Did you ever question how UK companies are advanced in defending against cyberattacks in 2025? The rapid increase of cybercrime is showing, and simultaneously, coming to the view of hackers are becoming more complicated, and thus, perhaps, their target range could be anything from corporate systems to tiny corporate networks. Selecting Cyber Security Solution Providers in London and IT security service providers has never been more crucial than now.
This guide will lead you through the leading London cybersecurity firms, explain the kinds of solutions offered, spotlight trends and data impacting UK companies, and assist you in locating a partner meeting your specific needs. This book has you covered, whether you are a small business looking for managed security solutions or a big corporation needing total threat protection.
Global Cybercrime Statistics
Rising alarmingly, cybercrime in the UK is impacting companies of all sizes. The first step in picking the appropriate data security solution is knowing the extent of these assaults.
- UK Business Attacks: Highlights the rising digital threat scene, around 43% of UK companies had a cyberattack in the last year.
- AI-Driven Attacks: Artificial intelligence is being more and more used by cybercriminals to design automated, aimed attacks. Concurrently, UK security companies are employing artificial intelligence for predictive threat detection.
- High-frequency threats: Rise of large-scale bot scanning and network probing. For example, one of the leading UK telecoms found more than 2,000 possible attack signals per second, therefore demonstrating the frequency and force of present cyber threats.
Protect your business by consulting with Qualysec today to assess your vulnerability to modern threats. Contact us today!
Breaches in Cyber Security and Computer Security Metrics
Driven by demand for cybersecurity managed services and preventative threat detection, the UK’s cyber security companies are expanding quickly. The impact of cybercrime on the financial and operational sides is shown by these statistics:
- Economic Damages: The British cyberattacks have caused economic losses of more than £44 billion over the past five years, thus highlighting the need to invest in security proactively.
- Industry Value Contribution: Leading cybersecurity companies have greatly benefited the UK economy; email security companies alone have added over £2.17 billion in gross value.
- Rising Firm Numbers: The number of registered cybersecurity providers keeps growing; therefore, companies now have access to more goods and services than they have ever had.
Sectors Most Impacted
Cyberattacks are not equal: some sectors are more often attacked because of the sensitivity of their data or the scope of their activities.
- Retail: High-profile businesses, Marks & Spencer and Harrods, have been hit with aggressive attacks that have compromised consumer confidence and sales.
- Education: Last year, as many as 91% of UK universities experienced cyberattacks that put confidential staff and student data at risk.
- SMEs & Critical Services: Smaller companies and providers of vital services are becoming more and more targeted. Government programs seek to assist weak industries in improving their cyberdefense posture.
Protect your industry from emerging data breaches with Cybersecurity Solutions for Every Industry. Book a customized penetration testing assessment today!
Get Your Free Security Assessment
New Developments in Cybersecurity Solutions
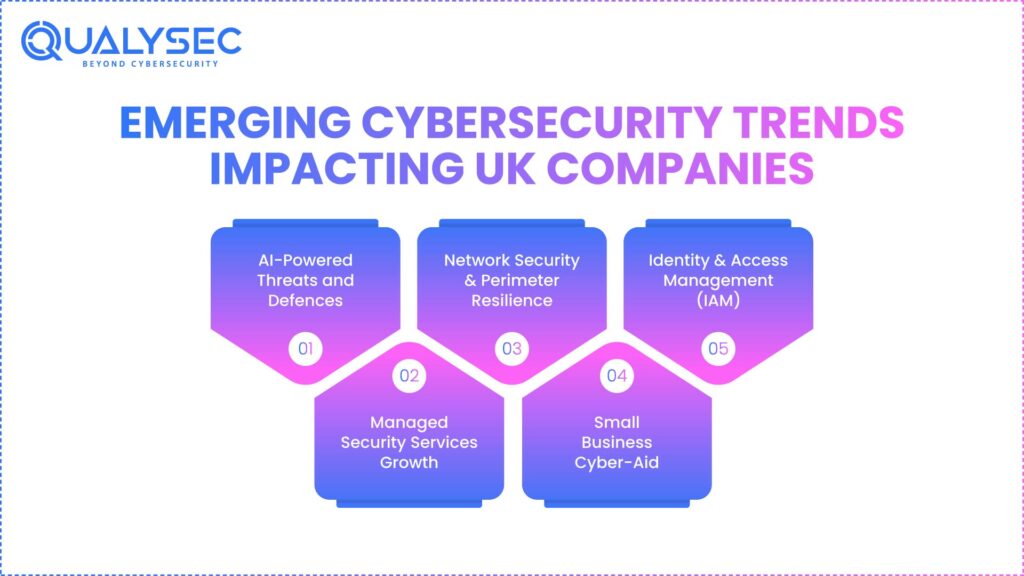
Staying ahead of developing trends is essential for safeguarding your company since cybersecurity is changing so quickly:
- AI-Powered Threats and Defences: Cybercriminals use artificial intelligence to automate attacks; security firms forecast and mitigate dangers employing AI-driven detection.
