From global banks to fast-scaling SaaS startups, Microsoft Azure powers a majority of today’s digital infrastructure. With powerful services like Azure Virtual Machines, Cosmos DB, and Azure security services, the platform offers speed, scale, and global reach like never before.
Most organizations assume that turning on Azure’s built-in security features is enough. But misconfigured policies, excessive access rights, and blind spots in infrastructure design are some common causes of cloud breaches.
That’s where Azure security services come in. It is critical to ensure that you choose partners who independently validate, test, and harden your Azure security environment against real-world threats through Azure Penetration Testing.
In this guide, we will talk in detail about how Azure security services can help protect your cloud infrastructure.
Key Features of Azure Cloud Platform
Before diving into security, it’s important to understand what makes Azure such a dominant platform. The answer? The diverse range of features it has.
Here are the features that set Azure apart:
1. Global Availability Zones & Redundancy
Azure offers data center redundancy across 60+ regions worldwide. That gives organizations more control over data safety and disaster recovery.
2. Integrated Identity & Access Management (IAM)
Azure Active Directory (AAD) offers secure access control across users, apps, and infrastructure. However, one needs to be careful about improper configurations, as that can lead to overexposure.
3. Advanced Networking Capabilities
Azure Virtual Networks, NSGs (Network Security Groups), and Azure Firewall give teams deep control. However, these must be continually configured and reviewed to prevent exposure via Azure network security.
Latest Penetration Testing Report

Why Is Azure Cloud Security Important?
Imagine – you have migrated to Azure for scalability, performance, and innovation. However, with every service you sign up for, you also expose yourself to more attack surfaces. The more powerful your infrastructure, the more damage a single misstep can cause.
In the past years, Microsoft has disclosed more than 1200 attacks per second on its cloud platforms. There are no more theoretical risks. From improperly exposed storage buckets to unsecured identities, misconfigurations have become the cloud’s primary concern area.
Some consequences include:
- Breaches due to excessive permissions in Azure AD configurations
- Ransomware delivery via unmonitored virtual machines
- Data exfiltration through poorly defined NSGs or unmanaged APIs
- Audit failures during SOC 2 or HIPAA reviews due to missing controls or weak remediation documentation
While it’s true that Azure has default security tools, they are only configured to catch what they can see. Azure cloud security services are unable to identify logic flaws, manual escalation vectors, and custom vulnerabilities.
That’s why Azure cloud security is no longer optional. It’s foundational, especially if your business handles sensitive customer data or financial transactions.
Explore our blog on Cloud Security Services for Azure!
Overview of Azure Security Services
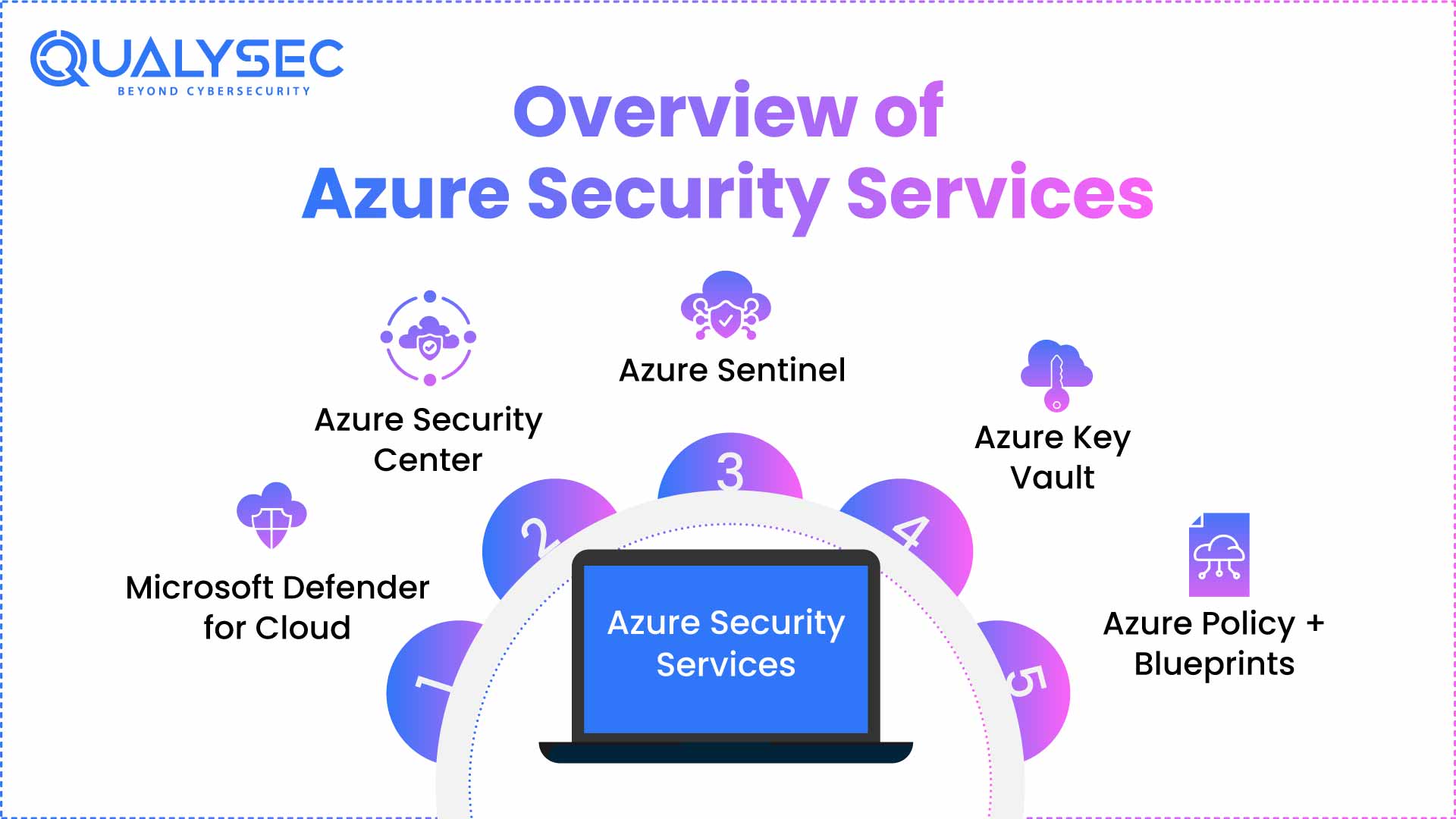
Microsoft offers a powerful suite of security tools built into Azure. The challenge is knowing how, when, and why to use them effectively.
