Artificial intelligence is rapidly becoming a frontline protector against increasingly complex threats, rather than merely a buzzword in cybersecurity. Traditional security systems (signature-based antivirus or static rule-based systems) are increasingly unable to find polymorphic malware, zero-day exploits, or covert insider threats. AI threat detection strengthens defenses by continuously analyzing behaviors across the network and endpoints, flagging anomalies that conventional security might miss.
What Is AI Threat Detection?
Fundamentally, AI threat detection entails using sophisticated artificial intelligence (AI) and machine learning (ML) to constantly monitor, evaluate, and categorize security-relevant data—that is, identifying threats in real time instead of just matching known harmful signatures.
This is building models that understand “normal” system behavior using supervised and unsupervised learning so that deviations (anomalies) can be quickly marked. By matching it with prior events, Qualysec emphasizes how AI Threat Intelligence can analyze great amounts of data—for instance, authentication logs—to identify threat actor activity. Hence, artificial intelligence-threat detection changes security from reactive to predictive.
Watch how Qualysec uses machine learning and behavioral analytics to find dangers before they spiral out of control; inquire right now for a demo.
How AI & ML Identify Threats in Real Time
Using several complementary powers, AI and ML swiftly identify threats:
Behavioral analytics include the development of baselines of user and system behavior using ML models. The system flags as suspicious new activity that departs from this baseline (e.g., unusual login hours, side movement). AI finds known malicious patterns (e.g., malware execution behavior) inside data streams. Advanced pattern recognition reveals delicate hacker behavior concealed in great telemetry.
ML projects how possible future threats could seem based on past occurrences and historical threat intelligence, hence enabling proactive defense. Artificial intelligence can analyze email content, linguistic clues, and metadata in order to spot AI phishing detection in real time. More sophisticated solutions, according to Qualysec, can even generate information on discovered threats and automatically recommend actions.
All of this together helps to produce strong AI-driven threat detection that allows AI cyber detection across cloud environments, endpoints, and networks. Experience first-hand automatic threat detection and reaction by assessing Qualysec’s real-time machine-learning system.
Types of Cyber Threats AI Can Detect Automatically
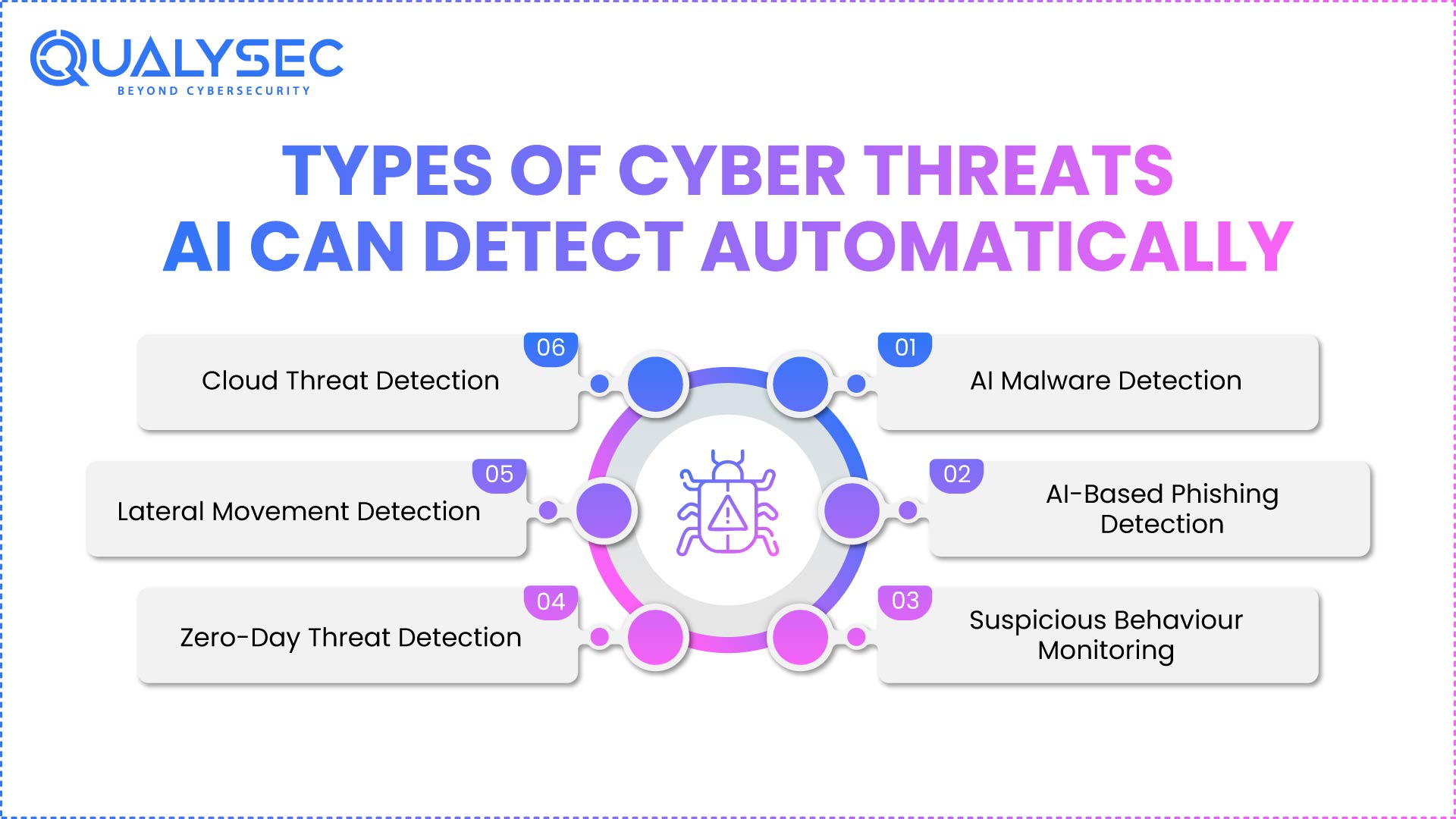
Handling a wide range of threats, AI threat detection is flexible. Among these are:
- AI discovers new AI-based malware detection across endpoints by examining file behavior instead of depending only on signatures.
- Using natural language processing and metadata analysis, artificial intelligence in cybersecurity can detect AI-driven phishing even if it is extremely targeted.