- Managed Security Services Growth: Outsourced cybersecurity as a service responsibilities, including threat monitoring, incident response, and network security, are becoming a major strategy for British firms in managed security services expansion.
- Network Security & Perimeter Resilience: Hybrid and remote working arrangements expose networks to more risk. Today, companies give network perimeter, VPNs, and access control top importance.
- Small Business Cyber-Aid: Government grants and programs now especially help small businesses in high-risk industries implement basic security precautions by providing them with Cyber-Aid.
- Identity & Access Management (IAM): IAM is of utmost importance with cloud-based processes because it enables user access control. To lower unlawful intrusions, MFA and role-based access are becoming more and more widely used.
You might like to know more about AI Security Testing: Protecting Intelligent Systems.
Cyber Security Solution Defined
Cybersecurity solutions include any good or service intended to protect an organization from internet attacks. Against a spectrum of attack vectors, these defenses protect consumer endpoints, infrastructure, sensitive data, and consumers. They range from simple antivirus programs to enterprise-class managed security services and threat intelligence systems.
- Endpoint Protection: Shields computers, desktop computers, and servers against ransomware or malware.
- Network Firewalls: Prevent illegal access by controlling and observing network traffic using network firewalls.
- Identity & Access Management: Identity and access management confirm users’ authentication and suitable permissions.
- Managed Security Services (MSS): Continuous protection is maintained by outsourced incident response and monitoring.
- Threat Intelligence & Incident Response: Proactively detects threats and lowers their harm before they hit: Threat Intelligence & Incident Response.
Varieties of Cybersecurity Solutions in UK
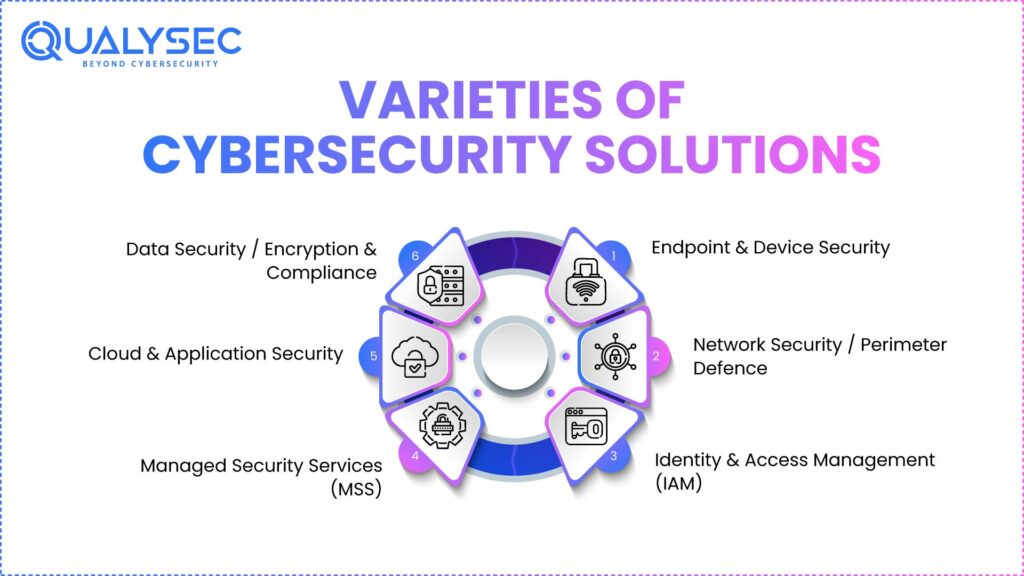
- Endpoint & Device Security: Safeguards individual devices like laptops and cellphones against malware and unapproved access. It guarantees that flaws at the device level do not damage the whole network.
- Network Security / Perimeter Defence: Using firewalls, intrusion detection systems, and traffic monitoring, network security service providers defend the network’s perimeter. Remote work situations call for this especially.
- Identity & Access Management (IAM): Restricts access by confirming identities and guaranteeing users have access just to data and resources suited to their role. Important here is MFA.
- Managed Security Services (MSS): Managed Security Services (MSS) play a key role in reducing the internal security team’s need by their outsourced services of monitoring, detection of threats, and incident response, thus giving continuous security around the clock.
- Cloud & Application Security: Securing the cloud and applications from malfunctions of web applications, APIs, and cloud infrastructure while guaranteeing the correctness of data and compliance with regulations.
- Data Security / Encryption & Compliance: Data security/encryption and compliance use encryption for data both at rest and in transit while ensuring that companies fulfill the requirements of the law, such as GDPR or HIPAA.
Top 10 Cyber Security Solution Providers in London, UK
A detailed assessment of the leading London-based cybersecurity businesses follows:
1. Qualysec
Qualysec is a leading cybersecurity company providing penetration testing, vulnerability assessment, and end-to-end security validation for businesses in the UK and globally. The company is known for its 100% manual testing methodology, which allows it to find deep and business-logic vulnerabilities that automated tools frequently overlook.
