satisfaction | 25% | Reflects real-world performance |
| Service Breadth | 25% | Ensures comprehensive coverage |
Top 10 Software Security Companies in the United States
1. QualySec – Leading the Pack in Application Security Excellence
In the case of software security companies, it is obvious that QualySec is the market leader. In addition, this company has transformed the manner in which businesses deal with application security. Thus, knowing what qualifies QualySec as a unique company can be a good reason why it is the first in our list.
All-Encompassing Security Testing Services: QualySec is an expert in penetration testing and vulnerability assessment. Moreover, they also provide software VAPT services, which help them locate security vulnerabilities before hackers are in place. Moreover, they use a mix of automated scanning and hand testing skills. As a result, clients are provided with detailed and proper security assessments.
Expert knowledge in the industry. The company has certified professionals who are experienced in the area of security. Likewise, their group follows the current attack vectors and defense measures. In addition, QualySec has alliances with large security frameworks. Thus, customers are exposed to the latest knowledge and established techniques.
Custom-fit Solutions to Each Business. As opposed to generic solutions, QualySec will design an assessment to fit your needs. Moreover, they cooperate with small-scale companies, medium-sized companies, and corporate clients. Moreover, the models of their flexible engagement are suited to different budgets and timeframes. As a result, businesses will have access to enterprise-level security.
- Web application penetration testing
- Cybersecurity of mobile applications
- API security testing
- Cloud security audits
- Network intrusion testing.
- Check testing (PCI DSS, HIPAA, SOC 2)
Why QualySec Excels:
- Continuous communication: Clients are involved in the testing process.
- Detailed reporting: Actionable findings with remedial suggestions.
- Quick turnaround: Effective testing without jeopardizing quality.
- Competitive pricing: high-end services at affordable prices.
- Viable history: Hundreds of successful projects in industries.
Location: United States
The excellence is what makes QualySec the best among cyber security software companies. They also have a customer-centred approach that will deliver maximum value to businesses. Moreover, they do not merely pinpoint the problems, but they also assist in their resolution.
Ready to secure your applications? Schedule a free consultation with QualySec now and discover how their experts can protect your business from evolving threats.
See our pricing & talk with an expert to choose the best solution for your organization.

2. Palo Alto Networks – Enterprise Security Pioneer
Palo Alto Networks is known as one of the most well-known firewalls in the field of enterprise cybersecurity, which has advanced to the next generation. They also have several customers all over the world of more than 85,000. This has led to their use by large organizations in the protection of their networks. Their Prisma Cloud and Cortex solutions provide a single security solution to hybrid environments.
Location: Santa Clara, California
3. CrowdStrike – Cloud-Native Endpoint Protection
CrowdStrike has transformed the endpoint security sector with its cloud-native Falcon platform that has 5-star ratings of service quality. Additionally, they offer real-time monitoring and response to threats. Hence, the cloud-based protection does not require complex infrastructure, and the businesses enjoy its benefits. Their threat intelligence unit keeps a watch over cyberattacks across the world using the OverWatch provided by CrowdStrike.
Location: Austin, Texas
4. Fortinet – Integrated Security Fabric Leader

