The growing incidence of digital transformation in companies has led to widespread cloud adoption worldwide. Many businesses are adopting a hybrid cloud security solutions approach, which combines private and public cloud solutions to maximize the benefits of both, while also presenting specific security challenges.
Businesses must be aware of the threats and adhere to best practices for managing hybrid cloud network security. The blog provides best practices and examines the security issues encountered in hybrid cloud environments.
What Is Hybrid Cloud Security?
Hybrid cloud security solutions refers to the set of methods and tools designed to safeguard data and infrastructure that integrate aspects of private cloud, public cloud, and on-premises infrastructure into a unified architecture. The IT setting combining these components is a hybrid cloud.
By utilizing more features available in those settings, the hybrid cloud offers significant flexibility in rapidly transferring workloads to various environments. Although there are compelling reasons to use a hybrid cloud system, it introduces additional security issues that can be addressed. Let’s first consider hybrid cloud network security challenges in applications.
Hybrid Cloud Security Challenges In the Philippines
Running a hybrid cloud model has several disadvantages, as it has a wider threat surface. Managing the compliance posture, implementing security policies for every storage, establishing role-based access control, and mitigating a wide range of cyber threats are some key hybrid cloud security challenges. Let’s discuss them in detail.
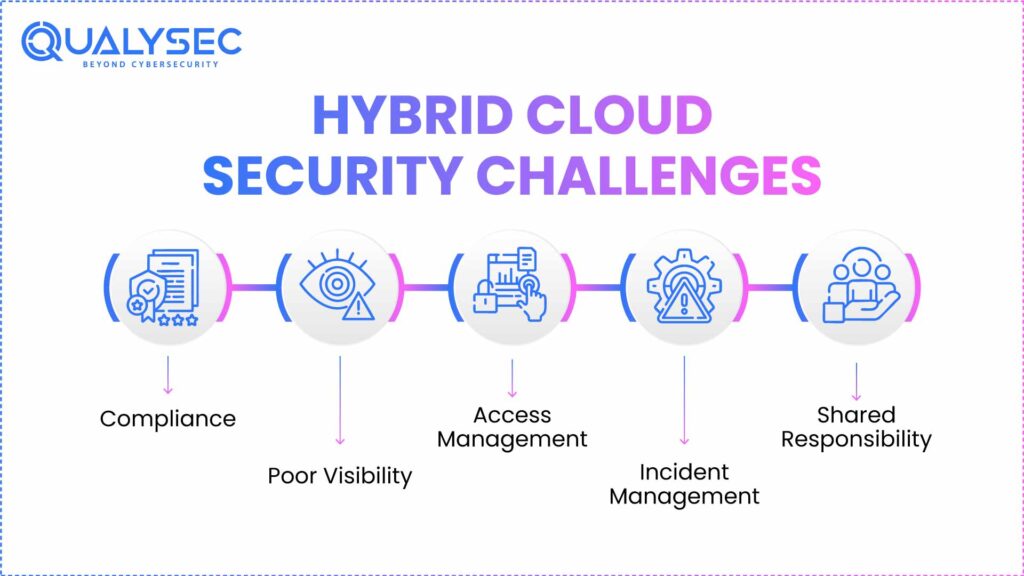
1. Compliance
Due to the separate systems and processes, a hybrid cloud environment provides greater control. Particularly for heavily regulated sectors such as financial services, healthcare, and government, a distributed environment presents new difficulties and complexity. Meeting other regulatory requirements, such as HIPAA, GDPR, and NIST, complicates the already complex hybrid architecture by adding more checklists and complexity.
Explore more: Cloud Security Compliance: 2025 Standards & Best Practices
2. Poor visibility
Real-time visibility is essential for managing all the moving parts of a hybrid cloud installation, particularly to meet the requirements of mandated regulatory systems. Gaps that could lead to a security event can easily be overlooked without a dedicated and centralized management dashboard.
3. Access management
Because of its distributed feature, access control gets more complex compared to an on-premises environment. This is the case when multiple cloud systems with different roles, each with its own access requirements, are involved. To circumvent this, your team has to determine the permutation combination for every use scenario.
4. Incident management
Investigating an event is one of the drawbacks of a distributed setting. Tracking the cyber threat chain can be difficult when you have many systems. Considering the variations in each system, troubleshooting and isolating the event takes longer. Coordinating the reaction across multiple settings is challenging, even after it has been recognized.
5. Shared responsibility
Expect less complexity in a situation with shared responsibility than in one where a single team or person is responsible for managing the cloud architecture’s compliance, security, risks, and operations.