The company blends high-level security expertise along with a structured testing methodology that is suitable for organizations looking for reliable, transparent, and accurate security assessments. Qualysec offers tailored solutions for web applications, mobile applications, cloud, and APIs, aligned to the modern threat landscape.
Download a sample penetration testing report prepared by expert cyber security solution providers to identify vulnerabilities, reduce risks, and strengthen your security posture.
Get a Free Sample Pentest Report

2. Darktrace

Employing machine learning and artificial intelligence, Darktrace responds to cyberattacks in real time. Companies looking for ongoing, proactive monitoring would find them ideal because of their automatic threat-neutralizing abilities. They especially excel at finding unusual events that human teams could miss. From financial to critical infrastructure, Darktrace serves a variety of sectors.
3. NCC Group
Among the many cyber security companies, NCC Group provides risk assessments, managed security services, and consulting. They guarantee independent security assurance and assist companies in finding flaws. From penetration testing to compliance audits, their experience makes them ideal for companies wanting a reliable outside evaluation of their security posture.
4. BAE Systems Digital Intelligence
Especially for crucial infrastructure and government customers, BAE Systems, one of the leading cyber security solution providers, specializes in large-scale cybersecurity and digital intelligence solutions. Offering protective services, monitoring, and threat intelligence helps to stop significant attacks. For corporate-level security, their answers sometimes combine defensive and intelligence-gathering tools.
5. 6Point6
6Point6 focuses on end-to-end cybersecurity management as well as incident response, extended detection, and response (XDR). They support companies in getting ready for, identifying, and recovering from attacks. Combining proactive monitoring with quick response, their strategy helps mid-to-large companies to lessen the effects of security events, therefore making them a good option.
6. Focus Group
Dark-web monitoring, endpoint protection, and threat detection are among the services provided by Focus Group. They enable businesses to spot compromised credentials, track possible cyber attacks, and protect endpoints from assaults. For companies wanting to get ahead of developing risks and protect sensitive data, their solutions are especially helpful.
7. Softcat

Though its services include powerful cybersecurity features, Softcat is mostly a supplier of IT infrastructure. Their emphasis is on network security service providers, secure IT systems, and cloud security solutions. Softcat lowers operational risks by enabling businesses to plan, deploy, and administer safe IT systems.
8. PortSwigger
The primary domain of PortSwigger is web application security, and it is well known for offering penetration testing resources such as Burp Suite, the centerpiece of which is the famous Burp Suite. Furthermore, they conduct training for developers to make them more aware of security so that they can create secure applications. Cyber security solution providers products will be a great fit for those organizations looking to secure their online applications from cross-site scripting or SQL injection attacks.
9. S-RM
Offering board-level reporting, threat simulations, and incident response, among other services, S-RM is a cyber risk advisory. They assist companies in grasping strategic risks, planning for disasters, and clearly alerting executives. Their concentration on corporate boards makes them a reliable advisor for risk management and governance.
10. Ultima
For hybrid systems, Ultima offers cloud-based security solutions and improved detection and reaction. Tools for threat detection, compliance, and system monitoring that help businesses protect both on-premises and cloud settings are provided. Their responses suit companies needing all-around protection in complex IT environments.
11. Babble
Particularly for smaller enterprises, Babble melds IT services with cybersecurity awareness and education. While they put in place effective security measures, they center on educating staff on cyberattacks. Their method enables small businesses without extensive internal data security teams to find accessible and manageable cybersecurity.
Explore detailed case studies to discover how our cyber security solutions protect businesses.
See How We Helped Businesses Stay Secure

Ideal Cybersecurity Solutions for Small Companies
Though they have fewer assets, small companies continue to be prime targets. , increasing the need for reliable Cyber Security Solution Providers.
- Endpoint Protection + Anti-Malware: Simple antivirus and endpoint protection can stop the majority of assaults.
- Managed Firewall / Network Perimeter Services: Outsourced managed firewall/network perimeter solutions provide continuous protection without the need for a full-time IT staff.
- IAM with Multi-Factor Authentication (MFA): IAM support prevents unwelcomed intrusion and breaches of data through the use of MFA.
- Regular Backups + Disaster Recovery: Ordinary backups plus disaster recovery: regular backups + disaster recovery. Get your company ready for worst-case scenarios and reduce downtime.
- Training and Awareness: Employees are sometimes the weakest link; awareness of security lowers phishing and social engineering attacks.
- Managed Security Services (MSS): Small businesses may get enterprise-level security via Managed Security Services (MSS), free of much cost.
Qualysec can design cost-effective security strategies for small businesses!
Small Companies: Do They Need Cybersecurity?
Of course. Rather than a luxury, cybersecurity is a corporate must. Experience attacks also struck smaller businesses; cybersecurity for small businesses is essential as data theft, operational disturbance, and brand loss are among the possible effects. The implementation of basic and advanced security systems determines asset protection and assured business continuity.
