The world is filled with smart devices and systems and therefore buzzing with smart devices and systems data. As we continue to maximize the number of devices that can connect, we are also expanding the opportunities hackers have to enter the IoT/IIoT ecosystem without proper IOT Security Assessment. Organizations and homes have a great deal of vulnerability if devices are not secured.
Experts project that the global IoT security assessment will experience tremendous growth by 2025, which highlights how much protection will be needed. In one country alone, the U.S., the market is projected to increase from just under 9 million in 2024 to over 100 million globally by early 2030. Companies must look at their IoT security strategy, as it matters now more than ever.
Understanding IOT Security Assessment
An IoT security assessment focuses on identifying weaknesses in connected devices before they’re discovered by attackers. It examines devices, firmware, networks, and data paths searching for vulnerabilities.
Heightened complexity over traditional IoT security assessments comes from device hardware limits, the use of embedded systems, and communication between devices. Any sensor, smart meter, or camera can be a hacker’s entry point if sufficient testing doesn’t occur.
Your 5-Step Plan for Safer Connected Devices
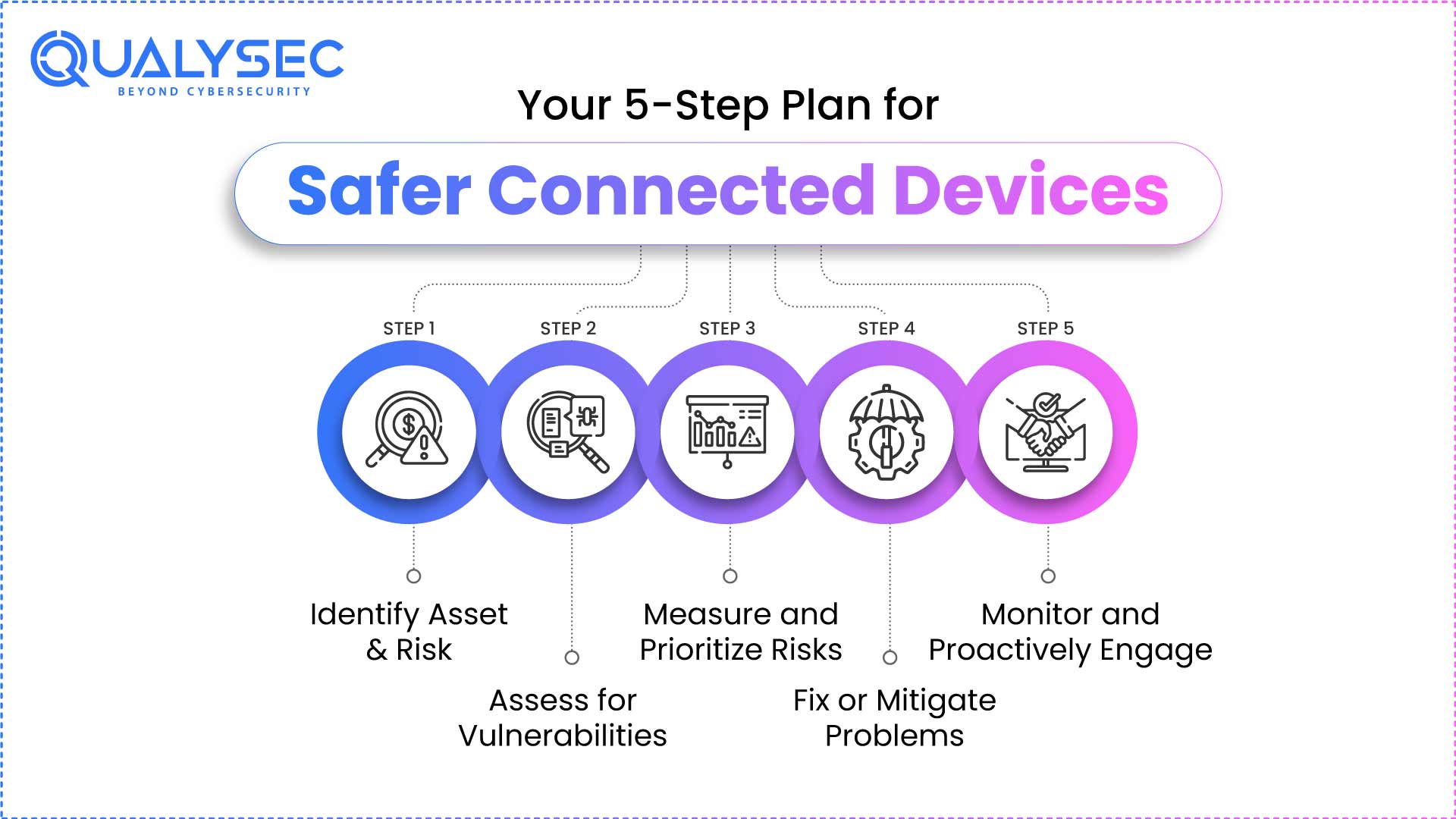
By using clearly defined, repeatable steps, you can stay a step ahead of ever-evolving threats. Here is how:
Secure Your IoT Devices Today – Partner with Qualysec
Step 1: Identify Asset & Risk
The first step in an IoT Security Audit is to develop a comprehensive asset inventory of every IoT device that is connected to your network, from smart sensors to industrial controllers. Categorize assets by type of device, the data it collects, and the potential harm if compromised.
This also means locating “shadow IoT” devices that employees may have connected without going through IT. In this step, you should also document threats such as outdated firmware, weak authentication, unencrypted communications, etc. Having a complete picture of assets is the fundamental first step for all subsequent steps.
Step 2: Assess for Vulnerabilities
Once you know what devices you have on your network, you’ll want to identify the real security of each device. This means performing vulnerability scans to identify any (known or unknown) vulnerabilities, performing penetration tests that approximate how a real attack might occur through that device, and looking at general areas of concern such as encryption strength, firmware integrity, open ports, and insecure APIs.
