In India, industries are getting smarter day by day. Factories, utilities, and energy grids rely on smarter machines which is now connected to a network. And that connection brings both convenience and risk.
That is where OT Cybersecurity steps in.
Operational Technology cybersecurity concerns the safeguarding of the systems that govern physical processes. It provides protection to industrial tools such as programmable logic controllers, sensors, and control software responsible for the secure running of factories, energy supply systems, and critical infrastructure regions.
In the past, these systems were safely isolated. They couldn’t be reached from the internet, and cybersecurity barely applied to them. Today, with Industry 4.0 connecting operational networks to IT systems, one wrong link or one infected USB drive can trigger downtime or safety incidents worth crores.
In this blog, we dig deeper into OT cybersecurity and talk about everything we need to know.
What is OT cybersecurity?
Operational Technology, or OT, is the term used to describe the combination of hardware and software that play a direct role in the control of physical devices, processes, and infrastructure. When a power plant adjusts voltage, or an assembly line moves at perfect rhythm, that is OT in action.
For decades, these systems were air gapped, meaning they were completely separated from business networks and the internet. That isolation acted as their shield. But now, modern efficiency depends on connectivity.
Factories use cloud-based dashboards to monitor performance, vendors log in remotely for maintenance, and production data flows to IT teams for analytics. Every new connection improves visibility but also opens another doorway to potential attacks.
Due to the mentioned reasons, ot security has become a necessity for Indian industries that are adopting automation and smart manufacturing. It guarantees not only data protection but also the maintenance of uptime, safety, and the ongoing operation of the plant.
Start your OT cybersecurity roadmap now!
Difference between IT and OT cybersecurity
Many organisations assume that if their IT network is secure, their cyber security ot is covered too. That assumption is misleading and can lead to heavy financial losses.
| Aspect | IT Security | OT Cybersecurity |
| Purpose | Protect data confidentiality, integrity, and availability | Protect the uptime, safety, and reliability of operations |
| System Type | Computers, networks, databases, applications | Controllers, sensors, actuators, SCADA, and DCS systems |
| Tolerance for Downtime | High, systems can be restarted easily | Very low, shutdowns disrupt production and safety |
| Threats | Data theft, ransomware, insider misuse | Disruption, manipulation, physical damage |
| Update Cycle | Frequent patches and updates | Infrequent, systems often remain operational for years |
| Impact of Breach | Financial or reputational loss | Physical harm, production loss, environmental damage |
Common Threats to OT Systems in India
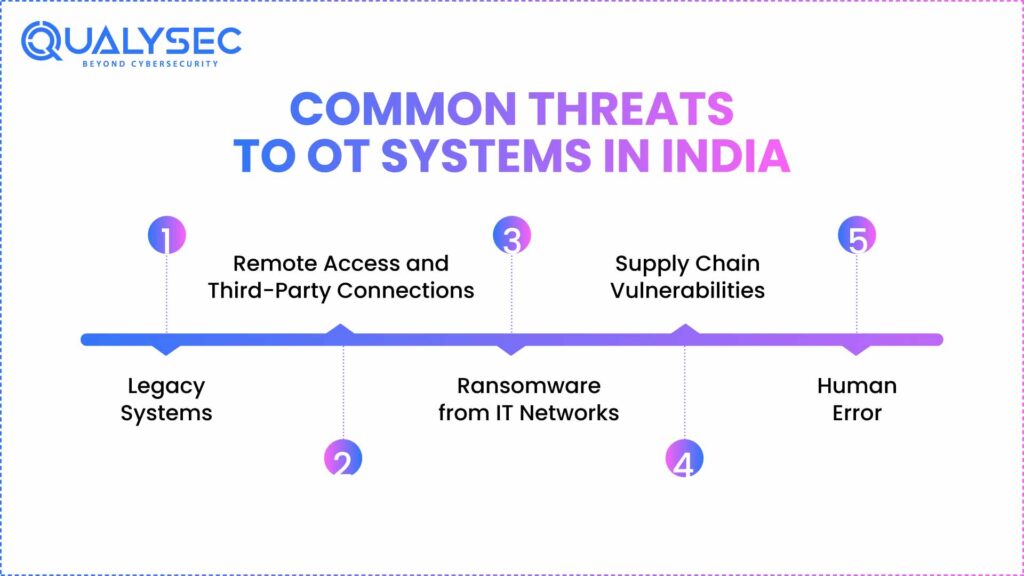
India’s industrial ecosystem is growing fast, and so are the threats to it. A great number of the facilities, from electrical power grids to industrial production, still rely on obsolete systems that were never designed with security measures to be an integral part of their overall concept.
