One of the most crucial pillars for any business is its network infrastructure. That is also why it is a tempting attack point for malicious cyber criminals. Enterprises in the Philippines are eagerly stepping into the digital field. The increasing number of cyberattacks emphasizes the need for an accurate network vulnerability assessment checklist.
Even the slightest aspects, such as weak passwords and improperly configured gadgets, have been the causes of malicious attacks in this era of constantly changing threats. These may cause perilous breaches, and therefore, the significance of testing the vulnerability of the network remains absolute. Selecting the right partner for a network security vulnerability assessment is crucial.
In this blog, we provide a detailed breakdown of network vulnerability testing, the benefits, a step-by-step guide, and a checklist.
What is Network Vulnerability Assessment?
Network security vulnerability assessment is the process of systematically scanning, analysing, and validating weaknesses across an organisation’s network infrastructure. It aims to identify potential entry points before attackers can actually exploit them.
An accurate network vulnerability testing follows a clear, established methodology:
- Planning and Scoping – defining what systems, networks, and wireless segments are in scope.
- Discovery – identifying live devices, services, and network paths.
- Vulnerability Detection – using automated and manual techniques to uncover flaws.
- Analysis – verifying results, reducing false positives, and prioritising risks.
- Reporting and Remediation – documenting findings with remediation guidance.
Benefits of Network Vulnerability Testing
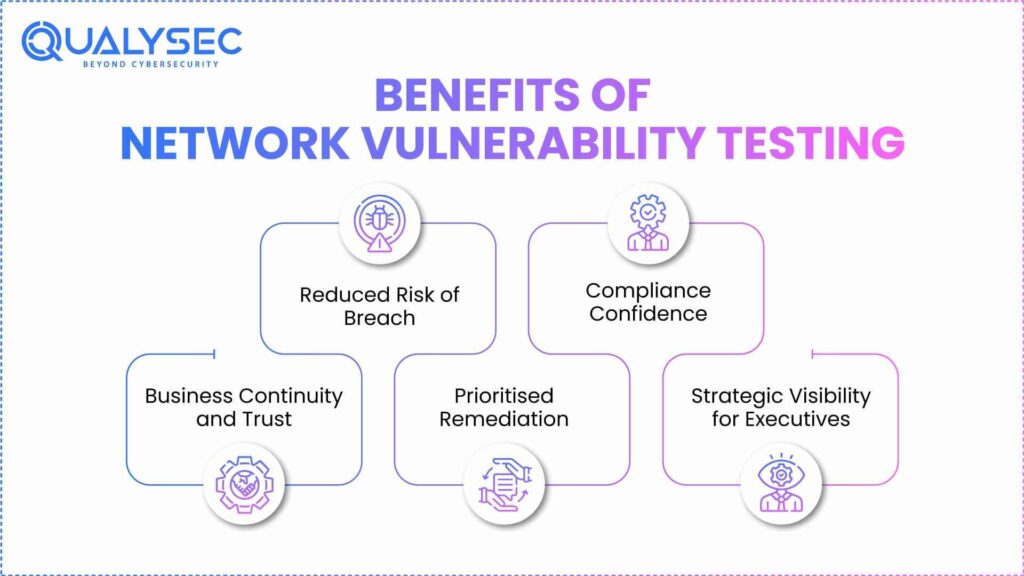
Investing in network security vulnerability assessment provides measurable advantages that extend beyond technical security. For organisations in the Philippines where regulatory scrutiny is increasing and digital adoption is rapid, the benefits are both strategic and operational:
1. Reduced Risk of Breach
Organisations secure entry points into systems that attackers exploit by identifying weaknesses such as routers, switches, firewalls, endpoints, and wireless access points. This restricts the potential impact of ransomware and phishing-induced breaches or insider threats.
2. Compliance Confidence
Testing helps organisations in meeting expectations laid out by regulators such as Bangko Sentral ng Pilipinas (BSP), which has mandated regular VAPT sessions for financial institutions, as well as internationally recognized standards such as PCI DSS for card data, ISO 27001 for information security, and CIS Controls for critical infrastructure. A repeatable testing procedure gives assurance to regulators, auditors, and partners.
3. Business Continuity and Trust
Downtime resulting from a successful compromise suspends operations and erodes customer confidence. The structured vulnerability program reduces such incidents, thereby preserving smooth continuity and brand equity.
4. Prioritised Remediation
Instead of inundating IT teams with meaningless alerts, vulnerability testing points out problems categorized by severity and business impact. Therefore, the critical vulnerabilities get fixed first, ensuring the best use of resources and time.
5. Strategic Visibility for Executives
The reports from vulnerability testing provide key leadership with a clear picture of organisational exposure. This allows decisions to be made with respect
Find vulnerabilities before hackers do. Request a Network Security Assessment today.