Remember that for resource-constrained devices (devices that cannot operate many heavy security tools), you may need techniques for testing. Your goal is to find obvious and hidden vulnerabilities.
Step 3: Measure and Prioritize Risks
Some problems are worse than others. When your team is finished testing, you should look at each problem and assess the potential harm caused and how frequently you would expect it to occur. It may be most beneficial to prioritize issues that affect devices that are crucial to daily work or those that serve important control functions. With this prioritization, your team can address the least arguably harmful problems last, rather than treating all problems equally.
Step 4: Fix or Mitigate Problems
Once you have assessed risk, you should take action quickly on the prioritized risks. This may seem obvious, but it could mean updating devices, changing weak settings, or utilizing stronger logins and passwords. You can also separate IoT devices from your critical business systems to lessen the consequences of potential damage. In some cases, best practices would dictate that the safest option is simply to remove unsupported or old devices altogether.
Step 5: Monitor and Proactively Engage
IoT device security is not a one-time event, and it should not be thought of in this way. New risks can arise, new devices may be added, and updates can introduce new issues. Use tools to monitor for anomalous activity. Review your perennial safeguards at least annually or at the time of any significant device introductions or software updates. Regular review will pave the way for identifying risks and potentially remediating them before there is a serious risk to your business.
Best Practices for Ongoing IoT Security
Keeping IoT devices safe is a continuous effort, not a project with a single endpoint. Always begin with securely onboarding devices, with secure authentication and encryption for every new device before it goes online. Utilize encrypted communication protocols for any data in transit and segment IoT devices from the main business networks.
Plan for device retirement, as outdated devices are often easy targets for hackers. Follow a zero-trust security framework, requiring any device to continuously prove its identity before accessing any resource. Finally, ensure your device users are trained on the risks associated with IoT device use so they don’t unintentionally put you on the front page.
Latest Penetration Testing Report

How Qualysec Can Help?
Qualysec supports companies aiming to make their IoT devices safer, which regularly assess devices through tactile methods and tools. Qualysec offers assessment methods that identify issues that others might not. Once they identify an issue, they coach your team to fix it, re-test it for free to ensure it is resolved, and assist you in complying with critical security guidelines/standards.
Whether they are evaluating the security of a smart home device or equipment on the factory floor, Qualysec will develop and implement a tailored plan that enables you to make deliberate decisions that keep you secure from evolving threats.
Don’t Wait for a Breach – Connect with a Trusted IoT Security Company
Conclusion
The Internet of Things (IoT) has permeated our lives, with the associated risks lurking. A systematic IoT security assessment will assist you and your organization in confronting and accommodating those risks before they convert to real-world threats.
With an established playbook – identifying all of your assets, testing them against various internal and external threats, remediating all security concerns – you can confront cyber threats proactively.
It is important to have strong repeatable processes for risk assessment, and follow up on new devices, as well as having professionals available to support IoT protections in your environment, such as Qualysec consultants.
Let Qualysec Help You Eliminate IoT security Risks Fast
Talk to our Cybersecurity Expert to discuss your specific needs and how we can help your business.
FAQ’s
1. What is an IoT security assessment, and why is it important?
An IoT security assessment examines devices, firmware, networks, and APIs for vulnerabilities. This is important work because IoT devices are a preferred attack surface for adversaries—and it’s just impossible to secure something you don’t know is vulnerable.
2. How is an IoT risk assessment different than a security assessment?
An IoT risk assessment encompasses a broader view—the impact, the likelihood, and the business risk. An IoT security assessment focuses on the technical side to find and test specific vulnerabilities. Both a risk assessment and a security assessment have distinct roles, but are necessary.
3. What vulnerabilities do IoT devices commonly exhibit?
Common shortcomings in IoT devices include weak or compromised authentication, unpatched or obsolete firmware, weak encryption, unprotected network access, and vulnerable APIs, particularly in devices with limited hardware capabilities.
4. How often should organizations perform IoT security assessments?
Once a year is the ideal frequency for assessments, although they should be performed every time a new device is installed or if device firmware is modified significantly. Using some form of continuous monitoring and threat detection helps organizations account for issues independently of full assessment events.
5. What standards or regulations govern IoT cybersecurity?
Some important standards are EN 17927 (SESIP), or the standard evaluation criteria for the secure evaluation of IoT platforms. Other references are recorded in ISO/IEC 15408 (or Common Criteria), IEC 62443, and the European Union Cyber Resilience Act. NIST also has guidelines, in addition to its subject-specific regulations (e.g., Medical Devices), focused on cybersecurity requirements.























































































































































































































































































































































































































































































































































































































0 Comments