Fortinet has a complete security solution with its Security Fabric strategy, which was rated 5 stars in professional quality. Also, they provide FortiGate firewalls that offer high-performance NGFW with built-in SD-WAN. Moreover, they are good at network integration and security. Therefore, distributed enterprises are opting to use Fortinet as a single point of protection.
Location: Sunnyvale, California
5. Check Point Software – Advanced Threat Prevention
The Infinity architecture offers multi-layered security solutions by Check Point to networks and clouds. Further, their threat prevention performance is at the industry level. Also, they cater to controlled sectors that need strict adherence. Thus, the government agencies and financial institutions are confident in their solutions.
Location: San Carlos, California
6. Rapid7 – Unified Vulnerability Management
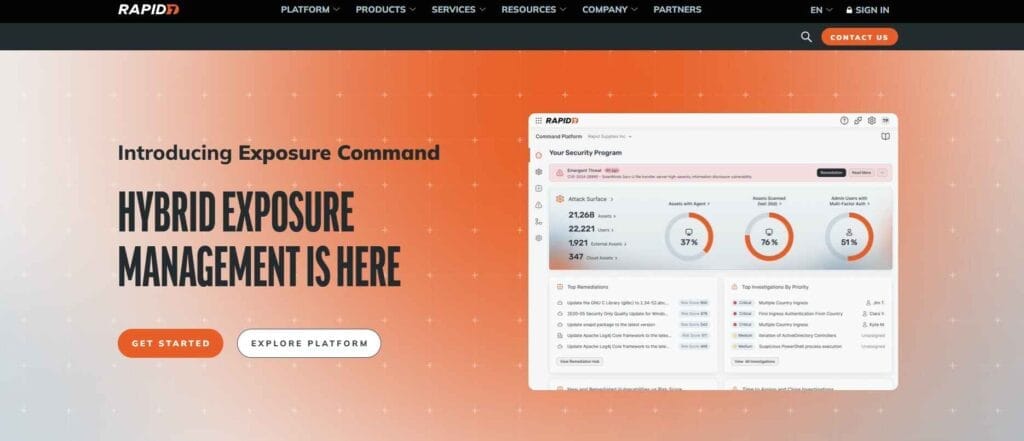
Rapid7 eases security operations by means of its cloud-native Insight Platform that integrates vulnerability management and SIEM. They also have their InsightVM, which provides risk-based vulnerability management. Moreover, the solutions of these individuals assist lean teams to cope with complex environments. Therefore, medium-sized companies like their easy-to-use philosophy.
Location: Boston, Massachusetts
7. IBM Security – Enterprise-Grade Intelligence
IBM Security has decades of experience in the contemporary world in dealing with threats, and it has become known in terms of the quality of its services. Besides, they use AI via Watson to detect threats. They also have global security services under their management. Thus, businesses are appreciating their end-to-end security expertise.
Location: Armonk, New York
8. Qualys – Cloud-Based Vulnerability Scanning
Qualys is a cloud-based vulnerability scanning and security solutions provider. It enables companies in real time to find, address, and fix vulnerabilities throughout their IT infrastructure. Moreover, they assist organizations to be regulatory compliant. As a result, firms within the controlled industry depend on their ratings.
Location: Foster City, California
9. Trend Micro – Hybrid Cloud Security