In circumstances where there are many clouds with a team assigned to each, it is crucial to properly divide the responsibility, needs, and expectations for all stakeholders, internal departments, and consumers as well. Everybody engaged should know their duties thoroughly.
Discover hidden gaps in your cloud security before hackers exploit them- Request your cloud gap analysis today.
Qualysec’s cloud pentest gives you results—no endless emails, no digging through PDFs, no guesswork.

Security Best Practices for Hybrid Cloud
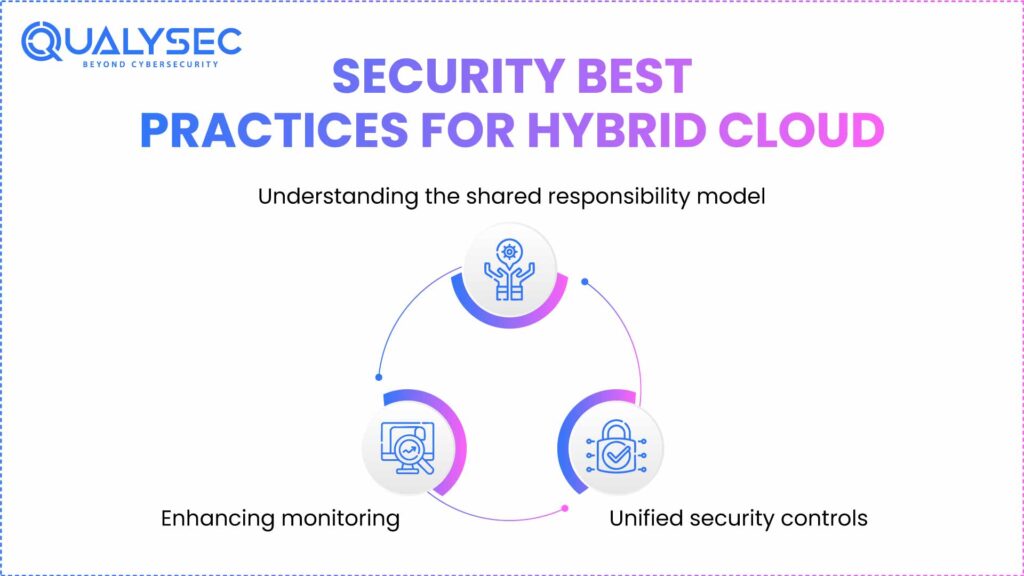
Several security best practices can be used inside a hybrid cloud environment to reduce these threats:
1. Understanding the shared responsibility model
The foundation for cloud security governance is the Shared Responsibility Model. Businesses trying to understand who is accountable for what may run into difficulties in a hybrid cloud setting if they don’t get it right. One must have a thorough understanding of this model, which describes the customer as being in charge of security in the cloud and the cloud provider as responsible for protecting the cloud.
Most hybrid cloud systems utilize infrastructure and storage solutions where consumers are responsible for securing the applications and services running on top of them. Having a thorough understanding of this model enables security teams to define their duties and fully use the security advantages the cloud provider provides.
Read also: Top 20 Cloud Security Provider Companies for 2025
2. Enhancing monitoring
Since we highlighted visibility as a major challenge within a hybrid cloud, monitoring becomes one of the key components of a successful security plan. Having total awareness of the security posture of all mixed cloud workloads is critical. This enables quick responses to security threats.
Businesses should invest in security tools that can monitor the security posture of the hybrid cloud and automate responses based on threat signals. Due to the large volume of data produced, artificial intelligence (AI) and machine learning (ML) also support such tools.
Read also: Secure Your AI/ML Systems with Expert Penetration Testing
3. Unified security controls
Maintaining security in a NIST hybrid cloud calls for the standardization of security measures. Maintaining various levels of security throughout systems results in a significant degree of risk and blind spots that hackers can exploit. Organizations must approach cloud security as a unified approach, utilizing standardized security guardrails to maintain a consistent level of security across all settings. This guarantees that data is safe wherever it is stored.
Facing unique hybrid cloud challenges? Consult with a Qualysec expert to develop a customized security strategy tailored to your business needs.
How Qualysec Can Help
Designed from the ground up to address the specific hybrid cloud security challenges, Qualysec‘s cloud security is a robust solution. It has among its main characteristics:
Unified cloud security: Cloud security provides a unified layer that covers the security of all cloud layers, including Infrastructure as a Service (IaaS), Platform as a Service (PaaS), and Software as a Service (SaaS).