Network Vulnerability Testing Checklist
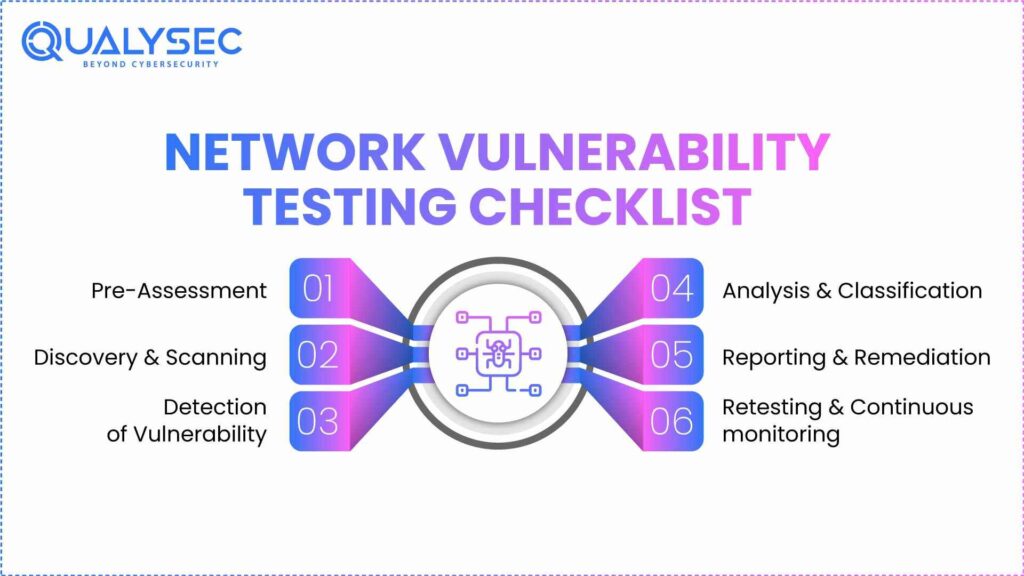
A vulnerability assessment of networks is most appropriate when designed as a repeatable process. Organizations often use a practical network vulnerability assessment checklist mapped against various frameworks as the baseline:
A. Pre-Assessment
- Define scope, objectives, etc. (wired or wireless, compliance obligations).
- Update asset inventory and make sure it is correct (assets here mean devices, servers, endpoints, access points, etc.).
- Document network topology and segmentation (internal vs guest zones).
Read also: Why Security Assessments in Philippines Are Essential in Business
B. Discovery & Scanning
- Perform host discovery and port scanning using different tools.
- Identify running services and banner versions.
- Wireless network vulnerability assessment: enumerate SSIDs, validate encryption standards (WPA2 → WPA3), and detect rogue APs.
C. Detection of Vulnerability
- Utilize automated scanning tools (e.g., Nessus, OpenVAS) to identify configuration issues related to the use of weak ciphers and outdated firmware.
- Check for default credentials, open SNMP, Telnet, or legacy protocols.
D. Analysis & Classification
- Manually validate the findings to scrap false positives.
- Express vulnerabilities in terms of CVSS scores and associate them with business effects.
- Remediate according to who can exploit it and what assets are critical.
E. Reporting & Remediation
- Audit vulnerabilities with data and a proper course of action.
- Translate the technical finding into business language for executive interpretation.
- Track fixes to confirm remediation dates.
Explore: VAPT Report Sample: A Complete Guide For Business
F. Retesting & Continuous monitoring
- Re-test when patching takes place
- The output of the merges into the continuous monitoring tools (SIEM, IDS/IPS).
Protect Your Business With End-to-End Vulnerability Testing! Request a demo now.
Our experts at Qualysec have helped secure fintech, SaaS, and enterprise systems across 25+ countries. Manual + Automated Pentesting. No false positives. Actionable reports.

Network Vulnerability Testing: Step-By-Step Guide
While it’s true that a network vulnerability assessment checklist makes certain that everything is covered, the necessity to conduct vulnerability testing requires a step-by-step, organized approach. Following is a practical process on how to go about and how to achieve a cyber security vulnerability assessment:
1: Planning and Scope
- Specify the scope of the assessment (internal requirement, compliance, vendor requirement).
- Quantify what is in scope: cloud connectors, servers, endpoints, network devices, and wireless segments.
- Identify testing intervals to minimise business inconvenience.
2: Asset Discovery & Mapping
- Perform host discovery to identify all live systems within the network.
- Create a network topology diagram to visualise interconnections and segmentation (internal vs DMZ vs guest networks).
- Validate asset inventory against existing records to detect shadow IT.
3: Vulnerability scanning
- Scanning: Can be scanned automatically using ports, services, and operating systems.
- Wireless attaching involves encryption levels, disclosure of SSID, and detection of rogue access points.
- Baseline Vulnerabilities: First, before proceeding to deeper validation, it is beneficial to identify the baseline vulnerabilities.
Read Also: What Is Vulnerability Scanning? Types, Tools and Benefits
4: Validation & Risk Prioritisation
- Manually validate critical findings to eliminate most false positives.