Trend Micro offers solution-based protection of hybrid environments, and the quality of services is rated at 3 stars. In addition, they are brilliant in cloud workload security. Also, their threat research team defines new risks. That is why international companies are confident in their multi-layered security strategy.
Location: Tokyo, Japan (US operations nationwide)
10. Cisco Security – Network-Centric Protection
Cisco incorporates security in its network infrastructure by using its SecureX platform, which gets 5-star ratings for the quality of services. Moreover, they use Cisco Talos threat intelligence. Moreover, their Umbrella and Duo Security products offer end-to-end protection. In turn, Cisco networks offer integrated security to organizations with such networks.
Location: San Jose, California
Want expert guidance on choosing the right security partner? Talk with QualySec’s security experts today and get personalized recommendations for your business needs.
Speak directly with Qualysec’s certified professionals to identify vulnerabilities before attackers do.
Why Should Software Security Matter More Than Ever in 2026?
The significance of optimal software security enables the rationale of protection investments. Furthermore, the threat environment is constantly developing at a high pace. Thus, now the security is more than ever a priority for businesses.
Rising Cybercrime Costs
By 2026, cyberattacks will cost the United States more than 904 billion dollars a year. Also, personal violations have meant damages of $9.48 million. Moreover, ransomware attacks saw a massive rise last year. Prevention is, therefore, cheaper as compared to recovery.
Regulatory Compliance Requirements
In addition, the governments of the world implement more stringent data protection regulations. Also, failure to comply attracts huge fines and the loss of reputation. The use of certified internet protection companies, therefore, provides regulatory compliance. Moreover, compliance proves that it is committed to the privacy of customers.
Advanced Persistent Threats
Attackers are increasingly advanced by cybercriminals, such as AI-powered attacks. Further, the supply chain weaknesses provide new entry points. Moreover, there are zero-day exploits that are produced frequently. As a result, conventional security is not adequate anymore.
Remote Work Security Challenges
The transition to working hybrid made the attack surfaces large. In addition to this, employees utilize systems across different locations and devices. Also, the use of the cloud augmented the security complexity. Hence, it is necessary to provide complete protection at the endpoints.
Business Continuity Imperatives
Lastly, security incidents destroy operations through downtime. The loss of customer trust also goes away easily once breaches are made. Also, the recovery process is costly and time-consuming, in terms of money and time. Therefore, business continuity is safeguarded by proactive security.
How Do You Choose the Right Software Security Partner?
The choice of the cyber security software companies should be carefully considered. In addition, the appropriate partner safeguards your investment and image. Thus, the following are guidelines for evaluating options.
Assess Your Specific Needs
Definitely, the first step is to define what you are trying to protect. You should also take into account the peculiarities of your industry. Moreover, assess your prevailing security position. Subsequently, this transparency aids in the reduction of inappropriate providers.
Evaluate Technical Capabilities
Then review the technology stack of every provider. In addition, make sure that they are covering your whole attack surface. Also, ensure that they are familiar with your environment (cloud, on-premise, hybrid). The point is, therefore, that reputation is not as important as technical fit.
Consider Integration Requirements
The security solutions should integrate well with the systems that are in place. Moreover, smooth integration lowers the operational friction. Also, the presence of an API makes it possible to automate. In this case, therefore, have a preference towards vendors who have well-developed integration ecosystems.
Review Pricing and ROI
Compare the costs to the possible breach costs. Besides, think in terms of long-term value in addition to initial pricing. Also, include the cost of support and maintenance. That is why, total cost of ownership gives a more advantageous comparison.
Check Customer Support Quality
Lastly, test raping times and responsiveness. Also, consultation of documentation and training materials. In addition, challenge their readiness to tailor solutions. Therefore, with high support, your investment in security is maximized.
Ready to enhance your security posture? Download QualySec’s comprehensive penetration testing report and see how professional assessments identify critical vulnerabilities before attackers do.
Get Your Free Sample Report!

Conclusion
The selection of the leading software security companies has a great influence on the resilience of your organization. In addition, the landscape is also in the process of developing as new threats arise every day. Hence, collaborating with reputable software security firms offers the necessary security. Also, companies such as QualySec are the pioneers in the industry because of their innovativeness and expertise. Moreover, they deal with the challenges of the modern world of security with a holistic approach. Therefore, spending on good security services safeguards your business, customers and image.
The right internet protection companies are not only selling products, but they also make strategic partners. Likewise, they fit solutions to your special world and objectives. In addition, they offer support in a continuous manner as threats change. Thus, you should wait and consider alternatives by our metrics and suggestions. After that, you will get a partner who is capable of providing sustainability and tranquillity.
Also Explore: Top Cybersecurity Companies in USA.
Chat with our intelligent AI Assistant and get tailored insights in seconds.

Frequently Asked Questions
1. Which are the top software security companies in the USA?
QualySec, Palo Alto Networks, CrowdStrike, Fortinet, and Check Point Software are the best Software Security Companies. Also, Rapid7, IBM Security, Qualys, Trend Micro, and Cisco Security have added to the list. These USA-based Software Security Companies provide complete security in diverse security areas.
2. What factors define a good software security company?
Good cyber security software companies are those that exhibit good market presence, technology innovation, as well as client satisfaction. In addition, they are all inclusive in terms of services, have up-to-date certificates and offer customer support. Also, established track records and clear pricing are the characteristics of the most appropriate software security providers.
3. How do I select the best one for my business?
Begin by determining your own security requirements and costs. Perform next, an assessment of technical capabilities and integration of various best software security firms. Moreover, look at reviews of customers and demand demonstrations. Lastly, internet protection companies provide tailored services to your industry and size.



















































































































































































































































































































































































































































































































































































































































































































0 Comments