Qualysec’s cloud security capabilities provide a unified view of the hybrid cloud security posture, eliminating visibility issues within the hybrid cloud environment. We can also create a cloud asset inventory, thereby giving a view into your cloud assets.
Qualysec stands out as the company that can effectively monitor the security of SaaS systems, such as Google Suite, where conventional solutions may fall short. Furthermore, it can utilize artificial intelligence, as well as User and Entity Behavior Analytics (UEBA), to skillfully analyze the vast volume of data available and identify irregularities.
This also enables it to identify insider threats, particularly within SaaS offerings. It flags privileged activity attempts as well as suspicious data access, therefore pointing to an insider threat.
Qualysec’s hybrid cloud security services provide automated security response capabilities for specific use cases. This helps with immediate risk reduction and response, particularly in the event of misconfiguration of cloud resources. Businesses can reduce the risk of unintentional cloud misconfigurations and stop them from being used by automating response and restoration.
Take control of your hybrid environment. Download our free Cloud Penetration Testing Sample Report and see how we uncover and secure vulnerabilities.
Latest Penetration Testing Report

Conclusion
Hybrid cloud security solutions in the Philippines offer significant security advantages, including greater flexibility and control, yet they also present new challenges. Companies can fully benefit from Qualysec’s hybrid cloud security by understanding these risks and applying top-notch solutions.
Looking for a proven hybrid cloud data protection? See how Qualysec can simplify your security with a personalized demo.
Talk to our Cybersecurity Expert to discuss your specific needs and how we can help your business.
FAQ
1. What is the security of a hybrid cloud?
Hybrid cloud network security in the Philippines involves the use of policies, technologies, and tactics to safeguard data, applications, and workloads across both public and private cloud environments, thereby ensuring compliance, encryption, access controls, and threat detection for seamless and secure operations.
2. What are hybrid cloud solutions?
Hybrid cloud solutions enable companies to execute workloads across both public and private cloud infrastructures flawlessly by integrating them seamlessly. Meeting various business and compliance demands, they allow better flexibility, scalability, data storage optimization, disaster recovery, and enhanced security.
3. What are the cloud security solutions?
Cloud security solutions offer tools and frameworks designed to protect hybrid cloud applications and workloads from cyber threats and breaches in cloud environments. These solutions include firewalls, encryption, identity and access management (IAM), intrusion detection, endpoint security, and continuous monitoring.
4. What is hybrid cybersecurity?
Hybrid cybersecurity combines modern cloud-native security techniques with conventional IT security procedures. Simultaneously protecting cloud assets and on-premises systems, it guarantees thorough threat detection, compliance, and risk reduction across all contexts inside a single security framework.
Related resources:
- Cloud Application Penetration Testing
- Cloud Infrastructure Security – Importance and Best Practices
- Top Cloud Computing Vulnerabilities & How to Address Them?
- The Best Way to Cloud Vulnerability Management
Have any questions? Feel free to ask now—our cybersecurity experts are here to help.























































































































































































































































































































































































































































































































































































































0 Comments