Let’s take a look at these ot network security threats –
1. Legacy Systems
Outdated PLCs and control servers often run old software that cannot be patched or upgraded. Attackers exploit these weaknesses to gain entry into control environments.
2. Remote Access and Third-Party Connections
The remote connections that maintenance teams and vendors use for equipment control can turn into security breaches if not appropriately monitored or secured.
3. Ransomware from IT Networks
Today’s ransomware is very sophisticated, and apart from just encrypting files, it can even reach control systems, disrupt sensors, and halt production. The latest studies of different parts of the world have indicated that this trend is on the rise in the Asia Pacific region, including India.
4. Supply Chain Vulnerabilities
Software updates or external components from suppliers can carry hidden risks. If not verified, they may introduce malware or unauthorized access points.
5. Human Error
Simple actions such as using personal USB drives, skipping password updates, or ignoring alarms can cause major incidents. Human behaviour remains one of the most consistent causes of OT failures.
OT cybersecurity best practices
Here are the three best ot security practices every industrial organisation should follow to keep its OT systems secure, reliable, and compliant.
1. Build a Complete and Verified Asset Inventory
One of the foremost things to do is to start identifying every asset connected to your OT environment. It is critical to document details such as model numbers, firmware versions, network addresses, and physical locations. Keep in mind that hidden or forgotten devices often become the easiest targets for attackers. A verified inventory gives your team total visibility before any defence strategy begins.
2. Segment and Isolate Networks
If all systems share the same network, a single compromised endpoint can move laterally to control systems and safety devices within minutes. That is why it is important to divide your OT environment into zones. Place firewalls, routers, or data diodes between these zones to strictly control traffic.
3. Control Remote Access Strictly
Remote access is a great help to manufacturers in the areas of troubleshooting and maintenance, at the same time it poses a considerable risk. Thus, it is very important to come up with a comprehensive remote access policy that stipulates the who, what, when, and how of the connections made. Additionally, each remote user should be authenticated via multi-factor authentication.
OT cybersecurity: Frameworks to remember
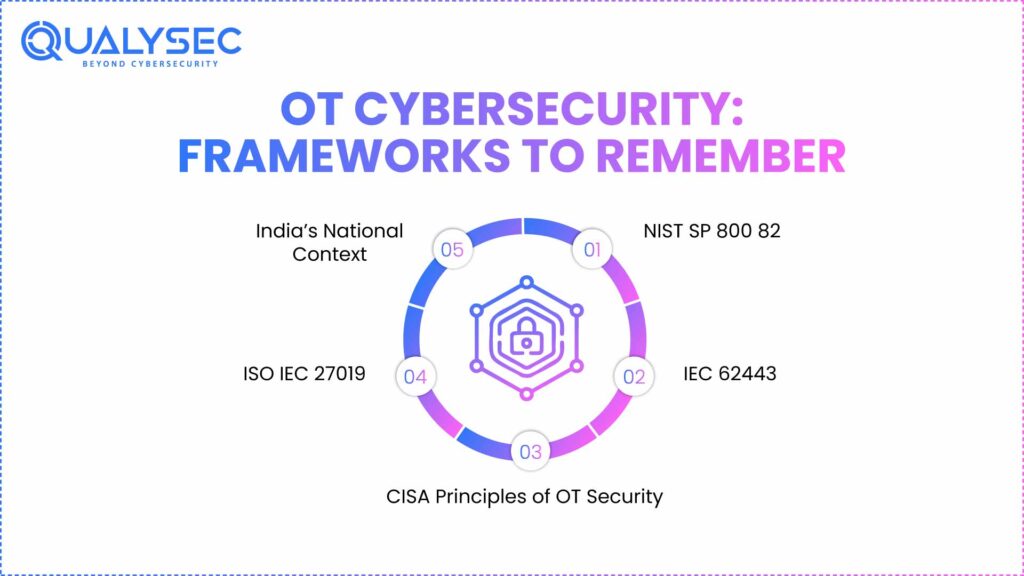
Frameworks provide structure and accountability. They ensure that security is measurable and repeatable.
1. NIST SP 800 82
It is a publication by the National Institute of Standards and Technology and presents a lucid model based on five steps: Identify, Protect, Detect, Respond, and Recover. Its application is pretty widespread in the industrial sectors around the globe.
2. IEC 62443
The international benchmark for ot in cyber security. It introduces the zones and conduits concept, helping organisations isolate sensitive assets and apply layered protection. Many Indian energy and manufacturing companies align their practices with this framework.
3. CISA Principles of OT Security
CISA simplifies OT protection into practical focus areas: visibility, risk management, controlled access, continuous monitoring, and response readiness. It is ideal for teams building the first program for ot in cyber security.
4. ISO IEC 27019
A specialised extension of ISO 27001 designed for the energy sector. It aligns information security with operational safety in critical facilities such as power grids.