Let’s take a look at the various Azure security services:
1. Microsoft Defender for Cloud
- A unified security management system for workloads across Azure, hybrid, and multi-cloud environments.
- Offers Secure Score to highlight weaknesses in your configuration.
- Provides threat detection using built-in analytics—but it’s only as accurate as your logging setup.
2. Azure Security Center
- Centralized visibility into your cloud security posture.
- Flags misconfigurations across compute, networking, and identity layers.
- Also integrates with Defender for automatic threat mitigation, but it won’t cover deeper logic flaws or overlooked edge cases.
3. Azure Sentinel
- Microsoft’s cloud-native SIEM (Security Information and Event Management) tool.
Collects logs across platforms, correlates them with threat intelligence, and surfaces alerts. - Sentinel helps you detect and investigate attacks, but real-time response requires well-trained teams and refined automation rules.
4. Azure Key Vault
- Secures keys, secrets, and certificates.
- Prevents hardcoding secrets into apps or scripts.
- Best used with strict RBAC and logging, but often misconfigured in fast-moving DevOps environments.
5. Azure Policy + Blueprints
- Ensures cloud governance and policy enforcement.
- Prevents deployments that violate predefined compliance or security rules.
- These tools maintain order—but don’t retroactively fix gaps that already exist.
Your Complete Azure Security Checklist
Securing Azure is not about using every feature. It’s more about implementing the right controls in the correct order and verifying that they actually work.
Here is a comprehensive Microsoft Azure security checklist –
Multi-Factor Authentication (MFA): Make MFA compulsory for all privileged accounts. Provide conditional access policies to all tenants.
Back Up Important Data: Regularly test the backup data to ensure there is no ransomware or accidental data loss.
Focus on Role-Based Access Control: Regularly audit all user roles, service accounts, and API permissions.
Encryption Is Important: Opt for encryption of all data using Azure Key Vault and managed keys.
Mapping Azure Security to U.S. Compliance Frameworks
Most businesses using Azure operate under one or more compliance requirements.
At Qualysec, we ensure your cloud infrastructure is in accordance with U.S. compliance frameworks, backed by an exceptional Azure security audit.
- SOC 2 (Type I & II): Controls like access logging, data classification, and change monitoring must be proven. Only enabling them is not enough. We produce pentest evidence and remediation summaries mapped to Trust Services Criteria.
- HIPAA: Covered entities must ensure that PHI is encrypted, auditable, and access-controlled. This is especially applicable for Azure Blob Storage and databases. Our reports validate whether actual security practices align with administrative safeguards.
- ISO 27001: Requires organizations to identify risks and implement controls. Our Azure security assessments map directly to ISO control objectives.
- NIST CSF: The framework demands visibility into Identify, Protect, Detect, Respond, and Recover functions. Our pentest reports explicitly align with these functions.
Future of Azure Security
Without a doubt, Azure will continue to lead the cloud landscape. However, organizations must be careful to update and ensure proactive, real-world security.
It is important to understand that what makes your business successful on Azure is exactly what makes it vulnerable too. That’s why Azure security services are so important.
Secure your Azure infrastructure with Qualysec today!
Conclusion
Securing Azure is no longer a choice. It’s critical to maintain business security and achieve Azure cloud compliance.
From network configurations and identity governance to encryption and compliance alignment, Microsoft Azure provides the tools. But Azure Security Services alone don’t create a secure environment. You need to know how to configure, validate, and monitor these tools to ensure your cloud is as secure as it can be.
That cannot be done just by ticking off checkboxes. It requires expert validation, manual inspection, and strategic guidance. And Qualysec is ready to provide all these with exceptional services and customer satisfaction.
Book your Azure cloud security assessment with Qualysec today.
Talk to our Cybersecurity Expert to discuss your specific needs and how we can help your business.
FAQs:
Q. What are the four types of Azure services?
Azure offers four primary service categories:
- Infrastructure as a Service (IaaS)
- Platform as a Service (PaaS)
- Software as a Service (SaaS)
- Serverless
Q. Why should businesses use Azure Security Services?
Businesses should use Azure Security Services because they help:
- Detect and prevent threats in real-time
- Monitor misconfigurations
- Protect sensitive data and access
- Establish compliance with SOC 2, HIPAA, and other frameworks
Q. What are the most common security threats addressed by Azure Security Services?
The most common security threats addressed by Azure Security Services include misconfigured identity and access permissions, exposed storage, unmonitored API endpoints, no encryption, unpatched workloads, etc.

























































































































































































































































































































































































































































































































































































































0 Comments