The financial landscape in India is experiencing a digital overhaul. Keeping this in mind, Cybersecurity in Banking, NBFCs, and FinTech has now become a priority in the country. To protect customers’ information and digital services in this scenario, the Reserve Bank of India has developed a set of guidelines related to cybersecurity issues, commonly referred to as RBI certification.
Although the RBI does not issue a certificate, regulated organizations are required to demonstrate their complete compliance with the RBI Cyber Security Framework and the Cyber Security Guidelines issued by the RBI, based on audits, reporting, and third-party security validation.
Below is an in-depth explanation of what an RBI certification entails, who needs an RBI certification, how one can be achieved, and the importance of having an RBI certification in Cybersecurity for Financial Services, including Cybersecurity in FinTech.
Understanding RBI Certification in Cybersecurity
The RBI certification is widely discussed as a means of referring to adherence to the cybersecurity regulations issued by the RBI. It implies the capabilities of an organization in complying with the prescribed controls, frameworks, and audits by the RBI.
Circulars addressed to banks, NBFCs, payment aggregators, and FinTech entities:
- The RBI Cybersecurity Framework
- Periodic audits, including RBI VAPT Services
- Supervisory inspections and compliance reporting
In place of distributing a downloadable certificate, RBI bases its evaluation of cybersecurity maturity in terms of compliance and risk assessments.
Why RBI Cybersecurity Compliance Is Critical
Let’s understand the reasons why RBI cybersecurity compliance is critical:
1. Rising Cyber Threats in Financial Services
Banks and FinTech firms are vulnerable to threats such as ransomware, phishing, API misuse, and data breaches. Banks can face financial fraud.
2. Regulatory Enforcement
Failure to comply with RBI cybersecurity guidelines can result in:
- Cyber
- Heavy penalties
- Operational
- Loss of Licences in severe cases
3. Customer Trust and Market Credibility
Having effective cybersecurity and RBI compliance enables building trust with customers.
Who Needs RBI Cybersecurity Certification?
All entities regulated by the RBI are to follow RBI Cybersecurity Compliance. The entities include:
- Scheduled Commercial Banks
- Coop banks
- Non-Banking Financial Companies (Payment banks and small finance banks)
- Payment aggregators and payment gateways
- Companies offering financial services that are regulated
- Digital lending platforms
Although Cybersecurity in Fintech is expanding rapidly, the RBI has also enlarged its regulatory coverage to technology-driven financial platforms.
Learn more on: RBI Payment Aggregator Pentesting
RBI Cybersecurity Framework: An Overview
Cyber Security Framework by RBI is a holistic regulatory model developed for improving the overall cyber resilience of banking, NBFC, and other regulated entities within the Indian sector. Although it takes alignment from globally recognized models like ISO 27001, NIST, and PCI DSS Compliance, the Cyber Security Framework is tailored to meet the Indian requirements and risks associated with digital payments and banking.
Cyber Security Framework by RBI has a particular emphasis on good governance, with a focus on continuous risk assessment and proper implementation of security controls. Cyber Security Framework by RBI also promotes continuous monitoring by the Security Operations Center (SOC), proper response mechanisms for incidents, and periodic internal and external audit processes. The RBI VAPT service mandate is also a part of this Cyber Security Framework.