- Score vulnerabilities with CVSS v3/v4 and business context to establish a risk ranking.
- Orchestrate remediation prioritisation based on exploitability and potential impact.
5: Reporting
- Produce well-structured reports for the technical team (detailed vulnerabilities with PoC evidence) and executives (risk overview, compliance mapping).
- Include remediation options and patching guidance.
Download our Sample Penetration Testing Report to understand how vulnerabilities are reported and mitigated.
Latest Penetration Testing Report

6: Remediation & Retesting
- Track implementation of fixes/configuration changes.
- Retest to verify that the vulnerabilities were addressed.
- Make this an ongoing loop, ensuring the periodic re-evaluation of vulnerabilities as the environment changes.
Vulnerability Assessment Vs Penetration Testing
| Aspect | Vulnerability Assessment (VA) | Penetration Testing (PT) |
| Purpose | Broad identification of known weaknesses across systems, networks, and applications. | Simulates real-world attacks to validate how vulnerabilities can actually be exploited. |
| Approach | Breadth over depth – wide coverage using automated scans & manual validation. | Depth over breadth – focused, attacker-style methods to break through defences. |
| Methodology | Scanning tools (e.g., Nessus, OpenVAS) combined with manual verification. | Red-team style testing, active exploitation, chained attack paths. |
| Output | Prioritised list of vulnerabilities with remediation guidance. | Proof of exploitability, real attack scenarios, and risk of data compromise. |
| Best Use Case | Routine risk management, regulatory audits, and maintaining baseline hygiene. | Testing resilience against advanced adversaries, validating detection and response. |
Know more about difference between vulnerability assessment and penetration testing. Book Your Network Vulnerability Test Today.
Conclusion
Cyber security vulnerability assessment is no longer an optional IT task – it is an absolutely essential for the business. In the Philippines, where the use of the digital infrastructure is expanding and regulatory activity is increasing, proactive testing is an obvious benefit to enterprises. It makes breaches less probable, instills confidence in compliance, and maintains customer trust.
At Qualysec, we offer excellent network vulnerability testing. We provide compliance-ready deliverables to ensure your business remains secure.
Get Expert-Led Network Vulnerability Testing by Qualysec!
Talk to our Cybersecurity Expert to discuss your specific needs and how we can help your business.
FAQs
1. What is a network vulnerability assessment checklist?
A network vulnerability assessment checklist is a list of processes and tools that can be used to identify gaps in the network infrastructure. That way, it becomes easier to pinpoint the gaps or poor security settings that hackers could otherwise exploit.
2. Why is a checklist important for vulnerability assessments?
A checklist is important for vulnerability assessments because it helps you to cover all the critical access points. It also aids in improving the efficiency of the workflows, easy mitigation of the risks, and efficient allocation of resources.
3. What key items should be included in a network vulnerability checklist?
A cyber security vulnerability assessment checklist must contain key items like making an inventory of the network assets, analyzing the defenses of the network perimeter, verifying the internal systems, etc.
4. How often should a network vulnerability assessment be done?
At least, a network vulnerability assessment should be conducted at the end of each quarter. This may differ according to many factors, including the risk profile, niche, etc.
5. Who should perform a network vulnerability assessment?
Network vulnerability testing has to be conducted by skilled personnel. Knowledge of the right tools and training will play a crucial role in ensuring the report is both accurate and reliable.
Have any questions? Feel free to ask now—our cybersecurity experts are here to help.

























































































































































































































































































































































































































































































































































































































0 Comments