- Behavioral analysis points to odd access patterns, late-night logins, or big file transfers.
- Because it is not limited to known signatures, artificial intelligence can find zero-day activity by detecting abnormalities.
- Lateral movements or command-and-control behaviors are caught with continuous traffic monitoring.
- AI threat detection in cloud settings can identify runtime irregularities, container compromise, or workload drift.
This enables Advanced threat detection to be much more comprehensive and proactive.
With Qualysec’s artificial intelligence-driven threat detection, protect against both known and newly discovered threats—get in touch for a free trial.
Talk to Us About AI Threat Detection for Real-Time Cybersecurity
Real-Time Threat Detection Workflow: Step-by-Step
Based on industry standards and guidelines, an AI-based real-time threat detection system, often enhanced with AI/ML pentesting, usually operates as follows:
- Collect logs from network flows, user behavior, identity systems, and threat intelligence feeds, as well as endpoints.
- Organize, annotate, and clean data so that ML algorithms can understand it.
- Build behavioral baselines—user, device, network, using ML.
- Continuously compare incoming data against the baseline to identify deviations.
- Based on pattern recognition, classify detected anomalies (e.g., malware, phishing, insider threat) under threat classification.
- Alert security experts or set pre-defined actions—for instance, isolating a device, blocking a suspected process, or quarantining an email. Qualysec highlights how AI security may fully automate alerting and reaction.
- Over time, feed results back into the ML system so it sharpens its detection models.
- Artificial intelligence and ML’s persistent monitoring depend on this ongoing cycle.
You may like to know more about what an AI Risk Assessment is, its Importance, and the Process.
Benefits of Using AI and ML for Continuous Security Monitoring
Using AI-powered threat detection and AI-driven penetration testing has significant benefits:
- Early in the kill chain, artificial intelligence identifies threats, reducing dwell time.
- Behavioral analysis sharpens AI’s models to minimize noise. Advanced AI lowers false alarms by distinguishing benign from malicious activity.
- Automated playbooks considerably cut down the time between detection and mitigation.
- Qualysec’s cloud-native detection efforts especially value AI as it scales to great and complicated environments, including containers, endpoints, and cloud.
- Through AI security testing, alerts can be prioritized by risk, therefore assisting teams to concentrate on the most dangerous threat vectors.
- By simulating threat patterns, artificial intelligence offers predictive insight into forthcoming risk.
- Repetitive security jobs that are automated release human analysts for more thorough inquiry and strategic projects.
Request a custom walk-through now to see how Qualysec’s AI-driven network security can protect your business and enhance threat detection.