Step-by-Step Process to Get RBI Cybersecurity Compliance
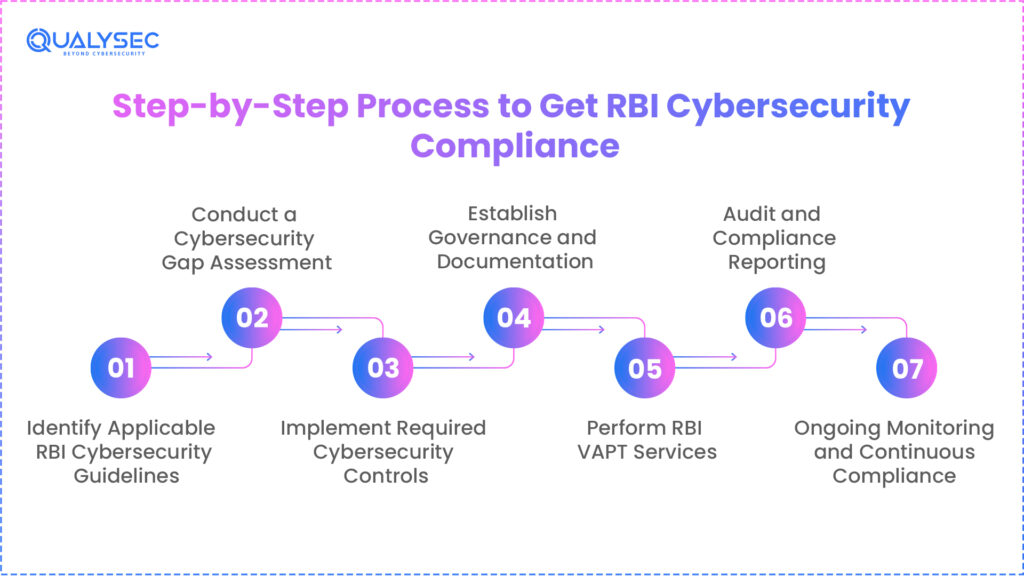
The following steps outline the essential lifecycle for financial institutions (Banks, NBFCs, and Fintechs) to meet the RBI’s baseline security requirements:
Step 1: Identify Applicable RBI Cybersecurity Guidelines
The RBI-regulated organizations fall under the scope of certain cybersecurity guidelines depending upon their risk category. The banks, Non-Banking Financial Companies, as well as FinTech firms, must identify the appropriate guidelines regarding IT governance, data security, and cybersecurity management. The correct identification of the RBI cybersecurity guidelines helps ensure the accuracy of the compliance process.
Step 2: Conduct a Cybersecurity Gap Assessment
A gap assessment is a process used to identify how current cybersecurity policies, systems, and processes align with RBI guidelines. A gap assessment includes a check on the overall governance structure, the current state of the technical infrastructure, access controls, and overall readiness for incidents. In “Cybersecurity for Financial Services,” this is one of the processes that helps in understanding gaps in compliance.
Step 3: Implement Required Cybersecurity Controls
A combination of technical and operational controls has to be applied based on gaps identified. Some of these controls include firewalls, intrusion detection systems, multi-factor authentication systems, secure APIs, and data encryption.
Better implementation of these measures has paramount importance in Cybersecurity in Banking and Cybersecurity in Fintech since high security is required in view of the transaction requirements in these sectors, which are processed in real time.
Step 4: Establish Governance and Documentation
RBI mandates strong cybersecurity governance supported by formal documentation. In this light, policies such as cybersecurity, IT risk management, incident response, and data protection must be approved and maintained. Clear documentation shows accountability, maturity, and regulatory seriousness.
Step 5: Perform RBI VAPT Services
RBI-mandated VAPT services are one of the necessities in order to identify vulnerabilities and test real-world attack scenarios. Similarly, the purposes of the vulnerability assessment and penetration test include confirming the efficiency of security controls already deployed. RBI will require timely remediation and proper reporting of the identified risks.
Step 6: Audit and Compliance Reporting
Organizations need to conduct audits and compile evidence on compliance after implementing controls and conducting VAPT. Audit reports document adherence to guidelines provided by RBI and track findings for remediation. This may be reviewed during the RBI inspection or supervisory assessments.
Step 7: Ongoing Monitoring and Continuous Compliance
Cybersecurity compliance in the RBI is an ongoing process and not an implementation-at-once process. There should be periodic audits, development of new controls based on new threats, as well as training of employees on the same. Ongoing Monitoring encompasses long-term Cybersecurity for Financial Services.
RBI Cybersecurity Compliance for FinTech Companies
FinTech companies lie at the intersection of finance and technology, thus highly vulnerable to cyber threats and regulatory concerns. They deal with digital payment systems, open banking APIs, real-time integrations, and handling a massive amount of sensitive data. Given this high risk, Cybersecurity in FinTech is a highly prominent area of concern for the RBI as a regulatory body.
FinTechs must adopt secure API architecture, data localization, and third-party risk management to mitigate supply-chain risks. Vulnerability Analysis and Penetration Testing, as well as security testing, assume paramount importance in scanning for vulnerable points in applications. Several FinTech Cyber Security organizations also assist new and developing Fintechs with rapid, organized, and compliant implementation of RBI cybersecurity norms.
Common Challenges in Achieving RBI Cybersecurity Compliance
Achieving cyber security RBI compliance in 2026 requires modernizing legacy systems to support zero trust architecture. Below are the common challenges in achieving the RBI cybersecurity compliance:
1. Lack of internal cybersecurity expertise
A lot of banks, NBFCs, and FinTech companies do not have in-house teams with deep regulatory cybersecurity knowledge. As a result, misinterpretation of the RBI guideline remains very common, and compliance efforts are either incomplete or delayed.
