If your company is headquartered in Dubai and uses customer data, digital solutions, or cloud platforms, chances are you have heard of DESC compliance. Many groups feel underwhelmed when they hear it, mostly because they envision infinite paperwork, rigorous audits, and complex technological requirements. Once the framework is well explained, the truth becomes much more manageable. Although DESCs are meant to help you safeguard your digital systems, secure your cloud environments, and prevent expensive cyber incidents, they are not meant to make your life challenging.
One of the most quickly digitalizing areas, Dubai’s development raises expectations for security. As more companies embrace cloud-first strategies, the risk of breaches and data misuse rises as well. By means of DESC compliance solutions, every company operating inside the emirate adheres to a single, dependable, and contemporary cybersecurity standard. Achieving compliance becomes a straightforward process with the appropriate preparation and support that enhances trust, builds resilience, and sets your business up for scalable expansion.
From the framework’s components to how companies can meet the requirements step by step, this guide covers everything you need to know. By the end, you will be able to clearly see why DESC is important, what you must put into action, and how to confidently work toward complete compliance.
What is DESC compliance?
The Dubai Electronic Security Center produced a set of cybersecurity standards known as DESC compliance. Published in the Information Security Regulation (ISR), these standards serve as a required guideline for Dubai enterprises controlling digital systems, applications, networks, and cloud environments. The main aim of DESC is to protect local digital ecosystems from cyberattacks impacting both public and commercial organizations by making them safe, coherent, and resilient.
The ISR is required for companies handling sensitive data, running corporate applications, or interacting with cloud systems. From governance and risk management to encryption and cloud security systems, the law encompasses dozens of security measures. It also helps companies to assess their present position, address flaws, and put in place safety protocols matching Dubai’s general digital transformation initiative.
DESC compliance solutions do not exclude large companies. The ISR applies to you regardless of whether you run a startup offering software, a health clinic using digital records, or a bank handling internet transactions. Its goal is to guarantee every Dubai digital service satisfies a safe and consistent minimum, independent of the size of the company.
If you want expert help in understanding ISR requirements or assessing your current readiness for DESC compliance, Qualysec can guide you through every step with structured assessments and clear action plans!
Download a Sample Pen Testing Report

WHY DESC COMPLIANCE MATTERS FOR DUBAI BUSINESSES
Businesses dealing with data or digital services inside Dubai must comply with DESC guidelines. As the area keeps building its intelligent infrastructure, cybercriminals are also getting more complex. Reputation may suffer, operational interruptions may be caused, and sensitive data may be revealed as a result of a security breach. Following the ISR keeps your company ready, protected, and in accordance with national security standards.
Furthermore, developing consumer confidence is the goal of the framework. Firms that adhere to DESC demonstrate to partners and customers their top priority of safe operations. This results in increased eligibility for government or company-level contracts as well as better opportunities and simpler onboarding procedures. Being compliant can give you a major advantage in competitive sectors like healthcare, telecom, and fintech.
At last, DESC enables companies to lower long-term dangers and expenses. Companies that follow defined cloud usage, risk management, and monitoring rules can minimize the possibility of mishaps and bypass costly recovery operations. Setting early, tough controls helps to avoid significant problems later, especially for businesses depending on digital transactions and cloud service providers.
Who has to comply with DESC?
Operating in Dubai, a great number of organizations use DESC. Any company managing digital systems or processing consumer data must abide by the ISR standards. This covers firms controlling cloud-based applications, online platforms, vital systems, and IT infrastructure.
These requirements apply to the private sectors, including e-commerce, retail, logistics, and real estate. Financial organizations, telecom companies, and healthcare providers also require tight cybersecurity measures to secure digital processes and safeguard customer information. To preserve operational integrity and trust, governmental and semi-governmental entities also depend much on DESC standards.
Organizations that use cloud-first technology anticipate more. You must adhere to particular cloud setup and monitoring recommendations if your firm controls APIs, creates digital platforms, or utilizes a cloud service provider. Using approved cloud security solutions, DESC guarantees the security of cloud environments, including SaaS, IaaS, and PaaS.