Best Practices for Implementing AI Threat Detection
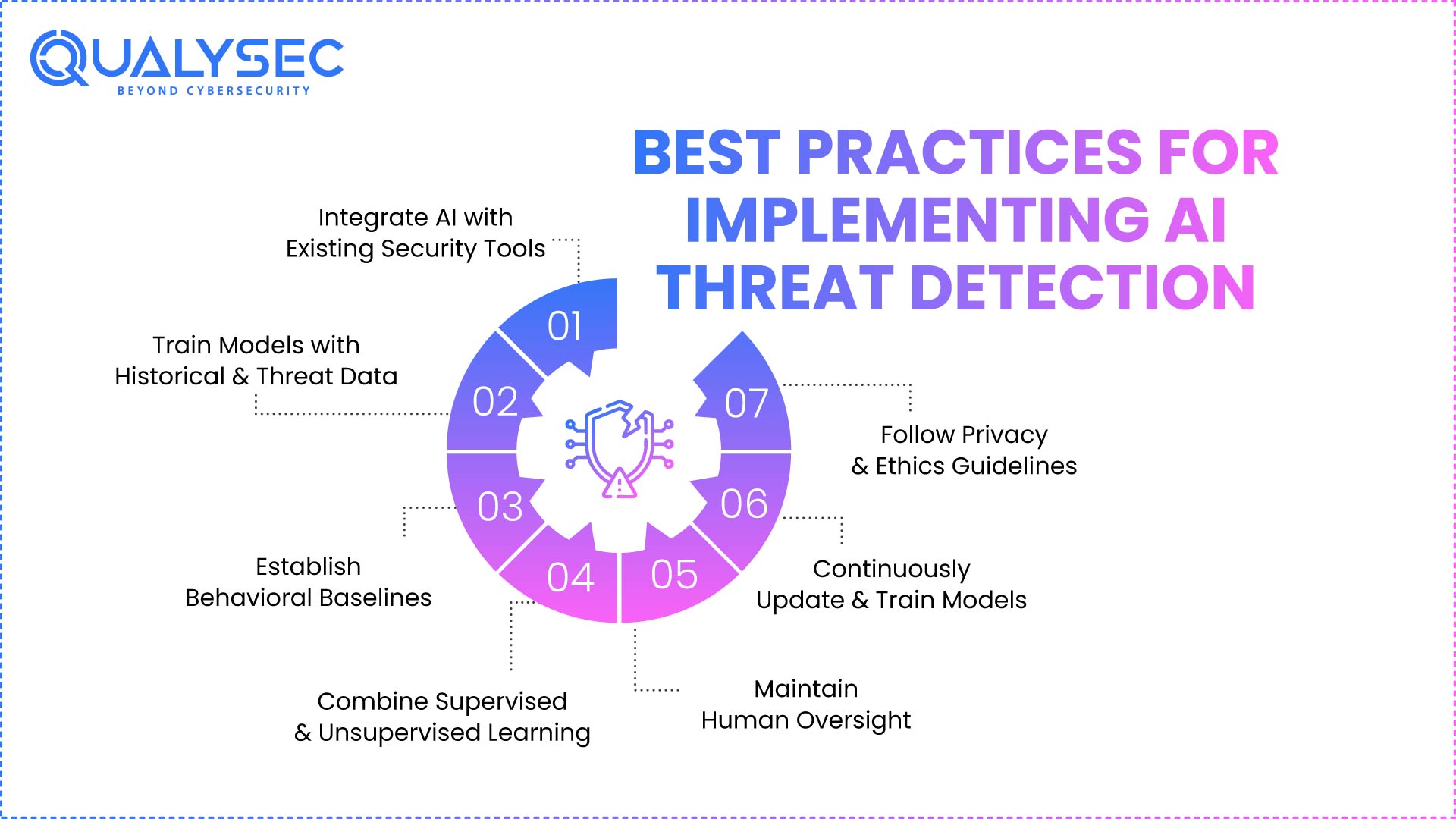
To get the most out of artificial intelligence while lowering risks, businesses should:
- AI solutions should consume from and feed your SIEM, SOAR, EDR/XDR, and IAM tools. Use of a hybrid model that combines rule-based and artificial intelligence-based detection.
- Teach your machine learning models using historical logs, identity data, and threat intelligence.
- Set early behavioral baselines with behavioral analysis to define ‘normal’ in your surroundings.
- Integrating supervised and unsupervised learning lets one identify seen as well as hidden hazards.
- Human oversight must be kept; people improve the models over time by means of validation of AI alerts.
- Models have to develop along with threat actors; thus, constant training and updating are essential.
- Be honest about data use and conform to compliance systems by means of the adoption of privacy and ethics policies.