5. India’s National Context
Indian agencies like CERT In and NCIIPC now issue alerts and guidance for critical infrastructure protection. The Ministry of Power has also started aligning energy cybersecurity policies with international standards. These efforts reflect India’s growing focus on industrial resilience.
How QualySec Strengthens OT Cybersecurity?
At Qualysec, one of the leading ot cybersecurity companies, we help customers from different industries achieve operational technology cyber security. Our testing procedures are intended to reveal weaknesses that even advanced automated scanners might overlook in the whole spectrum of web and mobile applications, cloud computing, API, IoT, and network environments. This expertise is easily transferable to industrial and critical infrastructure systems, where precision and safety are of utmost importance.
Our experts provide sample reports, clear methodologies, and comprehensive findings. We simplify navigating compliance expectations from ISO 27001 to sectoral mandates.
Book your OT cybersecurity consultation now!
Conclusion
Whether it’s preventing ransomware from halting production, stopping a remote-access exploit before it reaches a PLC, or ensuring compliance with national guidelines, OT security isn’t optional anymore. It’s the foundation for operational resilience.
Qualysec assists organisations in fortifying their critical areas by means of proficient penetration testing, IoT and industrial protection testing, and live vulnerability surveillance. Our professionals keep all the interconnected system devices in your ecosystem efficient and safe.
To know more, talk to our experts today!
FAQs
1. What is OT Cybersecurity and why is it important?
OT Cybersecurity (operational technology cyber security) is a concept that can be defined as the defense of industrial control systems, machinery, and physical processes against cyber attacks. It is significant since contemporary plants and utilities are based on interconnected systems. One intrusion will be enough to interrupt production, lose money, or even jeopardise safety. Operational technology security is an assurance of reliability, constant functionality, and adherence to industry standards.
2. How is OT Cybersecurity different from IT Cybersecurity?
IT security safeguards information, servers, and digital resources, emphasizing confidentiality and privacy. Whereas OT security protects the uptime, safety, and physical integrity of equipment and processes. An OT cyber attack can halt the production process or cause harm to machines, and as such, the solution should be much more regulated and risk aversion-oriented.
3. What are the common threats to OT systems?
OT systems face a mix of cyber and operational threats, including:
- Ransomware transmitted between IT and control networks.
- Infringement by vendors or contractors through remote access.
- Old devices that have old firmware or unsupported operating systems.
- Human factors, such as poor passwords or unsafe USB connections.
- Weaknesses in the supply chain, in either software or hardware updates.
4. What are the best practices for securing OT networks?
There are several best practices for obtaining operational technology security. Here are some of them:
- Keep a full list of asset inventory of the attached devices.
- Isolate critical systems by use of network segmentation (zones and conduits).
- Use tough measures of access control and least privilege policies.
- Introduce constant surveillance of suspicious behavior.
5. What tools and solutions are used for OT cybersecurity monitoring?
Commonly used solutions include:
- OT-sensitive intrusion detection systems (IDS) that identify industrial protocols.
- Siem tools that monitored the OT logs.
- Tracing asset discovery to determine new or rogue assets.
- Early warning of abnormal behaviour detection through network anomaly.























































































































































































































































































































































































































































































































































































































0 Comments