DESC compliance essential elements
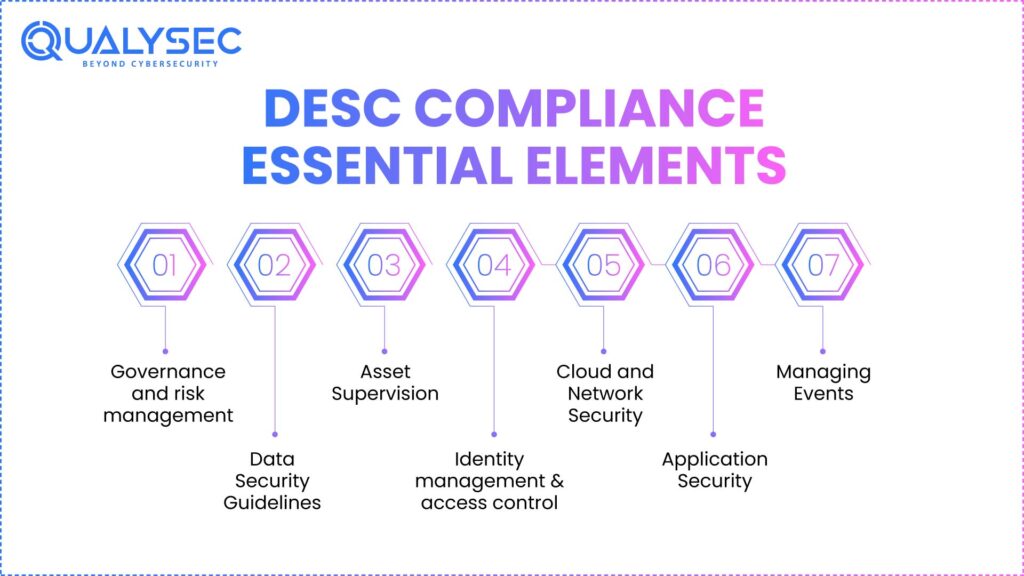
Several domains of DESC split its cybersecurity needs. Every area aims at a particular security aspect that businesses need to cover. Combined, these domains provide a robust end-to-end defensive attitude appropriate for Dubai’s digital environment.
1. Governance and risk management
Companies need to evaluate dangers, record hazards, delegate tasks, and create repeatable security procedures. This involves setting out unambiguous policies, doing frequent evaluations, and keeping an eye on how effectively controls are in use.
Identifying how risks might affect operations and creating reaction plans also fall under risk management. To keep abreast of ISR demands, groups have to carry out regular compliance security audits.
2. Data Security Guidelines
DESC demands that businesses establish organized, reviewed, and updated policies on data protection, access regulations, cloud use, and encryption. Every policy has to be recorded, shared with staff members, and examined in inspections.
Under this criterion also comes the use of cloud security solutions. Businesses have to make sure their cloud policies follow industry best practices, cloud provider terms, and the DESC’s ISR structure.
3. Asset Supervision
Asset management demands keeping comprehensive records of all digital assets. This covers data categories, devices, cloud resources, apps, and servers.
Eliminating shadow IT, preventing unmanaged systems, and guaranteeing every asset conforms to the correct security standards are all goals.
4. Identity management and access control
One of the main priorities is identity-based security. Organizations need to provide limited access privileges, robust authentication, and role-based permissions.
Increased monitoring and logging are needed for privileged accounts, and user access must be updated during onboarding and termination processes.
5. Cloud and Network Security
Businesses need to use firewalls, IDS/IPS, logging, and ongoing threat detection to protect their network design. Both local and cloud settings benefit from these controls.
Secure configurations, encryption, API security protocols, and vendor compliance requirements must be followed in cloud settings. Modern cloud security solutions and best practices fit this exactly.
6. Application Security
Application security guarantees that software is created and kept safe. This covers risk reduction, vulnerability scanning, penetration testing, patching, and secure coding.
Auditors anticipate finding specific paperwork for every test carried out, including reports from compliance security checks carried out by partners or in-house.
7. Managing Events
Businesses need to establish written incident response plans, specify reporting processes, and educate teams to quickly detect and manage incidents.
Post-incident evaluations should be conducted to stop recurring weaknesses and guarantee lessons learned are implemented into the next procedures.