Start with us; Qualysec helps your AI adoption path with top-notch templates and specialist advice
Download a Sample Pen Testing Report

Challenges of AI-Based Threat Detection
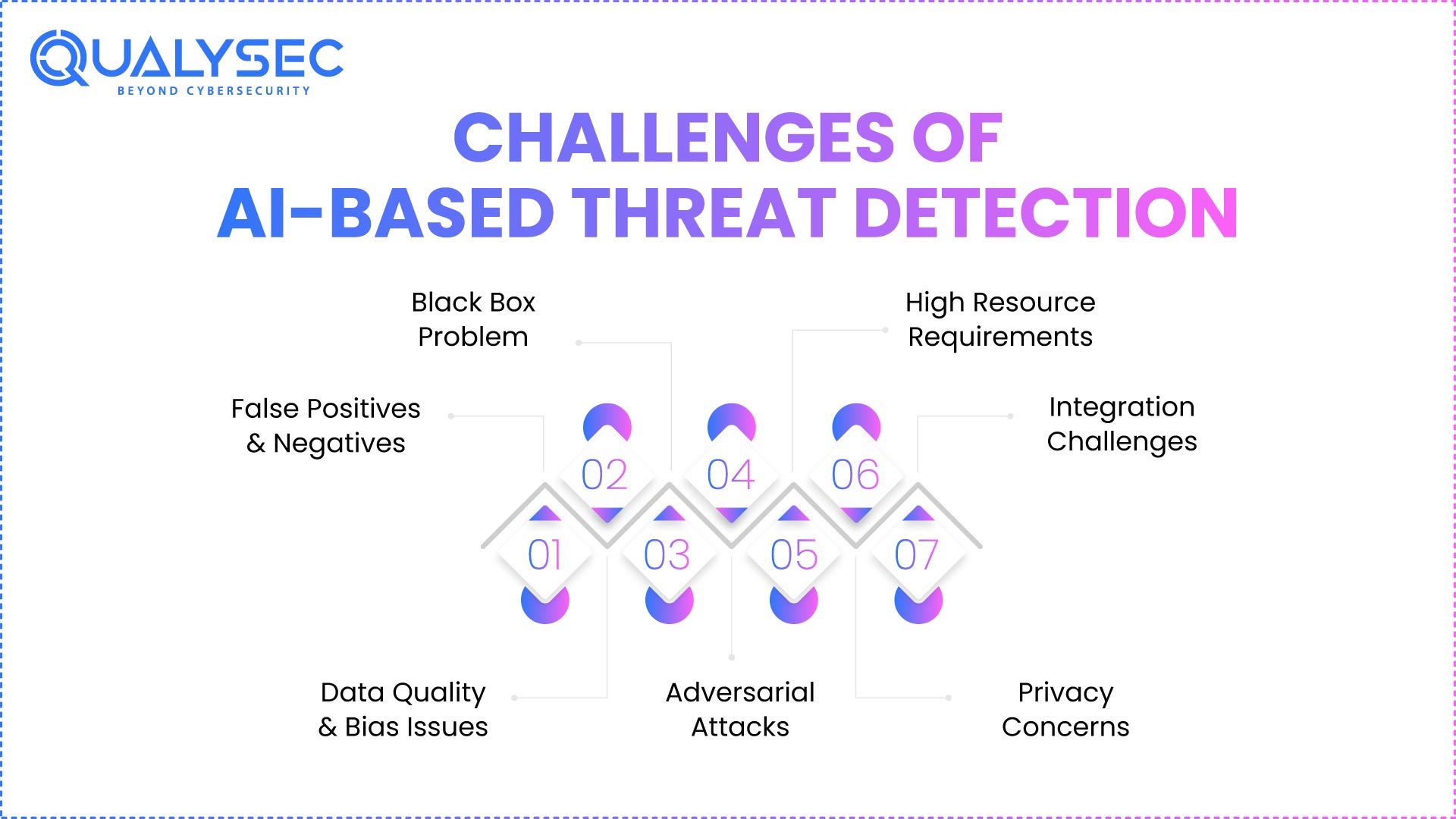
Although artificial intelligence is strong, it is not a silver bullet. The following are major problems and AI security vulnerabilities:
- Incorrectly trained models might misclassify natural behavior or overlook complex assaults, hence producing false positives or negatives.
- Detection accuracy suffers if training data is inadequate or biased, thus affecting data quality and bias.
- AI systems can work like a “black box,” therefore making their decision-making difficult to decipher.
- Hackers could seek to poison machine learning models or create inputs to escape discovery via antagonistic manipulation.
- Building, operating, and re-training artificial intelligence systems call for computing capacity and knowledgeable people, therefore incurring resource expenses.
- Ongoing behavioral monitoring brings up privacy questions and data security issues, especially without well-defined guardrails.
- Difficulties abound in using artificial intelligence in traditional settings and in coupling it with already installed security systems.