How Qualysec Can Help
Qualysec guides UK companies through the challenging cybersecurity environment. Among our services are:
- Thorough evaluation of your security attitude
- Implementation and recommendations of endpoint, network, IAM, and MSS solutions
- Help picking appropriate UK-based service providers.
- SLA monitoring and vendor management for continuous security enhancements
See what our clients say about their experience working with our cybersecurity team. Look at our client testimonial.
Conclusion
Selecting the appropriate Cyber security solution providers should not be a stressful process. This manual has given you:
- The first step is to know about the security threats in the UK and what they consist of.
- Knowledge about the primary categories of defense options
- A handpicked compilation of the best London firms
- Guidelines suitable for small and medium enterprises
Joining forces with Qualysec means that your company will be able to apply security measures that are designed for your specific needs, effective, and, more importantly, win the battle against the new threats.
Qualysec specializes in securing organizations of all sizes. Book a free consultation to tailor your protection!
Talk to our Cybersecurity Expert to discuss your specific needs and how we can help your business.
FAQs
1. What is a cyber security solution?
A service or product that is constructed primarily to safeguard your firm against the threats of the internet is a cybersecurity solution. These threats include, but are not limited to, malware, ransomware, phishing, network intrusion, and identity theft. Various solutions might consist of managed security systems, network security, endpoint protection, identity and access management, and threat intelligence. It is primarily anything that protects your digital assets, infrastructure, and sensitive information.
2. What are the different types of cyber security solutions?
Many different kinds of cybersecurity solutions cover several attack paths:
- Protects mobile devices, PCs, and laptops from malware or assault using endpoint and device security.
- To protect network infrastructure, firewalling, intrusion detection systems, and traffic monitoring are part of network security or perimeter defenses.
- Identity and Access Management (IAM): Makes certain users are verified and appropriately authorized.
- Managed Security Services (MSS) are outsourced monitoring and incident reaction.
- With cloud and application security, web applications, APIs, and cloud infrastructure are protected.
- Encryption, backup, and regulatory compliance strategies fall under data security and compliance techniques.
3. What are the top 5 cybersecurity companies?
Although the “top” firms rely on your business requirements, in the UK context, these are regarded as noteworthy:
- Darktrace is an artificial intelligence-driven autonomous response and threat detection.
- Cybersecurity Managed services and cybersecurity consulting by NCC Group.
- Digital intelligence and enterprise-level cybersecurity provided by BAE Systems
- S-RM: Threat simulation and incident response cyber risk advisory
- Including XDR and incident response, 6Point6 offers whole-spectrum cybersecurity solutions.
4. What are the best solutions for cyber security for small businesses?
Small enterprises must provide answers, including:
- Anti-malware software and fundamental endpoint protection
- Managed network boundary or firewall solutions
- MFA with IAM
- Consistent backups and catastrophe recovery preparation
- Staff awareness initiatives and training
- Outsourced managed security services (MSS) cut costs and simplify complexity
Small businesses can protect sensitive data without depending on a whole in-house security team by means of these techniques.
5. Do small businesses need cybersecurity?
Yes, of course. Because of their typically reduced security safeguards, small firms are increasingly targeted. Cybersecurity safeguards operational continuity, financial assets, and company reputation. Strong solutions help lower the chance of data breaches, ransomware, and other cyberattacks, which might otherwise be disastrous.























































































































































































































































































































































































































































































































































































































0 Comments