2. Legacy systems in banks and NBFCs
Legacy IT infrastructure does not have built-in security controls, and integration with modern monitoring tools also remains quite challenging. These legacy environments increase vulnerability exposure, along with complicating compliance with evolving RBI cybersecurity requirements.
3. Rapid scaling in FinTech environments
Fast-growing FinTech platforms tend to put speed ahead of innovation, often at the expense of security controls. The rapid development of new technologies leaves security holes in APIs, cloud infrastructure security, and third-party integrations.
4. Insufficient documentation
There is a strong emphasis by RBI on documented policies, procedures, and governance frameworks. Absence of documentation or absence of updated documentation leads to compliance failures even where technical controls have partial implementation.
5. Delayed vulnerability remediation
Operational compulsions may cause identified security flaws not to get fixed within acceptable timelines. These delays increase the threat of cybercrime and also lead to red flags during RBI audits and inspections.
This is designed to help organizations address these gaps through structured compliance programs and expert guidance by partnering with experienced FinTech cybersecurity companies.
Role of Third-Party Cybersecurity Firms
Third-party cybersecurity firms act as critical force multipliers, providing the specialized expertise and 24/7 monitoring capabilities that internal teams often struggle to maintain alone. Let’s understand the role of third-party cybersecurity firms:
1. RBI compliance gap analysis
Cyber security service providers analyze the existing security controls of the business against RBI guidelines. This enables organizations to know their compliance requirements and take necessary steps accordingly. Additionally, cybersecurity services enable banks to assess their internal security controls against the RBI.
2. Policy drafting and governance setup
Specialists are also involved in developing RBI-compliant cybersecurity policies, risk, and overall governance structures. Poor documentation can undermine board-level committee effectiveness and regulatory trust.
3. RBI VAPT services
External companies carry out vulnerability analysis and penetration testing in order to identify real-world Security Weaknesses. Such testing is used to evaluate the efficiency of Security Controls and satisfies RBI audit requirements.
4. Audit preparation and remediation
Cybersecurity companies help firms with auditing processes through evidence preparation and remediation of reported vulnerabilities. This speeds up the entire process of regulatory approvals.
For more complicated information technology environments, third-party knowledge helps achieve faster, correct, and effective RBI cybersecurity compliance.
Benefits of RBI Cybersecurity Compliance
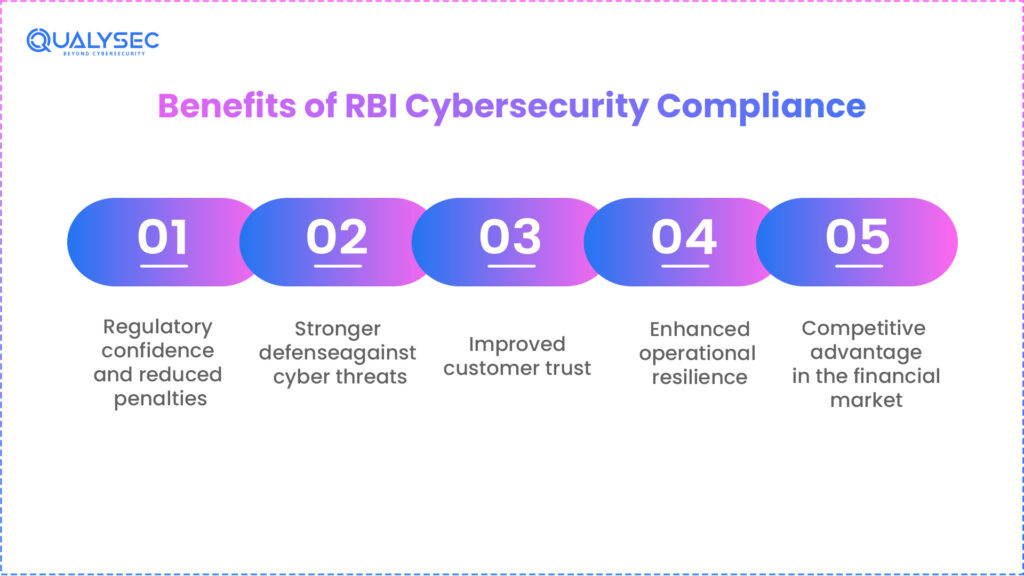
Beyond mitigating risks, adhering to the RBI’s stringent guidelines serves as a powerful catalyst for operational excellence and long-term institutional stability. By understanding the benefits of RBI cybersecurity compliance, financial entities can transform a regulatory obligation into a strategic advantage that fosters deep-rooted trust in an increasingly digital economy.
