Endpoint security service is an essential service in cybersecurity. It keeps all devices connected to your business network safe against cyber-related threats and malicious access. In the current digital world, where the number of cyberattacks has grown by 38% in the United States alone, the adoption of strong endpoint protection has proved important in all businesses, no matter how small or big.
An endpoint security service protects computers, mobile devices, servers, and Internet of Things (IoT) devices. Further, it connects to your corporate network. Thus, it offers total security against malware, ransomware, and data breaches. The attack surface has grown many times over, as about two out of three employees work with personal devices. It is now more important than ever to continue business continuity and safeguard sensitive data. The endpoint protection service solutions can help in this case.
What Types of Endpoints Need Protection?
Endpoint security service solutions must protect various device types that connect to your network:
- Desktop computers and laptops – Primary workstations used by employees
- Mobile devices – Smartphones and tablets accessing corporate data
- Servers – Critical infrastructure hosting business applications
- IoT devices – Smart devices connected to your network
- Virtual machines – Cloud-based computing resources
- Network printers and scanners – Often overlooked but vulnerable devices
Each endpoint represents a potential entry point for cybercriminals. Network endpoint security strategies must address all these device types to create comprehensive protection.
Get full insights on Endpoint Security.
| Endpoint Type | Risk Level | Protection Priority |
| Laptops/Desktops | High | Critical |
| Mobile Devices | Very High | Critical |
| Servers | Very High | Critical |
| IoT Devices | Medium | Important |
| Virtual Machines | High | Critical |
| Network Printers | Medium | Moderate |
Request a free demo for cybersecurity risk assessment to strengthen your endpoint security.
How Do Endpoint Security Services Work?
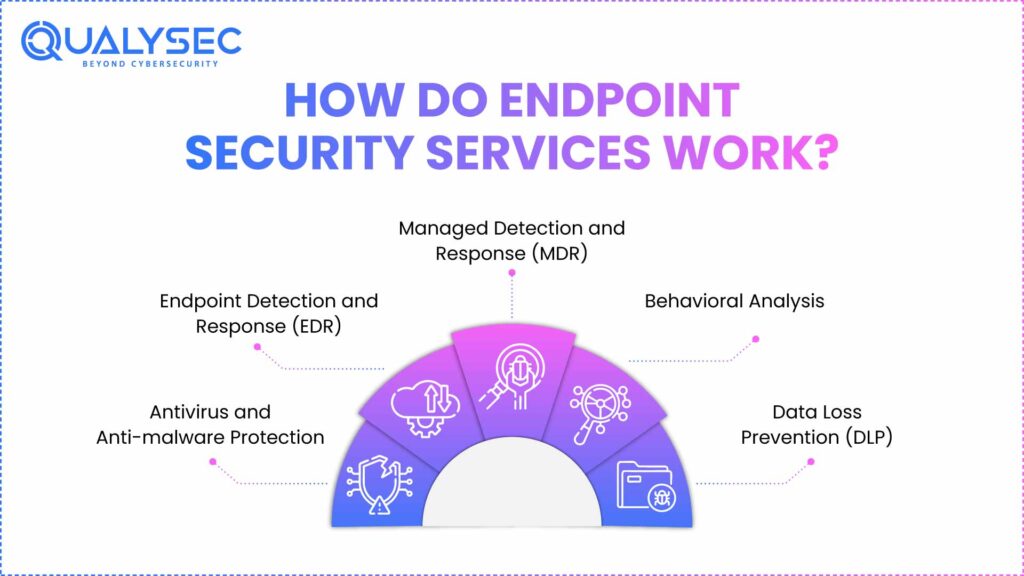
Multi-layered protection programs implemented by endpoint security vendors are multi-faceted security tools comprising multiple security technologies:
Antivirus and Anti-malware Protection
The basic endpoint protection is based on traditional antivirus software. Thus, these utilities can scan available malware signatures and suspicious file activities to avoid infection prior to the fact.
Endpoint Detection and Response (EDR)
EDR solutions offer superior threat hunting. Thereafter, they also track the actions of the endpoints in real-time and can identify advanced attacks that can circumvent the traditional antivirus systems. Further, EDR is frequently among the top endpoint security companies.
Managed Detection and Response (MDR)
MDR services are a combination of technology and human skills. Moreover, security analysts are on duty at any time of the day or night and act on threats in real time. Hence, this service is especially helpful when a company does not have the internal knowledge of cybersecurity.
Behavioral Analysis
Endpoints security services platforms today apply machine learning to detect suspicious activities that could represent a compromise. This is a proactive solution that detects zero-day attacks and advanced persistent threats.
Data Loss Prevention (DLP)
The DLP functions make sure that sensitive data does not go out of the network in an unauthorized manner. They keep a check on file transmission, email attachments, and cloud uploads so as to be in accordance with data protection rules.