Requirements for Dubai companies’ DESC compliance
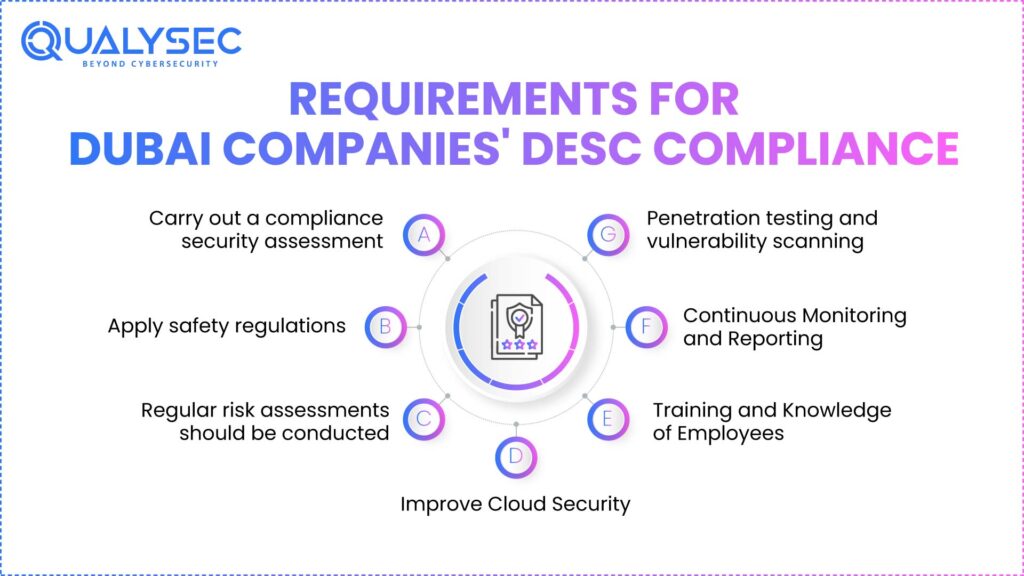
DESC defines many required conditions that every business has to meet. These conditions apply to cloud settings, auditing, security rules, training, monitoring, and configurations. Businesses remain ready for evaluations and stay free from gaps by clearly knowing them.
A. Carry out a compliance security assessment
Your present security posture is matched against DESC’s ISR model in a compliance security audit. It draws attention to areas where you satisfy demands as well as where development is required.
This audit comprises a review of paperwork, an assessment of technical controls, and tests of security measures across cloud and network systems.
B. Apply safety regulations
Companies have to create, record, and keep policies governing network rules, encryption algorithms, cloud use, authentication, and data governance.
These policies have to correspond with the size, activities, and cloud-based systems of the company.
C. Regular risk assessments should be conducted
Risk assessments point up weak access controls, outdated software, misconfigurations, and vulnerabilities.
At least once a year or following significant infrastructural changes, DESC expects companies to conduct risk evaluations.
D. Improve Cloud Security
Should your company depend on a cloud service provider, you need to make sure cloud settings adhere to safe configurations.
This includes encryption, IAM, secure APIs, multi-region backups, and constant monitoring geared with international cloud security solutions.
E. Training and Knowledge of Employees
Employees ought to be familiar with fundamental cybersecurity principles, secure data practices, phishing dangers, and incident reporting procedures.
DESC highlights training as a crucial defensive barrier.
F. Continuous Monitoring and Reporting
Companies have to monitor network activity, cloud logs, user access patterns, and odd behavior.
Meeting this need calls for either SIEM systems or SOC services.
G. Penetration testing and vulnerability scanning
Frequent testing reveals flaws in apps, networks, and cloud solutions.
Real-time insight into developing threats is provided by scanning, which guarantees that attackers cannot abuse gaps. Penetration testing helps to accomplish this. Explore the Difference Between Vulnerability Assessment and Penetration Testing.
DESC compliance vs NESA compliance
Many Dubai companies confuse DESC with NESA. Here’s a simple comparison.
| Factor | DESC (Dubai) | NESA (UAE National) |
| Focus | Dubai emirate | Federal UAE level |
| Governing Body | Dubai Electronic Security Center | National Electronic Security Authority |
| Scope | Dubai government and private entities | Critical infrastructure sectors across the UAE |
| Framework | ISR | UAE IAS |
| Coverage | Cloud, applications, networks, data | Broader national cyber protection |
| Applicability | Dubai businesses | Organizations with federal relevance |
Procedures for reaching DESC compliance
Approached scientifically, achieving DESC compliance is possible. The strategy below will help you to properly plan, close security flaws, and get ready for formal examinations.
I. Gap assessment should be done
Starting with a comparison of your current policies and rules against the ISR checklist.
This helps to find misplaced controls and allows you to give urgent repairs front priority.
II. Prioritize Critical Vulnerabilities
First tackle high-risk concerns, including antiquated systems, cloud misconfigurations, weak identity controls, and unsafe applications.
Early handling of these problems reduces your cyber danger exposure.
III. Run cloud security checks thirdly
Check that your cloud systems adhere to authorized cloud security solutions and cloud provider best practices.
Set up ongoing scanning, IAM rules, security settings, encryption, and monitoring.
IV. Create or strengthen security guidelines
Modify laws governing network segmentation, encryption, backup plans, access control, and cloud usage.
Relevant teams ought to be making policies meeting ISR needs.
V. Improve Identity Security
Use multi-factor authentication, privileged control, and role-based access restrictions.
Identity security protects the surface most frequently attacked.