1. Regulatory confidence and reduced penalties
A consistent level of compliance translates to effective risk management to the satisfaction of the authorities, thereby minimizing threats of penalties and enforcement.
2. Stronger defense against cyber threats
RBI-compliant security controls enhance protective measures against malware, ransomware, breaches of data, and fraud.
3. Improved customer trust
Customers feel more secure in their financial and personal information if it is safeguarded by the institutions they deal with. Good compliance practices boost the credibility of the brand and customer loyalty.
4. Enhanced operational resilience
Effective incident response and monitoring tools reduce downtime during cyber events. This results in uninterrupted core financial services even during an attack.
5. Competitive advantage in the financial market
Enterprises with good cybersecurity and RBI compliance have an easier time with mergers and acquisitions, as well as entering into other partnerships or ventures.
Conclusion
While RBI itself does not provide a specific certificate, demonstrating compliance with the RBI Cybersecurity Framework and RBI cybersecurity guidelines is no longer a choice but a compulsion for banks, NBFCs, and FinTech companies for regulatory approvals, continuity of operations, and customer trust.
Cybersecurity compliance with the RBI can be attained and continuously maintained through structured governance, strong technical controls, regular audits, and RBI VAPT services. Considering that cyber threats keep evolving, proactive investment in Cybersecurity for financial services remains one of the most critical strategic priorities for the financial ecosystem in India.
FAQ
1. What is RBI certification in cybersecurity?
In the case of RBI certification in the field of cybersecurity, it deals with compliance with the RBI guidelines and regulations related to cybersecurity audits and guidelines.
2. Is RBI certification mandatory for banks and NBFCs?
Yes, it is mandatory to follow the RBI guidelines regarding cybersecurity for banks as well as the NBFCs operating under the RBI framework.
3. Does RBI issue an official cybersecurity certificate?
There is no issuance of an official certificate by the RBI. There is an evaluation based on audit, inspection, and reporting.
4. What are the key RBI cybersecurity guidelines organizations must follow?
Some of these major guidelines include: Governance Controls, Risk Assessments, Security Monitoring, Incident Management, Audits, and Mandatory VAPT as per RBI Cyber Security Framework.
5. Who needs RBI cybersecurity compliance certification?
RBI-regulated entities, such as banks, NBFCs, payment systems operators, and regulated FinTech companies, must be RBI cybersecurity compliance-ready.
6. What is the role of VAPT in RBI certification?
The RBI VAPT services assist in the identification of vulnerabilities, testing the security controls, and proving technical compliance for the RBI cybersecurity expectations.

























































































































































































































































































































































































































































































































































































































0 Comments