Schedule a free consultation with our endpoint security experts to determine the best protection strategy for your business.
Talk to our Cybersecurity Expert to discuss your specific needs and how we can help your business.
Why Choose Qualysec as Your Endpoint Security Assessment Partner in the India?
Leading Cybersecurity Excellence Across America
Qualysec is the leading cybersecurity assessment firm in India and all across the Globe, which deals with a security evaluation of endpoints as a comprehensive security evaluation company. Moreover, Qualysec provides unparalleled security assessment through a combination of state-of-the-art technology and a vivid industry knowledge due to its headquarters being spread out in a wide location to serve businesses across the country.
Key Services Offered:
- End-to-end endpoint security evaluation with state-of-the-art tools.
- Full endpoint vulnerability and penetration testing.
- HIPAA, SOC 2, and PCI DSS compliance audits.
- Risk evaluation and risk avoidance strategies that suit your business.
- 24/7 monitored security services have a quick reaction to an incident.
Why Qualysec Stands Out:
Proven Track Record: Qualysec has been able to carry out more than 1,000 security audits on Fortune 500 corporations, health care facilities, banking, and government entities throughout India.
Industry Recognition: Certified by the most recognized cybersecurity models, such as CREST, OWASP, and NIST, assessments are done to the highest standards of the industry.
Expert Team: Our cybersecurity experts are highly qualified (CISSP, CEH, OSCP) and have decades of aggregate experience with endpoint security.
Cutting-edge Technology: Advanced scanning technology, artificial intelligence-based threat detection, and proprietary evaluation techniques are employed to detect weaknesses not found by other systems.
Comprehensive Reporting: Detailed reports consist of the executive summaries, technical findings, risk ratings, and remediation steps to be taken with timelines.
Location Advantage: Qualysec has its offices in the biggest cities of the India and is able to work remotely allowing offering personalized service at a reasonable price.
Client-Centric Approach: Tailored assessments based on your specific industry, compliance requirements, and business objectives.
The assessment of the endpoint protection service offered by Qualysec has assisted clients in minimizing security incidences by an average of 85% in six months of the service. The proactive model helps to detect the main vulnerabilities and prevent them before they become the subject of cybercriminals.
Download our sample endpoint security assessment report to see how we can strengthen your security posture.
What Are the Key Benefits of Managed Endpoint Security Services?
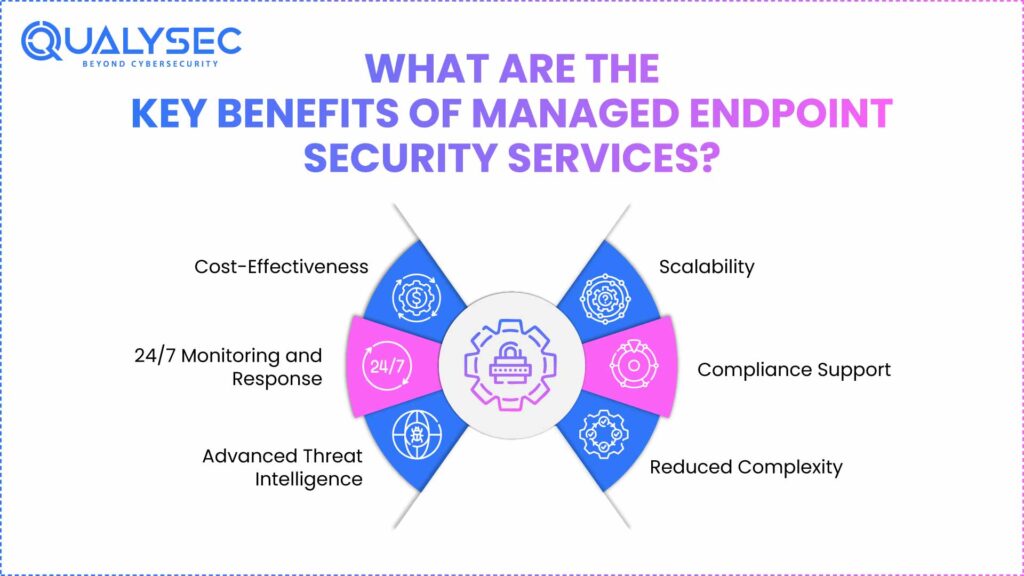
The endpoint protection service solutions have many benefits compared to conventional in-house security management:
Cost-Effectiveness
The managed services do not require costly security infrastructure and expertise. It is expected that businesses will save 40-60% as compared to the development of internal capabilities.
Make the right choice with our Endpoint Protection Cost guide.
24/7 Monitoring and Response
The endpoint security firms offer 24/7 monitoring, which makes sure that threats are detected and counteracted instantly, even when the business is closed.