Read our case studies to discover how Qualysec’s AI-driven threat detection system can help you stay ahead of contemporary cyber threats.
Conclusion
Detection of threats through machine learning and the behavior of users is an AI that has become revolutionary in the world, where cyber threats evolve faster than ever. By transforming signature-based approaches to intelligent and adaptive models, organizations are able to identify AI phishing detection, AI-based malware detection, zero-day threats, insider threats, and so on, in real time.
According to the best practices and real experience of the world leaders, such as Qualysec, Palo Alto Networks, and SentinelOne, AI threat detection offers faster response, better threat detection, and fewer false alarms. However, success will be achieved through their integration with the existing security systems, ensuring the tremendous data, and maintaining human oversight. Adopting AI security tools is a tactical step of predictive, autonomous, and scalable cybersecurity, and not merely a technological upgrade.
Are you prepared to change your security stance? Discover how the AI-based threat detection in Qualysec can protect your digital infrastructure- contact us to have a demo or a consultation.
Speak directly with Qualysec’s certified professionals to identify vulnerabilities before attackers do.
FAQ
1. How does AI enhance threat detection compared to signature-based methods?
Once artificial intelligence relies on behavioral analytics, pattern recognition, and predictive modeling rather than the use of known threat signatures alone, therefore, it becomes much more effective against unknown threats or zero-day threats. An artificial intelligence model identifies changes in the normal operation of a system in order to identify an anomaly or malware.
2. Which three AI-driven cybersecurity capabilities significantly enhance threat detection and response?
Particularly, three AI-powered security functions enhance response and threat detection: behavioral analysis (including baseline building and anomaly detection) and Anomaly detection, as well as pattern recognition. According to Qualysec, providing prescriptive direction, automated response, and remediation.
3. Can AI detect zero-day vulnerabilities?
Artificial intelligence makes it possible to detect zero-day vulnerabilities. Yes. As artificial intelligence does not rely on familiar malware detection signatures, it can detect anomalous activity or abuse patterns that portray zero-day threats.
4. How accurate is AI-based threat detection?
The training data, the quality of the behavioral baselines, and how well models are maintained all affect accuracy. Usually, AI provides higher detection rates with fewer false positives than rule-based systems when properly trained and managed. Qualysec also alerts about possible inaccuracies or bias if models are not well set.
5. What is AI-driven anomaly detection?
AI-driven anomaly detection uses machine learning to create a model for “normal” behavior (for users, devices, networks) and then monitors for any deviations from that baseline. Anomalies discovered—such as an atypical login or odd data transfer—are noted for further inquiry.
6. How is AI used in threat detection?
AI helps us to:
- Eat and evaluate security information (log files, telemetry, threat intelligence)
- Baseline behavior should be learned using behavioral analytics.
- Find attack predictive patterns, anomalies, and signals.
- Analyze email/text material using NLP to detect AI phishing.
- Investigate file behavior to provide artificial intelligence-based detection of malware.
- Use generative AI (in advanced systems) to automate response measures or direct remediation.
Talk to our AI assistant about letting Qualysec’s AI-driven security organize this whole detection-to-response process for your business.























































































































































































































































































































































































































































































































































































































0 Comments