If you want help completing a gap assessment, strengthening cloud environments, or preparing for the DESC audit, Qualysec offers specialized testing and compliance consulting tailored for Dubai businesses!
How Qualysec Supports your DESC compliance journey
By means of systematic assessments, hands-on testing, and end-to-end support, Qualysec helps Dubai-based companies to satisfy DESC requirements. Our team reviews applications, identifies compliance problems, protects cloud services, and produces the paperwork needed for audits. For your company, we translate the challenging ISR requirements into clear, workable acts.
By cloud-based assessments, secure architecture audits, and continuous monitoring recommendations, we assist businesses. Whether your hybrid infrastructure, Azure, GCP, or AWS runs, our team guarantees your cloud systems satisfy ISR-mandated controls. On the application level, to ensure whole coverage, we perform vulnerability assessments, API security evaluations, and extensive penetration testing.
From policy reviews and audit reports to remediation plans and building requirements, Qualys provides all the documents required. We remain engaged until your business satisfies every compliance expectation, thus ensuring simple and stress-free travel.
If you want a partner who can handle your full DESC compliance process—assessment, testing, cloud review, and documentation—Qualysec is ready to help!
Conclusion
For companies in Dubai, DESC compliance is not just a legislative requirement but a means to a safer digital environment that is more resilient. By being in line with the ISR framework, organizations gain cloud security, protect sensitive data, and mitigate their risk from the escalating cyberattacks. Furthermore, it paves the way for greater business opportunities, boosts customer confidence, and ensures smoother approvals when partnering with government or commercial customers.
If the process is broken down into simple steps, it becomes more manageable even if it seems initially daunting. If the right support and training are in place, companies can confidently meet the DESC requirements and build a strong cybersecurity posture. No matter if you are running a startup, a medium-sized company, or a large corporation, the road to compliance will give you the results in terms of better security, smoother operations, and long-lasting trust.
Speak directly with Qualysec’s certified professionals to identify vulnerabilities before attackers do.
FAQs
Q1. What is DESC compliance?
Total adherence to the cybersecurity rules established by the Dubai Electronic Security Center (DESC), which entail securing the operation of digital systems, applications, networks, and cloud environments, is the meaning of DESC compliance.
Q2. Why is DESC compliance required in Dubai?
DESC compliance serves to strengthen the security of organizations against cyber threats, encourage the safe use of the cloud, enhance data protection, and align companies with Dubai’s security law.
Q3. What does DESC compliance include?
It encompasses the frameworks, policies, and processes for infrastructure security, identity management, incident response, auditing, monitoring, and the provision of cloud security services.
Q4. What are the key requirements of DESC compliance?
Among the main requirements are risk analyses, revised security policies, audits, cloud security technologies, staff education, and penetration testing.
Q5. How do organizations achieve DESC compliance?
Several key requirements include conducting risk assessments, revising security policies, performing audits, adopting cloud security technologies, providing employee training, and conducting penetration testing.
Q6. What is the difference between DESC and NESA compliance?
They go through the ISR office document preparation, policy updating, compliance audits, provision of secure cloud services, and reinforcement of identity management controls.























































































































































































































































































































































































































































































































































































































0 Comments