Advanced Threat Intelligence
When it comes to endpoints, managed service providers can access the global threat intelligence networks and ensure they remain safe against the newer threat vectors.
Scalability
You can expand your business without the need to invest big in infrastructure because managed endpoint security services can be expanded without much hassle.
Compliance Support
Most managed services come with compliance reporting and compliance with laws such as GDPR, HIPAA, and PCI DSS. Read more on data security compliance.
Reduced Complexity
One dashboard allows easier security management and a shorter learning curve on the part of your IT team.
Talk with our experts about customising a managed endpoint security solution for your specific needs.
Latest Penetration Testing Report

Conclusion
The solution of endpoint security services is needed in defending contemporary businesses against the more advanced cyber threats. Cyberattacks cost India businesses an average of ₹220 million per attack, so investing in a holistic endpoint protection is not merely recommended, but a matter of life and death.
To achieve effective endpoint network security is necessary to use a multi-layered system with a combination of conventional antivirus, high-quality EDR, behavioral analysis, and professional monitoring service. The collaboration with the qualified endpoint security firms, such as Qualysec, enables the companies to deploy solid security and concentrate on their operations.
The threat landscape in the cyber world is constantly changing, and it is necessary to select providers of endpoint protection services that will keep abreast of the latest threats by constantly innovating and employing expert opinions.
If you have any questions, please feel free to reach out — our experts will assist you in making the right decision for your next project.
FAQ
1. What is an endpoint security service?
An endpoint security service is a full-scale cybersecurity service that safeguards all devices that are linked to your business network against malware, ransomware, and unauthorized access. These are services that integrate various security technologies such as antivirus, EDR, and managed monitoring to give full endpoint security.
2. Why do businesses need endpoint security services?
All kinds of businesses need these endpoint security services since the number of attacks aimed at endpoints has grown significantly, and more than 68 percent of organizations experienced endpoint attacks in 2024. The solutions of endpoint protection services eliminate data breaches, ensure compliance, and provide business continuity protection by securing all network-connected devices.
3. What is an example of an endpoint service?
Managed antivirus protection, EDR monitoring, and mobile device management (MDM) solutions are common examples of endpoint security services. Endpoint protection service platforms combine multiple security technologies to secure devices across the organization. Leading endpoint security vendors offering these services include CrowdStrike, Microsoft Defender, and Carbon Black.
4. What are the three main types of endpoint security?
The three primary categories of endpoint protection are signature-based detection, which detects known malware codes, and behavioral analysis. Further, it tracks suspicious activity on the devices and cloud-based endpoint security service providers that offer real-time threat intelligence. The current network endpoint security practices integrate these methods to provide holistic protection against known and unidentified threats.
5. Which tool is commonly used for endpoint security?
Some of the popular endpoint security service platforms are Microsoft Defender for Enterprise, CrowdStrike Falcon Complete, and Symantec Endpoint Protection provide a complete endpoint protection service platform. The top endpoint security vendors are offering integrated platforms. It combines antivirus, EDR, and managed services to make it easy to manage the endpoint protection service within any kind of business.
6. What are the benefits of using a managed endpoint security service?
The advantages of a managed endpoint protection service are round-the-clock surveillance and response, lower costs than in-house solutions, access to advanced threat intelligence, scalability when business grows, compliance, and easy security management. End-point security managed services providers usually decrease security breaches by 70-85%.























































































































































































































































































































































































































































































































































































































0 Comments